Featured News
-

 92Password
92PasswordPIN number: Police want codes on ALL devices
Police hope to work with leading mobile phone manufacturers such as Samsung to build in the requirement for a password or PIN...
-

 90Password
90PasswordBanking security – new apps ‘know’ your touch
Everyone hates passwords - even the guy who invented them - but some bank app users in the Nordic region are experiencing...
-

 236Lists
236ListsTop 5 Torrent sites of 2014
In the world of torrent downloading, you must understand one thing that there always will be more “Leechers” than “Seeders”. Telling about...
-

 93Malware
93MalwarePhishing emails: U.S. nuke authority hit three times
America’s Nuclear Regulatory Commission was successfully attacked three times within the past hree years, by unknown attackers, some foreign - and largely...
-

 162Privacy
162PrivacyTwitter hacked – Cricket legend ‘Beefy’ Botham exposed
One of England’s greatest-ever cricketers, Sir Ian Botham, appeared to have been the victim of a Twitter hack yesterday as an obscene...
-
 389News
389NewsHackers Sending Fake Ebola Virus reports in emails with Malware and Phishing Links
A new malicious campaign has been identified by security researchers spreading fake news about the Ebola virus, in order to redirect users...
-
 325Geek
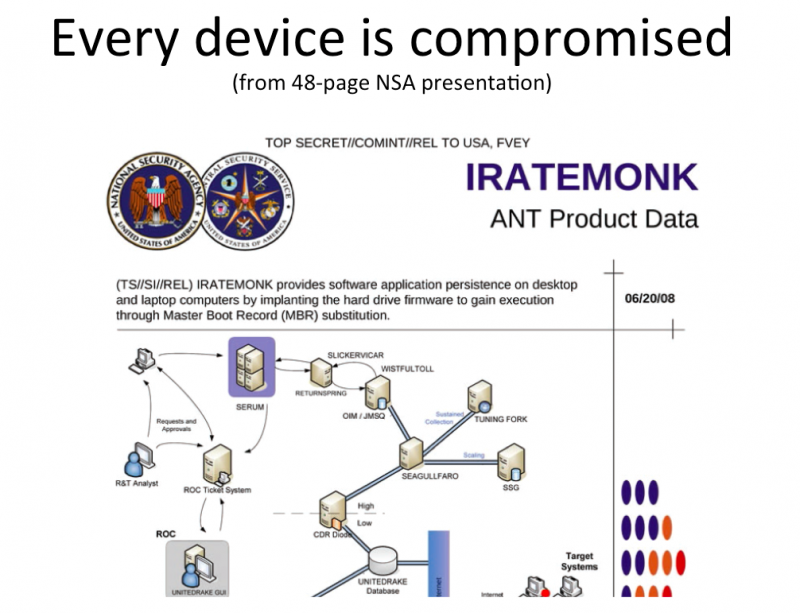
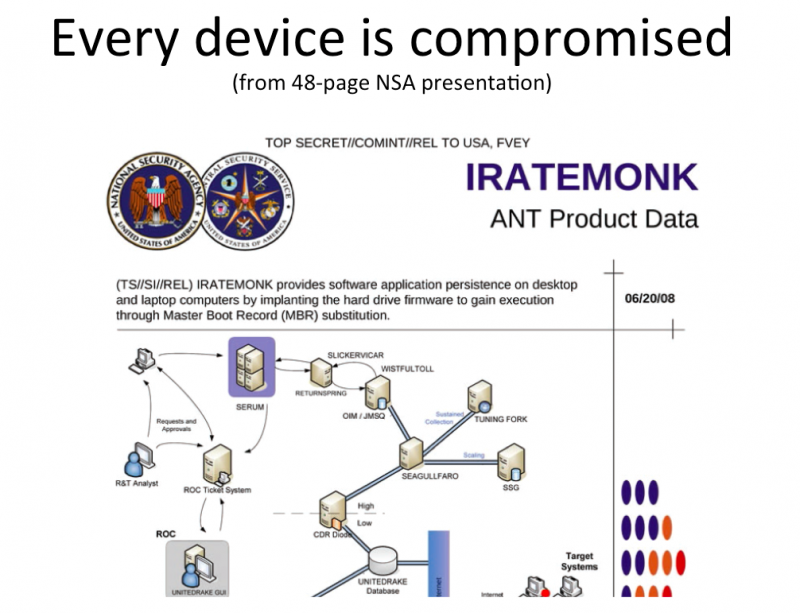
325GeekDon’t freak out about Facebook messenger app, NSA already has your chats
Privacy concerns over the Facebook Chat App is at an all time high. Increasingly more and more people are voicing their concern...
-

 190Privacy
190PrivacyPrivacy: Workers “would pay” to stop snoopers
Online privacy has gone from being a minority concern to something that worries the man in the street - after a study...
-

 82Cyber Crime
82Cyber CrimeGamescom: How gaming grew up into a target for crime
Video games have gone since the late 1970s and early 1980s from being a small offshoot of the "traditional" computing industry to...
-

 169Cyber Crime
169Cyber CrimeWeek in security: Blackphone unmasked, RATs vs Androids, and browsers kill cars
Blackphone, billed as a privacy tool to keep the puplic safe ruled the headlines when it was is hacked in five minutes,...
-

 285Scams
285ScamsRobin Williams’ last phone call? Sick Facebook video scam exploits celebrity suicide
Sick-hearted scammers have proven themselves to have no morals once again, exploiting the death of Robin Williams with their latest Facebook scam.
-

 75Cyber Crime
75Cyber CrimeRussian PM has his Twitter account hacked, announces “I resign”
There may be red faces in Red Square, after Russian prime minister Dmitry Medvedev had his Twitter account hacked.
-

 95Password
95Password‘Biometric’ earbuds invisibly prove it’s you, with no need for passwords
Biometrics are touted as a replacement for the passwords and PINs we all know and hate - and Intel’s new earbuds could...
-

 91Malware
91MalwareGamescom 2014: World of Malware?
The gaming industry keeps growing, and the crowds at Cologne's Gamescom 2014, show why big game titles are rapidly becoming a target...
-

 105Scams
105ScamsPhone scams: card fraud with that steak, Sir?
A new telephone scam in upscale restaurants in London, has “convincing” scammers calling restaurant staff and tricking them into believing there's a...
-

 139Hacking
139HackingWill web browsers turn cars lethal?
Two researchers have launched a petition to change how car companies and technology cmpanies work together - with a new villain: in-car...
-

 94Cyber Crime
94Cyber Crime2FA – are big banks failing America?
The Target breach caused real damage to millions of American card users - but big financial institutions are doing little to remedy...
-

 386Cyber Crime
386Cyber CrimeWɑit! Stοp! Is that ℓιηκ what it claims to be?
Can you tell the difference between exɑmple and example? Google adds non-Latin support to Gmail, and we explain why characters matter when...
-

 373Password
373PasswordWi‑Fi security – routers “like fish in a barrel”
Researchers flexed their hacking muscles at DefCon 22 to hunt the technology world’s most defenceless beasts - routers. More than a dozen...
-

 173Privacy
173Privacy‘Secure’ Blackphone hacked in 5 minutes
An ultra-secure phone claimed to be the first privacy-focused smartphone on sale swiftly fell victim to a security researcher - who hacked...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




