Featured News
-

 221Scams
221ScamsFacebook scams target grieving families of Flight MH17
Callous cybercriminals have used the Malaysia Airlines Flight MH17 tragedy as a lure for Facebook scams - creating fake profiles for victims...
-

 225Cyber Events
225Cyber EventsAnonymous asks Elite hackers to join them in a massive cyber attack on Israel
The online hacktivist Anonymous has a message for Israeli government in which the group has asked elite hackers from around the world...
-

 293News
293NewsPalestinians and Israelis take battle to social networks
Now, the battle waged by both sides also extends to social networks. Israelis and Palestinians are increasingly using sophisticated methods in an attempt...
-

 343Data Security
343Data SecurityDangerous Malware steals credit card information from Android devices
Security experts at Dr. Web have warned Android users to be careful with a new Trojan that is stealing credit card details while...
-

 380Password
380PasswordWi‑Fi security alert on Chromecast as ‘Rickmote’ hijacks nearby boxes
A security researcher has built a remote control which hijacks any nearby Chromecast highlighting a Wi-Fi security issue, which allows an attacker...
-
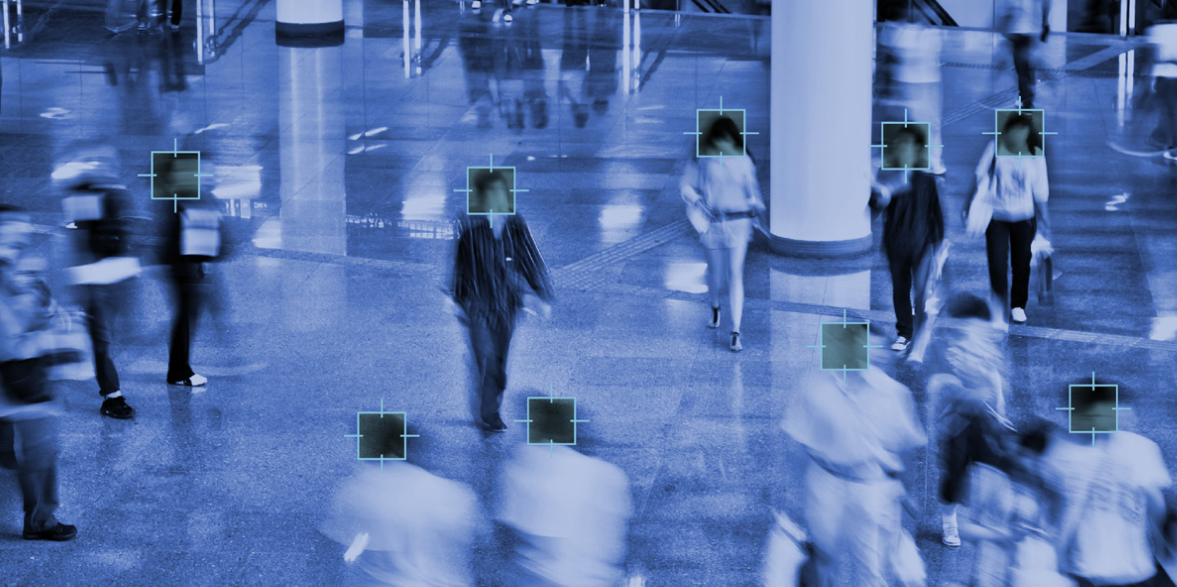
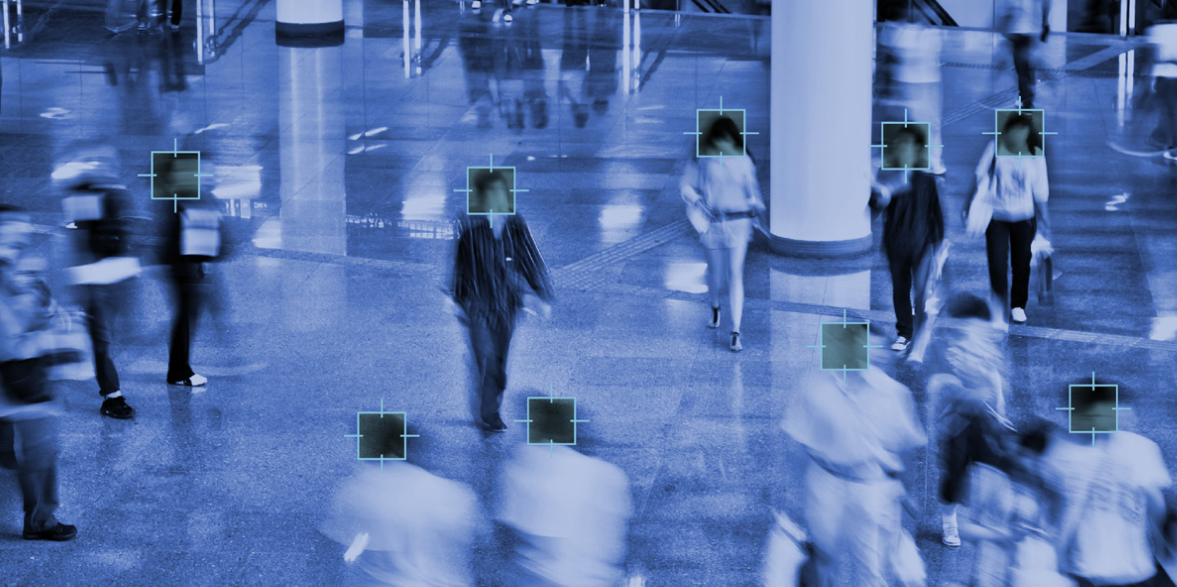 111Privacy
111PrivacyPrivacy concerns over Police ‘instant ID’ camera trial
New facial recognition technology which can instantly identify people from any digital image in seconds is being trialled in the UK for...
-

