Featured News
-
 177Lists
177ListsLast Day of Orkut : 11 Embarrassing & Funny Things We Did on Orkut, a GIF Essay
Yesterday my friend reminded me that September 30th is Orkut‘s last day. It took me back in time when I stopped using...
-

 154Privacy
154PrivacyHow George Clooney made sure phone hackers didn’t ruin his wedding
Newly weds George Clooney and Amal Alamuddin supplied guests with "burner phones" to prevent photographs from falling into the hands of hackers...
-

 230How To
230How ToWrite Your Message in the Sky and Name with the Galaxies
Each time we look at the sky we get amazed by its brilliance and vastness . Whenever I need to spend some...
-

 242Geek
242GeekHong Kong protesters targeted with Android spyware disguised as OccupyCentral app
The pro-democracy protesters in Hong Kong have been targeted with an Android spyware disguised as an #OccupyCentral app, according to a team of security...
-

 342News
342NewsResearcher Hacks iPhone6 TouchID, Big Question over ‘Apple Pay’ Security
Remember when Apple’s iPhone 5S fingerprint sensor or in other words TouchID was hacked? Well history is repeating itself because the Apple...
-
 213Data Security
213Data SecurityShellshock Bash Bug Leaves Almost Every User on The Internet Vulnerable
They call it Shellshock bug, they say it is way more dangerous than the previous Heartbleed bug which left all the secure SSL...
-

 95Cyber Crime
95Cyber CrimeWeek in security: Bash Bug, BlackEnergy and hoax attacks
This week, a serious software vulnerability, which rapidly became known as the ‘Bash Bug’ or ‘Shellshock’ dominated the headlines, as two other...
-

 333Linux
333LinuxHow to resolve Shellshock on Mac OS X, web servers and more
The "Bash Bug" or "Shellshock" vulnerability means a wide range of devices, servers and computers, including Mac OS X, will need to...
-

 233Opinion
233Opinion4Chan: destructive hoaxes and the Internet of Not Things
The media have associated a number of destructive hoaxes with 4chan: people need some historical perspective on how the site actually works.
-

 64Cyber Crime
64Cyber CrimeHealthcare data worth ten times price of credit card data
Medical information is now worth up to 10 times the price of credit card details on online black markets, due to weak...
-

 67Cyber Crime
67Cyber CrimeeBay scams – site says ‘no plans’ to ban ‘active’ listings
Auction site eBay has remained defiant about ‘active’ listings ,containing computer code, despite multiple reports indicating that these are being used for...
-

 68Cyber Crime
68Cyber CrimeDestiny game servers under attack
The hit shoot ‘em up Destiny has been targeted by a cybercriminal gang thought to be behind recent attacks on game companies...
-

 160How To
160How ToHow The Pirate Bay Remains Untouchable
The Pirate Bay still remains the world’s largest torrent site which handles requests from millions of users every single day and is...
-
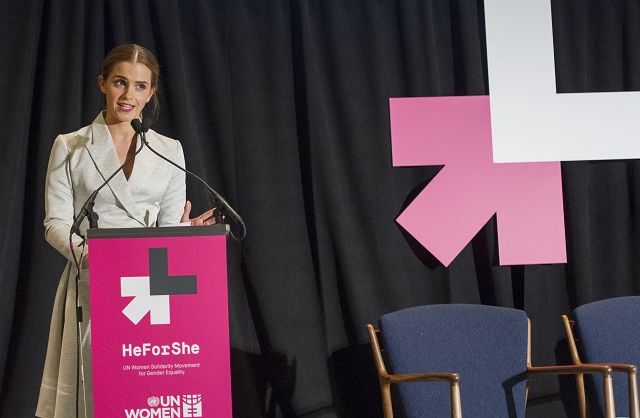
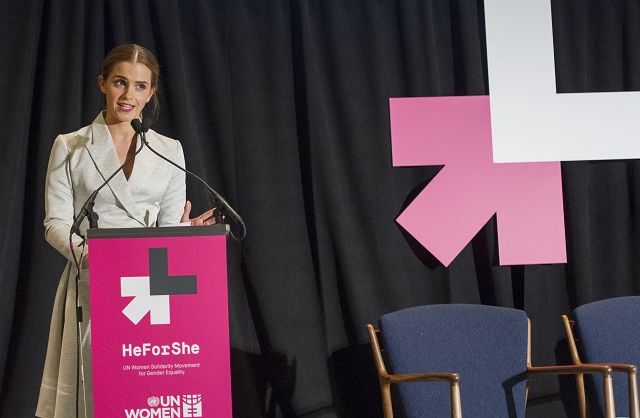 142Cyber Crime
142Cyber CrimeEmma Watson images – ‘countdown’ to leak after UN speech
In what appears to be a misogynist attack directed at Harry Potter actress Emma Watson, a site has appeared supposedly offering a...
-

 93Privacy
93PrivacyFacial recognition – boom in sites such as dating services
Facial recognition is booming, with the market expected to grow from $1.92 billion to $6.5 billion in 2018 - and invading markets...
-

 85Cyber Crime
85Cyber CrimeWhat’s behind the rise in cybercrime? Find out from this recorded presentation
Home Depot says it was hacked to the tune of 56 million payment cards. What is behind the current wave of cybercrime?...
-

 180Malware
180MalwareBack in BlackEnergy *: 2014 Targeted Attacks in Ukraine and Poland
State organizations and private businesses from various sectors in Ukraine and Poland have been targeted with new versions of BlackEnergy, a malware...
-

 136Cyber Crime
136Cyber CrimeHome Depot data breach – ‘warnings ignored since 2008’
Home Depot staff repeatedly ignored the concerns of employees about the security of its systems, prior to the Home Depot data breach,...
-

 116Scams
116ScamsFacebook to start charging $2.99/month? It’s nonsense!
Thousands of Facebook addicts are feverishly sharing a "news report" claiming that from November 1st you'll be paying $2.99 every month to...
-

 107How To
107How ToHow to protect yourself after the Home Depot breach
Home Depot has issued a statement today that provides more details about their recent breach, as well as indicating that the malware...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




