Search results for "Cloud"
-

 2.7KVulnerabilities
2.7KVulnerabilitiesTwo important vulnerabilities ( CVSSv3 score > 7) in VMware ESXi, vCenter Server & Cloud Foundation
The leader in virtualization and cloud computing technologies, VMware, has released a security fix for two vulnerabilities in its vCenter Server software...
-
 4.7KVulnerabilities
4.7KVulnerabilitiesResearchers Disclose Critical Vulnerability in Oracle Cloud Infrastructure
Researchers have disclosed a new severe Oracle Cloud Infrastructure (OCI) vulnerability that could be exploited by users to access the virtual disks...
-

 2.9KCyber Attack
2.9KCyber AttackHackers Behind Twilio Breach Also Targeted Cloudflare Employees
Web infrastructure company Cloudflare on Tuesday disclosed at least 76 employees and their family members received text messages on their personal and...
-

 2.1KMalware
2.1KMalwareAlibaba Cloud Compromised to Distribute Malware via Steganography
Researchers have identified a malicious campaign using Alibaba Cloud’s Object Storage Service (OSS) (also known as Aliyun) for malware distribution and illicit...
-

 1.1KInfosec
1.1KInfosecGhangorCloud Introduces Next Generation Unified Compliance & Data Privacy Enforcement Solution
One of the biggest challenges that global organizations face is the pervasive risk of serious fines as mandated by consumer data privacy...
-

 2.7KMalware
2.7KMalwareExperts Uncover New CloudMensis Spyware Targeting Apple macOS Users
Cybersecurity researchers have taken the wraps off a previously undocumented spyware targeting the Apple macOS operating system. The malware, codenamed CloudMensis by...
-
 3.2KMalware
3.2KMalwareMantis Botnet Behind the Largest HTTPS DDoS Attack Targeting Cloudflare Customers
The botnet behind the largest HTTPS distributed denial-of-service (DDoS) attack in June 2022 has been linked to a spate of attacks aimed...
-

 2.0KTutorials
2.0KTutorials5 best free API security testing tools. Protecting your cloud CI/CD Pipeline
Applied Programming Interfaces (API) are an essential component of most modern programs and applications. In fact, cloud applications and mobile applications now...
-
 3.0KVulnerabilities
3.0KVulnerabilitiesCritical Flaws in MEGA Cloud Storage Let Attacker Decrypt User Data
The experts at one of Europe’s leading universities, ETH Zurich, Switzerland reported a critical vulnerability in MEGA cloud storage that allows the...
-

 6.4KMalware
6.4KMalwareA Microsoft Office 365 Feature Could Help Ransomware Hackers Hold Cloud Files Hostage
A “dangerous piece of functionality” has been discovered in Microsoft 365 suite that could be potentially abused by a malicious actor to...
-
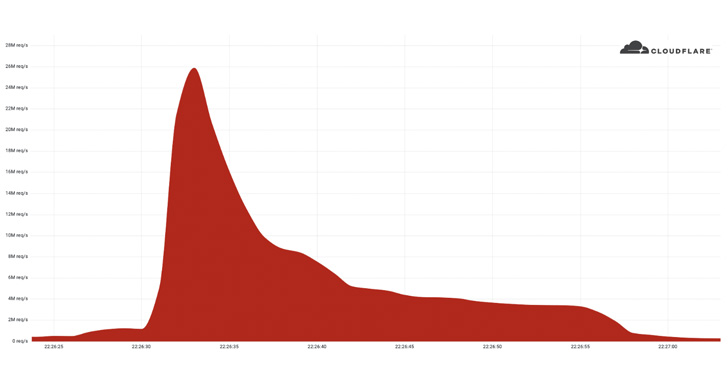
 3.4KCyber Attack
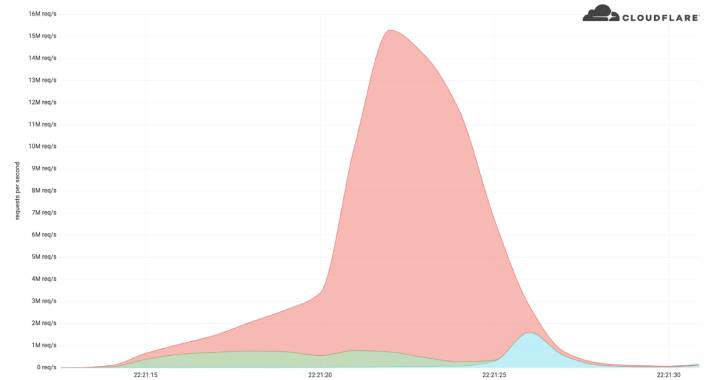
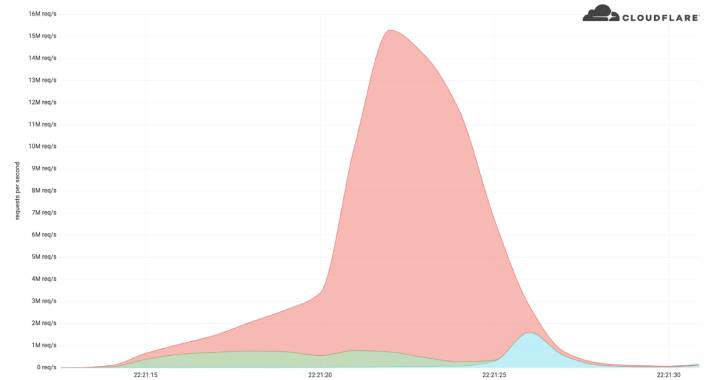
3.4KCyber AttackCloudflare Saw Record-Breaking DDoS Attack Peaking at 26 Million Request Per Second
Cloudflare on Tuesday disclosed that it had acted to prevent a record-setting 26 million request per second (RPS) distributed denial-of-service (DDoS) attack...
-

