Featured News
-
 177Vulnerabilities
177VulnerabilitiesKemoge Android Adware Campaign Can Lead to Device Takeover
Google has been busy removing a number of apps from Google Play that are disguised as popular selections that are actually pushing...
-
 191Hacked
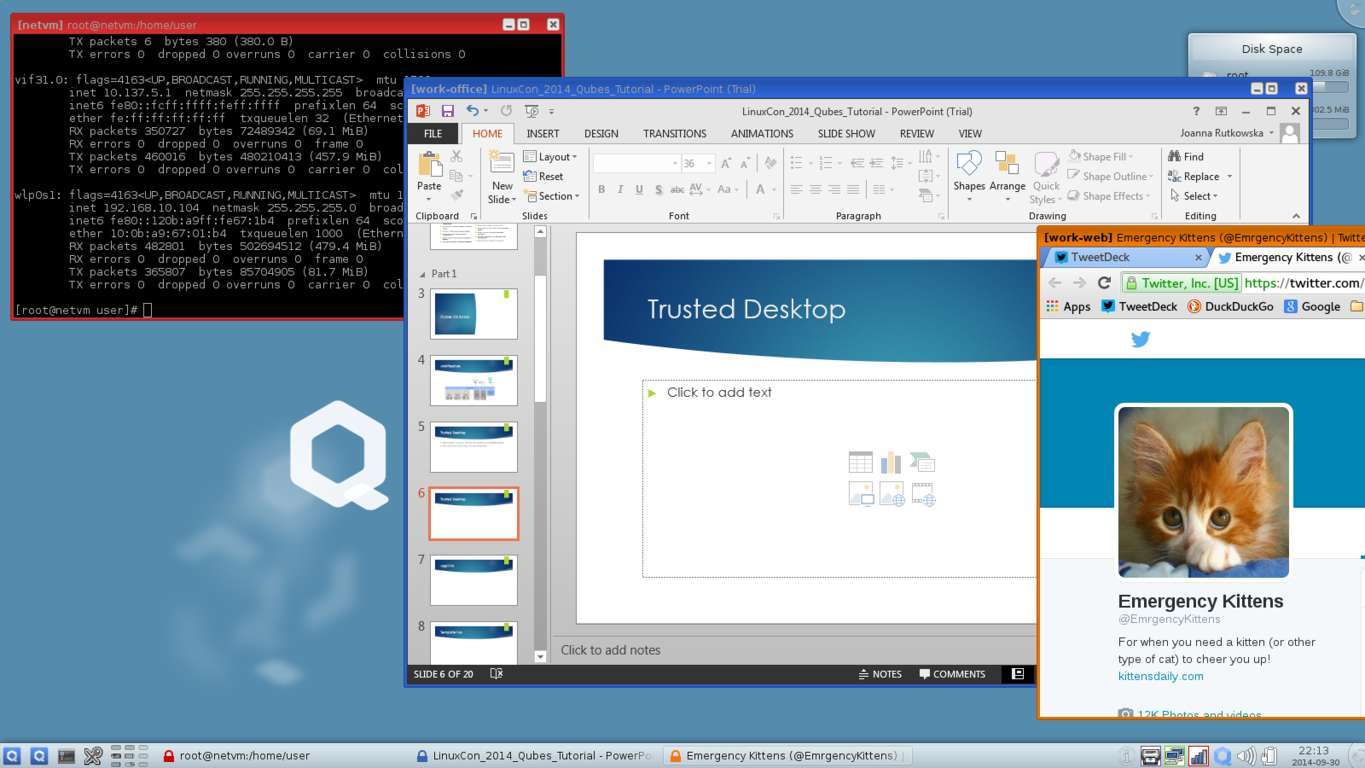
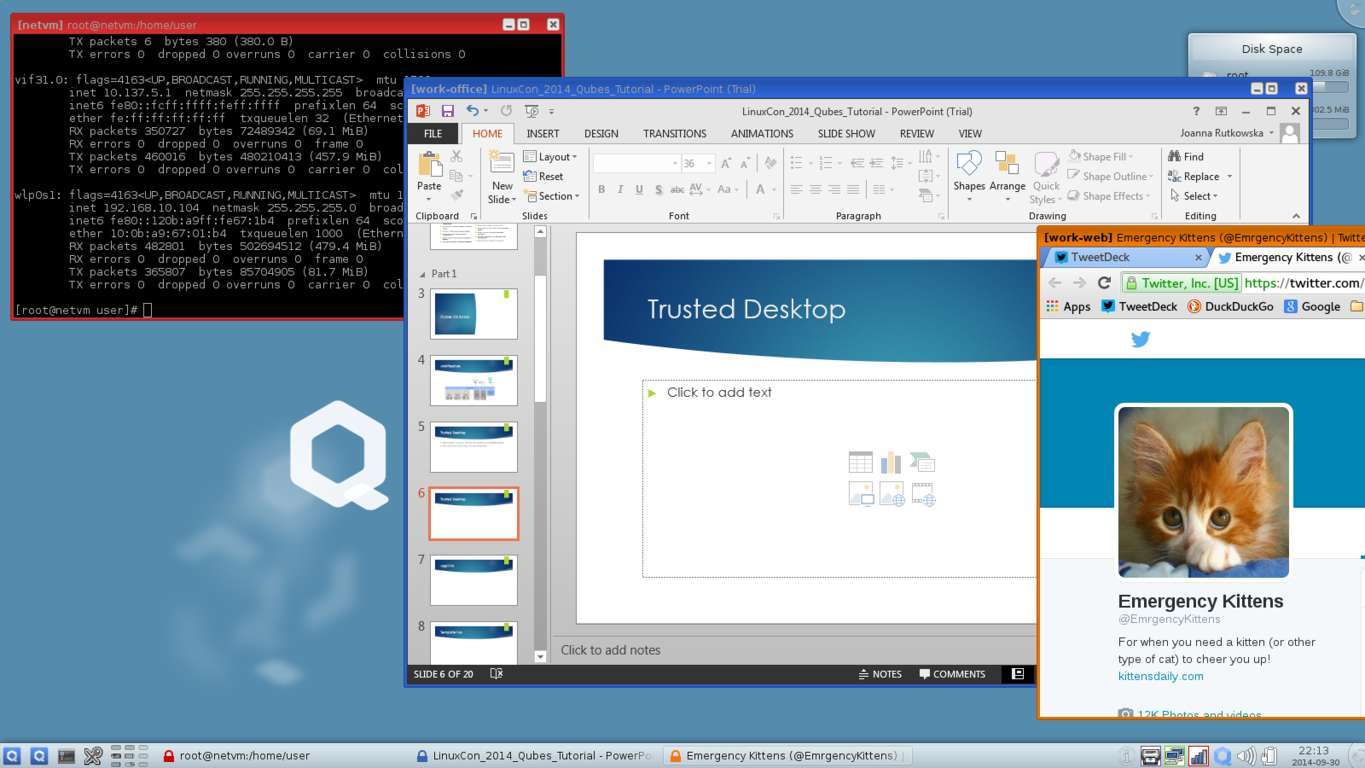
191HackedFree and Secure Qubes OS Protects You By Assuming that It’s Already Hacked
Short Bytes: Qubes OS is a free and open-source software (FOSS) that takes the security standards to a new level. It makes use...
-

