Featured News
-
 111Malware
111MalwareBeware overdue invoice malware attack, wrapped in an .ARJ file!
Online criminals are spamming out messages claiming that invoices are overdue. But attached to the emails are .ARJ files containing a malicious...
-

 326How To
326How ToHow to Install Gnome Desktop Environment in Ubuntu 14.04 LTS?
Gnome is one of the most popular and most used desktop environment for Linux systems . It is a desktop environment which...
-

 78Cyber Crime
78Cyber CrimePhishing email: UK hit with three times as many ‘bad’ links as U.S.
British internet users opening a spam email are three times more likely to be facing a malicious URL than users in the...
-

 70Cyber Crime
70Cyber CrimeWeek in security: Home Depot speaks, Gmail and Android ‘leak’
This week, American chain Home Depot admitted its systems had been breached, Gmail users got a fright, and a series of videos...
-

 276Lists
276ListsConnect Your Phone and Computer with These Free Apps and Enhance Your Productivity
You can make your phone even more productive if you can connect them with your computer. Connecting them isn’t just about using...
-
 92Privacy
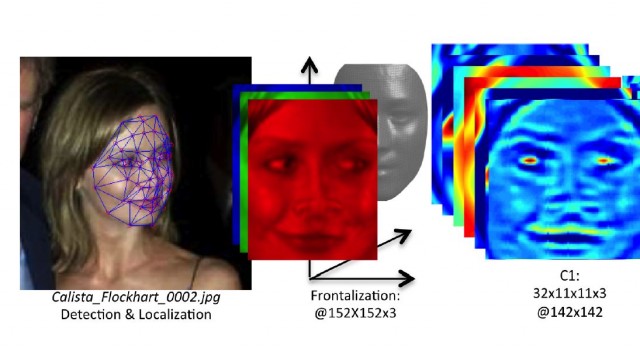
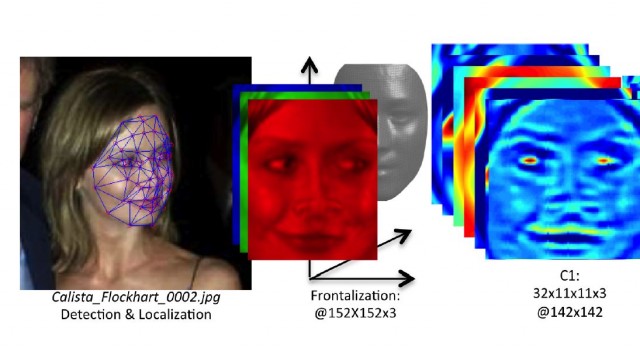
92PrivacyFacebook tag – fears over “Faceprints” after genetic match
A young man who got an email from Facebook ‘identifying’ him via Facebook tag in a series of photographs which turned out...
-

 84Cyber Crime
84Cyber CrimeSalesforce software – millions of users at risk of Dyre malware
A strain of malware which previously targeted banks has turned its attention to users of the popular Customer Relationship Management (CRM) software...
-

 73Cyber Crime
73Cyber CrimeFive million Gmail credentials posted online
Some five million people who used their Gmail address as a user name had their passwords published by someone who apparently thinks...
-

 362Cyber Crime
362Cyber CrimeMH17 plane crash victims exploited by cold‑hearted scammers
The sad truth is that scammers and fraudsters don't have any conscience, and are prepared to do anything if it might net...
-

 132Privacy
132PrivacyBitcoin creator – could he be ‘outed’ after email ransom?
Bitcoin’s mysterious creator, who goes by the pseudonym ‘Satoshi Nakamoto’, could be about to have his identity made public, after a series...
-

 143Cyber Crime
143Cyber CrimeNude Celebs, Target, Home Depot: Who is to blame? Criminals!
The blame game rages on in the wake of Celebgate and massive payment card hacks like Home Depot and Target, as though...
-

