Featured News
-

 3.1KVulnerabilities
3.1KVulnerabilitiesCritical Jenkins Vulnerability Exposes Servers to RCE Attacks – Patch ASAP!
The maintainers of the open-source continuous integration/continuous delivery and deployment (CI/CD) automation software Jenkins have resolved nine security flaws, including a critical...
-
 792Malware
792MalwareChina-backed Hackers Hijack Software Updates to Implant “NSPX30” Spyware
A previously undocumented China-aligned threat actor has been linked to a set of adversary-in-the-middle (AitM) attacks that hijack update requests from legitimate...
-
 2.2KMalware
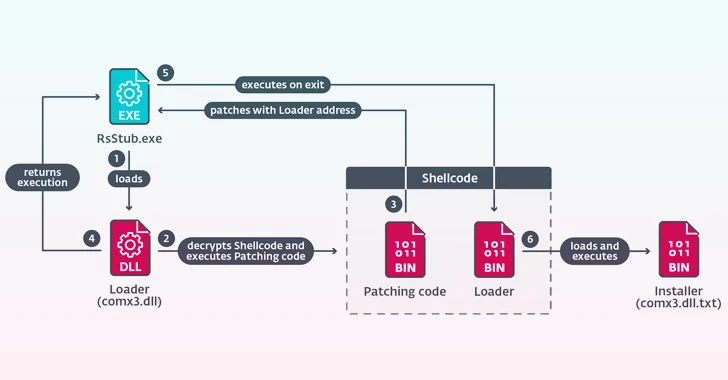
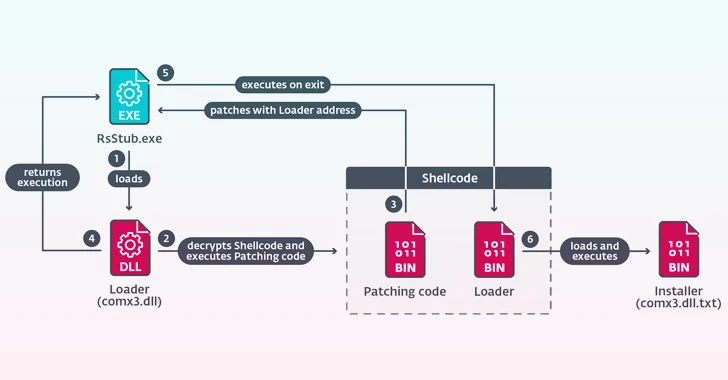
2.2KMalwareNew CherryLoader Malware Mimics CherryTree to Deploy PrivEsc Exploits
A new Go-based malware loader called CherryLoader has been discovered by threat hunters in the wild to deliver additional payloads onto compromised...
-

 418Data Breach
418Data BreachTech Giant HP Enterprise Hacked by Russian Hackers Linked to DNC Breach
Hackers with links to the Kremlin are suspected to have infiltrated information technology company Hewlett Packard Enterprise’s (HPE) cloud email environment to...
-
 304Vulnerabilities
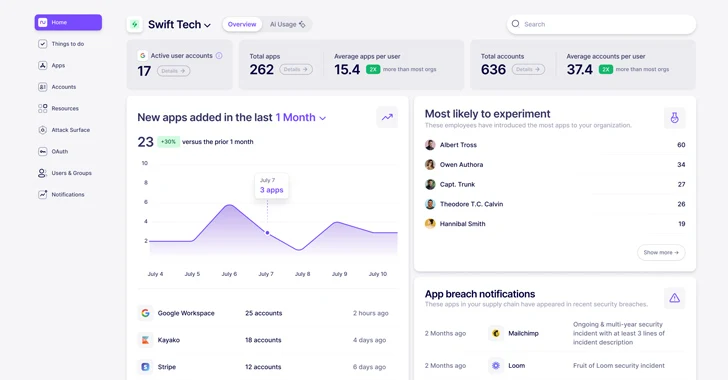
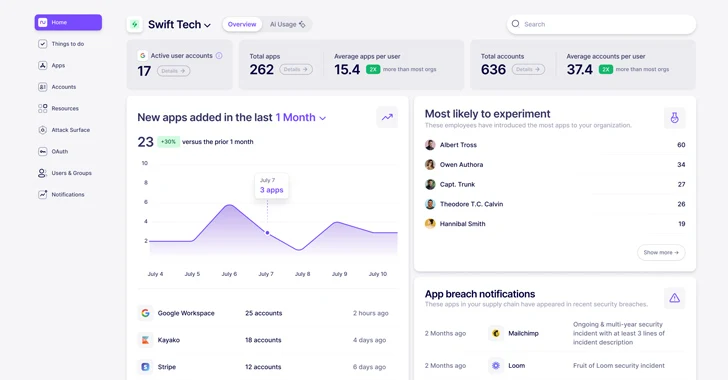
304VulnerabilitiesWhat is Nudge Security and How Does it Work?
In today’s highly distributed workplace, every employee has the ability to act as their own CIO, adopting new cloud and SaaS technologies...
-

