Featured News
-

 237Social Media
237Social MediaEaster Social Media Safety: video guides
Despite the holiday season though, you can't guarantee that hackers and cybercriminals won't be on the hunt for weak and vulnerable social...
-
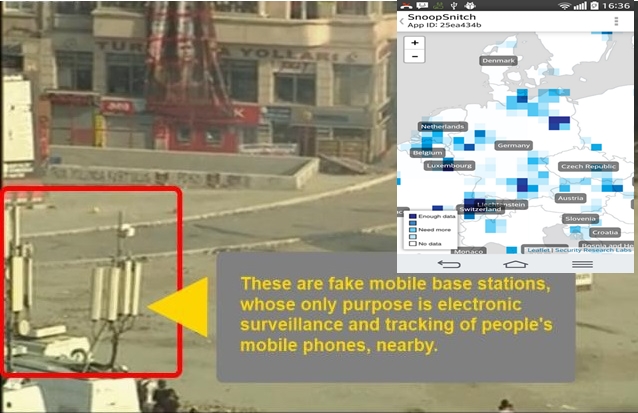
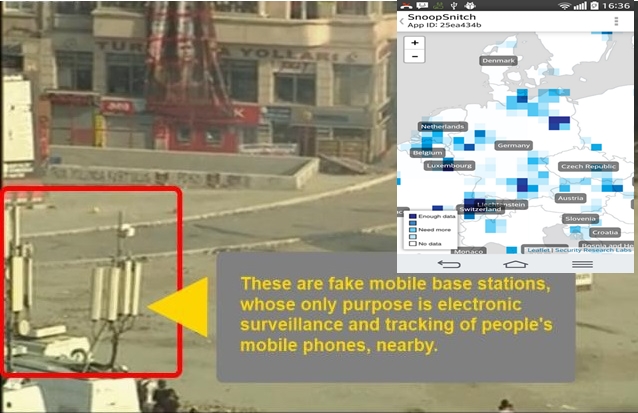 341Surveillance
341SurveillanceSnoopSnitch — An App That Detects Govt’s Stingray Mobile Trackers
Last week we reported on the Overwatch service that pinpoints every fake cell tower spying and tracking your smartphone. Now we present an...
-
 279Data Security
279Data SecurityHow You CAN Delete Almost any video on YouTube
Recently Google announced its current experimental program named Vulnerability Research Grants (VRG). No doubt it is a great concept. In this program...
-

 276Geek
276GeekBiohackers Identified the Way to Transform your Eyes into Night Vision Goggles
Biohackers Identified the Way to Transform your Eyes into Night Vision Goggles — It requires injecting your eye balls with a chemical...
-
 300Cyber Events
300Cyber EventsAnonymous Reveals 26,000+ Twitter Handles Allegedly having Links with ISIS
Anonymous hacktivist group continues its efforts to expose social media profiles of the notorious rebel group Islamic State of Iraq and Syria/ISIS militants...
-
 294Geek
294GeekGoogle Code Jam 2015: Here’s Everything You Should Know to Participate
ATTENTION!! Programmers, coders and hackers, students and professionals, techies and newbies – GEAR UP!! The countdown to one of the biggest programming...
-

 275Hacked
275HackedThe Pirate Bay Going for Its Own .PIRATE Domain Name
The Pirate Bay has been facing extreme pressure from the Hollywood and music industry backed domain name industry. In recent times, The...
-

 437Scams
437ScamsSEO Scams and Semi‑Scams
Search Engine Optimization: it's an essential component of internet marketing strategy, I guess, but one with a bad public image, especially in...
-

 361Malware
361MalwareEnergy companies hit with new data‑stealing malware
Energy companies have been targeted with a new multi-stage malware attack used to infect company computers and steal sensitive data.
-

 113Password
113PasswordInfographic: Alternatives to the password
The humble password has struggled in recent years, and is often seen as vulnerable to attackers. The interactive infographic below offers up...
-

 319Surveillance
319SurveillanceAdiós GPS: DARPA Working on Alternative Position Tracking Technology
Good Bye GPS — DARPA to present another position-tracking technology. The U.S government’s Defence Advanced Research Projects Agency (DARPA) has prioritized the development...
-
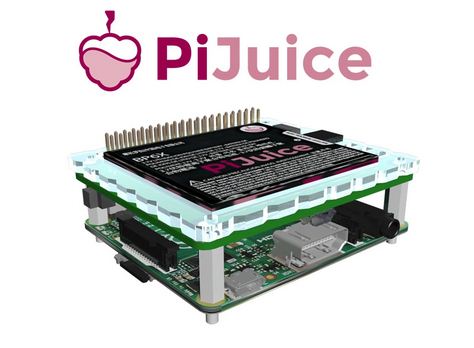
 285Geek
285GeekMeet PiJuice- The Ultimate Module For Portable Raspberry Pi Projects
Think Do-It-Yourself Computing, Think Raspberry Pi! Such a phenomenon this mini-computer has been! From the Pandora’s Box of Projects that is Kickstarter...
-

 188Geek
188GeekResearchers Find Technique to Bypass iPhone Lockscreen
Researchers at MDSec, an IT security firm, have identified a method that allows thieves and hackers to bypass iPhone’s lockscreen utilizing equipment...
-

 272Cyber Crime
272Cyber Crime‘Payment Reversal’ Another PayPal Phishing Scam Targeting Customers
A new email that has been targeting PayPal users states that the company is examining a payment reversal regarding Apple and user’s...
-

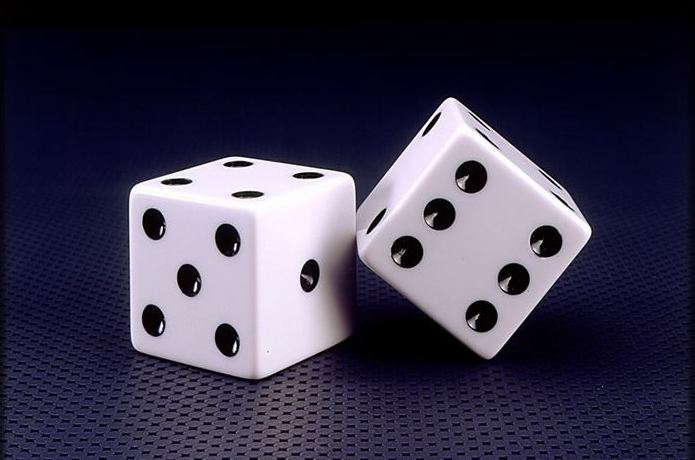
 75Cyber Crime
75Cyber CrimeRetailers’ heavy handed fraud prevention leads to loss of sales
Online retailers battling with fraud prevention are losing out on genuine sales by treating their customers like criminals, according to a new...
-

 154How To
154How ToSix ways to backup your data
Today is World Backup Day, and it goes without saying that backing up data is a thoroughly sensible thing to routinely get...
-

 97Privacy
97PrivacyQueen Elizabeth consults with cybersecurity expert over privacy fears
Queen Elizabeth has been consulting one of the United Kingdom's most prominent cybersecurity experts, leading to speculation the Royal Family may be...
-
 345Hacked
345HackedCreate Uncrackable Passphrases that Even NSA Can’t Crack
Did thinking the most secure password takes out the best of you?? And, still, it seems that it is not sufficient. Your first...
-

 214How To
214How ToMicrosoft Finally Releases Spartan Browser, Here’s How to Get It
Microsoft has finally rolled out the Spartan browser as an official release. This is one of the most anticipated features of Windows...
-

 294Cyber Events
294Cyber EventsOp_Israel: Anonymous Threatens Israel with ‘Electronic Holocaust’
In a latest video footage from Anonymous, the notorious hacker group, a masked individual appears in a suit and delivers a well-structured...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




