Featured News
-

 315Data Security
315Data SecurityHackers Can Exploit Security Flaws In Drones To Hijack Flight Controller
Security flaws have been found in drones that could allow hackers to target and attack the flight controller which includes numerous sensors...
-

 385News
385NewsExperian Hack Leads To Data Breach of T-Mobile Customers
Experian, a major credit reference agency has suffered a huge data breach. Around 15 million T-Mobile users (who signed up for T-Mobile’s...
-

 254Geek
254GeekFacebook Becomes Livelier with a 7-sec Video Profile Pic
On Tuesday, Facebook announced that tests are being conducted which will allow users to change their static profile pic to a 7-sec video clip. Facebook is now...
-

 183Hacked
183Hacked15 Million T-Mobile Users’ Data Stolen From Experian Hack
Short Bytes: T-Mobile CEO John Legere has confirmed that its 15 million users’ database has been hacked as its credit vendor Experian...
-
 292Hacked
292HackedHackers Spreading New Router Malware That Actually Makes Routers More Secure
Short Bytes: Linux.Wifatch not only prevents further attacks from router malware, it also shows a message telling the people to change passwords and...
-

 107Geek
107GeekMicrosoft Reconsiders Privacy Policy, Windows 10 Will Continue To Pull Data
Since the official public launch of Microsoft’s new operating system Windows 10 and the announcement of the company’s revised all-in-one privacy policy,...
-

 224Incidents
224Incidents15 million T-Mobile customers affected in Experian hack
SCHAUMBURG, Ill. — Credit-reporting agency Experian said on Thursday that hackers accessed the Social Security numbers, birthdates and other personal information belonging...
-

 268Hacked
268HackedHackers Release Gigabytes of Stolen Data From Patreon Donation Site
Short Bytes: Hackers have released potentially damaging 15GB worth of private data after attacking Patreon, a crowdfunding website for artists. On an...
-

 111Vulnerabilities
111VulnerabilitiesApple swiftly closes hole in iOS 9 Lock screen
Apple just released iOS 9.0.2. This new version claims to close the well-publicised Lock screen hole that lets anyone view and edit...
-
 97Vulnerabilities
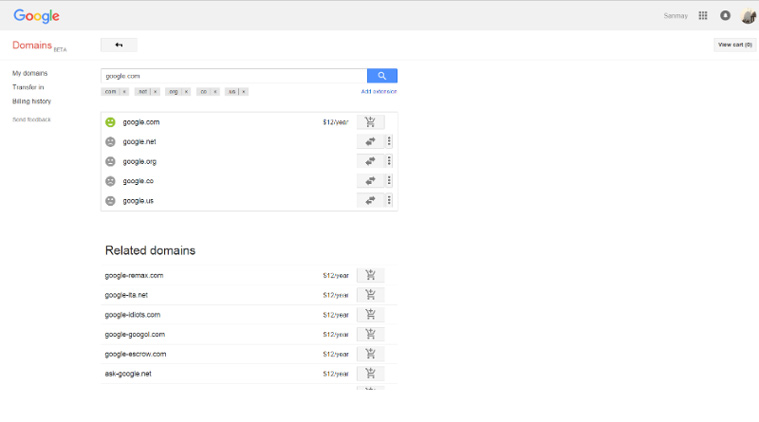
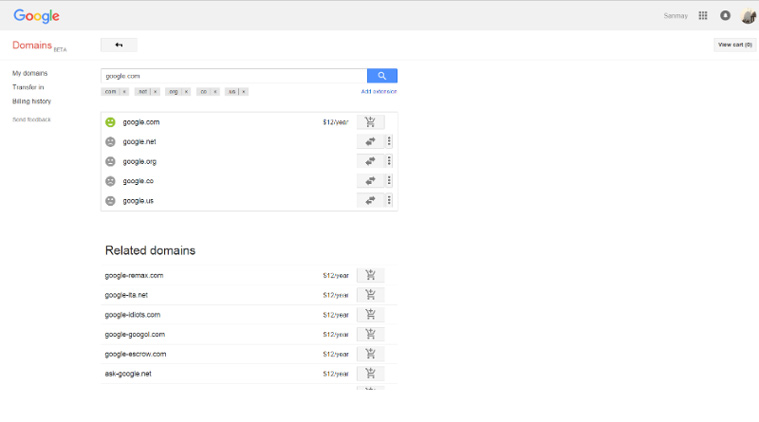
97VulnerabilitiesMeet Sanmay Ved, the Indian who owned Google.com for a minute
Ex-Googler Sanmay Ved was lucky enough to grab Google.com domain, but only for a minute. google.com purchase screen In a detailed post...
-
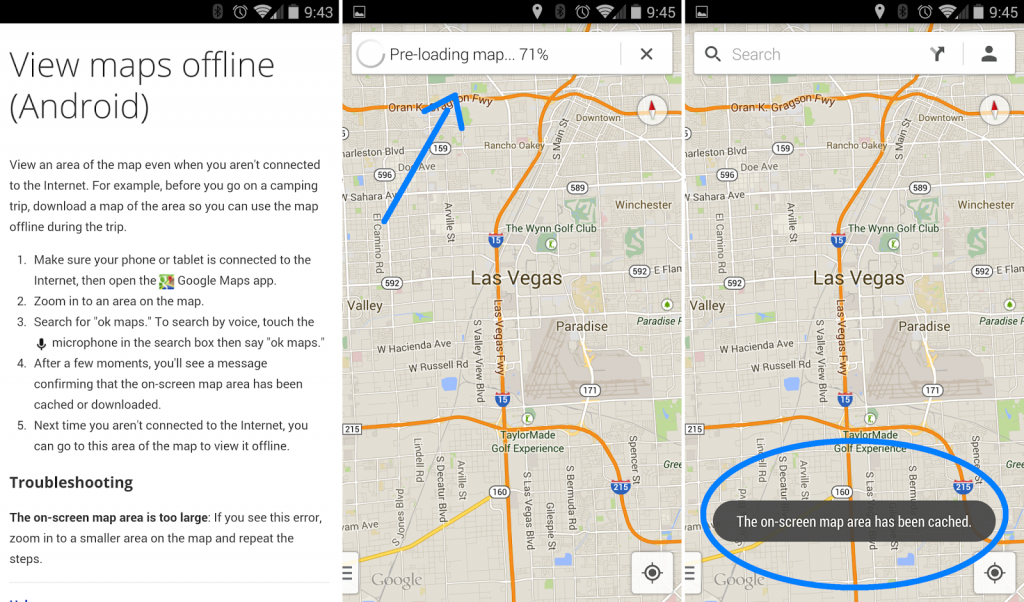
 188Android Hacking
188Android HackingHow to use Google Maps in Offline mode
The moment your phone reads “No service,” Google Maps suddenly drops out.That is, unless you’ve saved your maps for offline access. With...
-
 273Hacked
273HackedDangerous “Breaking Bad” Ransomware is Completely Undetected By Antivirus Products
Short Bytes: The recently discovered Breaking Bad ransomware remains undetected by the majority of the 57 security products listed on Google’s VirusTotal antivirus...
-

