Search results for "Cloud"
-
 3.8KTutorials
3.8KTutorialsAzure cloud security tutorial series – Chapter 4 [Establish VNet Peering]
Objective In the last chapter we saw on how to add resource to a VNet now in this chapter we will see...
-
 223Tutorials
223TutorialsAzure cloud security tutorial series – Chapter 3 [Add resource to VNet]
Overview In the last chapter (Azure cloud security tutorial series – Chapter 2 [Virtual Network]) we saw on how to create VNet...
-
 853Tutorials
853TutorialsAzure cloud security tutorial series – Chapter 2 [Virtual Network]
Basic Overview Network is combination of many different systems connected together. In the Azure cloud security tutorial series – Chapter 1 [Azure...
-
 3.6KTutorials
3.6KTutorialsAzure cloud security tutorial series – Chapter 1 [Azure Account]
Basic Overview Azure is the mostly used cloud in IT organizations. Before cloud came into existence many companies or organizations were using...
-

 4.9KMalware
4.9KMalwareIranian Company Cloudzy Accused of Aiding Cybercriminals and Nation-State Hackers
Services offered by an obscure Iranian company known as Cloudzy are being leveraged by multiple threat actors, including cybercrime groups and nation-state...
-
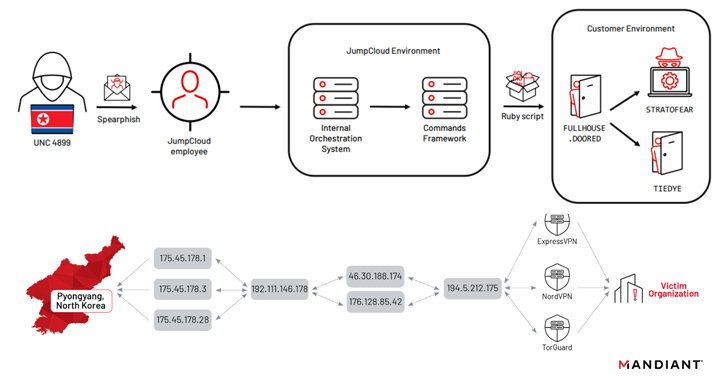
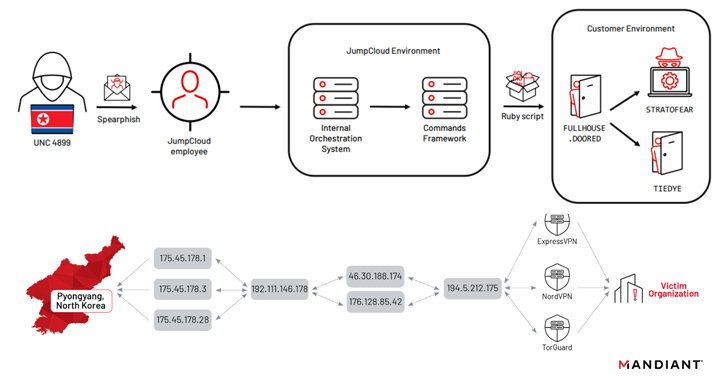 2.6KCyber Attack
2.6KCyber AttackNorth Korean Nation-State Actors Exposed in JumpCloud Hack After OPSEC Blunder
North Korean nation-state actors affiliated with the Reconnaissance General Bureau (RGB) have been attributed to the JumpCloud hack following an operational security...
-