 2.9KMalware
2.9KMalwareKasseika Ransomware Using BYOVD Trick to Disarm Security Pre-Encryption
The ransomware group known as Kasseika has become the latest to leverage the Bring Your Own Vulnerable Driver (BYOVD) attack to disarm...
-

 1.1KVulnerabilities
1.1KVulnerabilitiesThe Unknown Risks of The Software Supply Chain: A Deep-Dive
In a world where more & more organizations are adopting open-source components as foundational blocks in their application’s infrastructure, it’s difficult to...
-

 1.6KData Breach
1.6KData BreachU.S., U.K., Australia Sanction Russian REvil Hacker Behind Medibank Breach
Governments from Australia, the U.K., and the U.S. have imposed financial sanctions on a Russian national for his alleged role in the...
-
 4.2KVulnerabilities
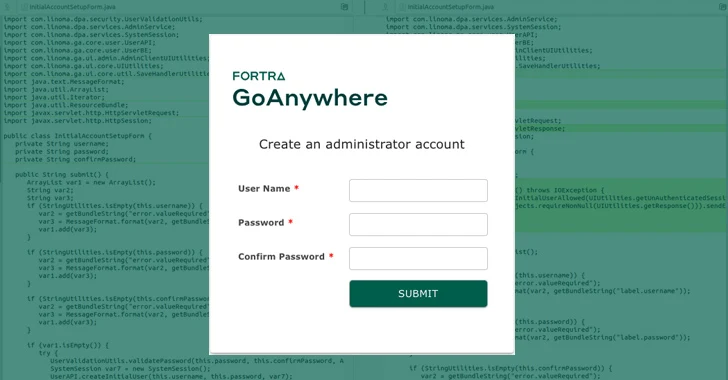
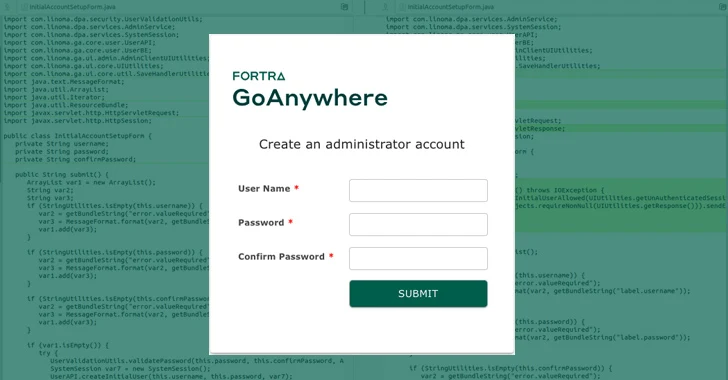
4.2KVulnerabilitiesPatch Your GoAnywhere MFT Immediately – Critical Flaw Lets Anyone Be Admin
