Featured News
-

 347Cyber Crime
347Cyber CrimeAnonymous Market Place ‘Silk Road’ Domain Seized, Owner Arrested by FBI
The FBI has arrested a 29 year old man in San Francisco, California for allegedly owning and running an underground anonymous marketplace...
-

 284News
284NewsESET Distributors for Israeli, Palestinian and Jewish Community Website Hacked by AnonGhost
The Slovakia based IT Security company ESAT has confirmed that their domains designated as distributors for Israel and Palestine were hacked yesterday....
-
 203Cyber Events
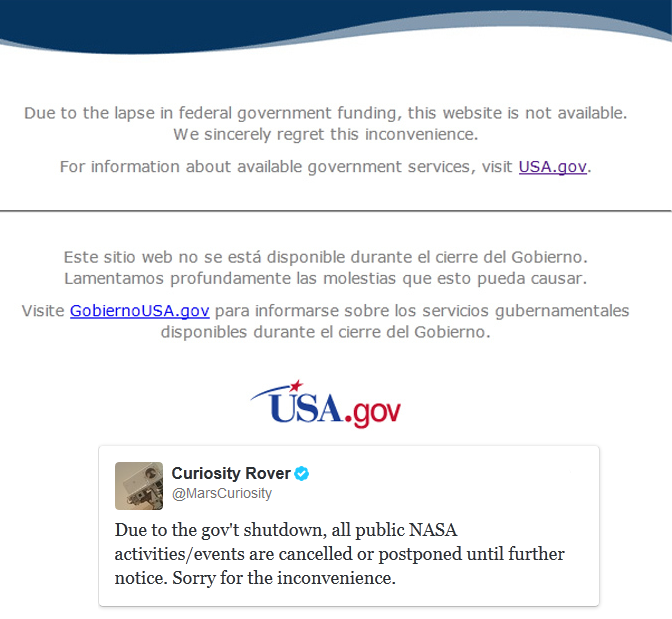
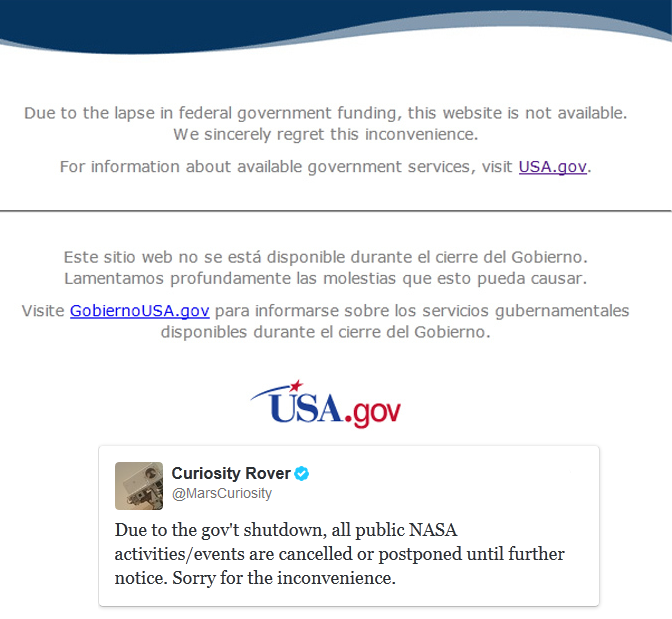
203Cyber EventsNASA and National Park Websites Taken Down Following Government Shutdown
The official websites of NASA (http://www.nasa.gov) and National Park ()have been shutdown until further notice by the United Stated Government. It is...
-