 919Data Security
919Data SecurityTop 5 free cloud security tools, that can protect your AWS & Azure cloud data from hackers
The Cybersecurity and Infrastructure Security Agency (CISA) has come up with a list of free tools that businesses may use to protect...
-
Data Breach
JumpCloud Blames ‘Sophisticated Nation-State’ Actor for Security Breach
A little over a week after JumpCloud reset API keys of customers impacted by a security incident, the company said the intrusion...
-
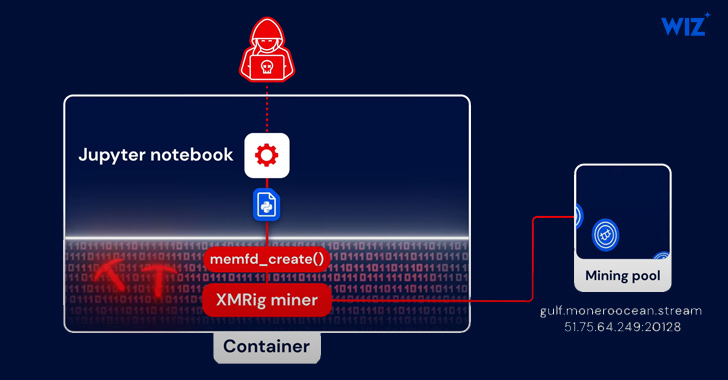
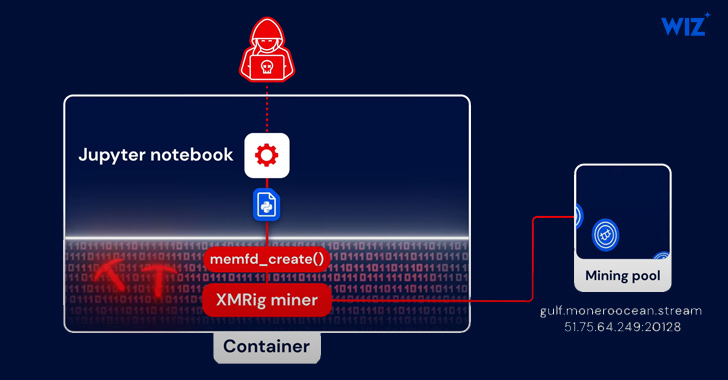 3.5KMalware
3.5KMalwarePython-Based PyLoose Fileless Attack Targets Cloud Workloads for Cryptocurrency Mining
A new fileless attack dubbed PyLoose has been observed striking cloud workloads with the goal of delivering a cryptocurrency miner, new findings...
-
 2.0KMalware
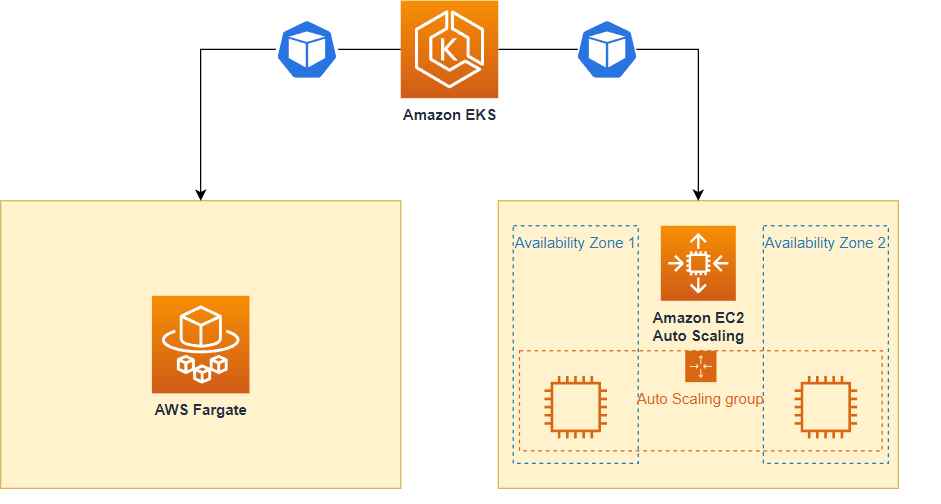
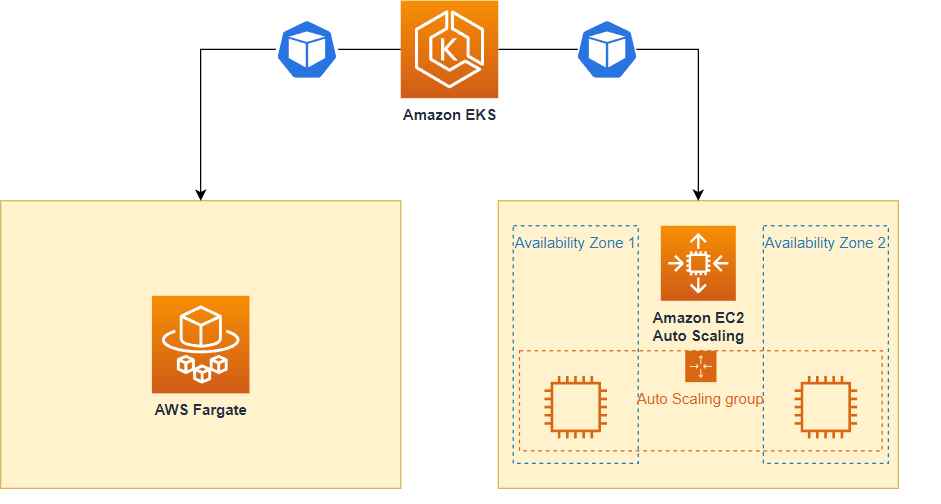
2.0KMalwareHow cyber criminals are hacking into AWS Fargate, EKS & evading cloudtrail logs detection
Sysdig, a company that specializes in cybersecurity intelligence, uncovered a sophisticated hacking operation known as Scarleteel in February. Since then, Scarleteel has...
-

