Featured News
-
 3.5KMalware
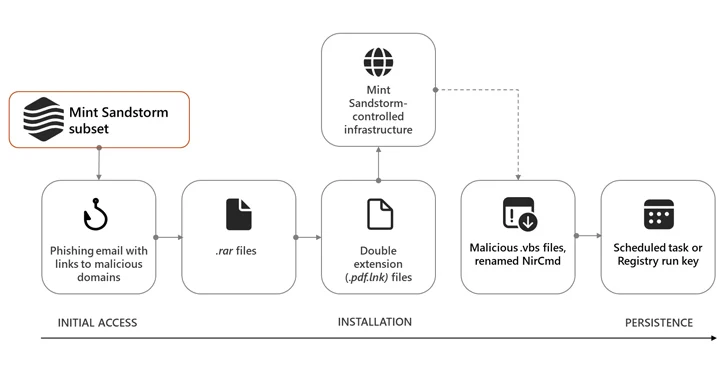
3.5KMalwareIranian Hackers Masquerade as Journalists to Spy on Israel-Hamas War Experts
High-profile individuals working on Middle Eastern affairs at universities and research organizations in Belgium, France, Gaza, Israel, the U.K., and the U.S....
-

 4.1KMalware
4.1KMalwareFeds Warn of AndroxGh0st Botnet Targeting AWS, Azure, and Office 365 Credentials
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI) warned that threat actors deploying the AndroxGh0st...
-
 1.4KVulnerabilities
1.4KVulnerabilitiesGoogle Chrome Browser Zero-Day Vulnerability Exploited in Wild – Emergency Patch!
Google Chrome has released its stable channel update version 20.0.6099.234 for Mac, 120.0.6099.224 for Linux, and 120.0.6099.224/225 for Windows. However, Google stated...
-

 3.6KVulnerabilities
3.6KVulnerabilitiesGitHub Rotates Keys After High-Severity Vulnerability Exposes Credentials
GitHub has revealed that it has rotated some keys in response to a security vulnerability that could be potentially exploited to gain...
-

 941Vulnerabilities
941VulnerabilitiesCitrix, VMware, and Atlassian Hit with Critical Flaws — Patch ASAP!
Citrix is warning of two zero-day security vulnerabilities in NetScaler ADC (formerly Citrix ADC) and NetScaler Gateway (formerly Citrix Gateway) that are...
-
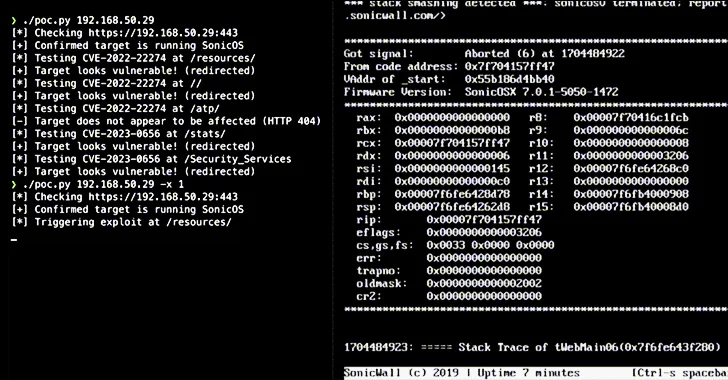
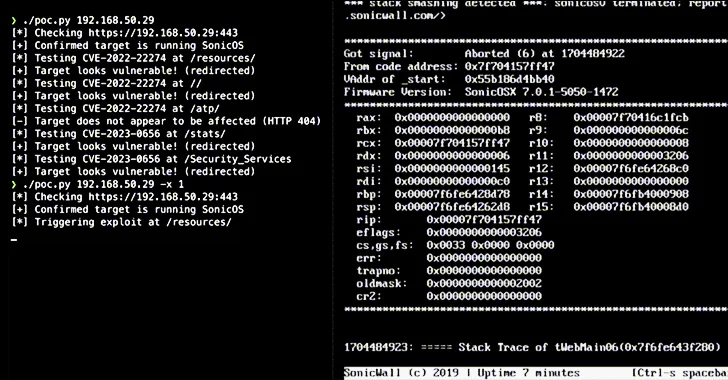 3.2KVulnerabilities
3.2KVulnerabilitiesAlert: Over 178,000 SonicWall Firewalls Potentially Vulnerable to Exploits – Act Now
Over 178,000 SonicWall firewalls exposed over the internet are exploitable to at least one of the two security flaws that could be...
-

