Featured News
-

 111Geek
111GeekMicrosoft Reconsiders Privacy Policy, Windows 10 Will Continue To Pull Data
Since the official public launch of Microsoft’s new operating system Windows 10 and the announcement of the company’s revised all-in-one privacy policy,...
-

 229Incidents
229Incidents15 million T-Mobile customers affected in Experian hack
SCHAUMBURG, Ill. — Credit-reporting agency Experian said on Thursday that hackers accessed the Social Security numbers, birthdates and other personal information belonging...
-

 274Hacked
274HackedHackers Release Gigabytes of Stolen Data From Patreon Donation Site
Short Bytes: Hackers have released potentially damaging 15GB worth of private data after attacking Patreon, a crowdfunding website for artists. On an...
-

 114Vulnerabilities
114VulnerabilitiesApple swiftly closes hole in iOS 9 Lock screen
Apple just released iOS 9.0.2. This new version claims to close the well-publicised Lock screen hole that lets anyone view and edit...
-
 100Vulnerabilities
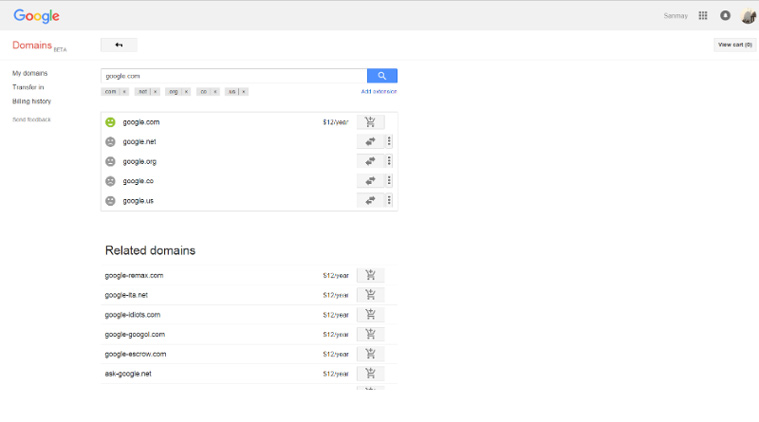
100VulnerabilitiesMeet Sanmay Ved, the Indian who owned Google.com for a minute
Ex-Googler Sanmay Ved was lucky enough to grab Google.com domain, but only for a minute. google.com purchase screen In a detailed post...
-
 190Android Hacking
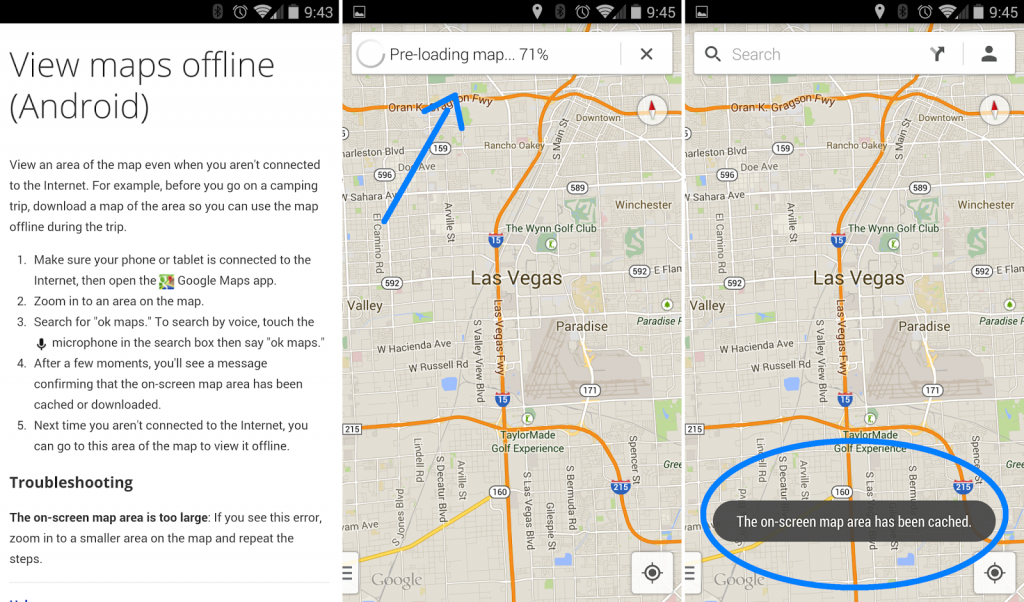
190Android HackingHow to use Google Maps in Offline mode
The moment your phone reads “No service,” Google Maps suddenly drops out.That is, unless you’ve saved your maps for offline access. With...
-
 276Hacked
276HackedDangerous “Breaking Bad” Ransomware is Completely Undetected By Antivirus Products
Short Bytes: The recently discovered Breaking Bad ransomware remains undetected by the majority of the 57 security products listed on Google’s VirusTotal antivirus...
-