A critical security flaw has been disclosed in Fortra’s GoAnywhere Managed File Transfer (MFT) software that could be abused to create a...
-
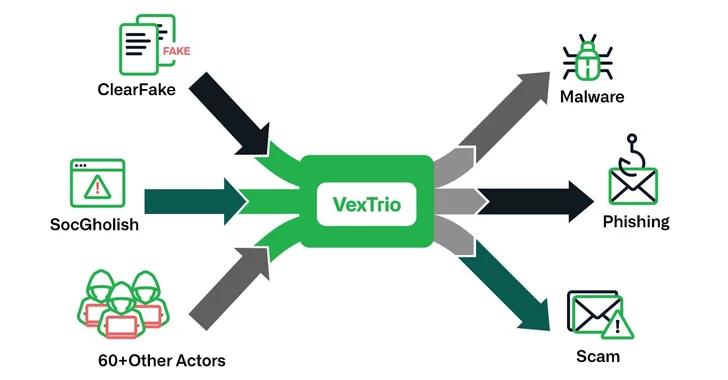
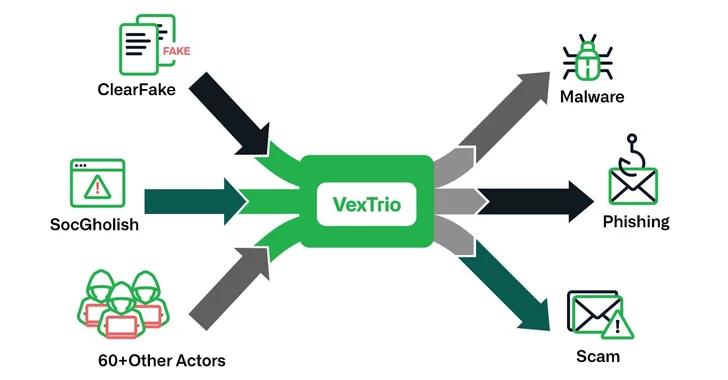 4.3KMalware
4.3KMalwareVexTrio: The Uber of Cybercrime – Brokering Malware for 60+ Affiliates
The threat actors behind ClearFake, SocGholish, and dozens of other actors have established partnerships with another entity known as VexTrio as part...
-
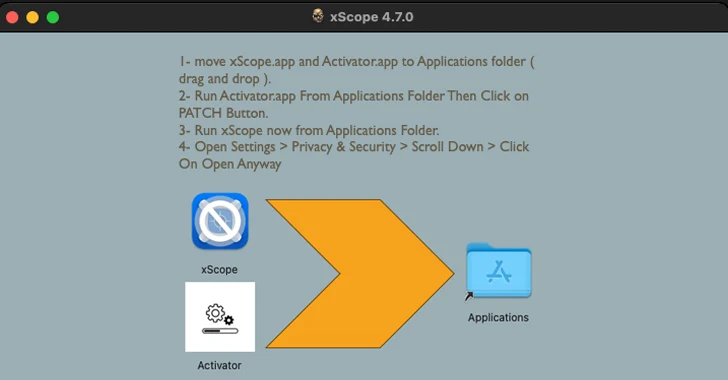
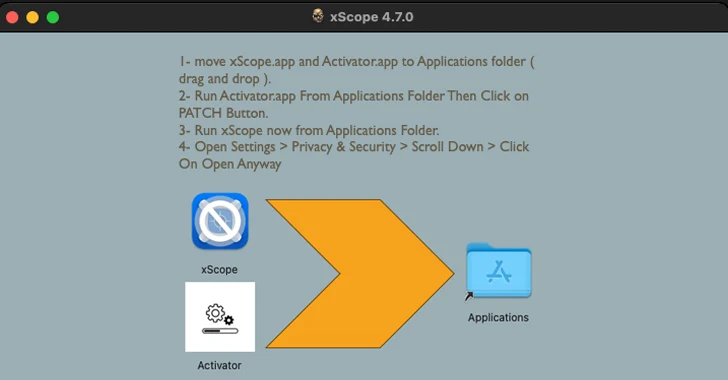 3.5KMalware
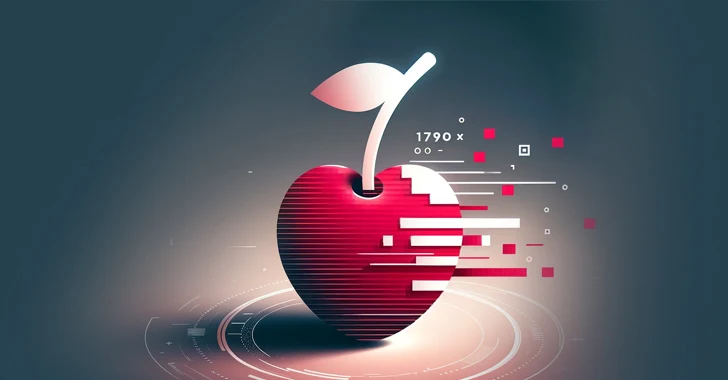
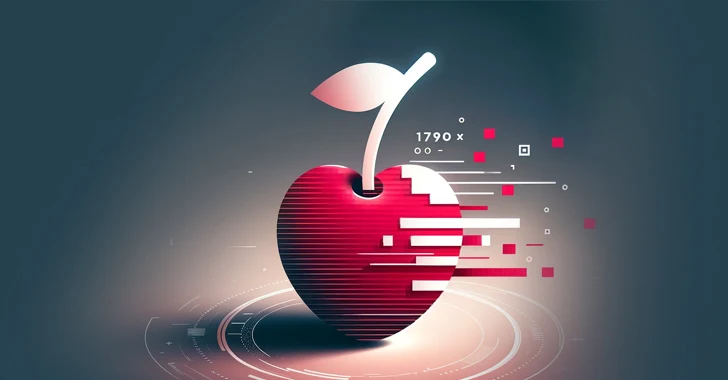
3.5KMalware“Activator” Alert: MacOS Malware Hides in Cracked Apps, Targeting Crypto Wallets
Cracked software have been observed infecting Apple macOS users with a previously undocumented stealer malware capable of harvesting system information and cryptocurrency...
-

