Search results for "AWS"
-

 195Cyber Crime
195Cyber CrimeUS rules on reporting cybersecurity flaws set to change according to source
Cyber vulnerability hoarding? The US government publishes its Vulnerabilities Equities Policy (VEP) and describes the process by which cyber flaws found by...
-

 236Hacked
236HackedLinux Security Alert: Tons Of Linux Kernel USB Flaws Found By Google Hacker
The general perception of the public is that Linux and macOS operating systems are far more secure as compared to Windows. While...
-

 110Vulnerabilities
110VulnerabilitiesFlaws in IEEE P1735 electronics standard expose intellectual property
Experts discovered flaws in IEEE P1735 electronics standard, which describes methods for encrypting electronic-design intellectual property (IP). Crypto flaws in the IEEE P1735 electronics standard expose highly-valuable...
-

 128Vulnerabilities
128VulnerabilitiesVulnerabilities in Google Issue Tracker exposed details about unpatched flaws
A flaw in the Google Issue Tracker, also known as the “Buganizer,” might have exposed details about unpatched flaws listed in the...
-
Security Tools
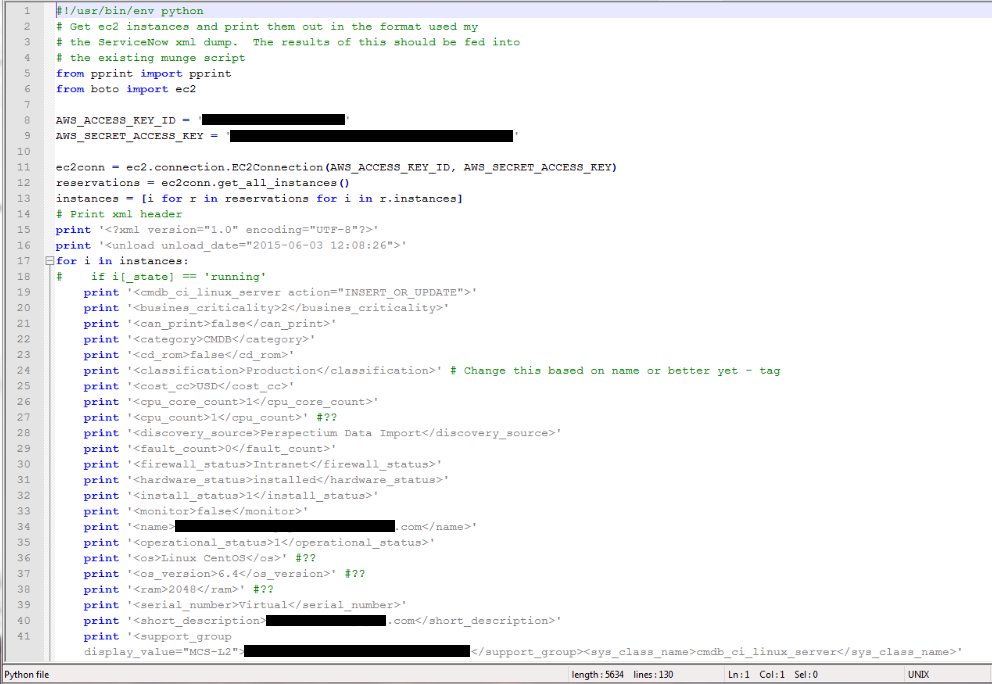
Cloud Security Suite – One stop tool for auditing the security posture of AWS infrastructure
One stop tool for auditing the security posture of AWS. Pre-requisites Python 2.7 pip git Installation git clone https://github.com/SecurityFTW/cs-suite.git cd cs-suite/ sudo...
-
 248Vulnerabilities
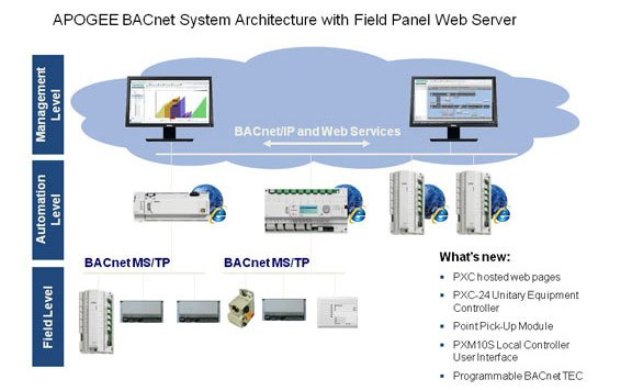
248VulnerabilitiesFlaws in Siemens Building Automation Controllers open to hack. Fix them asap
Siemens has released a firmware update that addresses two vulnerabilities in its BACnet Field Panel building automation controllers. This week Siemens has...
-
Security Tools
AWSBucketDump – Security Tool to Look For Interesting Files in S3 Buckets
AWSBucketDump is a tool to quickly enumerate AWS S3 buckets to look for loot. It’s similar to a subdomain bruteforcer but is...
-

 285News
285NewsGoogle Found 7 Security Flaws In Dnsmasq Network Software
Security researchers have discovered not one or two, but a total of seven security vulnerabilities in the popular open source Dnsmasq network...
-