 226Hacked
226HackedGoogle Expert Detects Zero-Day Exploit in Avast Antivirus
Short Bytes: Avast was detected with a serious zero-day exploit by a Google security expert. The antivirus software was vulnerable to malicious...
-

 110Data Security
110Data SecurityNew Moker RAT Bypasses Detection
Researchers warned Tuesday the latest APT to make the rounds features a remote access Trojan that can effectively mitigate security measures on machines and grant...
-

 189Vulnerabilities
189VulnerabilitiesZero-Day Exploit Found in Avast Antivirus
Avast was vulnerable to malicious HTTPS connections. One of Google’s security experts found a zero-day exploit inside the Avast antivirus, which the company...
-

 189News
189NewsBrazilian Hackers Target Government Websites, Question Corruption and NSA Snooping
A group of Brazilian hackers took over a couple of government-owned domains on Sunday posing the question, if these websites are so easy...
-

 300News
300NewsMicrosoft Transforms Sci-Fi into Real Life with Wearable HoloLens Kit
Microsoft, at their Windows 10 Devices event in New York, unveiled the pricing and availability of the HoloLens Development Edition. During the...
-

 383Surveillance
383SurveillanceSnowden Exposes “Smurf Suite”, Reveals GCHQ Hacked Cisco Routers in Pakistan
Since joining Twitter, Edward Snowden is more active than ever. In his latest revelation, the whistleblower has claimed that the British intelligence agency...
-

