Featured News
-

 244News
244NewsIranian Hacker Hacks Israeli Job Portal, Leaks 3349 Login Accounts of Israeli Users
An Iranian hacker going with the handle of Dr.3v1l from Black_Devils B0ys hacking group has breached to an Israeli based job search portal, as...
-

 116Malware
116MalwareStop, thief! Five new tricks used by cybercriminals – and how to stay safe
From legitimate companies delivering software with a “side-order” of malware, to PC attacks that persuade you to infect your own phone, here...
-

 120Android
120AndroidSecurity alert over sensors in smartphones – is your accelerometer selling you out?
Most smartphones today contain an accelerometer - without them, the latest fitness apps don’t work - but a Stanford researchers has shown...
-

 292Surveillance
292SurveillanceBitTorrent Bashes NSA In Stunning Billboard Campaign
If you live in New York or San Francisco, you will know the importance of its billboards and strange messages mentioned on...
-

 395Cyber Crime
395Cyber CrimeSome D‑Link routers contain “backdoor” which allows remote access, researcher warns
Some models of the popular routers made by D-Link contain a “backdoor” which could allow a remote attacker access to settings and...
-

 272News
272News#OpTrollIsrael: 65 Israel Websites Hacked by AnonGhost
The Moroccan based online hacktivist going with the handle of AnonGhost has hacked and defaced 65 Israeli websites under the banner of...
-
 213News
213NewsBSNL Telecom India Domain Hacked and Defaced by P4K-M4D-HUNT3R-Z
A Pakistani hacker going with the handle of Ch3rn0by1 from P4K-M4D-HUNT3R-Z has hacked and defaced the official domain of India’s Bharat Sanchar Nigam Limited (BSNL) Telecom yesterday....
-

 298News
298NewsPakistani Hacker Defaces official Google, Google Images and Google Plus Malaysia Domains
In a high profile hack, a famous Pakistani hacker going with the handle of H4x0r HuSsY from MadLeets hacking crew has...
-
 133News
133NewsBMPoC Hacker Defaces another NASA Domain but not against NSA or Syrian War
The world renowned BMPoC hacker who got fame by defacing 14 official NASA domains against NSA’s spying over Brazil and Syrian war has now defaced...
-

 426News
426NewsAnonymous Palestine – KDMS Team Defaces Websites Anti-Virus ESET, BitFinder, Penetration Software Metasploit and Rapid7
The online hacktivists from Anonymous Palestine – KDMS Team has hacked and defaced the official websites of anti-virus giant ESET, BitFinder along with...
-

 247Malware
247MalwareWin32/KanKan – Chinese drama
In this blog post, we will describe software detected by ESET products as Win32/Kankan, and explain why its discovery shocked many Chinese...
-

 82Cyber Crime
82Cyber CrimeThe wrong cable guys: Card skimmers install bogus wires into cash registers in Nordstrom store
A trio of men plugged keyloggers disguised as ordinary connectors into cash registers in a Nordstrom department store in Florida, and returned...
-

 387Password
387PasswordSupercar security? Porsche and Lacie unveil “ultra‑secure” encrypted USB stick
For many PC users USB keys must seem like a relic of a bygone age - but for security-conscious workers, keys can...
-

 161How To
161How ToFive bad PC habits many of us STILL have – and how to stop today
Tiny things such as using an admin account on your PC when you don’t need to can give cybercriminals their “way in”....
-
 86Password
86PasswordSmartphone users want more protection – and don’t mind being fingerprinted, says Paypal
Smartphone users want more protection for the data on their cellphone - and are perfectly comfortable being fingerprinted if that’s the best...
-
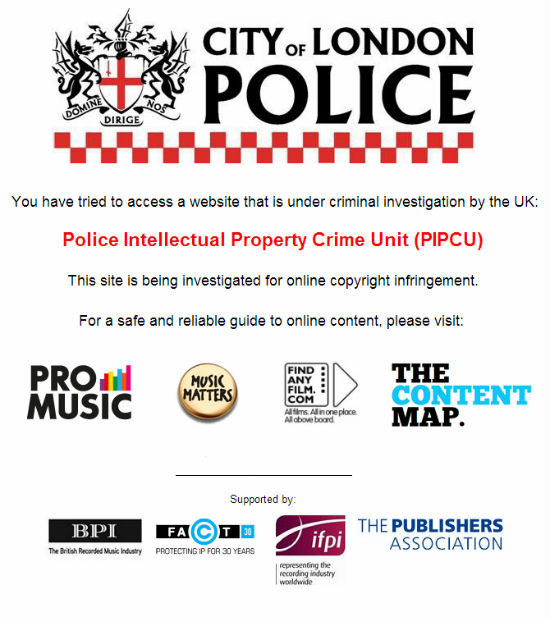
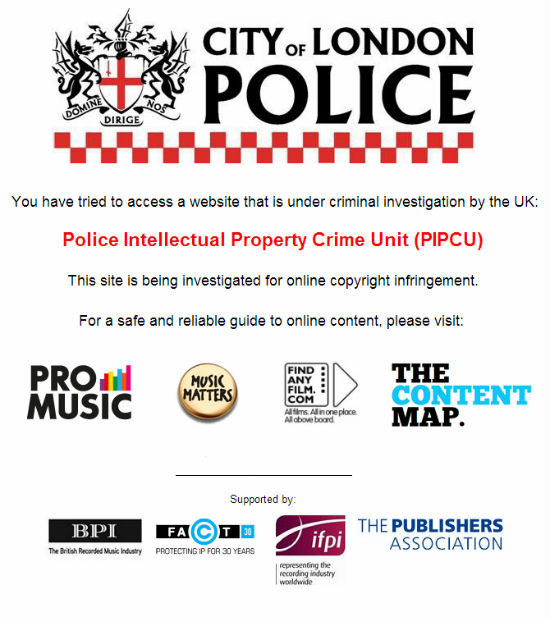 209Cyber Crime
209Cyber CrimeUK Police Orders Registrars to Shutdown Major Torrent Sites
The newly formed Intellectual Property Crime Unit of the City of London Police (IPCU) is in action. In its first operation the...
-

 265News
265NewsSyrian Hacker Dr.SHA6H Hacks and Defaces City of Mansfield, OH Website for Free Syria
Famous Syrian Hacker Dr.SHA6H has hacked and defaced the official website of U.S. City of Mansfield, OH earlier today in support of a...
-

 68Cyber Crime
68Cyber CrimeEU cyber agency warns of “outdated” systems in power plants – and suggests new safety measures
Cyber attacks against Industrial Control Systems pose a risk to power plants and other critical infrastructure - and action is needed to...
-
 71Cyber Crime
71Cyber CrimePonemon study shows costs of cybercrime still rising – each attack now costs $1 million
The costs of cybercrime have continued to rise for victims, for the fourth consecutive year, according to a survey conducted by the...
-

 271News
271NewsAlexa Internet Search Domains Defaced by Anonymous Palestine – KDMS Team
The official domains of Alexa internet search have been hacked and defaced by Anonymous Palestine affiliated group KDMS Team. KDMS hackers left...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