 75Cyber Crime
75Cyber CrimeOnline ad threat – Yahoo, Amazon, YouTube ‘victims of malvertising’
Anyone who has visited popular domains such as YouTube.com, Amazon.com or Ads.Yahoo.com could be a victim of a new, mutating malware attack...
-
 210How To
210How ToHow to Install a Screensaver in Ubuntu ?
You know the time when LCD, LED screens were not common and CRT monitors were mostly used for video output? it was...
-

 154Privacy
154PrivacyChat apps leak: Billion app users from OKCupid to Grindr at risk
Nearly a billion users of a dozen chat apps for Android including popular apps such as Instagram, Oovoo, OKCupid and Grindr could...
-

 236Cyber Crime
236Cyber CrimeHome Depot credit cards: chain confirms breach, fraud spikes
The world’s largest home improvement chain store, Home Depot, yesterday confirmed a data breach affecting credit cards and debit cards used in...
-

 94Privacy
94PrivacyPrivate browsing – Americans ‘care deeply’ about privacy
A new Harris survey found that almost all Americans care about online privacy, and 71% said that they ‘care deeply’ about it....
-

 103Password
103PasswordStrong password – Chrome now offers ‘pronounceable’ choices
Google Chrome will now recommend pronounceable password hoices, according to developer and Chrome “happiness evangelist” Francois Beaufort, who announced the change via...
-
 200Geek
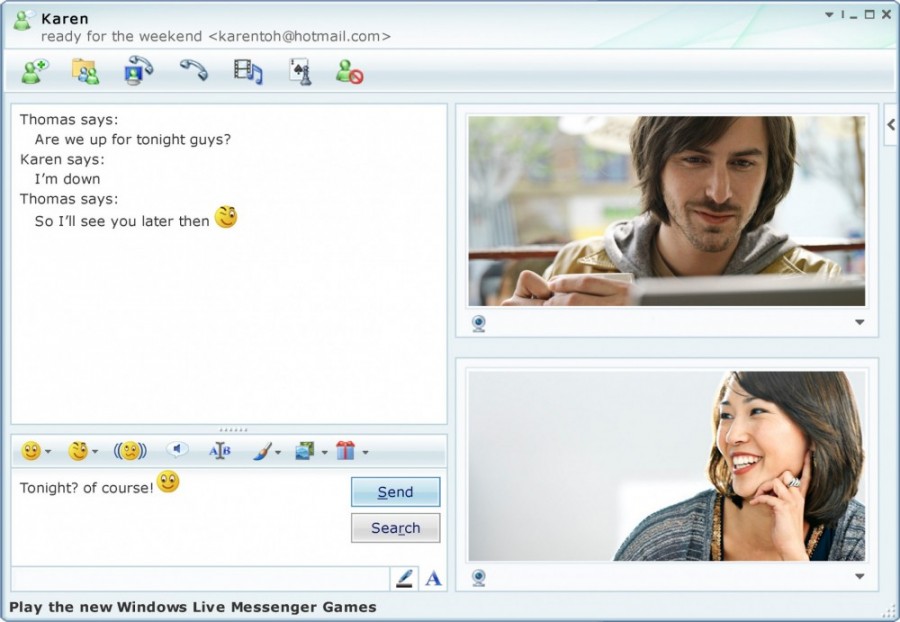
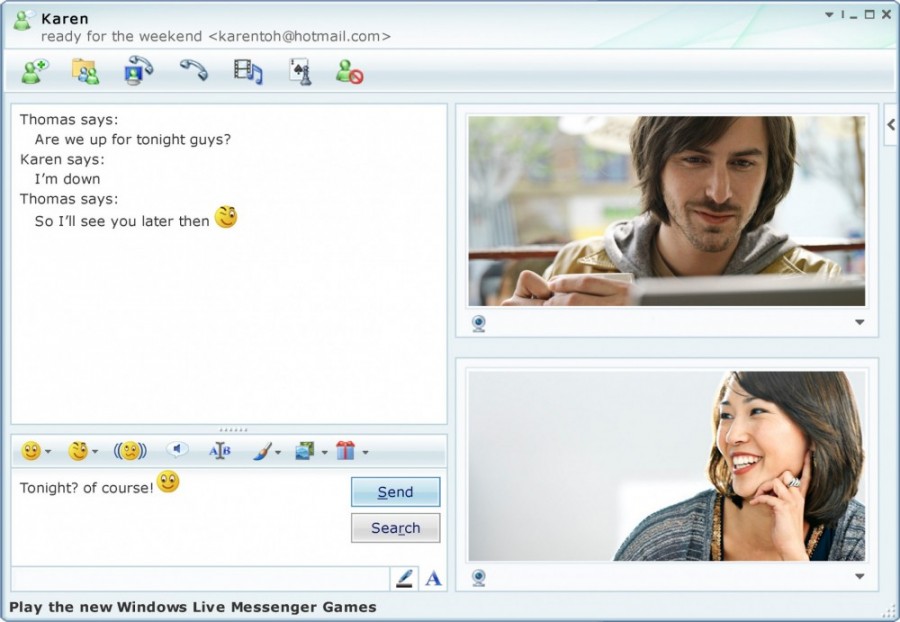
200GeekR.I.P MSN Messenger :(
It’s time to say good bye to once the best instant messaging platform MSN Messenger (also known as Windows Live Messenger). Microsoft started shutting...
-

 231How To
231How ToHow to Install Cinnamon on Ubuntu 14.04?
Cinnamon is a popular Linux desktop based on GTK+ that got its start as a fork of GNOME Shell . It is...
-
 223How To
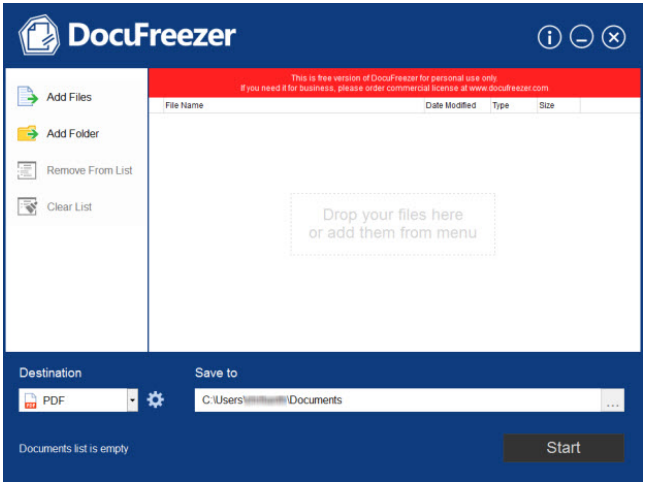
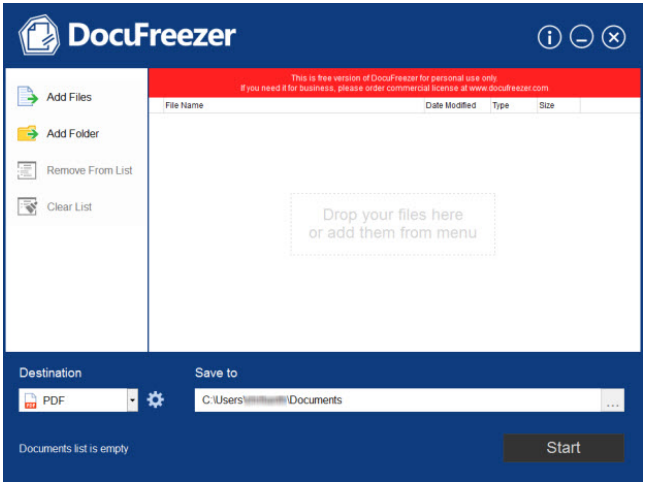
223How ToDocuFreezer: Offline conversion of documents to PDF and JPEG’s demystified [Review]
People handling hundreds of documents weekly as part of their personal or professional work know how it feels when their internet connection...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




