Featured News
-
 454Password
454PasswordGoogle buys firm with password‑busting “silent sound” authentication system
Google has bought a company offering a new form of two-factor authentication - using “silent” sounds played via PC and smartphone speakers...
-
 277Scams
277ScamsTax Scams, Malware, Phishing and a 419
A roundup of scam information, including a tax scams article, email with a link to malware, a phish, and the worlds laziest...
-

 293Mac
293MacNew to Mac? Four security tips you need to know
Mac OS X is a slick, easy-to-use operating system with an impressive record on security – and basic malware detection built in...
-
 96Malware
96MalwareMysterious ‘Moon’ worm spreads into many Linksys routers – and hunts new victims
Malware dubbed ‘Moon’ due to images found within the malware has spread rapidly through many models of Linksys routers - even ones...
-

 87Password
87PasswordThe password is ‘burger joint’; places could be key to secure passwords
Could places, not phrases, be the basis of secure passwords. UAE researchers have created a system for creating complex passwords using facts...
-

 85Password
85PasswordKickstarter hacked. Users told to change passwords
Security expert Graham Cluley takes a look at the Kickstarter hack, and discovers there's more to think about than just changing your...
-
 217Cyber Events
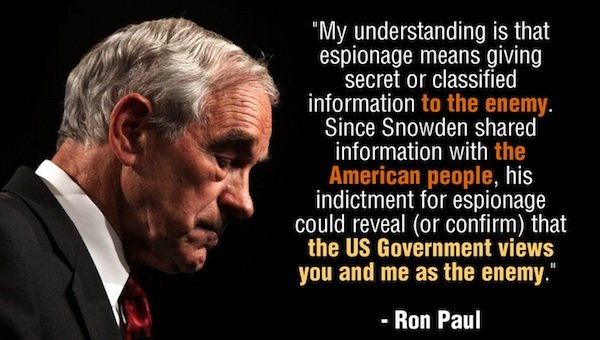
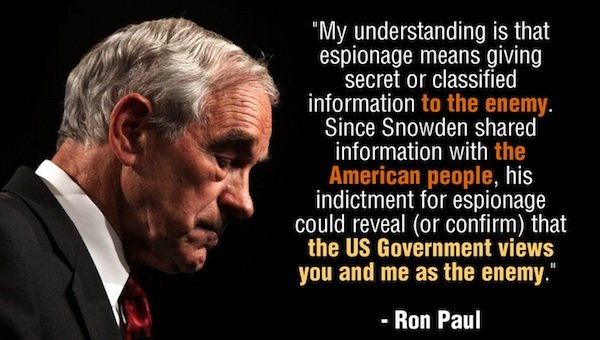
217Cyber EventsRon Paul Launches Clemency Petition for Snowden!
Ron Paul, a former Texas congressman, has launched a petition seeking clemency for Edward Snowden, the whistleblower who leaked data about the NSA surveillance...
-
 182Geek
182GeekEgyptian hacker removes Mark Zuckerberg’s Facebook Timeline Photo
An Egyptian hacker removed Mark Zuckerberg’s Facebook timeline cover photo from his account using a private exploit, according to a latest hacker...
-

 232Cyber Events
232Cyber EventsBrazil is spying on social media accounts of protesters, hoping to protect World Cup
According to the officials, the security forces of Brazil are constantly using secret agents and thoroughly supervising the social media in order...
-

 221News
221NewsLulzSec Peru hacks Twitter account of Venezuela’s Ruling Party against Twitter Cencorship
World renowned hacktivists from LulzSec Peru have hacked a verified Twitter account of United Socialist Party of Venezuela (PSUV). After taking over the Twitter account, the hacktivists...
-

 286News
286NewsRedHack Leaks Contact Details of US Embassy staff in Turkey
Turkish based RedHack hacktivist claims to leak personal information and contact details of US embassy’ staff in Turkey. The dumped data shows...
-