 132Vulnerabilities
132VulnerabilitiesStagefright 2.0 Vulnerabilities Affect 1 Billion Android Devices
When researcher Joshua Drake published details in August about critical Android vulnerabilities in the Stagefright media playback engine, he promised there would...
-

 171Data Security
171Data SecurityCar-Hacking Tool Turns Repair Shops Into Malware ‘Brothels’
the security research community has proven like never before that cars are vulnerable to hackers—via cellular Internet connections, intercepted smartphone signals, and...
-
 219Data Security
219Data SecurityRussian hackers tried to infiltrate Hillary Clinton’s home server
Hackers with links to Russia tried to infiltrate Hillary Rodham Clinton’s home e-mail server at least five times — even as other...
-
 157Data Security
157Data SecurityFBI: We unmasked and collared child porn creep on Tor with spy tool
Dark-web deadbeats may not be as anonymous as they think. A bloke in the US was charged on Friday after FBI spyware...
-
 313Geek
313GeekLearn to Code Windows 10 Apps: Microsoft’s Free Course for Beginners
Short Bytes: Microsoft has launched a free course to teach you how to code Windows 10 Universal Apps using C#. Take a...
-

 111Data Security
111Data SecurityCyber-Criminals Throw Molotov Cocktails at Dr.Web Antivirus Headquarters After Being Exposed
Cyber-crime syndicate tried to intimidate antivirus vendor. In some cases, cyber-security work can turn really dangerous, and even deadly, if you manage to...
-

 193Hacked
193HackedTesla Model X Has A Crazy Bio-weapon Defence Mode Button
Short Bytes: New Tesla Model X has a bio-weapon defense air mode that will give you a hospital level air quality inside...
-

 178Vulnerabilities
178VulnerabilitiesApple Gatekeeper Bypass Opens Door for Malicious Code
Gatekeeper is Mac OS X’s guardian against rogue applications and malware sneaking into Apple’s famous walled garden. It’s also been a favorite...
-

 340News
340NewsDonald Trump Hotels Data Breach Incident Confirmed
In a previous article, we brought you news of Trump Hotels being breached by hackers. To update, we can now report that...
-

 359Geek
359GeekHow to Protect Your Wi-Fi Router From Hacking Using Simple Tricks
Short Bytes: The humble wireless router in your home, as you might not think, could be the biggest loophole in your personal...
-

 123Geek
123GeekDon’t Fall for Stupid Scam, Facebook Won’t Charge You any Privacy Fee
Last week, news spread across the web (appearing in newsfeeds of many users) that Facebook is about to assign a fee for...
-
 172Hacked
172HackedWinRAR Exposed to Dangerous Vulnerability: Attack Just by Unzipping Files
Short Bytes: The latest WinRAR SFX v5.21 update has a serious vulnerability that allows remote attackers to execute any malicious code on your...
-

 181Vulnerabilities
181VulnerabilitiesMicrosoft Exchange Server Fixed Against Information Disclosure Bug
Vulnerability allowed hackers to hijack active user sessions.Microsoft Exchange Server has been recently patched to fix an important security vulnerability which would...
The Latest
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment
-
 Data Security
Data SecurityHow Safe is Your TinyProxy? Step-by-Step Guide to Exploiting Tinyproxy’s Zero Day Vulnerability
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications




