Featured News
-

 83Cyber Crime
83Cyber CrimeTech giants take action on ad click fraud
Some of the biggest digital companies have banded together to take action on the rising tide of ad click fraud.
-
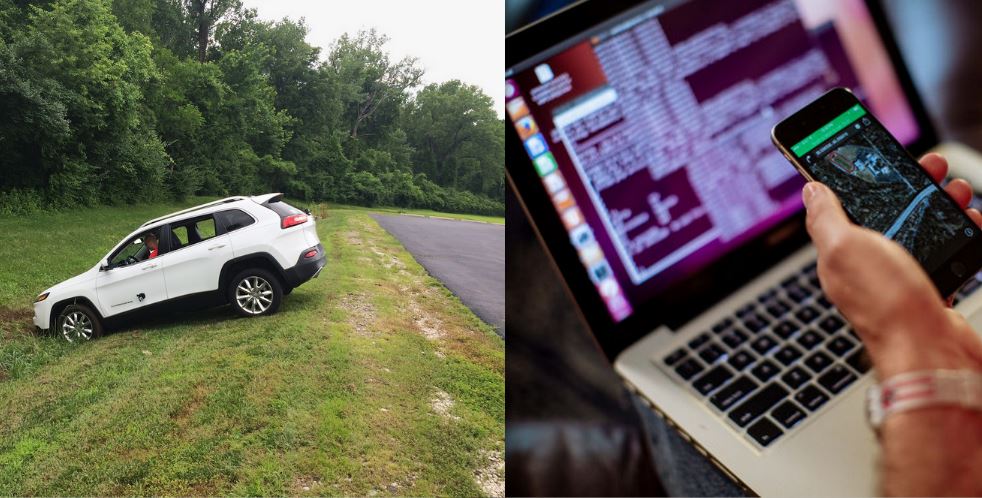
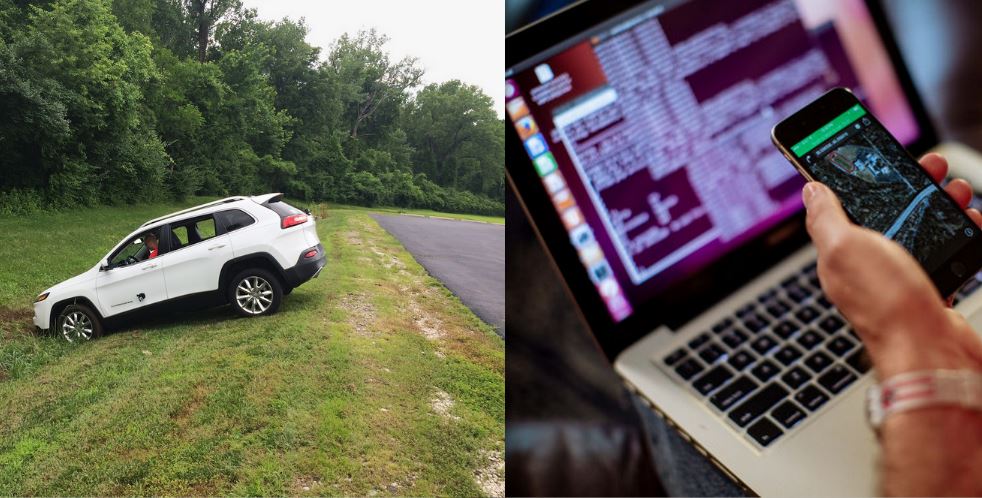 187Hacked
187HackedHackers Remotely Hacked This Car Running at 70mph on Highway
As our vehicles become smarter and more dependent on computers, the risk of a car hack automatically increases. Articles titled how to...
-

 104Privacy
104PrivacySmartwatch security ‘lacking’ says HP study
Smartwatch security is noticeably absent in most devices, leaving users at risk of cyberattacks.
-
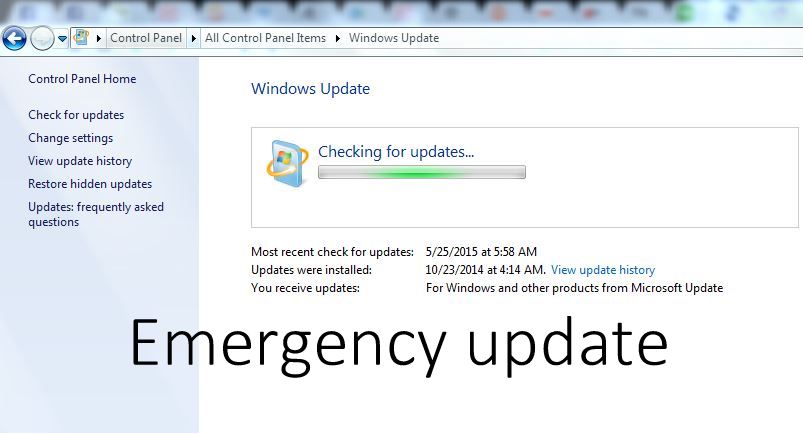
 188Hacked
188HackedDownload this Critical Windows Update Now, Flaw Allows Hackers to Control Entire System
A newly discovered vulnerability can allow hackers to remotely execute codes and take over your entire system. A user could be tricked...
-