 155Vulnerabilities
155VulnerabilitiesCISCO addressed several critical IOS flaws that expose devices to remote attacks
Cisco has released security updates for its IOS Operating System to fix more than a dozen critical and high severity vulnerabilities. Cisco...
-
 265Vulnerabilities
265VulnerabilitiesViacom left the keys of its digital kingdom on a publicly exposed AWS S3 bucket
The security researcher Chris Vickery discovered that Media giant Viacom left sensitive data and secret access key on unsecured Amazon AWS S3 bucket....
-

 317Geek
317GeekGet $1M for reporting zero-day flaws in Tor to “help Govt fight crime”
Usually, a bug bounty program helps companies secure their software and products from zero day vulnerabilities that can cause massive damage if cyber...
-

 334Geek
334GeekMicrosoft Patches 85 Flaws, One Allowed FinFisher Spyware Installation
Microsoft Releases Patch for Dangerous .NET Vulnerability in Latest Security Updates. Microsoft has finally patched a vulnerability in Microsoft Windows that was...
-
 258Geek
258GeekYouTube MP3 Converter Site Shut Down After Labels Win Lawsuit
There are several websites allowing users to download YouTube videos such as odownloader but in 2016, Youtube-mp3.org (YTMP3), a popular YouTube-ripping site...
-

 210News
210NewsTwo Critical Zero-Day Flaws Came Out In Foxit PDF Reader
Are you using Foxit PDF Reader? If so, then you need to look back. Security researchers discovered two critical security vulnerabilities Zero...
-

 276Data Security
276Data SecurityFlaws in ISP gateways let attackers remotely tap internet traffic
Defcon is the most important event for the DIY hacking community and this year too, the conference was held in the same...
-
 187Vulnerabilities
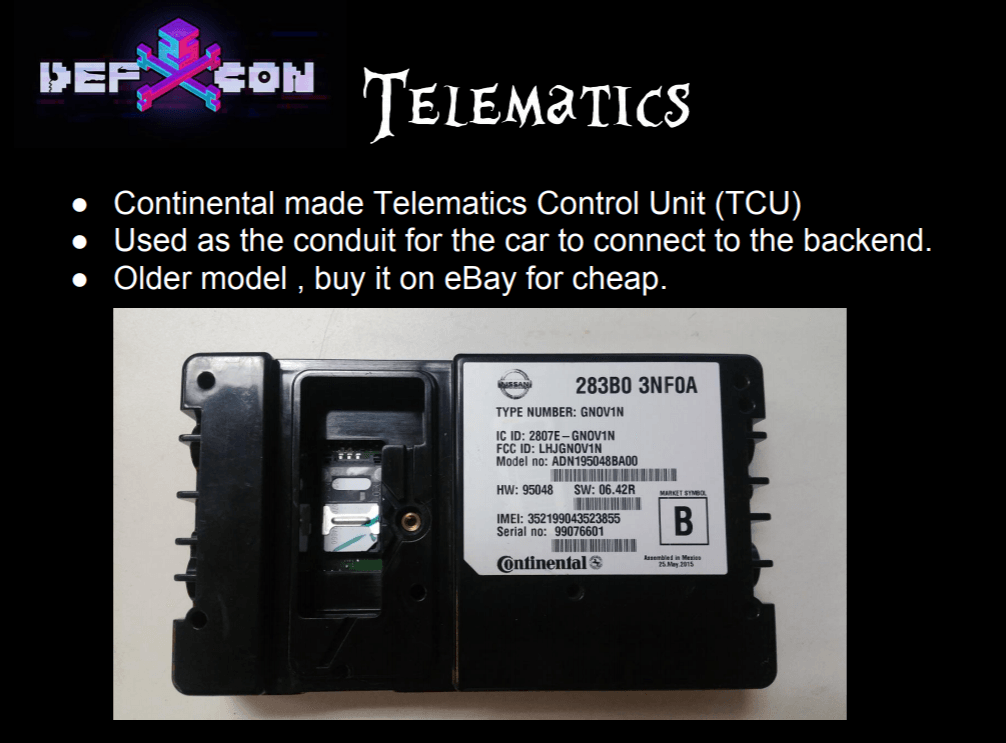
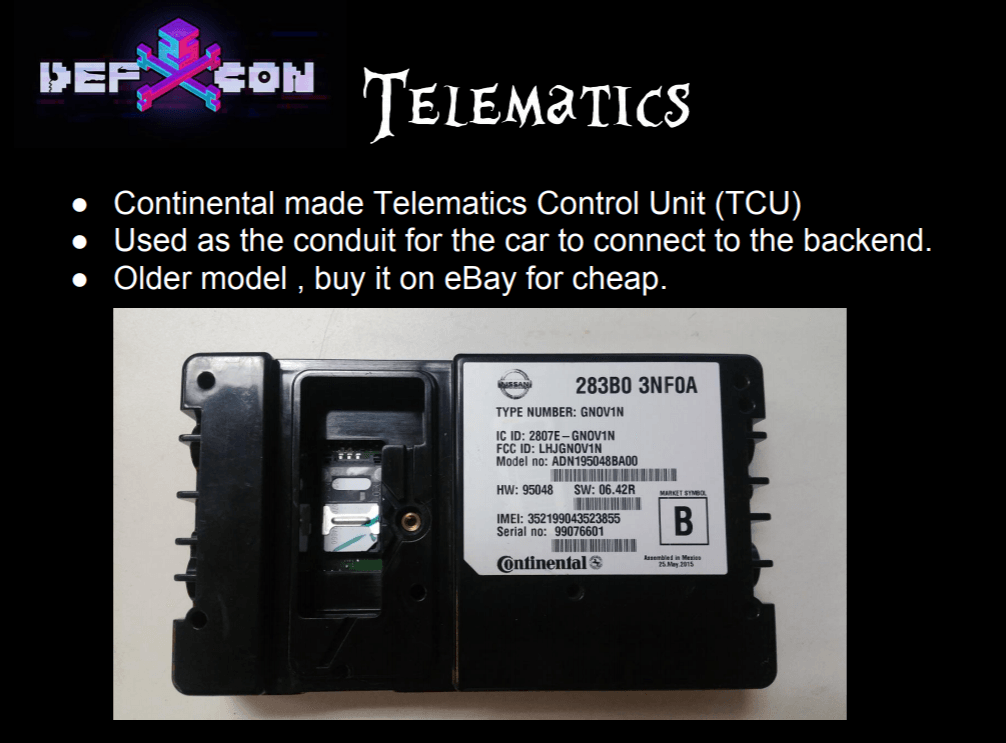
187VulnerabilitiesSecurity flaws affect TCUs used in BMW, Ford, Infiniti, and Nissan vehicles
Three security researchers have discovered security vulnerabilities in the telematics control units (TCUs) used in BMW, Ford, Infiniti, and Nissan vehicles. Three...
-