 310Geek
310GeekFacebook Will Send Conversation Data To Select TV Networks
Facebook Will Send Conversation Data To Select TV Networks. According to a recent report in the Wall Street Journal, social networking website...
-
 281News
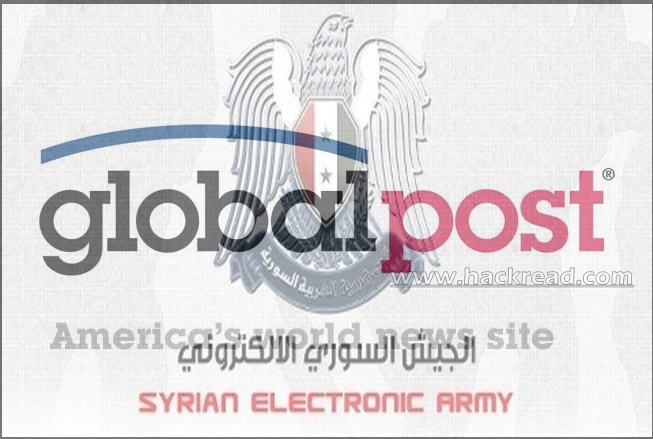
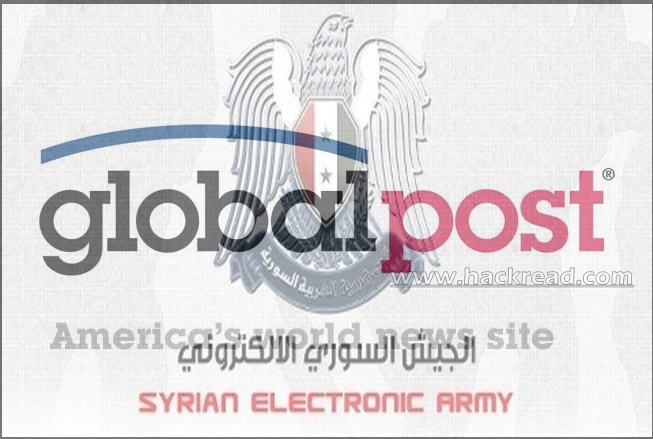
281NewsGlobalPost Twitter and Website Hacked by Syrian Electronic Army
The hardcore supporters of President Bashar Ul Assad from Syrian Electronic Army (SEA) have hacked the official website of U.S. based online news...
-

 180News
180NewsJohn McAfee: My New Gadget Will Defeat NSA and Protect Users Privacy
John McAfee who is the founder of McAfee anti-virus has told that he will unveil a gadget that would enable internet users...
-

 262News
262NewsIsraeli Defense Contractor ISPRA Website Hacked by AnonGhost
The online hacktivist going with the handle of AnonGhost has hacked and defaced a website belonging to an Israel based Defense Contractor ISPRA...
-
 167Cyber Events
167Cyber EventsUnited States Department of Agriculture Website Taken DOWN Following 1st Government Shutdown
The official website of United States Department of Agriculture (USDA) http://www.usda.gov/fundinglapse.htm has been shutdown until further notice by the United Stated Government....
-

 382Password
382PasswordGetting warmer? New Hotspot 2.0 “could offer safer public Wi‑Fi”
Logging into public Wi-Fi hotspots can be risky, particularly for business users with sensitive data on their devices - but a new...
-

 88Password
88PasswordLoose lips sink ships: Apple’s voice assistant Siri lets ANYONE in – again
An Israeli security researcher has found another way round Apple’s Fingerprint ID security system - this time via a two-step lock-screen glitch...
-

 295News
295NewsU.S. Says Iran Hacked Our Navy Computers
Some of the US officials of the Navy have stated that some hackers from Iran have penetrated into the unclassified computer networks...
-

 114Geek
114GeekBritain Military Going Cyber: Hiring IT Warriors for Its Cyber Task Force
Britain Military Going Cyber- Warriors: MoD to hire hundreds of Cyber Geniuses and IT Professionals for their Military Cyber Units. Britain’s ministry...
-