 219Cyber Events
219Cyber EventsAnonymous Targets Canadian Police, Crashes RCMP’s Website
This week, on July 17th, there was a police-involved shooting in Dawson Creek, British Columbia Canada, where one of the members of...
-
 137How To
137How ToHow to turn night mode ON in Google Chrome
Google Chrome is the most used browser on the Internet as it is fast and secure. Google Chrome has many extensions in...
-
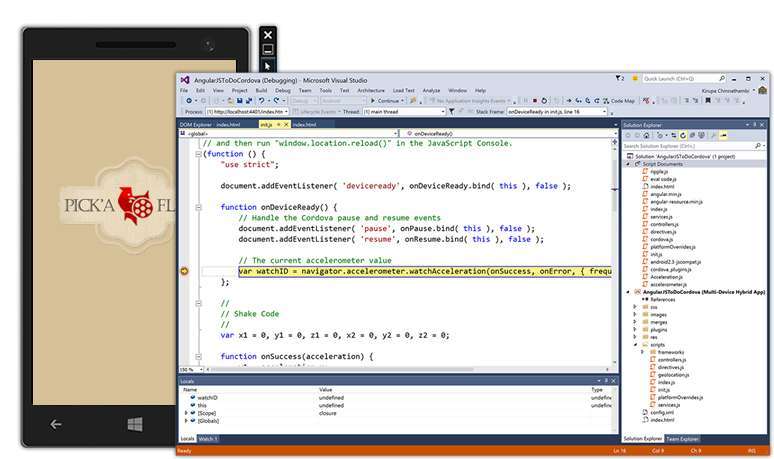
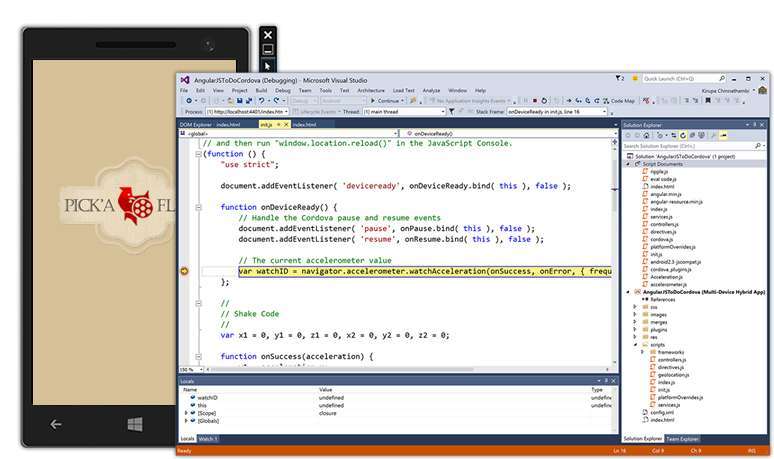 218Geek
218GeekVisual Studio 2015 and .NET 4.6 Released, Download Now
Today is the Visual Studio 2015 and .NET 4.6 release day. These software from the house of Microsoft have finally graduated exiting...
-

 218News
218NewsHacknet , a real Hacking game.
Developed by Team Fractal Alligator, an Australian one-man studio, Hacknet is “an immersive, terminal-based hacking simulator for PC.” Here’s the official...
-

 131Scams
131ScamsMicrosoft advises ‘spoofed’ Skype users to change passwords
Skype users have been advised by Microsoft to change their passwords following reports that 'spoofed' messages are being sent without user permission.
-

 184Hacked
184HackedInstagram Can Totally Hijack Your Account And Give To Some Celebrity
How cool would it be if somehow your parents were Pitt’s and ended up to name you Brad, or a simple Messi...
-

 103Cyber Crime
103Cyber Crime37 million relationship cheats could be exposed by Ashley Madison hack
The 37 million users of hacked infidelity site Ashley Madison are at risk of having their names and private details leaked, reports...
-
 387Hacked
387HackedMicrosoft: Free Windows 10 Upgrade Comes With 10 Years of Free Updates
Windows 10 is one of most talked about topics on various online forums. Microsoft is leaving no stone unturned to achieve its...
-
 266Hacked
266Hacked37 Million Adulterers Exposed, Online “Cheating” Site Ashley Madison Hacked
Online cheating website AshleyMadison.com has been hacked, and as a result, large chunks of data has been stolen. The compromised data has...
-
 197Hacked
197HackedCyberGhost Privacy Accelerator Program Offers €100,000 if You Can Make Web a Secure Place
“How Government secretly read your e-mails with this insane law?“ “Snowden’s Revelations: XKEYSCORE is NSA’s search engine.” “Real-Time Cyber Attacks across the globe. ““NSA’s...
-