 149Vulnerabilities
149VulnerabilitiesSecurity Flaws In “Smart” Car Wash Can Be Exploited to Cause Physical Injuries
Two US security researchers have found vulnerabilities in smart car wash solutions sold by PDQ, a US-based vendor of Internet-connected car wash...
-

 214Cyber Crime
214Cyber CrimeChinese Cyber Security Laws Force Apple to Build Data Center in China
Apple Inc. will soon be storing cloud data of its Chinese customers with a Chinese government-owned company in accordance with the latest...
-
 385Geek
385GeekLDAP & RDP Relay Flaws Found in Windows Security Protocols
Security researchers at behavioral firewall specialist firm Preempt have discovered two critical security flaws in the Microsoft Windows NT LAN Manager (NTLM)...
-

 302Hacked
302HackedJohn McAfee Can Finally Use His Name, Settles Lawsuit But Intel Still Wins
It was last year when, John McAfee, the co-founder of an antivirus company that’s now owned by Intel, took Intel to the...
-
 202Incidents
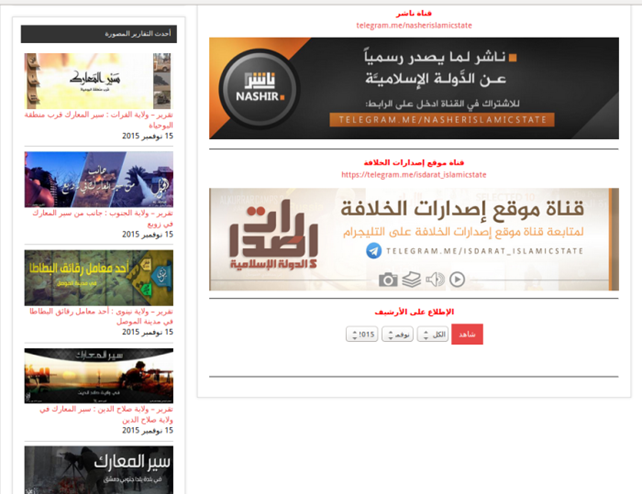
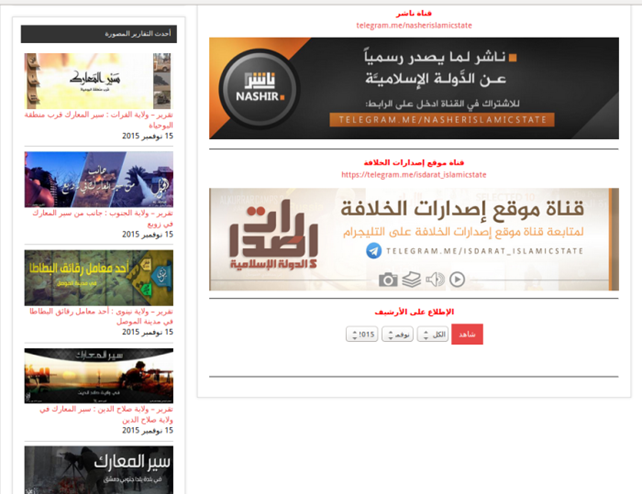
202IncidentsRussian Gov is threatening to ban Telegram because it refused to comply data protection laws
Russia threatens to ban the Telegram instant messaging app because the company refused to be compliant with the country’s new data protection...