 198Cyber Events
198Cyber EventsAnonymous Starts Operation Black October To Target Banking Sector
It’s time to Pull your Money Out of the Banks- Suggests the Online Hacktivist Group — Anonymous Takes Hacktivism to Another Level. The...
-

 209Opinion
209OpinionAre healthcare organizations ready to get serious about security … now?
ESET security researcher Lysa Myers looks at a few of the questions she has been hearing more often about the recent surfeit...
-

 124Scams
124ScamsWhatsApp scam extends into multiple countries and brands
IKEA, KFC, H&M and 7-Eleven are just a few popular brands that are being exploited by cybercriminals via WhatsApp. We take a...
-
 507Scams
507ScamsTech Support Scams: Top of the Pop‑Ups
Support scams and fake alerts are still big business. We look at scammer psychology and a little parapsychology.
-

 100Data Security
100Data SecurityCreators of the Benevolent Linux.Wifatch Malware Reveal Themselves
Linux.Wifatch’s creators call themselves The White Team.The Linux.Wifatch malware, also dubbed as the “vigilante malware” has been going around the Internet, infecting...
-

 226Hacked
226HackedBeijing is 100% Covered by the Skynet of Surveillance Cameras
Short Bytes: China, in its effort to improve its security during the National Holiday, covered entire Beijing under video surveillance. In the...
-

 259News
259NewsSouth Korean subway system hacked, North Korea a possible culprit
The Subway system at the heart of Seoul, South Korea was hacked in 2014 and a local lawmaker claims that the culprit...
-
 203Data Security
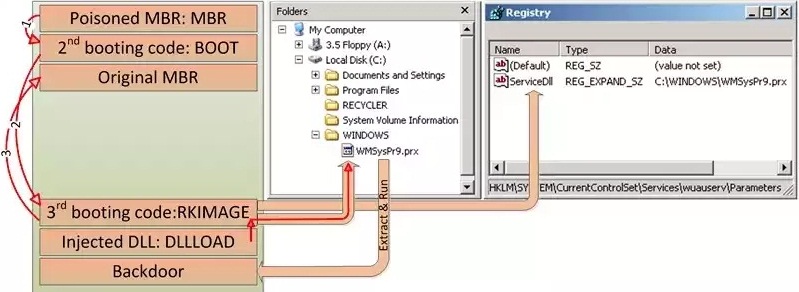
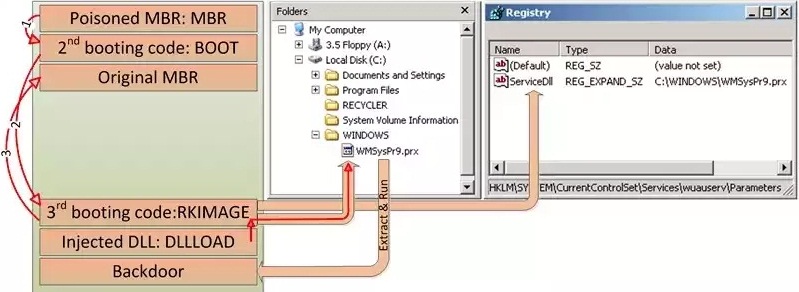
203Data SecurityHDRoot Bootkit Impersonates Microsoft’s Net Command
HDRoot is the work of the Winnti APT group. Hackers activating mainly in South-East Asia have developed a new bootkit trojan, which disguises...
-

 115Vulnerabilities
115VulnerabilitiesRemote code exec hijack hole found in Huawei 4G USB modems
Ruskies sling malicious packet to trigger denial of service. Positive Technologies researchers Timur Yunusov and Kirill Nesterov have found since-patched remote execution...
-

 165Vulnerabilities
165VulnerabilitiesCisco shuts down million-dollar ransomware operation
Group used Angler Exploit kit to push ransomware on unsuspecting Internet users. Security researchers have disrupted an online criminal operation they estimated...
-

 185Geek
185GeekBanking Malware Masked as PayPal App Targeting Android Users
Hackers are targeting users with fake PayPal app update email which actually comes with an embedded link of an Android banking malware....
-
 176Lists
176ListsWhich Phones Are Getting the Android 6.0 Marshmallow Update? The Complete List
Short Bytes: The Android 6.0 Marshmallow update party has begun and we are here with the complete list of devices that are getting...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




