Featured News
-

 217News
217NewsDatabase of Ubuntu Forum Breached, hackers got access to every user’s local username, password, and email address.
I am breaking this news for you that operating system Ubuntu has got its forum hacked as a result of a breach...
-

 285News
285News220 websites hacked and defaced by Turk Hack Team
Famous Turkish hackers from Turk Hack Team is back with another hack, this time one of their hacker going with the handle...
-
 227News
227News473 British websites hacked by Pak Cyber Eaglez
A well known Pakistani hacker Sizzling Soul from Pak Cyber Eaglez is back in news with his latest attack in which 473 British based...
-
 289News
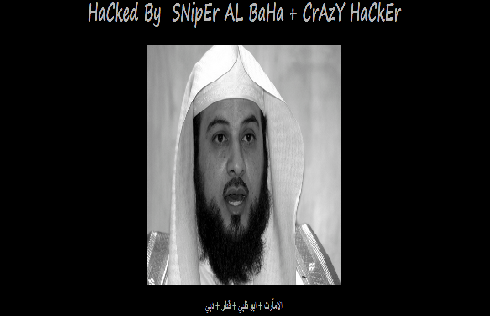
289NewsWebsite of National Transport Authority UAE hacked & defaced by Saudi hackers
Three Saudi hackers going with the handles of SNipEr AL BaHa, CrAzY HaCkEr and SNIPER MAKKA have collectively hacked and defaced the official...
-

 213News
213NewsWebsite of Pakistani Entertainment Channel HUM TV Hacked by MadcodE Haxor
A Pakistani hacker going with the handle of MadcodE Haxor has hacked and defaced the official website of Pakistan based famous entertainment TV...
-

 76Cyber Crime
76Cyber CrimeNew ransomware uses Organized Crime unit threat to scare users
New “ransomware” attempts to terrify users into paying up by using the name of Britain’s SOCA crime unit - the Serious Organized...
-

 335Cyber Crime
335Cyber CrimeMan in UAE arrested for uploading assault video on YouTube
The Police in Dubai have arrested an Indian national for filming and uploading a video on YouTube of a senior government official...
-
 249News
249NewsAnonymous hacks, leaks emails and passwords of US Congress
Anonymous hackers have claimed to breached the official website of US congress and its mail server (mail.house.gov and senate.gov), as a result around...
-
 280News
280NewsFEMA hacked: Anonymous hacks US server in defense of Snowden and against threats from agency
A group of Anonymous hacker has said to hack into a server used by Federal Emergency Management. According to them, the data...
-

 94Kids Online
94Kids OnlineChildren are “the enemy” of good IT security
“Children are a formidable adversary - unlike any other,” says Microsoft security researcher Stuart Schechter, in a paper to be presented at...
-

 90Cyber Crime
90Cyber Crime“Black swan” warning as cybercrime hits half of world stock exchanges
More than half of securities exchanges around the world faced cyber attacks last year, according to a paper released by the International...
-

 205Surveillance
205SurveillanceBlackBerry allows Indian government a direct access to emails and Chats
Government agencies in India are now allowed to access your blackberry devices directly, allowing them to track conversations, emails and attachments sent...
-

 451News
451NewsTrueCaller Phone Directory Hacked, Database with Millions of Facebook, Twitter, Linkedin & Gmail accounts dumped
Syrian hackers known for their hardcore support for President Bashar Ul Assad from Syrian Electronic Army are back in news, this time...
-

 321Password
321PasswordHow to create strong passwords (without driving yourself mad)
There are a few tricks to making passwords that will at least slow down cybercriminals - buying you time to reset your...
-
 90Password
90PasswordTumblr warns users over iPhone app password danger
Micro-blogging site Tumblr has warned users that passwords can be “sniffed” from its iPhone and iPad apps - and issued a “very...
-

 419Cyber Crime
419Cyber CrimeTexas restaurant sues credit card giant after point‑of‑sale hack
A Texas restaurant chain is suing one of its suppliers over a point-of-sale system which allowed hackers to steal customer data -...
-

 344Cyber Crime
344Cyber CrimeHacked signal‑boosters let cybercriminals “listen in” on cellphones
A $250 signal-boosting device for cellphone users can be hacked, two researchers claim - offering total access to phone calls, internet use...
-

 83Malware
83Malware“Warning fatigue” means browser users ignore up to 70% of security alerts
Browser security warnings can work to protect users from phishing and malware sites - but “warning fatigue” means important alerts over site...
-
 101Password
101PasswordFacial recognition system “reads” blood vessels for unbreakable security
A new biometrics system could “read” blood vessels under the skin using thermal imaging cameras - a system which its inventors claim...
-

 298News
298NewsLulzSecPeru defaces, leaks data of Peru’s government portals for using NSA’s backed hosting service
LulzSecPeru known as one of the most skilled online hackavists are back, this time by the hackers have hacked and defaced the...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




