Featured News
-

 215Data Security
215Data SecurityAny iPhone, iPad Within Wi-Fi Range can be Crashed due to Security Flaw
Researchers at the RSA conference explained about a newly found vulnerability that allows attackers to crash just about any iOS device. San...
-

 122Mobile Security
122Mobile SecuritySamsung Galaxy S5 could be open to fingerprint theft
The Samsung Galaxy S5 and other 'unnamed Android devices' are vulnerable to having the fingerprints they use for authentication cloned by hackers,...
-
 81Cyber Crime
81Cyber CrimeRansomware: Should you pay the cybercriminals?
If your files are encrypted by ransomware, should you pay the ransom? We examine the options...
-

 186Surveillance
186SurveillanceVoices from hacked Baby monitor tells child to “stay in bed”
A Lacey, (Washington) resident claims that another woman’s voice was heard from her son’s baby monitor while he was taking a nap....
-

 308Cyber Events
308Cyber EventsDept of Homeland Security to Open Cyber Security Office in Silicon Valley
According to U.S. Secretary of Homeland Security Mr. Jeh Johnson, the department will be opening a Cybersecurity related Satellite office in Silicon Valley. Jeh...
-
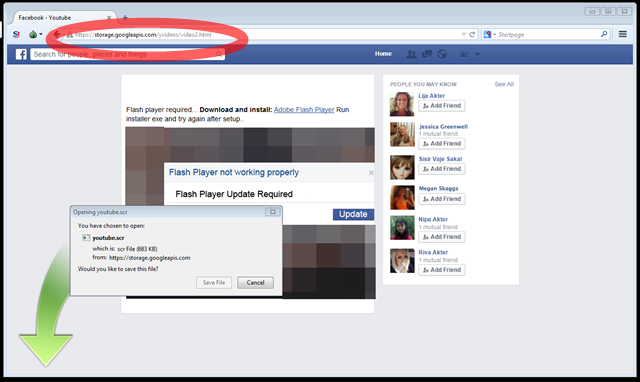
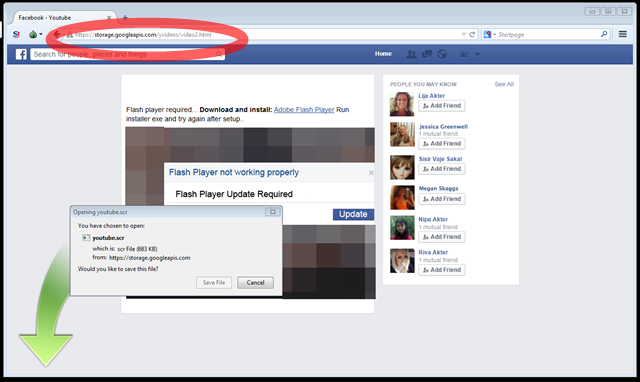 324Data Security
324Data SecurityFacebook users hit with “Hot Video” scam, delivering Trojan
A fake Facebook interface will display an attractive looking “Hot Video” link. If you hit Play button, you will be requested to...
-

 111Privacy
111PrivacyHackers spy on Kansas family through unsecured baby monitor
A Kansas family are the latest victims of a hacked nanny cam, after noticing the device purchased to monitor their three-month-old baby...
-
 314Data Security
314Data Security2500+ GTA V PC Accounts Rumored to be hacked but Rockstar Denies
Grand Theft Auto 5’s hub Rockstar Social Club was rumored to have been hacked. In reality, it is safe and another unnamed site...
-
 187Geek
187Geek10 Best Features in Ubuntu 15.04, Favorite Platform of Developers
This year’s first Ubuntu release – Ubuntu 15.04 – is being loved by all. Ubuntu is the favorite platform of developers and it...
-
Secure Coding
How to create a keylogger in notepad
Here is a basic keylogger script for beginners to understand the basics of how keylogging works in notepad. This script should be...
-

 68Cyber Crime
68Cyber CrimeCanada commits $36.4 million to cybersecurity measures in 2015 budget
The Conservatives' 2015-16 federal budget sees some investment in security, with $36.4 million promised over five years to address cybersecurity threats.
-
 203How To
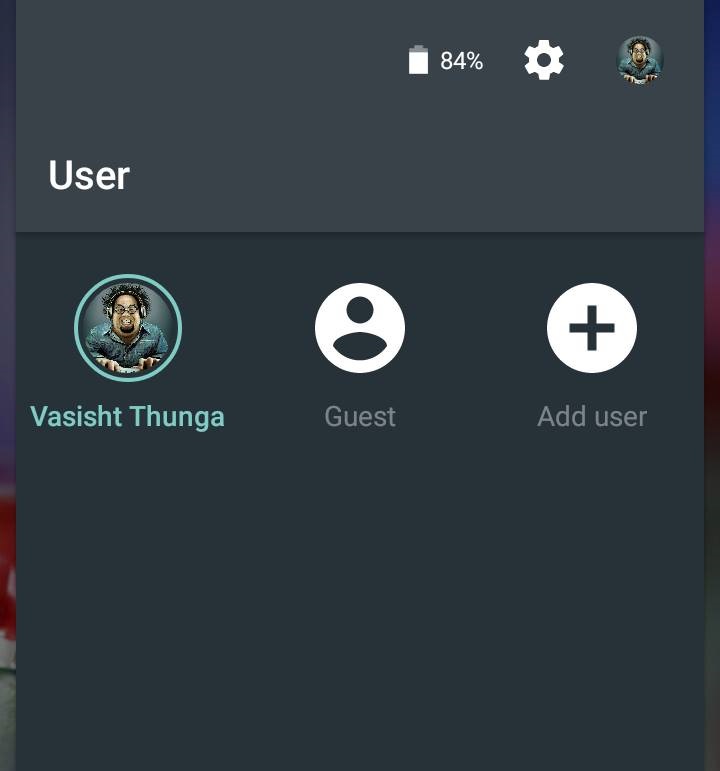
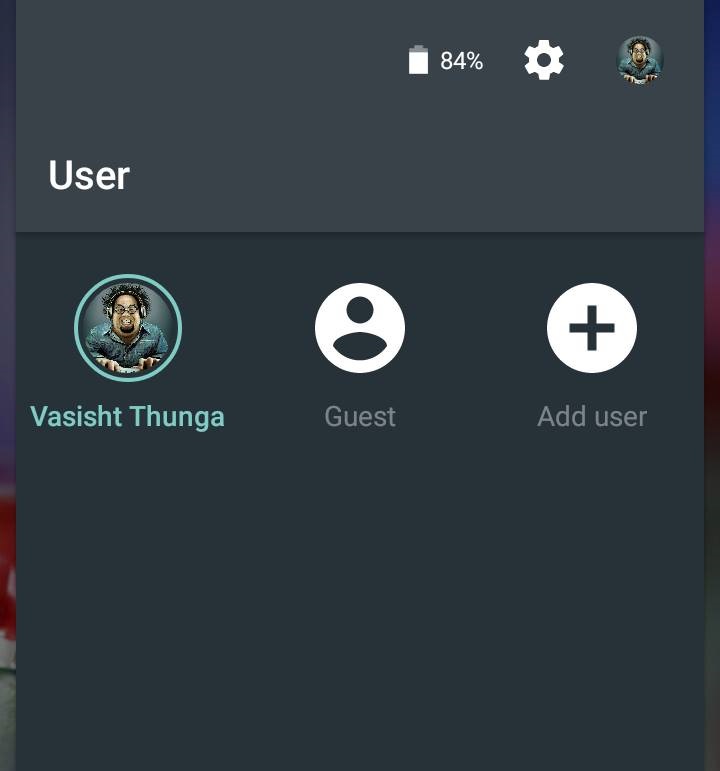
203How ToHow To Enable Guest Mode On Android
Android 5.0 Lollipop lets you quickly switch to a separate guest profile. This guest user will not contain your personal data like...
-
 123Data Security
123Data SecuritySerious Security Flaw found in 1,500 iOS apps—Checkout if your iPhone is at risk
Researchers have identified a serious vulnerability in at least 1,500 iOS apps. This security flaw has made the apps exploitable by hackers...
-
 258Cyber Events
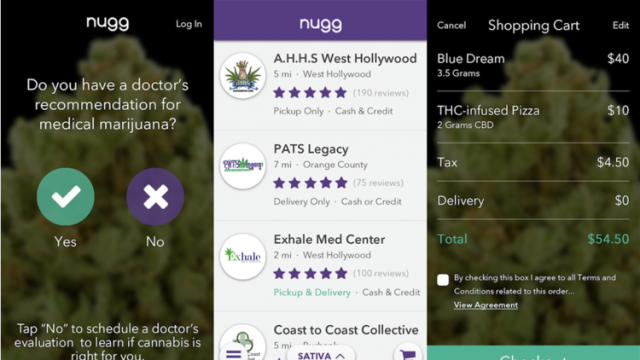
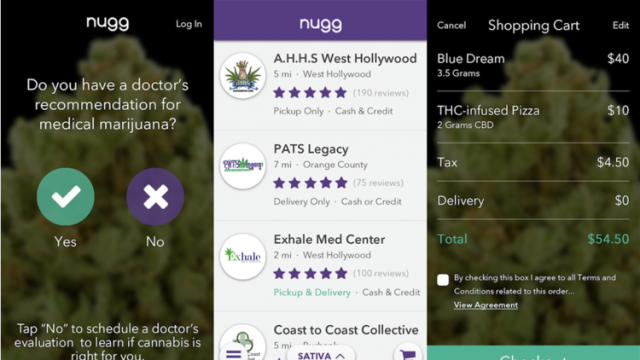
258Cyber EventsNugg App Lets You Order Medical Marijuana From Your Smartphone
Los Angeles and Orange Counties patients could order medical marijuana through Nugg, a new app. They may even schedule marijuana deliveries and...
-