 284News
284NewsSyrian Electronic Army hacks Forbes Website and Twitter account for spreading hate against Syria
The hardcore supporters of Syrian President Bashar-Al-Assad from Syrian Electronic Army have hacked the American business magazine Forbes. As a result of hack, a...
-
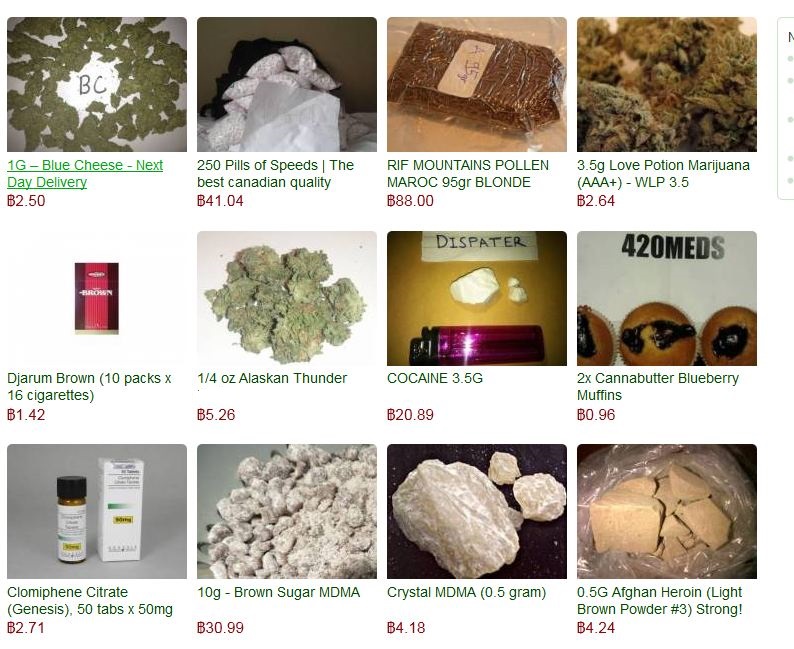
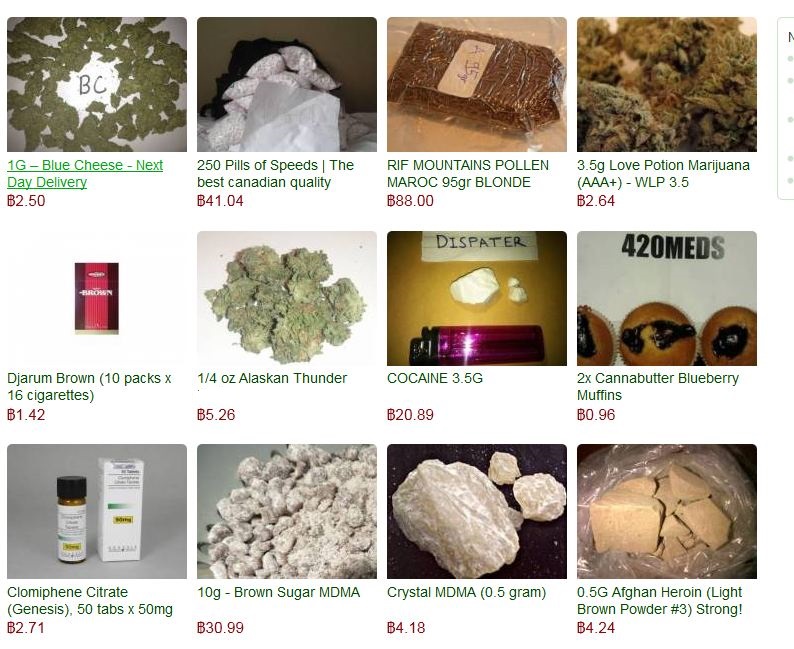 78Cyber Crime
78Cyber CrimeSilk Road 2.0 drug market hit, millions stolen from bitcoin reserve
A large scale cyber-theft has drained the relaunched ‘online drug bazaar’ Silk Road 2.0 of nearly all of its Bitcoin reserves -...
-
 298News
298NewsAnonymous Ukraine Claims to hack and leak secret email conversations of Vitali Klitschko’s UDAR party
Activists in Ukraine are fighting a battle on ground, while hacktavists are putting their share online. The Anonymous Ukraine, in an email...
-

 386Password
386PasswordTwo‑thirds of couples ‘share passwords to online accounts’, Pew research finds
Couples who have been in a long-term relationship indulge in risky online behaviour, such as sharing passwords for online accounts, with two-thirds...
-
 185Cyber Crime
185Cyber CrimeThe 400Gbps largest DDoS attack has hit Europe using NTP Amplification
For temporary abandoning the services of the host that is connected to some internet, the most widely used and favorite method that...
-
 94Cyber Crime
94Cyber CrimeKaspersky Uncovers sophisticated Spying operation ‘The Mask’ targeted diplomats, govts for 7 years
Kaspersky Lab, the Moscow-based computer security software firm, has unearthed a cyber-spying campaign apparently started by a Spanish-speaking country. The campaign targeted...
-

 106Malware
106MalwareCritical IE and other flaws discovered. Patch your systems now, says Microsoft
If your system administrator looks a little frazzled this week, be nice to him or her and don't grumble too much about...
-

 100Cyber Crime
100Cyber CrimePersonal email and cloud storage pose ‘biggest threat’ to corporate data, report claims
Nearly two-thirds of employees - 63% - use personal email to transfer work files, potentially leaving workplaces exposed to hacks against their...
-

 82Cyber Crime
82Cyber CrimeWorldwide cost of identity theft could be $5 billion per year, Microsoft survey finds
A Microsoft survey of 10,000 consumers found that the worldwide annual cost of identity theft and phishing could be as high as...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




