Featured News
-

 264Data Security
264Data SecurityHere is a list of URLs used by the NSA to install malware on PCs worldwide
Last month security researchers discovered an undetectable malware installed in the hard drives by the American National Security Agency (NSA) to spy...
-

 319Cyber Crime
319Cyber CrimeFamous Games Hijacked for Ransom Through TeslaCrypt Ransomware
Files of over 20 Games Encrypted by TeslaCrypt Ransomware – Out of 185, 50 file extensions are game-oriented. TeslaCrypt is a crypto-ransomware that...
-
 227Data Security
227Data SecurityBEWRE: Worm Being Spread via Facebook
Facebook users, if you have clicked the Ow.ly link (URL shortening service) then you might have gotten your computers infected by a worm. The link is being...
-
 343How To
343How ToHow to Enable Hidden Offline Browsing In Google Chrome
Hello everyone, I remember the last time when I shared an article on How To Watch and Download YouTube Videos Offline, someone asked me if I...
-

 267News
267NewsSony PlayStation User Accounts are Getting Hacked, Change Your Password
Do you use Sony PlayStation? Do you purchase related products or gaming content from Sony’s online store? Well, if you do we warn you...
-

 301Geek
301GeekSmart Davek Umbrella when Lost send Alerts to its owner
A New York based accessories company Davek claims to have made the “strongest, most high-quality umbrellas” and now it took to Kickstarter...
-

 333Cyber Events
333Cyber EventsSelfie Psycho: Paramedic Fired for Taking Pictures with Dying Patients
Selfie Mania Turning People Psychic-Reportedly, a Russian paramedic is fired for taking pictures with Dying patients. Paramedic staff is believed to be...
-

 88Geek
88GeekFacebook To Face Class Action Court Case Over Unrefunded Purchases Made by Kids
Facebook is in the news again but this time for all the wrong reasons. Reportedly, the social networking giant will be defending...
-

 331Surveillance
331SurveillanceManaging Insider Threats with Internal Monitoring
The number of annual security incidents caused by insider threats is increasing. InThe CERT Guide to Insider Threats, Capelli et al write,...
-

 87Cyber Crime
87Cyber CrimeWomen in Federal cybersecurity – How did they get their start?
While there may still be only a handful of women in Information Security, they can be found in increasing numbers in important,...
-

 332Data Security
332Data SecurityBeware– This Killer USB Drive Can Fry Your Laptop
The killer USB Drive has been designed especially to burn laptops – So be careful while inserting someone’s USB on your laptop. Have you heard...
-

 153Cyber Crime
153Cyber CrimeObama administration seeks more power to tackle botnets
The Obama administration wants greater power to shut down botnets, responding to the growing threat of cybercrime and increasingly complex, modern techniques.
-

 100Password
100PasswordBritish Bank trials heartbeat based authentication
A British bank has been trialling a different type of biometrics, allowing their customers to confirm their identity via heartbeat according to...
-

 150How To
150How ToHeimdal blog, 19 Experts, 50+ Security Tips
Heimdal asked a range of security experts for their essential security tips. 19 experts (including David Harley) offered over 50 tips.
-

 504Windows
504WindowsWill Windows 10 leave enterprises vulnerable to zero‑days?
One thing Microsoft has been very public about is Windows 10's new strategy of releasing patches to update the operating system at...
-
 286Cyber Events
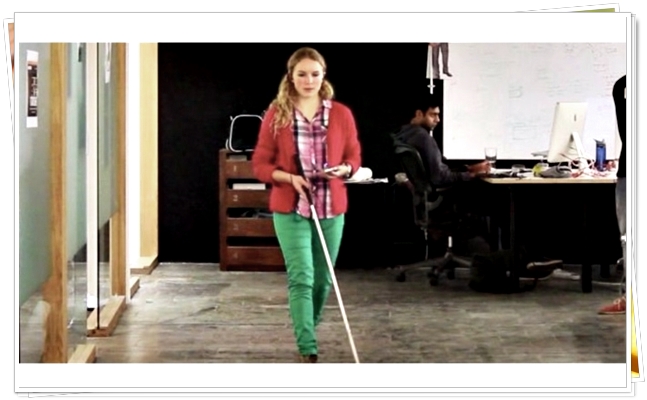
286Cyber EventsAn App that Helps Blind People Traverse London’s Tube via Sound
One of London’s tube stations will become more accessible for vision impaired and blind travelers by an amazing new Bluetooth setup. According...
-

 302Geek
302GeekDubai Police: Using VPN in United Arab Emirates is a Punishable Crime
Using VPN is a crime under UAE’s cyber laws – Anyone found using VPN can be charged for going against the country’s...
-

 185Surveillance
185SurveillanceU.S. Senate Rushing to Move Cyber-Surveillance CISA Bill Amid NSA Spying
The controversial cybersecurity legislation Cybersecurity Information Sharing Act (CISA) will be passed by the Senate Intelligence Committee on Thursday, said the panel’s...
-
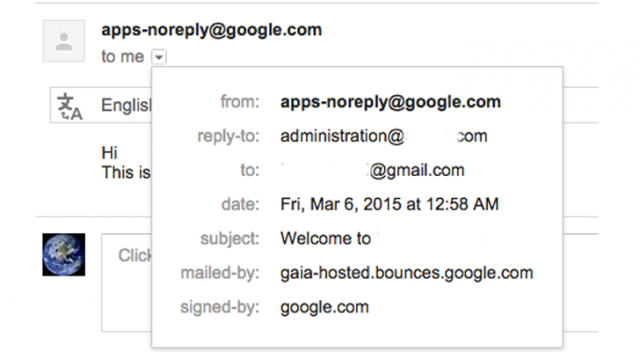
 284Data Security
284Data SecurityCybercriminals Abusing Vulnerability in Google Apps to Send Phishing Emails
It has been found that hackers can now easily abuse any website’s domain name based email addresses through the Google Apps for...
-

 114Privacy
114PrivacyThe immortality of data (and people) in the digital age
In the future, everything around us will be managed by data, and those who have data will have power. So, will anonymity...
The Latest
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
-
 Malware
MalwareNSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
-
 Vulnerabilities
VulnerabilitiesFour Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Vulnerabilities
VulnerabilitiesWhen is One Vulnerability Scanner Not Enough?
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Vulnerabilities
VulnerabilitiesNew “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024