 118Geek
118GeekWoman Suing Google For Losing “thousands” due to Google Play Store hack
Susan Harvey claims Google never reimbursed her even after admitting that she did not make the purchases. Madera, CA-based woman Susan Harvey...
-

 433Privacy
433PrivacyThe dirty secrets of webcam‑hacking peeping toms and sextortionists
Virtually every computer sold today comes with a dirty little secret. It can spy on you. Learn more, and how to protect...
-
 213Hacked
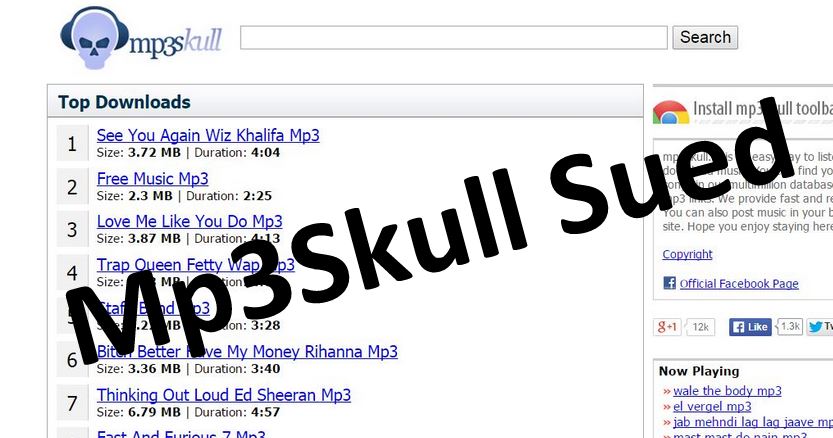
213HackedMP3 Download Website MP3Skull Being Sued Over Mass Piracy
MP3Skull is one of the most popular websites being used by people to download music illegally. TF reports that in a combined...
-

 415Malware
415MalwareNew malware ‘Punkey’ detected in new point‑of‑sale attack
A new advanced malware program targeting point-of-sale terminals is putting customer credit card details at risk, following a number of similar attacks...
-

 337Data Security
337Data SecurityXSS Vulnerability Found in Famous WordPress Plugins
Researchers have identified a relatively “common” cross-site scripting flaw (XSS) in some famous WordPress plugins — A coordinated plugin update has been released to...
-

 278Hacked
278HackedHow New Zealand and NSA Plotted Hack on China
China’s foreign ministry has expressed serious concerns over the reports of hacking attacks on China planned by New Zealand and NSA in recent...
The Latest
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
-
 Malware
MalwareNSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
-
 Vulnerabilities
VulnerabilitiesFour Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Vulnerabilities
VulnerabilitiesWhen is One Vulnerability Scanner Not Enough?
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Vulnerabilities
VulnerabilitiesNew “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024