 2.0KData Breach
2.0KData BreachBreachForums Founder Sentenced to 20 Years of Supervised Release, No Jail Time
Conor Brian Fitzpatrick has been sentenced to time served and 20 years of supervised release for his role as the creator and...
-

 1.8KVulnerabilities
1.8KVulnerabilities~40,000 Attacks in 3 Days: Critical Confluence RCE Under Active Exploitation
Malicious actors have begun to actively exploit a recently disclosed critical security flaw impacting Atlassian Confluence Data Center and Confluence Server, within...
-
 3.6KData Security
3.6KData SecurityHow to steal Windows password via Outlook email exploiting vulnerabilities in Windows Performance Analyzer (WPA) and File Explorer
Varonis Threat Labs has uncovered a significant vulnerability in Microsoft Outlook (CVE-2023-35636) that allows attackers to access NTLM v2 hashed passwords. This...
-

 882Malware
882MalwareNorth Korean Hackers Weaponize Research Lures to Deliver RokRAT Backdoor
Media organizations and high-profile experts in North Korean affairs have been at the receiving end of a new campaign orchestrated by a...
-

 4.7KVulnerabilities
4.7KVulnerabilitiesMavenGate Attack Could Let Hackers Hijack Java and Android via Abandoned Libraries
Several public and popular libraries abandoned but still used in Java and Android applications have been found susceptible to a new software...
-

 1.6KMalware
1.6KMalwareNS-STEALER Uses Discord Bots to Exfiltrate Your Secrets from Popular Browsers
Cybersecurity researchers have discovered a new Java-based “sophisticated” information stealer that uses a Discord bot to exfiltrate sensitive data from compromised hosts....
-

 520Vulnerabilities
520Vulnerabilities52% of Serious Vulnerabilities We Find are Related to Windows 10
We analyzed 2,5 million vulnerabilities we discovered in our customer’s assets. This is what we found. Digging into the data The dataset...
-

 773Malware
773MalwareApache ActiveMQ Flaw Exploited in New Godzilla Web Shell Attacks
Cybersecurity researchers are warning of a “notable increase” in threat actor activity actively exploiting a now-patched flaw in Apache ActiveMQ to deliver...
-
 1.6KCyber Attack
1.6KCyber AttackCISA Issues Emergency Directive to Federal Agencies on Ivanti Zero-Day Exploits
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday issued an emergency directive urging Federal Civilian Executive Branch (FCEB) agencies to...
The Latest
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor




