Featured News
-
 356Geek
356GeekFlashlight Apps Stealing Personal Information Stored On Your Smartphone
It is our duty to protect our data— but are we ready? No one would have thought that the most practical invention...
-

 272News
272NewsAnonymous Shuts Down Top Israeli Govt Sites Against Killing Of 14-Yr-Old Kid
The online hacktivist Anonymous is back with yet another cyber attack. This time the group has taken down 43 top Israeli government...
-

 144Privacy
144PrivacyNew Tor routers seeking crowdfunding by Kickstarter
A selection of rival privacy conscious Tor routers have appeared on crowdfunding sites after the Anonabox was surprisingly pulled just days after...
-

 105Password
105PasswordTwitter: “We’re finally getting rid of the password”
Popular microblogging platform Twitter is taking bold steps to try and put an end to the password as we know it, according...
-
 108Cyber Crime
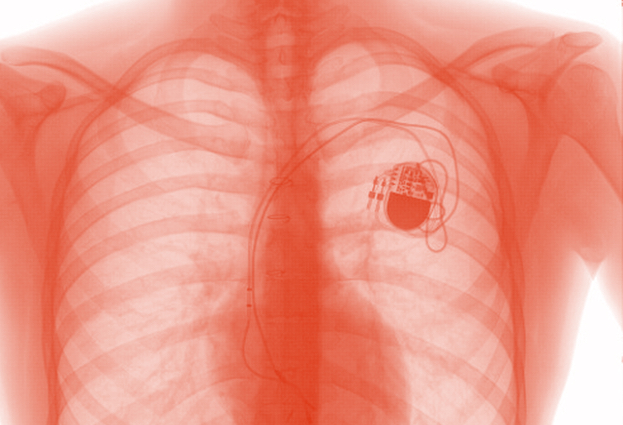
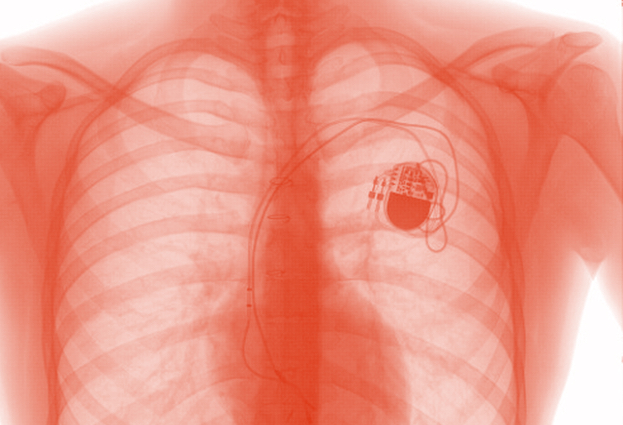
108Cyber CrimeCould hackers give you a heart attack or drugs overdose?
There is growing concern that in the rush to embrace technology to save and improve the lives of patients, medical scientists may...
-
 195How To
195How ToReady, set, shop: 10 top tips for a safe shopping season
Tips for safe holiday shopping: whether you shop online or at the mall, there are some simple strategies that can protect your...
-
 409Privacy
409PrivacyCounter surveillance tech – can gadgets spy‑proof your life?
Over the past few years, counter surveillance gadgets which might have been the preserve of secretive government departments a decade ago have...
-

 236Exploitation
236ExploitationCreate your own USB Password stealer
This tutorial will walk you through setting up a USB flash drive to steal the saved passwords on a computer. Method 1...
-
 423Cyber Crime
423Cyber Crime10-Year-Old Filipino Virtual Girl “Sweetie” Takes Pedophile To Prison In Australia
An Australian citizen Scott Robert Hansen, 37, was sentenced to one year in prison for keeping obscene conversations with children on the internet. Hansen...
-

 104Malware
104MalwareTop 5 Scariest Zombie Botnets
An army of the undead, wreaking havoc on the Internet – it's a nightmare scenario that has played out many times as...
-

 336Lists
336ListsTop Five Best But Lesser Known Features of Android 5.0 Lollipop
As I’ve written in my earlier posts, Android 5.0 Lollipop is the most significant change in Android line-up since 2011’s Android Ice...
-

 185Malware
185MalwareYahoo, Match and AOL hit by ransomware
Cybercriminals taking advantage of a 'malvertising' attack on big name sites including Yahoo!, Match.com and AOL were making in the region of...
-

 330Banking
330BankingThe Evolution of Webinject
Last month, we presented “The Evolution of Webinject” in Seattle at the 24th Virus Bulletin conference. This blog post will go over...
-

 93Password
93PasswordWindows 10 to tighten security with prominent 2FA
Microsoft is taking aim at traditional single password systems with the upcoming version of Windows, by including build in two-factor authentication according...
-
 82How To
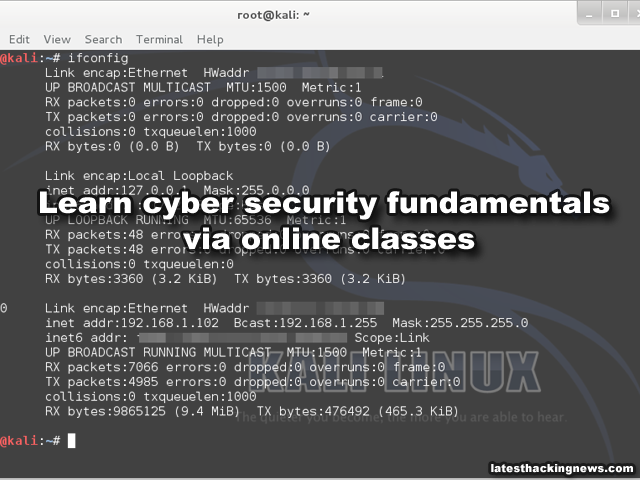
82How ToLearn cyber security fundamentals (Free course) (online classes)
SANS Cyber Aces Online makes available, free and online, selected courses from the professional development curriculum offered by The SANS Institute, the...
-
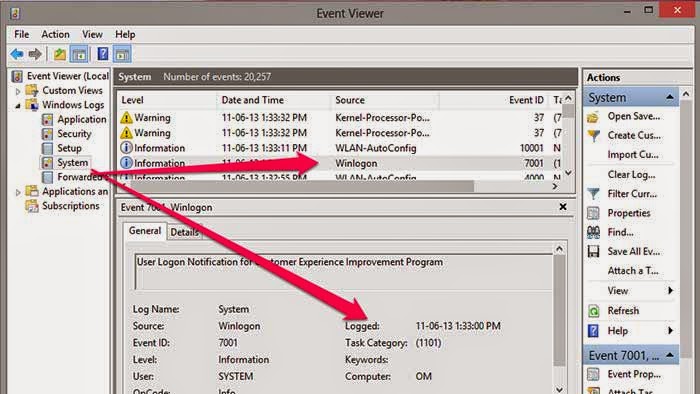
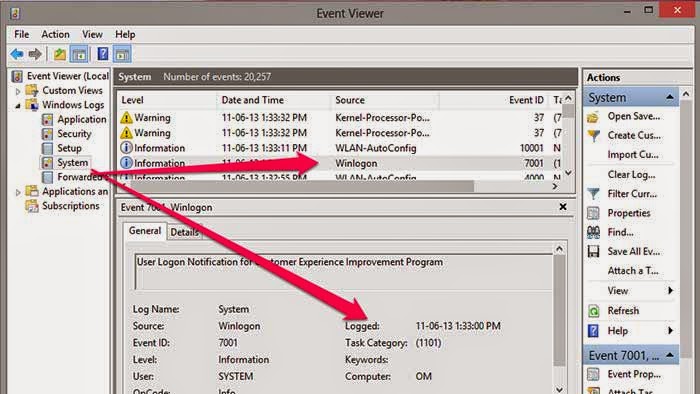 196How To
196How ToFind Out If Any One Opens Your Computer Without Your Permission
How to Know Who Logged into your computer and when? In Windows, there is one in-built too will records all events in...
-

 163How To
163How ToProtect your Eyes By Automatically Adjusting Computer Screen Brightness Based On Time of the Day
Today Most of the youngsters using their computers at night very long time than daytime. Staring at your computer screen for the...
-

 70Cyber Crime
70Cyber CrimeiCloud users in China under attack. But who could be after their passwords?
Make sure you are running a half-decent browser, don't ignore browser security warnings, and enable two-factor authentication. That appears to be the...
-

 94Cyber Crime
94Cyber CrimeUK takes aim at serious hacking offenses with planned life sentences
Law makers in Britain are discussing a dramatic increase in sentencing for serious hacking offences, according to The Register. Currently in discussion...
-

 134Password
134PasswordGoogle now offers USB key authentication
Google has added an extra layer of security to its browser, by introducing USB authentication to Chrome, the company has announced in...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