 2.5KVulnerabilities
2.5KVulnerabilitiesCase Study: The Cookie Privacy Monster in Big Global Retail
Explore how an advanced exposure management solution saved a major retail industry client from ending up on the naughty step due to...
-

 1.1KMalware
1.1KMalwareRemcos RAT Spreading Through Adult Games in New Attack Wave
The remote access trojan (RAT) known as Remcos RAT has been found being propagated via webhards by disguising it as adult-themed games...
-

 801Malware
801MalwareHackers Weaponize Windows Flaw to Deploy Crypto-Siphoning Phemedrone Stealer
Threat actors have been observed leveraging a now-patched security flaw in Microsoft Windows to deploy an open-source information stealer called Phemedrone Stealer....
-

 3.9KIncidents
3.9KIncidentsHow to exploit Windows Defender Antivirus to infect a device with malware
Trend Micro’s recent threat hunting efforts have uncovered active exploitation of CVE-2023-36025, a vulnerability in Microsoft Windows Defender SmartScreen, by a new...
-
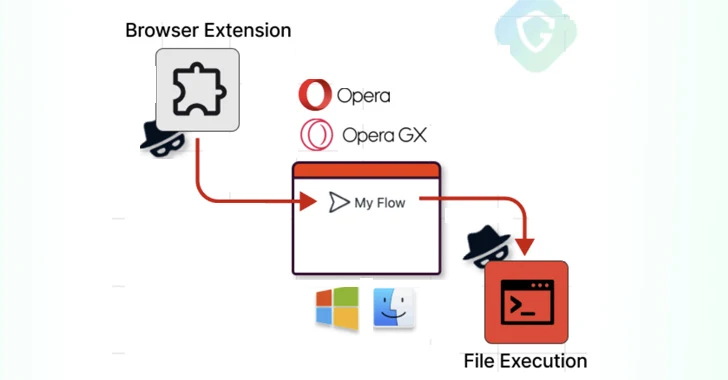
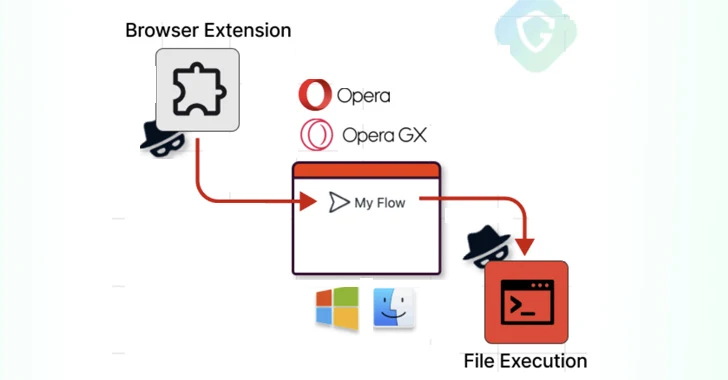 1.8KVulnerabilities
1.8KVulnerabilitiesOpera MyFlaw Bug Could Let Hackers Run ANY File on Your Mac or Windows
Cybersecurity researchers have disclosed a now-patched security flaw in the Opera web browser for Microsoft Windows and Apple macOS that could be...
-

