Featured News
-
 227Android Hacking
227Android HackingHow to bypass Android Lockscreen
Today i’m going to show you guys how to bypass android lockscreen using two methods. Method 1 What you need: Windows or...
-

 88Malware
88MalwareStealthy malware uses Gmail drafts to steal data
A new strain of malware that uses Gmail drafts in an invisible Internet Explorer window, has been discovered. According to Network World,...
-

 153Privacy
153PrivacyWearable tech and security – can watches help?
So far, wearable tech has been of interest mainly to fitness fiends - but a new generation of hi-tech wearables comes armed...
-

 266Geek
266GeekUbuntu 14.10 Released and Available for Download Here
On 26 October 2014 , Canonical marked the 10th anniversary of an OS that has revolutionized Linux – Ubuntu . And there...
-

 102Mobile Security
102Mobile Security‘Find My Mobile’ system can be used to attack Samsung handsets
One of the most popular and useful security functions of mobile handsets can be turned against the owner.
-
 207Cyber Crime
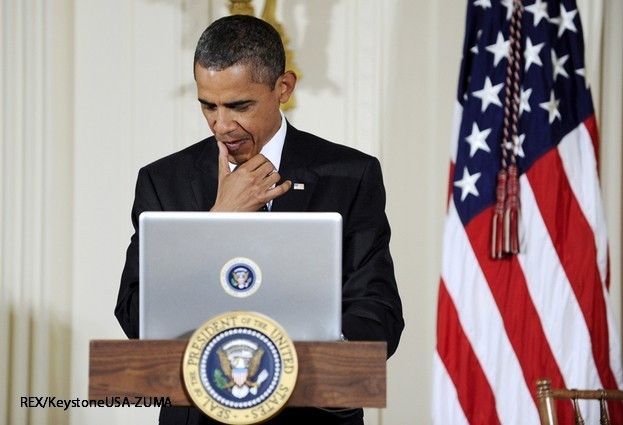
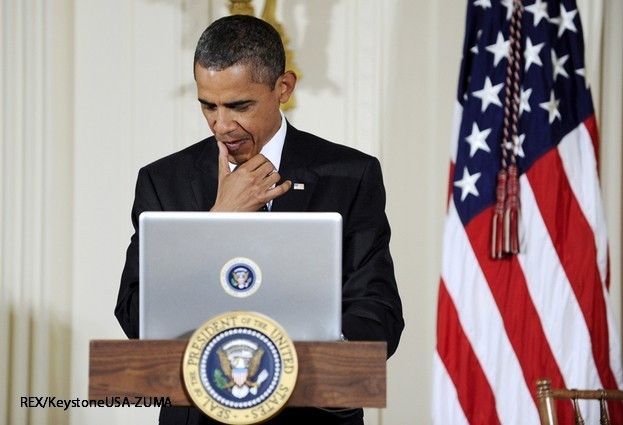
207Cyber CrimeWhite House hit by “sustained” cyber attack, hackers breach unclassified network
IT security staff have spent the last few weeks fighting hackers in the White House, after a computer network was breached. But...
-

 116Mobile Security
116Mobile SecurityGoogle outlines new security features in Android 5.0
Google has outlined the enhanced security credentials of the upcoming Android 5.0 - nicknamed Lollipop - in an official blog post.
-

 158Surveillance
158SurveillanceThis Camera-Covered Jacket Is Best Surveillance Tool To Record/Report Crime
Street crimes? not a problem now! With the newly designed jackets one can easily track down thieves and alert the respective authorities....
-

 218Tricks & How To's
218Tricks & How To'sRemotely shutdown computers
Note* For this to work you must be connected on the same network as the victim’s computer 1) Right-click on your desktop....
-

 315Information Gathering
315Information GatheringHow to get someones IP from facebook
When you’re talking with someone over chat, make sure your messages also notify you via email. Once someone sends a message and...
-