 1.6KVulnerabilities
1.6KVulnerabilitiesTwo critical command injection vulnerabilities in Fujitsu cloud storage system allow remote encryption or deletion of files
Two bugs in the web interface of a Fujitsu cloud storage system would allow authenticated threat actors to read, write, and even...
-
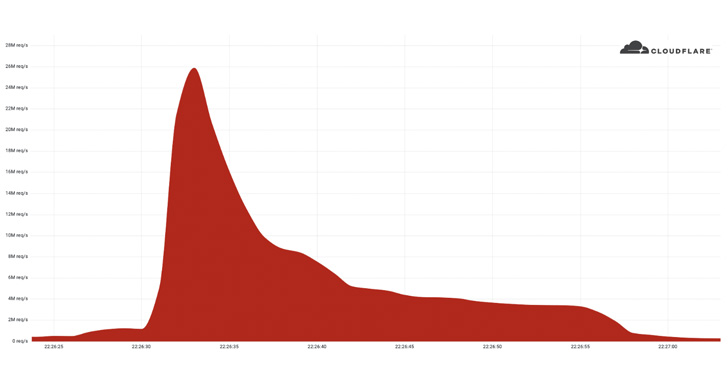
 1.2KCyber Attack
1.2KCyber AttackCloudflare Thwarts Record DDoS Attack Peaking at 15 Million Requests Per Second
Cloudflare on Wednesday disclosed that it acted to mitigate a 15.3 million request-per-second (RPS) distributed denial-of-service (DDoS) attack. The web infrastructure and...
-
 4.7KMalware
4.7KMalwareWatch Out! Cryptocurrency Miners Targeting Dockers, AWS and Alibaba Cloud
LemonDuck, a cross-platform cryptocurrency mining botnet, is targeting Docker to mine cryptocurrency on Linux systems as part of an active malware campaign....
-

 2.3KIncidents
2.3KIncidentsHow someone can easily steal NFT using your iCloud backup
The developers of the popular cryptocurrency software MetaMask asked Apple users to disable the automatic backup feature in iCloud after Domenic Lacovone,...
-

 3.8KVulnerabilities
3.8KVulnerabilitiesCritical code injection vulnerabilities in VMware Spring Cloud Gateway
Cybersecurity specialists report the detection of two vulnerabilities in VMware Spring Cloud Gateway, a library for creating API gateways over Spring and...
-

 3.0KVulnerabilities
3.0KVulnerabilities6 critical vulnerabilities in Western Digital My Cloud OS 5
Multiple vulnerabilities have been detected in My Cloud OS 5, the operating system of network-attached storage (NAS) solutions developed by Western Digital....
-

 2.4KVulnerabilities
2.4KVulnerabilities5 vulnerabilities patched in VMWare Cloud Foundation (ESXi). Update immediately
Cybersecurity specialists report the detection of multiple vulnerabilities in VMware Cloud Foundation (ESXi), a popular hybrid cloud platform. According to the report,...
-

 2.1KNews
2.1KNewsBetter Cloud Services: Tech giant Google Unveils Compute Optimized Virtual Machines (VMs) Powered by AMD EPYC Processors
An Instance refers to a server that is running our applications. Assume a single server is a single instance. Our cloud workloads...
-

 3.0KVulnerabilities
3.0KVulnerabilitiesNew vulnerability on Mac provides full access to iCloud accounts, PayPal and more of the affected users, as well as granting access to their microphone, camera and screen. The greatest reward ever delivered by Apple
This week, a young cybersecurity researcher demonstrated how to hack the webcams of Mac devices to leave the devices completely open to...
-
 603Cyber Attack
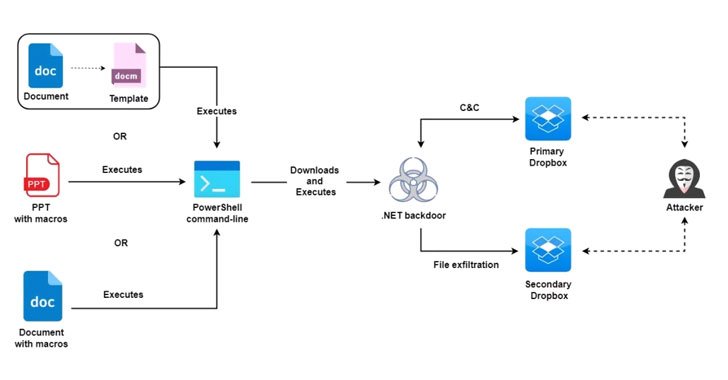
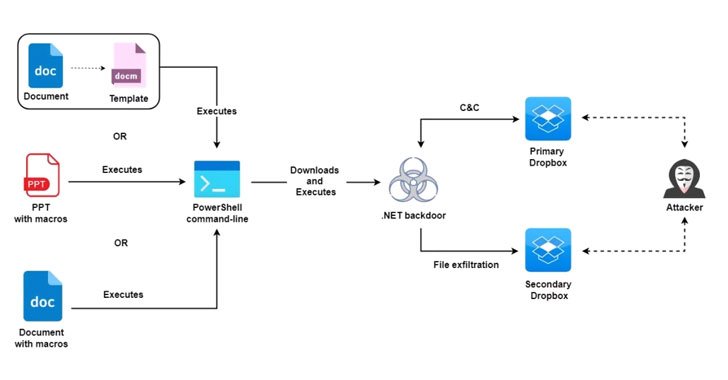
603Cyber AttackMolerats Hackers Hiding New Espionage Attacks Behind Public Cloud Infrastructure
An active espionage campaign has been attributed to the threat actor known as Molerats that abuses legitimate cloud services like Google Drive...






