Featured News
-

 102Surveillance
102SurveillanceFBI demands new powers to hack computers and spy on users around the world
The FBI is trying its best to convince an ambiguous regulatory body in Washington to modify its operation rules with the aim...
-

 285News
285NewsRussian Hackers Allegedly Hacked White House Computers
Unclassified White House computers are latest in the list of security breaches this year and the prime suspects for the breach are...
-

 86Malware
86Malware“More human” carder malware emerges for sale in dark web
A carder like tool for cybercriminals that promises to use stolen credit card details in a more 'human way' to bypass fraud...
-
 232Android Hacking
232Android HackingHow to bypass Android Lockscreen
Today i’m going to show you guys how to bypass android lockscreen using two methods. Method 1 What you need: Windows or...
-

 90Malware
90MalwareStealthy malware uses Gmail drafts to steal data
A new strain of malware that uses Gmail drafts in an invisible Internet Explorer window, has been discovered. According to Network World,...
-

 155Privacy
155PrivacyWearable tech and security – can watches help?
So far, wearable tech has been of interest mainly to fitness fiends - but a new generation of hi-tech wearables comes armed...
-

 270Geek
270GeekUbuntu 14.10 Released and Available for Download Here
On 26 October 2014 , Canonical marked the 10th anniversary of an OS that has revolutionized Linux – Ubuntu . And there...
-

 106Mobile Security
106Mobile Security‘Find My Mobile’ system can be used to attack Samsung handsets
One of the most popular and useful security functions of mobile handsets can be turned against the owner.
-
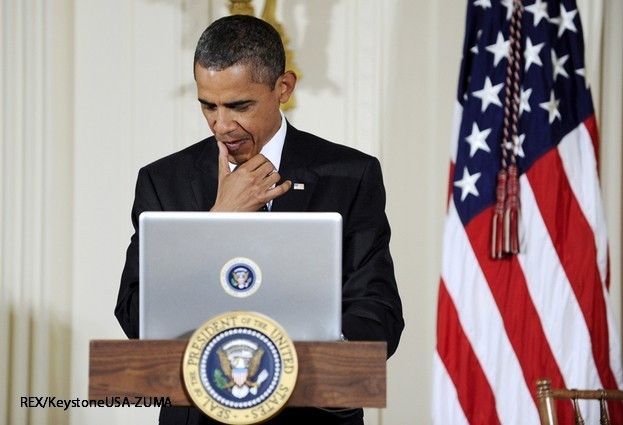
 210Cyber Crime
210Cyber CrimeWhite House hit by “sustained” cyber attack, hackers breach unclassified network
IT security staff have spent the last few weeks fighting hackers in the White House, after a computer network was breached. But...
-

 118Mobile Security
118Mobile SecurityGoogle outlines new security features in Android 5.0
Google has outlined the enhanced security credentials of the upcoming Android 5.0 - nicknamed Lollipop - in an official blog post.
-

 164Surveillance
164SurveillanceThis Camera-Covered Jacket Is Best Surveillance Tool To Record/Report Crime
Street crimes? not a problem now! With the newly designed jackets one can easily track down thieves and alert the respective authorities....
-

 223Tricks & How To's
223Tricks & How To'sRemotely shutdown computers
Note* For this to work you must be connected on the same network as the victim’s computer 1) Right-click on your desktop....
-

 323Information Gathering
323Information GatheringHow to get someones IP from facebook
When you’re talking with someone over chat, make sure your messages also notify you via email. Once someone sends a message and...
-

 169Privacy
169PrivacyBritish job centers to introduce biometric recognition
Job centers across the United Kingdom are due to get a technological makeover, courtesy of biometric and signature recognition pads, reports IT...
-

 307Information Gathering
307Information GatheringHow to find the IP of a Skype user
1.Log onto the computer as the “Administrator.” Go to “Start” > “Search.” 2.Enter “cmd” into the “Search” box. Press “Enter.” 3.Go to...
-

 98How To
98How ToHow do open source tools stay secure?
Security of open source code is a hot topic, what with Heartbleed, Shellshock, and Poodle making the news. Open source code is...
-

 94Cyber Crime
94Cyber Crime42% of Americans hit by regular online attacks
A study by Microsoft has revealed that 42 percent of Americans face 'weekly or daily' attacks by cybercriminals trying to access their...
-

 101Malware
101MalwareTor users targeted with exit node malware
An exit node on the Tor network has been discovered to be slipping malware on top of downloads, according to The Register....
-

 85Cyber Crime
85Cyber CrimeInternet trolls – how to deal with online abuse
Most internet users have faced some kind of problems with internet trolls - and a new study has thrown light on who...
-

 216News
216NewsIranian Hacker Defaces Website of UAE’s Telecom Regulatory Authority
An Iranian hacker going with the handle of MoHaMaD VaKeR hacked and defaced the official sub-domain ofTelecommunications Regulatory Authority (TRA) of United...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




