Featured News
-
 364Geek
364GeekMicrosoft Releases Updates To Spy On Windows 7, 8 and 8.1 Users
Back at the beginning of this month, we reported that how Microsoft has planned to spy on its users by releasing their...
-

 232Kids Online
232Kids OnlineMake password into a story and more parental hacks
It’s important to ensure your child's data and devices are secure at school and at home. Check out our to back to...
-
 318Privacy
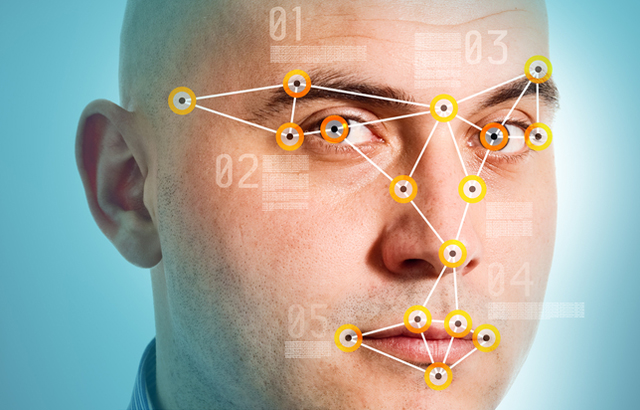
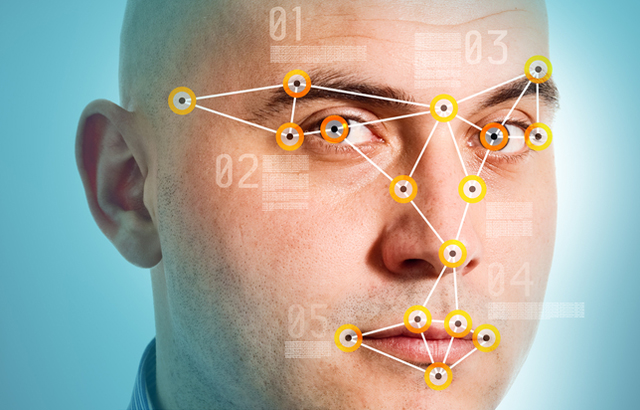
318PrivacyHow does facial recognition technology work?
In this hi-tech age, your face is increasingly becoming a digital ID for authenticating who you are online. We look at how...
-
 261Hacking Tutorials
261Hacking TutorialsReset Windows Password with Kali
Sometimes we forget our password, or even we want to reset the password of the windows OS of our friends, officemate or...
-

 318News
318NewsRoyal Saudi Air Force Website Hacked By Iranian Hackers
An Iranian hacker from Iran Hack Security Team hacked and defaced the official website of Royal Saudi Air Force this Friday morning. Though the...
-
 312Cyber Crime
312Cyber CrimeUniversity of Michigan Employees Trapped by Google Phishing Email
Around 150 University of Michigan employees lost sensitive information thanks to scammed emails, informs the university’s Division of Public Safety and Security....
-

 195Cyber Crime
195Cyber CrimeNew Amazon Phishing Scam Steals Credit Card Details
An email is being sent to users having the subject line ‘New Security feature’ and its sender appears to be Amazon. In...
-
 381How To
381How ToHere’s How to Use Microsoft Edge Without Installing Windows 10
Short Bytes: If you want to test Microsoft Edge without installing Windows 10 on your computer, here’s a good news for you....
-

 151Geek
151GeekWindows 10 Should be banned for Spying on Users – Demands Russia
After the release of Windows 10, we reported how the operating system spies on its users and how to disable selected features...
-

 420Geek
420GeekProtonMail is Now Open Source, iOS, Android Apps Unveiled
The world’s securest Switzerland based emailing service provider ProtonMail goes open source with the public release of their webmail interface version 2.0....
-

 407Hacked
407HackedRussians Demand Windows 10 Ban Because it “Spies on Users”
Short Bytes: Russian lawyers, lawmakers and state agencies have filed complaints seeking Windows 10 ban. They have claimed that Windows 10 OS...
-

 293Geek
293Geek4GB, 8GB Or 16GB; How Much RAM Do You Need?
Short Bytes: How much you should RAM: 4 GB, 8 GB or 16 GB? It’s one tricky choice that every computer buyer,...
-

 374Google Dorks
374Google DorksGoogle Dorks – Google Hacking
Google search engine find answer to our question which is helpful in our daily lives, search about our school assignments, reports, presentation and...
-

 341News
341NewsUK Based Recruitment Portal Suffers Massive Data Breach
A Saudi hacker going with the online handle of JM511 has breached into the server of a UK-based international network of independent...
-

 295Surveillance
295SurveillanceSpotify’s CEO Apologises For Collecting Private Data of its Users
Spotify wanted to collect everything that you don’t want to share with strangers and that includes your personal photos. The Internet is...
-

 173Kids Online
173Kids OnlineHow to nurture your child’s security genius
Is your child a security genius? If you think so, here’s what you can do to harness that potential for a career...
-
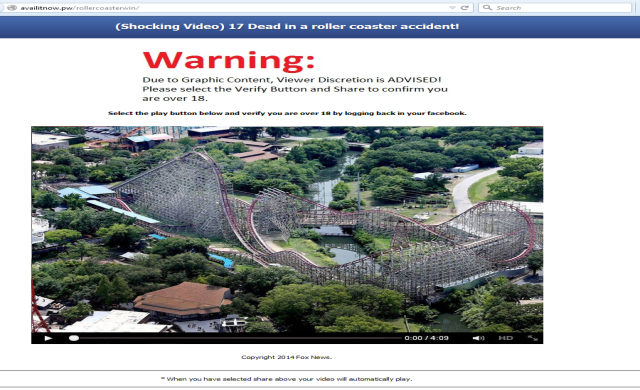
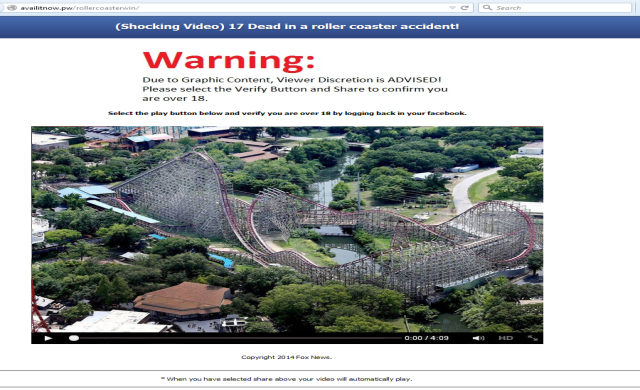 257Geek
257GeekFacebook Phishing Scam, ’17 dead in a roller coaster accident’
We just got to know that a new phishing scam has started to make rounds on the popular social media network, Facebook....
-

 329How To
329How ToHow to Fix Windows 10 Slow Performance Issue and Increase Overall System Speed
Short Bytes: Many Windows users are facing reduced performance issues in Windows 10. This appears in the form of input lags and could...
-

 292How To
292How ToHow to Boot and Install Kali Linux 2.0 with USB
In this tutorial we will teach you how to boot Kali Linux 2.0 in USB and Install it. Also Read: Download...
-

 288News
288NewsAnonymous Hacks South African Government Contractor for OpMonsanto
Remember the Anonymous hackers behind the massive World Trade Center (WTC) leak? Well, they are back with another breach. The online hacktivist...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