 279Geek
279GeekTop Netflix Open Source Projects You Must Know
This is the 3rd post in the series covering top open source projects by most popular companies in the world. Today, we...
-
 331News
331NewsCyberwar: Pakistani President’s Website Hacked by Bangladeshi Hackers
Pakistani President Mamnoon Hussain’s website has been hacked by Bangladeshi hackers — 72 other Pakistani government websites have been hacked as well....
-

 231Data Security
231Data SecurityWindows XP Anti-Malware Support Terminated – 180 Million Users Left Vulnerable
Millions of Windows XP users are now left vulnerable to malware attacks as Microsoft has decided to terminate support and security updates...
-

 313Hacked
313HackedThis Hacked Gun Mounted Drone Shoots Bullet in Terrifying Video
The world is getting scarier each day. And I don’t mean the terrorist attacks or cyber threats or global warming, or least...
-
 341Hacked
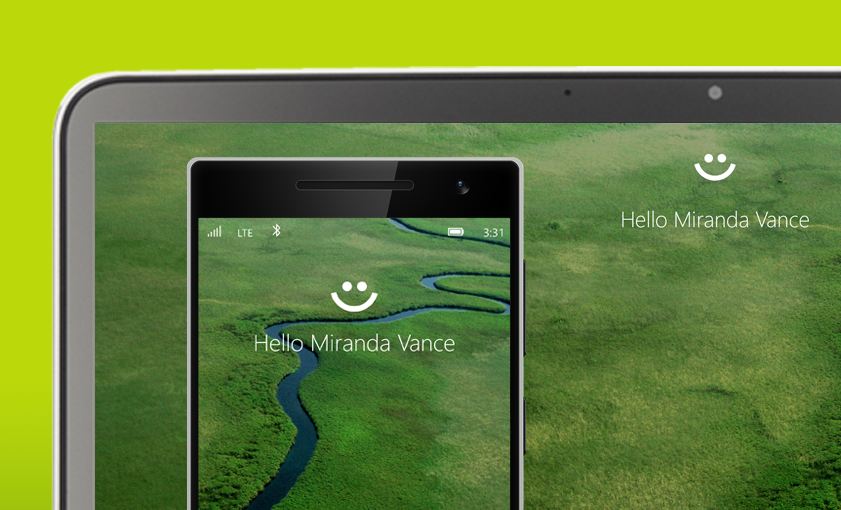
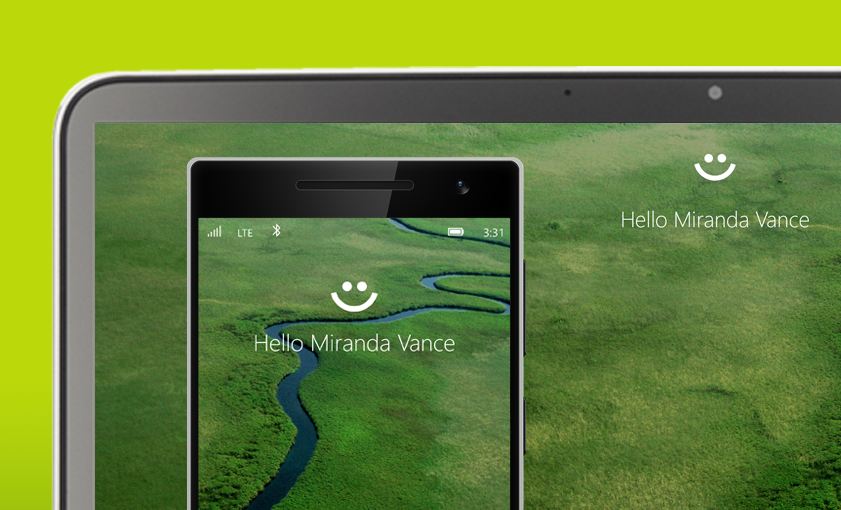
341HackedComplete List of PCs Supporting Windows Hello, the Password Killer Feature of Windows 10
With Windows 10’s Windows Hello feature, you will be able to log into your PCs without any password. Windows Hello users to...
-

 272Geek
272GeekMicrosoft Now Providing Support for Linux Users in Azure
Microsoft Azure cloud platform is very popular among Linux users and now Microsoft has announced that it will be offering limited support...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




