Featured News
-
 115Geek
115GeekExclusive: Minds Founder Talks Transparency, Security, Anonymous and Evolution
Remember those rumors about Anonymous hacktivists creating their own social media? Well, they aren’t! However, some privacy advocates are indeed working on a...
-

 165News
165NewsWikiLeaks Exposes NSA’s Addiction of Eavesdropping on Its Friends
A new assortment of documents have been released by WikiLeaks revealing National Security Agency has been spying on its German associates who are...
-

 300Geek
300GeekGoogle Image Recognition Software Tags Black Couple as Gorillas
Google Apologizes after its Image Recognition Software Mistakenly Tags Black couple as Gorillas. A computer programmer Jacky Alcine saw his and a...
-

 219News
219NewsDonald Trump Hotels Face Major Credit Card Breach as Hackers Target the Empire
The meltdown of Donald Trump’s empire is slowly but continuously gaining momentum and the latest to add more misery to the real...
-

 228Courses & Ebooks
228Courses & EbooksA Guide to become an Ethical Hacker
A person who hacks into a computer network in order to test or evaluate its security, rather than with malicious or criminal...
-

 77Cyber Crime
77Cyber CrimePCI Council updates encryption standards
A key update to the PCI standard has been issued by the PCI standards body, the Payment Card Industry Security Standards Council...
-

 292Hacked
292HackedRaspberry Pi Based Device Provides Anonymous WiFi, Puts You 2.5 Miles Away from Your IP Address
If you are well-informed about the basics of online security and anonymity, then you would be aware of the importance of IP...
-

 65Cyber Crime
65Cyber CrimeThe 6 biggest online gaming hacks
We Live Security looks at six of the biggest online gaming hacks to date – From Xbox Live and PSN, to Big...
-

 80How To
80How ToProtect your Pendrive with Password
Everyone now a days has one or two additional pendrives and hard disks with them because pendrive makes sharing of data very...
-
 243News
243NewsArmenian Hackers Leak ID Cards, Passports of 5k Azerbaijani Citizens
The cyber war between Armenians and Azerbaijani hackers is never ending. Just like today when Armenian hackers leaked trove of data containing personal...
-

 136How To
136How ToGet A Refund on Google Play Store Apps
Every Android mobile has Google Play Store pre-installed on its device. Play Store is an awesome market to download some awesome applications...
-
 296Geek
296GeekMicrosoft Joins the Linux Foundation’s R Consortium Along With Others
Today the Linux Foundation announced a new initiative called R Consortium- a group to unite the users of the open-source R programming...
-
 226Data Security
226Data SecurityDino Malware exposed: Found Spying on Iran and Syria
Links traced to “Animal Farm” group and State Sponsored cyber criminals who already have targeted Syrian and Iranian computers in 2013. Bratislava,...
-
 130How To
130How ToConvert your Facebook profile into a Page
Facebook is the number one social networking website with more than one billion active users. All of us have a Facebook profile...
-
 349How To
349How ToHow To Access Computer’s Hard Drive With Smartphone
Yes, you heard that right. You can access your computer’s hard drive with your smartphone in few simple steps. For this, you...
-

 105Privacy
105PrivacyEastern England councils in slew of data breach errors
A series of more than 160 data breaches have struck local authorities in Norfolk, Suffolk and Cambridgeshire over the past year, according...
-
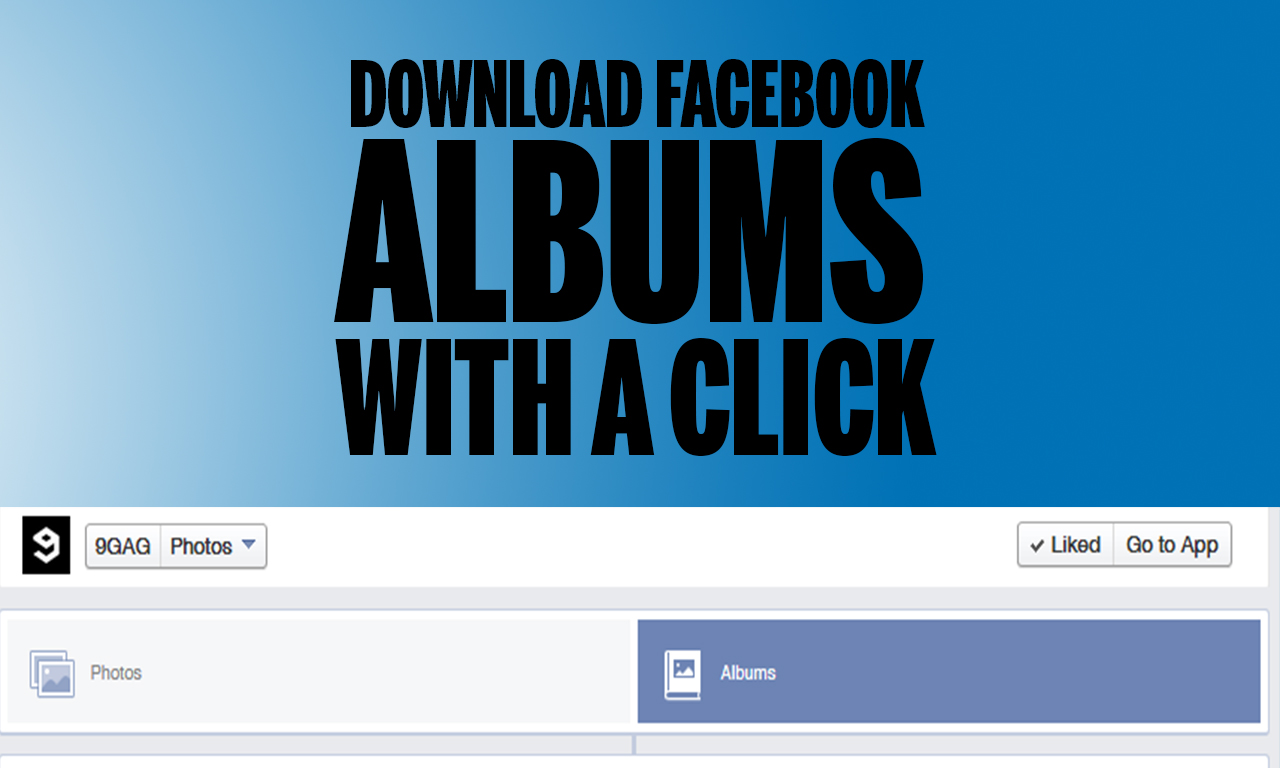
 120How To
120How ToDownload whole photo album on Facebook with a single click
Facebook is the No.1 Social Networking website with more than 1.2 Billion active users. Everyone posts images on FB. Whenever we surf...
-

 206Tricks & How To's
206Tricks & How To'sDownload Torrents with IDM
There may be many reasons to download torrent files using IDM. It may be that you get good speed using IDM, no...
-

 329Hacked
329HackedBad News: NSA Resuming US Mass Surveillance for Another 6 Months
If you were busy celebrating the fact that the Patriot Act will bring an end to NSA’s mass surveillance, you should take...
-

 257Cyber Events
257Cyber EventsAnonymous Shuts Down Canada Spy Agency Website
The online hacktivist Anonymous conducted a massive DDoS attack on the official website of Canadian Security Intelligence Service (CSIS) and forced it to go...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




