Search results for "AWS"
-

 255News
255NewsAnonymous Hack Italian Job Portals, Leak Trove of Data Against New Labour Laws
Anonymous has leaked personal details of CEOs, managers and other employees of hotshot companies in Italy to protest against the new labour...
-
 105Data Security
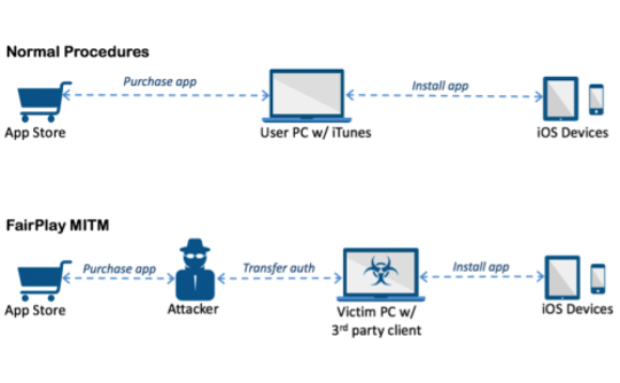
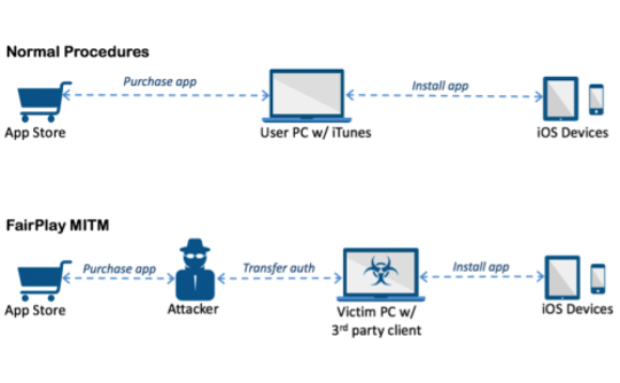
105Data SecurityAceDeceiver: First iOS Trojan Exploiting Apple DRM Design Flaws to Infect Any iOS Device
We’ve discovered a new family of iOS malware that successfully infected non-jailbroken devices we’ve named “AceDeceiver”. What makes AceDeceiver different from previous iOS...
-

 281News
281NewsHackers can change election result using flaws in Electronic Voting Machines
Hackers state that electronic voting machines in Brazil are deliberately flawed with serious vulnerabilities The electronic ballot boxes are controversial in Brazil,...
-
 261Vulnerabilities
261Vulnerabilities0-day critical flaws in mobile modems allow hackers to take over your PC
The Russian security tester Timur Yunusov has discovered critical flaw affecting routers and 3G and 4G mobile modems from Huawei, ZTE, Gemtek,...
-

 337Hacked
337Hacked9 Out Of 10 Windows Security Flaws Could Be Avoided By Just Removing Admin Rights
Short Bytes: The security firm Avecto has just released its security report on Windows operating system. The report outlines an important result...
-
 342Hacked
342HackedThe Anatomy of Copyright Lawsuits – Number Of People Sued Drops By 84% Since 2010
Image: Wtamu.edu Short Bytes: A report published by Mathew Sag claims that the number of people sued for illegal file sharing in...
-

 151Vulnerabilities
151VulnerabilitiesGoogle hacker criticized TrendMicro for critical flaws
A hacker with Google Project Zero research team, publicly disclosed critical vulnerabilities in the TrendMicro Antivirus. Tavis Ormandy, a researcher with Google’s...
-

 230Data Security
230Data SecurityCommon payment processing protocols found to be full of flaws
Stealing PINs and pillaging bank accounts are both trivial. Credit card users could have their PINs stolen, and merchants could have their bank...
-

 254Hacked
254HackedProposed Laws Can Result In Banning Tor And Free Wi-Fi In France
Short Bytes: The French government is actively researching the options to make its surveillance options more effective. In the wake of recent...
-
 242Data Security
242Data SecurityNSA claims it shares 91% of security flaws with its manufactures
NSA discloses 91 percent of the zero-day bugs it finds in the online systems to its manufacturers while it keeps the 9...
-
 105Vulnerabilities
105VulnerabilitiesAcademics Find Critical Flaws in Self-Encrypting Hardware Drives
Some consumer-grade, self-encrypting external hard drives are littered with security vulnerabilities that render their encryption an afterthought. An academic paper published in...
-

 319Data Security
319Data SecurityHackers Can Exploit Security Flaws In Drones To Hijack Flight Controller
Security flaws have been found in drones that could allow hackers to target and attack the flight controller which includes numerous sensors...
-

 133Incidents
133IncidentsApple hack exposes flaws in building apps in China
China’s “Great Firewall” may have been partly to blame for the first major attack on Apple Inc’s (AAPL.O) App Store, but experts...
-

 209Geek
209GeekAmazon Launches AWS Device Farm, Now Test Your Apps on Real Devices
To benefit the hard-working app developers and programmers, Amazon is starting a cloud-based service named AWS Device Farm. AWS Device Farm will...
-

 237Data Security
237Data SecurityUnpatched Security Flaws Openly Solicited by US Navy
Governments unsurprisingly are trying to buy unpatched security exploits in the name of surveillance or cyber defence but refrain from admitting it....
-

 317Surveillance
317SurveillanceNew Laws Force Google, Snapchat, WhatsApp to share chats with GCHQ
Summary: New surveillance laws will be formed to force the leading Internet firms such as Apple, Facebook and Google to hand over encrypted...
-

 112Privacy
112PrivacyUK government amends hacking laws to give intelligence service immunity
The British government has passed legislation amending the Computer Misuse Act to prevent GCHQ, the police and intelligence services from prosecution over...
-
 296News
296NewsFacebook to face lawsuit for ‘reading’ users’ messages.
JUDGE SLAPS FACEBOOK WITH PRIVACY VIOLATION RULING. U.S District Judge Phyllis Hamilton ruled thatFacebook must “face the consequences” of violating its...
-

 81Cyber Crime
81Cyber CrimeBelkin’s ‘Smart Home’ system has security flaws which could ‘black out’ homes – or start fires
Belkin’s WeMo home automation systems contain multiple vulnerabilities which could allow attackers to remotely control devices attached to a WeMo system -...
-

 110Malware
110MalwareCritical IE and other flaws discovered. Patch your systems now, says Microsoft
If your system administrator looks a little frazzled this week, be nice to him or her and don't grumble too much about...
-

 222Cyber Events
222Cyber EventsRedHack Hactivists Join hands with activists for a protest against Internet Censorship Laws in Turkey
The Turkish parliament has accepted a highly controversial reversal to a cyber law, granting authorities full power to block certain websites in...