 126Vulnerabilities
126VulnerabilitiesStagefright 2.0 Vulnerabilities Affect 1 Billion Android Devices
When researcher Joshua Drake published details in August about critical Android vulnerabilities in the Stagefright media playback engine, he promised there would...
-

 165Data Security
165Data SecurityCar-Hacking Tool Turns Repair Shops Into Malware ‘Brothels’
the security research community has proven like never before that cars are vulnerable to hackers—via cellular Internet connections, intercepted smartphone signals, and...
-
 215Data Security
215Data SecurityRussian hackers tried to infiltrate Hillary Clinton’s home server
Hackers with links to Russia tried to infiltrate Hillary Rodham Clinton’s home e-mail server at least five times — even as other...
-
 154Data Security
154Data SecurityFBI: We unmasked and collared child porn creep on Tor with spy tool
Dark-web deadbeats may not be as anonymous as they think. A bloke in the US was charged on Friday after FBI spyware...
-
 307Geek
307GeekLearn to Code Windows 10 Apps: Microsoft’s Free Course for Beginners
Short Bytes: Microsoft has launched a free course to teach you how to code Windows 10 Universal Apps using C#. Take a...
-

 107Data Security
107Data SecurityCyber-Criminals Throw Molotov Cocktails at Dr.Web Antivirus Headquarters After Being Exposed
Cyber-crime syndicate tried to intimidate antivirus vendor. In some cases, cyber-security work can turn really dangerous, and even deadly, if you manage to...
-

 189Hacked
189HackedTesla Model X Has A Crazy Bio-weapon Defence Mode Button
Short Bytes: New Tesla Model X has a bio-weapon defense air mode that will give you a hospital level air quality inside...
-

 176Vulnerabilities
176VulnerabilitiesApple Gatekeeper Bypass Opens Door for Malicious Code
Gatekeeper is Mac OS X’s guardian against rogue applications and malware sneaking into Apple’s famous walled garden. It’s also been a favorite...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