 795Vulnerabilities
795VulnerabilitiesHigh-Severity Flaws Uncovered in Bosch Thermostats and Smart Nutrunners
Multiple security vulnerabilities have been disclosed in Bosch BCC100 thermostats and Rexroth NXA015S-36V-B smart nutrunners that, if successfully exploited, could allow attackers...
-
 1.4KVulnerabilities
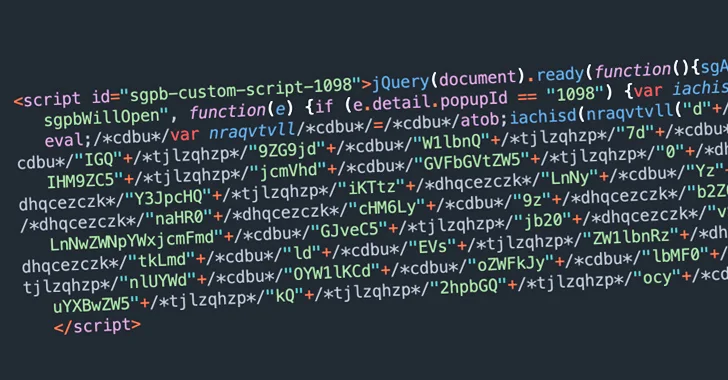
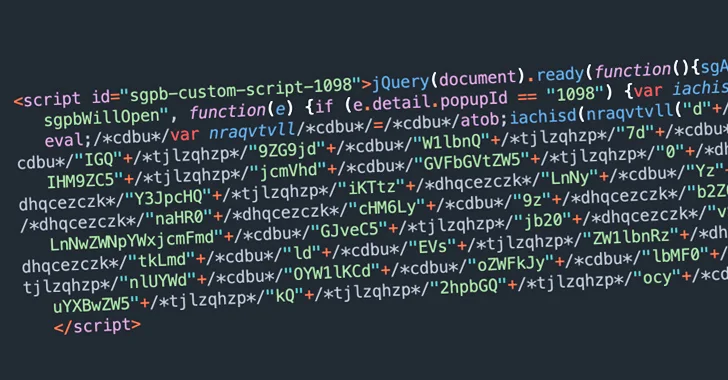
1.4KVulnerabilitiesBalada Injector Infects Over 7,100 WordPress Sites Using Plugin Vulnerability
Thousands of WordPress sites using a vulnerable version of the Popup Builder plugin have been compromised with a malware called Balada Injector....
-
 4.2KCyber Attack
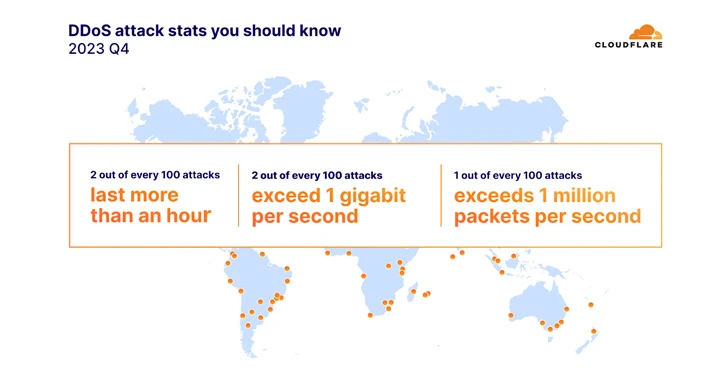
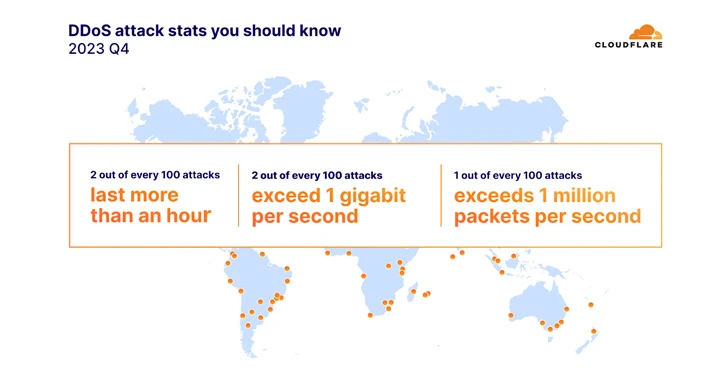
4.2KCyber AttackDDoS Attacks on the Environmental Services Industry Surge by 61,839% in 2023
The environmental services industry witnessed an “unprecedented surge” in HTTP-based distributed denial-of-service (DDoS) attacks, accounting for half of all its HTTP traffic....
-
 5.1KVulnerabilities
5.1KVulnerabilitiesNew Findings Challenge Attribution in Denmark’s Energy Sector Cyberattacks
The cyber attacks targeting the energy sector in Denmark last year may not have had the involvement of the Russia-linked Sandworm hacking...
-