 348Cyber Crime
348Cyber Crime“One click, then boom”: Spear‑phishing could “black out” energy companies, expert warns
Spear-phishing attacks on energy companies are becoming increasingly sophisticated, an expert has warned - and all it takes is one lucky strike...
-
 185News
185NewsFree Kashmir Says Pakistani Hackers after Hacking and Defacing 20,000 Indian Websites
Two Pakistani hackers going with the handle of Dr@cul@ and Muhammad Bilal have hacked and defaced twenty thousand (20,000) Indian websites against...
-

 111News
111NewsDeclassified Documents Show NSA Spied on Martin Luther King Jr, Muhammad Ali and Art Buchwald For Being War Critics
A new declassified document of NSA reveals that the agency spied communications of Muhammad Ali, Art Buchwald and MLK. During the midst...
-

 218Password
218PasswordWalk this way! Forget fingerprints – could our daily habits be the passwords of the future?
One day, your smartphone might “recognise” you by the way you walk, the way your fingers tap on a touchscreen - or...
-

 74Cyber Crime
74Cyber CrimeHelp for the little guys: Small businesses offered “cyber insurance” – starting at $800
Small businesses will be able to buy “cyber assurance” packages to protect against possible losses from cyber attacks - with a British...
-

 104Cyber Crime
104Cyber CrimeMillions of ID records on sale as five big data firms hacked “for months”
An “identity theft service” which specialises in selling personal details gained access to some of the biggest consumer data firms, including Lexis...
-
 146Geek
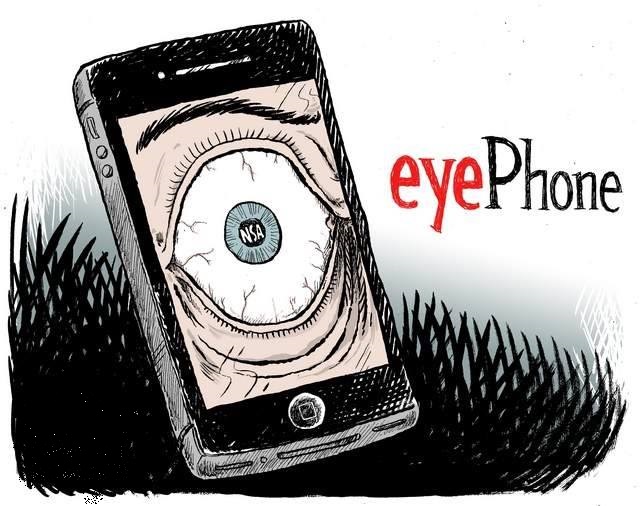
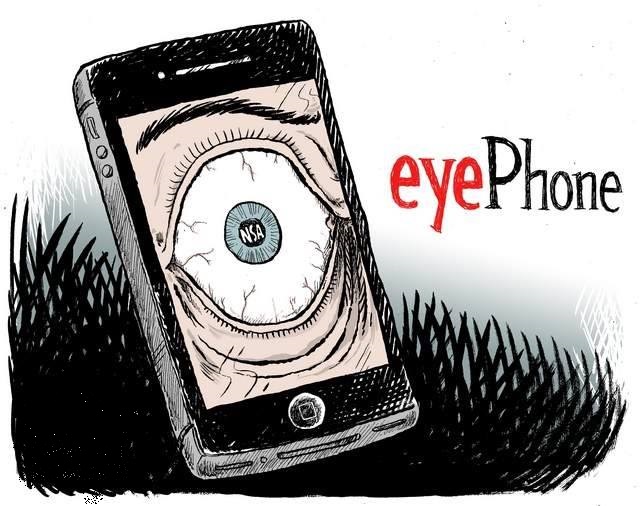
146GeekApple Allegedly Admits: iPhone 5s Fingerprint Database To Be Shared With NSA
The following report was taking from an independent news source, original report is available @ National Report. We at HackRead do not...
-

 200News
200NewsU.S. Senator asks if FBI can get iPhone 5S fingerprint data via Patriot Act
Since Senator. Al- Franken has become of part of the United States Senate, he has been the Chairman of Senate Judiciary Subcommittee...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks




