Search results for "Certificates"
-

 368Cryptocurrency
368CryptocurrencyHackers Illegally Purchasing Abused Code-signing & SSL Certificates From Underground Market
Threat actors using Abused Code-signing certificate from reputable companies as a layer of obfuscation in distributing malicious payloads. Abused Codesigning certificates would...
-

 292Cryptocurrency
292CryptocurrencyNew Method to Establish Covert Channel Communication by Abusing X.509 Digital Certificates
Security researchers from Fidelis identified a new method to establish a covert channel communication by abusing widely implemented X.509 public key certificates....
-
 288Malware
288MalwareMalware signed with stolen Digital code-signing certificates continues to bypass security software
A group of researchers demonstrated that malware signed with stolen Digital code-signing certificates continues to bypass security software. A recent study conducted...
-

 295Infosec
295InfosecGoogle Announces Final Decision in Distrusting Symantec SSL Certificates
Google has made a conclusive decision on the different dates they want to execute as part of the accord plan in distrusting...
-
 227Infosec
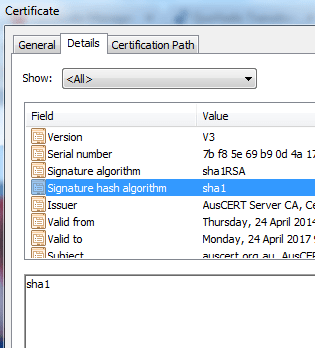
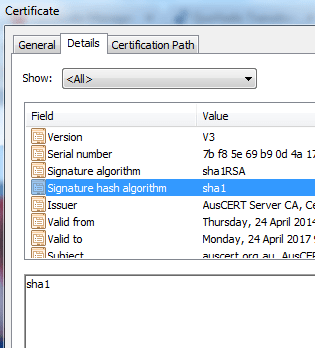
227InfosecMicrosoft boycott SHA-1 Certificates in Edge and Internet Explorer
[jpshare]The move from having SSL Certificates marked with the SHA-1 hashing algorithm to certificate signed with the SHA-256 set to start in...
-
 215Cryptocurrency
215CryptocurrencyFinal countdown for SHA-1 SSL certificates
SHA-1 SSL certificates which are more popular and an sucessor of MD5 algorithm are now in the final days of what was once...
-
 168Incidents
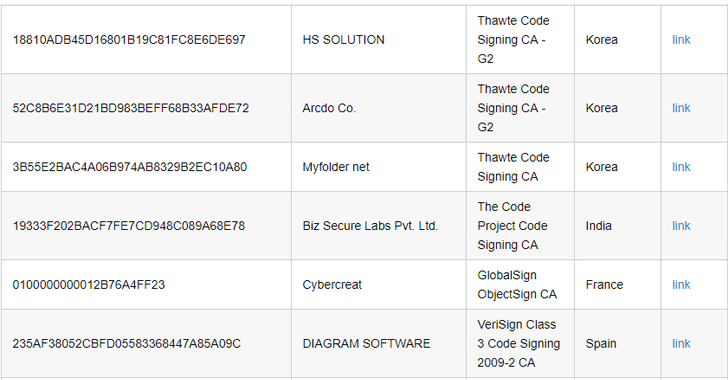
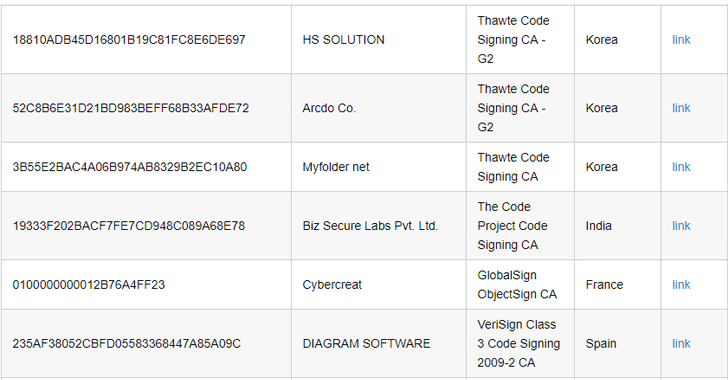
168IncidentsTo bypass code-signing checks, malware gang steals lots of certificates
Legitimate code-signing certificates provide secret cover for attack groups. There are lots of ways to ensure the success of an advanced hacking operation....
-

 158Data Security
158Data SecuritySuckfly: Revealing the secret life of your code signing certificates
A China-based APT group has an insatiable appetite for stolen code-signing certificates. Many security-minded organizations utilize code signing to provide an additional layer...
-

 243Data Security
243Data SecurityEmbedded Devices Share, Reuse Private SSH Keys, HTTPs Certificates
Researchers have found that thousands of Internet gateways, routers, modems and other embedded devices share cryptographic keys and certificates, exposing millions of...
-
 199Data Security
199Data SecurityDell does a Superfish, ships PCs with easily cloneable root certificates
Root certificate debacle that hit Lenovo now visits the House of Dell. In a move eerily similar to the Superfish debacle that...
-
 186Malware
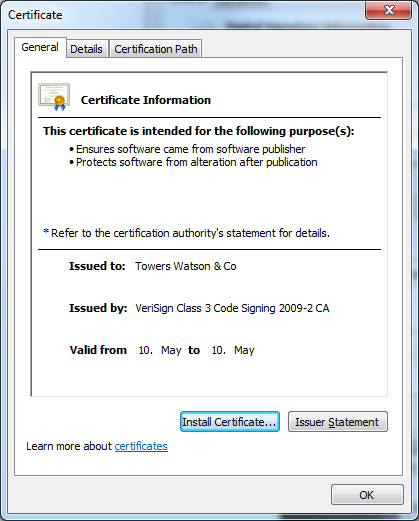
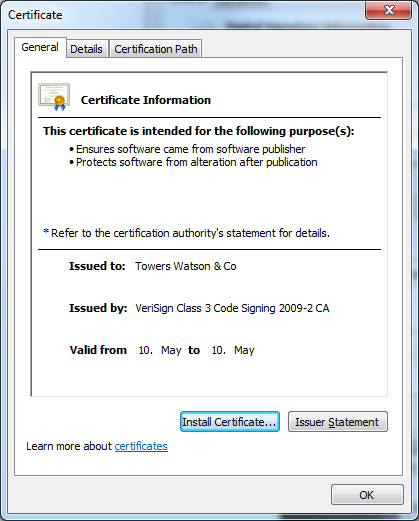
186MalwareTowering Qbot Certificates
New stolen digital certificates are used by the multi-purpose backdoor Qbot. The criminals behind the Qbot trojan are certainly not inactive. As...