 166Privacy
166PrivacyBritish job centers to introduce biometric recognition
Job centers across the United Kingdom are due to get a technological makeover, courtesy of biometric and signature recognition pads, reports IT...
-

 303Information Gathering
303Information GatheringHow to find the IP of a Skype user
1.Log onto the computer as the “Administrator.” Go to “Start” > “Search.” 2.Enter “cmd” into the “Search” box. Press “Enter.” 3.Go to...
-

 94How To
94How ToHow do open source tools stay secure?
Security of open source code is a hot topic, what with Heartbleed, Shellshock, and Poodle making the news. Open source code is...
-

 93Cyber Crime
93Cyber Crime42% of Americans hit by regular online attacks
A study by Microsoft has revealed that 42 percent of Americans face 'weekly or daily' attacks by cybercriminals trying to access their...
-

 98Malware
98MalwareTor users targeted with exit node malware
An exit node on the Tor network has been discovered to be slipping malware on top of downloads, according to The Register....
-

 83Cyber Crime
83Cyber CrimeInternet trolls – how to deal with online abuse
Most internet users have faced some kind of problems with internet trolls - and a new study has thrown light on who...
-

 213News
213NewsIranian Hacker Defaces Website of UAE’s Telecom Regulatory Authority
An Iranian hacker going with the handle of MoHaMaD VaKeR hacked and defaced the official sub-domain ofTelecommunications Regulatory Authority (TRA) of United...
-
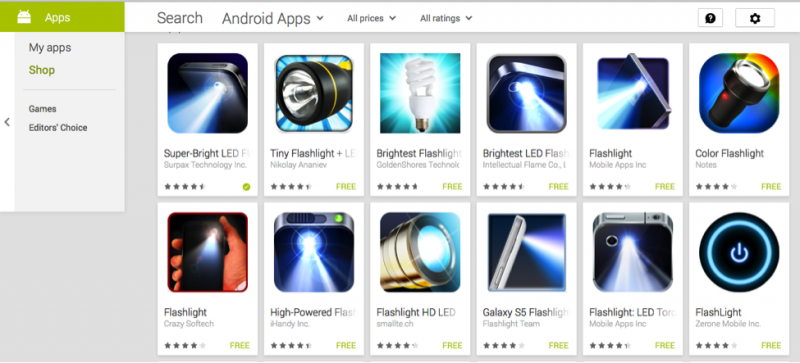
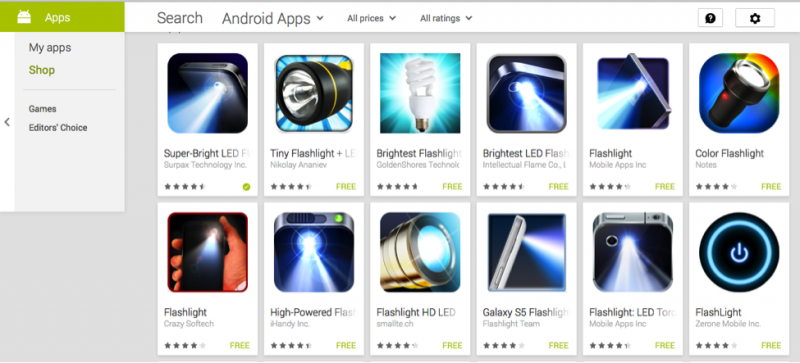 349Geek
349GeekFlashlight Apps Stealing Personal Information Stored On Your Smartphone
It is our duty to protect our data— but are we ready? No one would have thought that the most practical invention...
-

 265News
265NewsAnonymous Shuts Down Top Israeli Govt Sites Against Killing Of 14-Yr-Old Kid
The online hacktivist Anonymous is back with yet another cyber attack. This time the group has taken down 43 top Israeli government...
-

 143Privacy
143PrivacyNew Tor routers seeking crowdfunding by Kickstarter
A selection of rival privacy conscious Tor routers have appeared on crowdfunding sites after the Anonabox was surprisingly pulled just days after...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