 318News
318NewsIsrael’s Channel 10 TV Station Hacked by Hamas
Hackers from Hamas military wing in Palestine hacked the satellite communication of the Channel 10 TV station in Israel on Monday for a few...
-

 106Cyber Crime
106Cyber CrimeHacked Japanese porn sites spread banking malware attack
Thinking of spending some time perusing Japanese porn websites before you do your online banking? Security researchers at ESET have analysed an...
-

 180Cyber Crime
180Cyber CrimeWin32/Aibatook: Banking Trojan Spreading Through Japanese Adult Websites
Win32/Aibatook targets Japanese bank customers with an unusual Internet Explorer monitoring technique. We believe the malware has been in development for months...
-

 103Privacy
103PrivacyArtist mails NSA ‘uncrackable’ mixtape
An artist has created what he claims to be an ‘uncrackable’ mixtape, using freely available encryption tools and housed on a home-made...
-
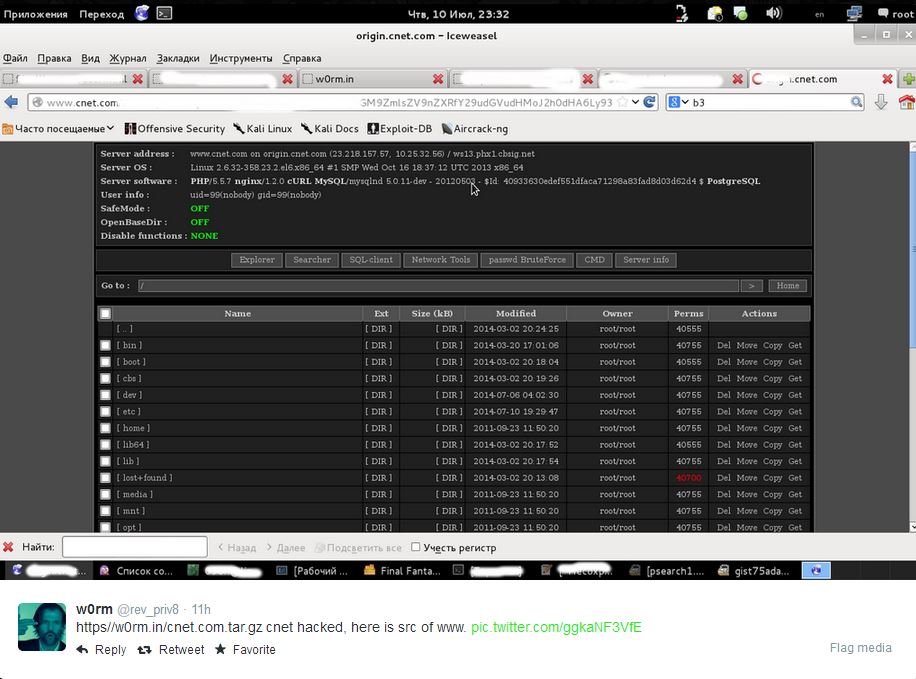
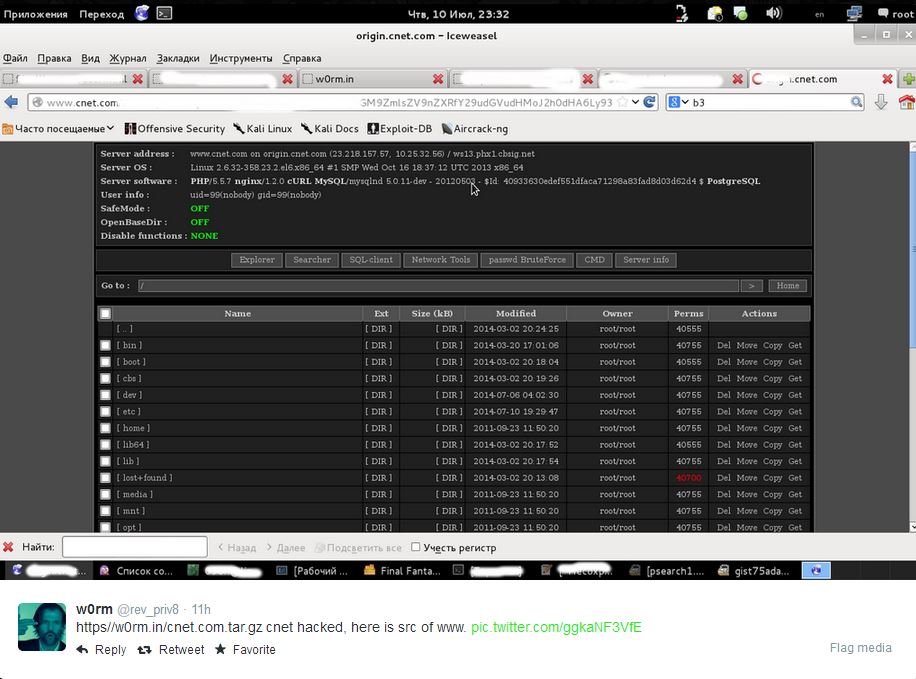 82Cyber Crime
82Cyber CrimeCNET ‘database leak’ – are your details safe?
Popular technology news and review website CNET faced the threat of having a million users' data exposed this week, with an unknown...
-
 148News
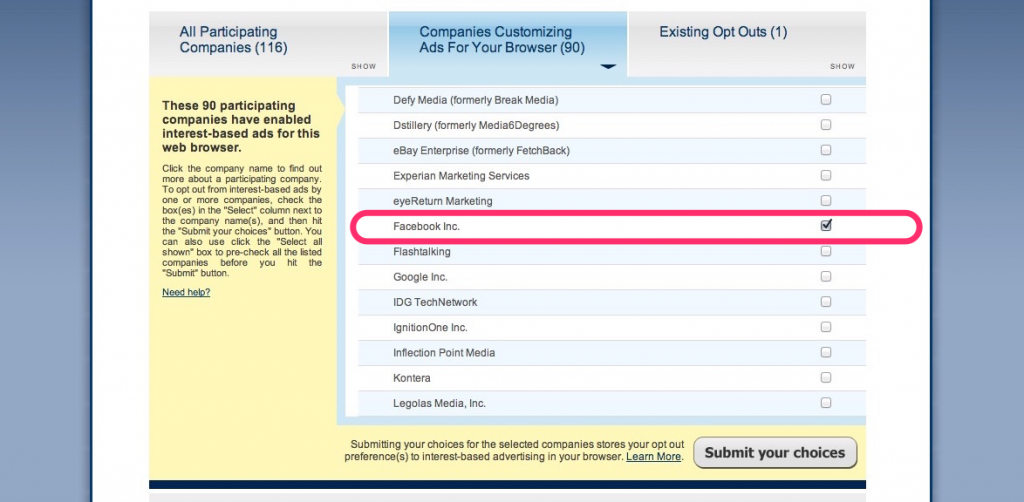
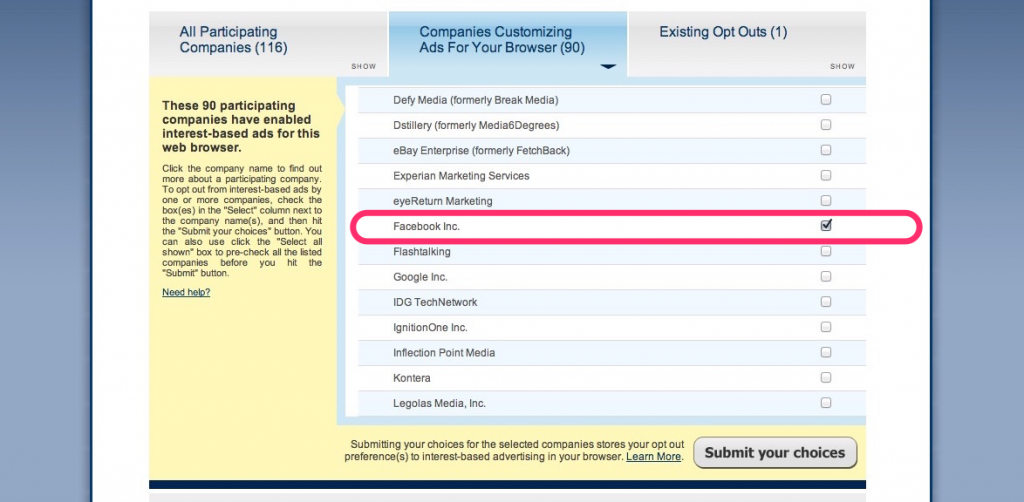
148NewsThis is How You Stop Facebook From Using Your Browsing History
A couple of weeks ago, the social media giant Facebook announced that in order to serve us with targeted ads – it will starting...
-

