Featured News
-

 226News
226NewsCyber War Continues as Bangladeshi Hackers Hacks more 200 Indian Websites
As I had reported earlier how Bangladesh Black HAT Hackers (BBHH) have started cyber war against Indian cyber space by hacking 90 Indian...
-
 281Cyber Crime
281Cyber CrimeAlleged Anonymous Hacktivist Arrested for Hacking Texas County Website
Last week the FBI had arrested an alleged hacker who they claim is a member of online hacktivist Anonymous group and took...
-
 178Surveillance
178SurveillanceBrazilian President Rousseff cancels state visit to US over NSA’s spying
Brazilian President Dilma Rousseff has decided to cancel her visit to the U.S. scheduled for October 23 against the NSA’s spying over...
-

 82Cyber Crime
82Cyber CrimeFake card reader “texts” PINs to thieves instantly – and drains bank accounts in three hours
A hacked card reader - similar to the ones used in shops and restaurants - is on sale on Russian forums for...
-
 173Malware
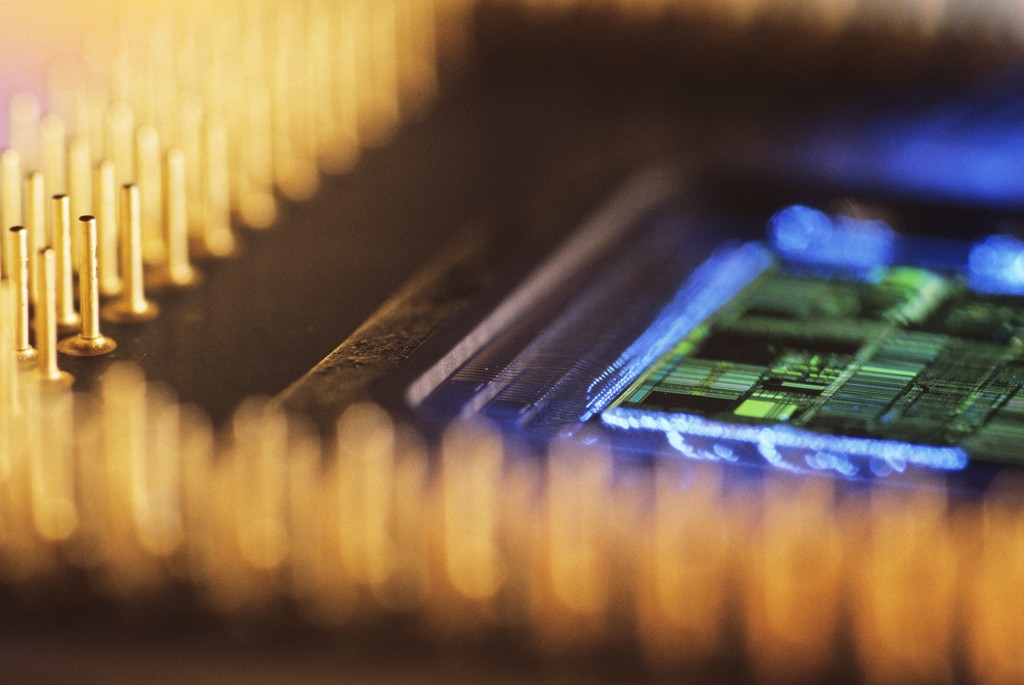
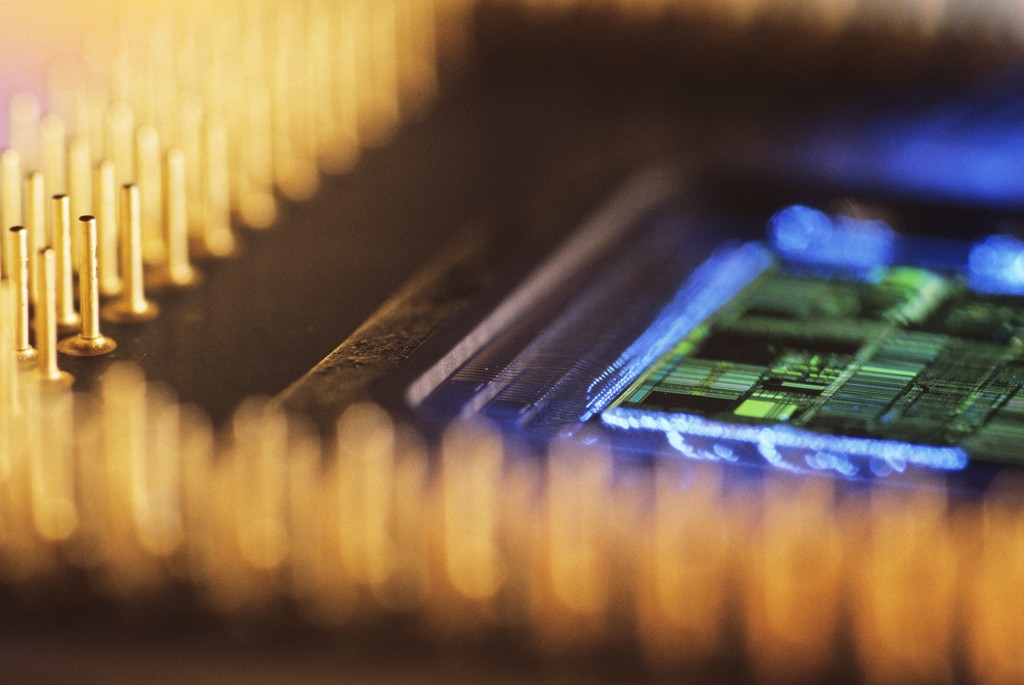
173Malware“Chemical Trojans” baked into circuits could offer invisible way to steal secrets
“Hardware Trojans” could be baked invisibly into circuits by attackers, allowing them to grab secret keys from computer components without fear of...
-
 190Geek
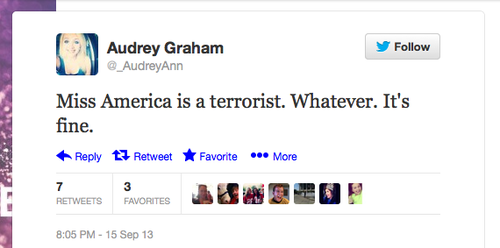
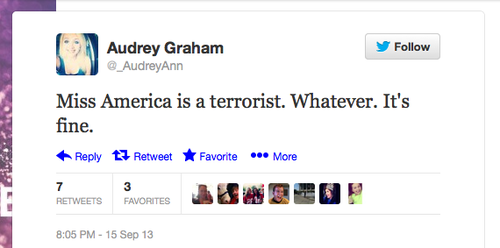
190GeekMiss America Faces Abuse, labeled as Terrorist on Twitter over Indian Descent
Nina Davuluri is a 24 year old Indian descent born in Syracuse, New. The first woman of Indian descent to be crowned...
-

 254News
254NewsOfficial Website of Pakistan International Airlines (PIA) Hacked and Defaced by Ch3rn0by1
The official website of Pakistan International Airlines (PIA) () has been hacked and defaced by a Pakistani hacker going with the handle...
-
 252News
252NewsV. O. Chidambaram Port Trust India Website Hacked by Sudanese Hackers
A Sudanese hacker going with the handle of Al Max Hacker has hacked a high profile official website of V. O. Chidambaram...
-
 360How To
360How ToRemote Desktop (RDP) Hacking 101: I can see your desktop from here!
With malicious remote access attacks of the rise it is time to check your computer's RDP configuration and apply restrictions, like turning...
-

 436Password
436PasswordBrainwave‑scanning hat could be most secure car key ever made
A brainwave scanner could be used as the ultimate biometric “car key” according to researchers at Tottori University - and even prevent...
-

 128Malware
128MalwareA dream job at a luxury store? Nope – just a clever $1.5 million phishing scam
Six Nigerian men have gone on trial today in London for an alleged phishing scam where job offers at London’s exclusive Harrods...
-

 208News
208NewsBan Porn says 3xp1r3 Cyber Army by hacking 30 Pornography websites
A Bangladeshi hacker going with the handle of ExpirED BraiN from 3xp1r3 Cyber Army has hacked and defaced 30 pornography websites, deleting...
-

 309Cyber Crime
309Cyber CrimeGang of 12 arrested for Hacking Bank Computers in London’s Most Sophisticated Plan
A group of twelve hackers have been arrested by the police for hacking into the computers of Santander bank branch in London...
-

 208News
208NewsIran Foreign Ministry Facebook page hacked against police brutality on protesters
An unknown hacker has hacked the official Facebook page of Iranian Foreign Ministry with over 2 million fans against police brutality on...
-
 250News
250NewsBangladeshi Hackers defaces 60 Indian websites, declare Cyber War against Border Security Forces
A group of Bangladeshi hackers going with the handle of Bangladesh Black HAT Hackers (BBHH) have hacked and defaced 60 Indian websites,...
-

 264News
264NewsTurk Hack Team Defaces 750 Websites for #OpNoWar
Turkish hackers from Turk Hack Team going with the handle of Black-Spy and WhooLe have hacked and defaced total 750 random websites...
-

 410Malware
410MalwareTibet‑targeting Mac OS malware rears its head again
A new variant on a family of Mac OS X malware which targets Tibetan activists has been found in the wild and...
-

 117News
117NewsCity of Durham, North Carolina’s Official Website hacked, hacker threatens to kill Obama
A sub-domain which belongs to the official website of City of Durham, North Carolina U.S has been hacked and defaced by a...
-

 265News
265NewsOfficial websites of Avira Anti-Virus Slovenia & United Nation Armenia hacked by Dr.SHA6H
A profile Syrian hacker going with the handle of Dr.SHA6H has hacked the official website of German based Avira antivirus software company designated...
-

 87Cyber Crime
87Cyber CrimePhishing warning after Vodafone hack leaks personal information for 2 million customers
A breach which has leaked personal data for two million Vodafone Germany customers has ben claimed to be the work of an...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