 4.2KVulnerabilities
4.2KVulnerabilitiesCritical RCE Vulnerability Uncovered in Juniper SRX Firewalls and EX Switches
Juniper Networks has released updates to fix a critical remote code execution (RCE) vulnerability in its SRX Series firewalls and EX Series...
-
 2.2KData Breach
2.2KData Breach29-Year-Old Ukrainian Cryptojacking Kingpin Arrested for Exploiting Cloud Services
A 29-year-old Ukrainian national has been arrested in connection with running a “sophisticated cryptojacking scheme,” netting them over $2 million (€1.8 million)...
-

 1.5KVulnerabilities
1.5KVulnerabilitiesNation-State Actors Weaponize Ivanti VPN Zero-Days, Deploying 5 Malware Families
As many as five different malware families were deployed by suspected nation-state actors as part of post-exploitation activities leveraging two zero-day vulnerabilities...
-
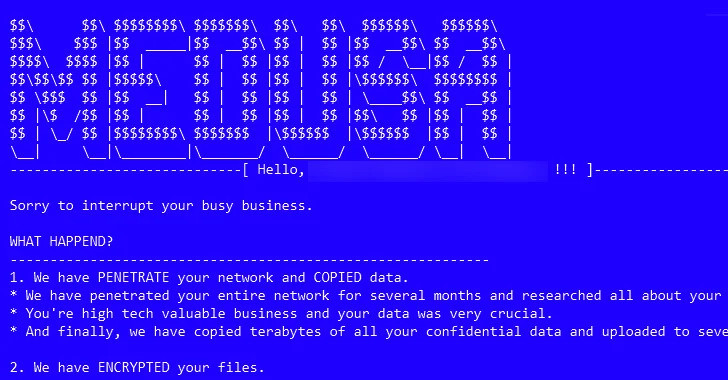
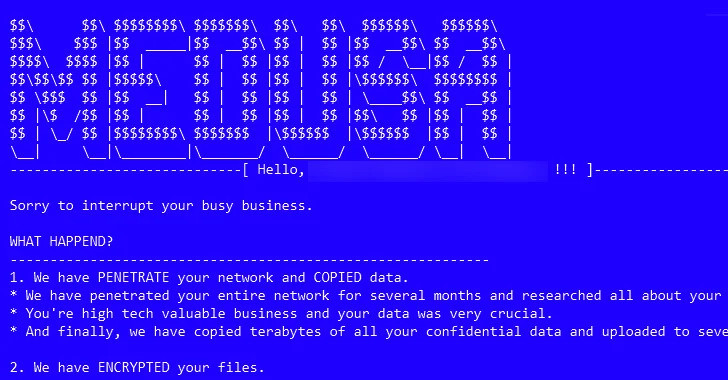 3.4KMalware
3.4KMalwareMedusa Ransomware on the Rise: From Data Leaks to Multi-Extortion
The threat actors associated with the Medusa ransomware have ramped up their activities following the debut of a dedicated data leak site...
-

 2.8KMalware
2.8KMalwareCryptominers Targeting Misconfigured Apache Hadoop and Flink with Rootkit in New Attacks
Cybersecurity researchers have identified a new attack that exploits misconfigurations in Apache Hadoop and Flink to deploy cryptocurrency miners within targeted environments....
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