 74Cyber Crime
74Cyber CrimeData breaches in New York have tripled
Data breaches have hit a record high in the state of New York, tripling since 2006, according to records released by the...
-

 64Cyber Crime
64Cyber CrimeGoogle Chrome security warnings – now in plain English
“Phishing attack ahead” is similar to the stark, clear warnings delivered by road signs - and web users will soon benefit from...
-

 70Cyber Crime
70Cyber CrimeKeylogger malware in hotel business centers – should you worry?
Guests who used business centers in American hotels may be at risk from gangs installing keylogger malware on the computers to steal...
-

 186Password
186PasswordRetina scanner for Samsung Galaxy Note 4?
A Tweet from an official Samsung Galaxy Note 4 account has dropped a very unsubtle hint that its upcoming Galaxy Note 4...
-

 114Privacy
114PrivacyLastPass security holes found by researcher, says password management firm – but no need to panic
LastPass has gone public about a couple of security holes that were found in its popular online password management software. That's enough...
-
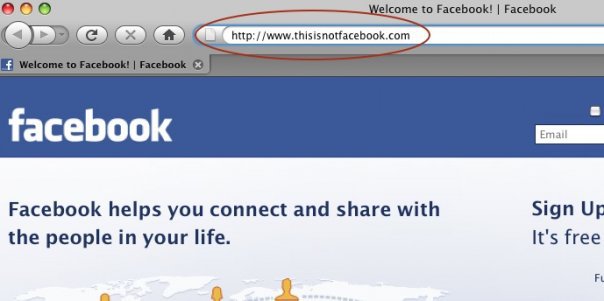
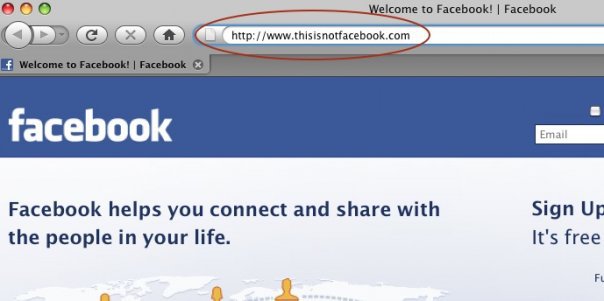 225How To
225How ToHow do Facebook accounts get hacked [Protect Yourself Against It]
Facebook phishing. Phishing is a way of attempting to acquire information such as usernames, passwords, and credit card details by masquerading as...
-

 78Cyber Crime
78Cyber CrimeBanking malware Shylock’s servers knocked out by law enforcement
A notorious strain of banking malware, known as Caphaw - or Shylock, due to snippets of Shakespeare’s Merchant of Venice embedded in...
-

 126Privacy
126PrivacyGoogle Drive privacy warning – could yours have leaked data?
Files sent as a link from Google Drive could have shared more than their senders intended, Google admitted this week - in...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