 3.9KData Breach
3.9KData BreachJumpCloud Resets API Keys Amid Ongoing Cybersecurity Incident
JumpCloud, a provider of cloud-based identity and access management solutions, has swiftly reacted to an ongoing cybersecurity incident that impacted some of...
-

 4.5KMalware
4.5KMalwareRansomware Hackers and Scammers Utilizing Cloud Mining to Launder Cryptocurrency
Ransomware actors and cryptocurrency scammers have joined nation-state actors in abusing cloud mining services to launder digital assets, new findings reveal. “Cryptocurrency...
-

 3.5KData Security
3.5KData SecurityNew zero day vulnerability in MOVEit Transfer & Cloud. How many more victims there will be?
As more organizations come out to declare data breaches that were caused by the program’s flaws, the developer of the popular MOVEit...
-
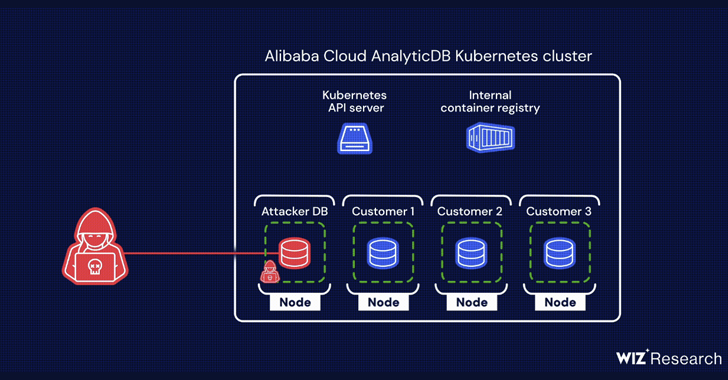
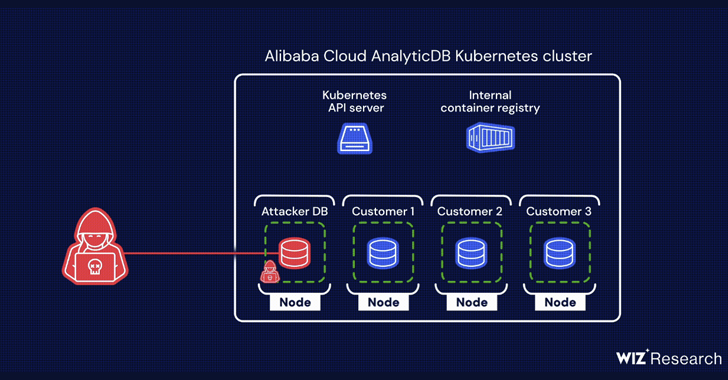 1.0KVulnerabilities
1.0KVulnerabilitiesTwo Critical Flaws Found in Alibaba Cloud’s PostgreSQL Databases
A chain of two critical flaws has been disclosed in Alibaba Cloud’s ApsaraDB RDS for PostgreSQL and AnalyticDB for PostgreSQL that could...
-
 861Malware
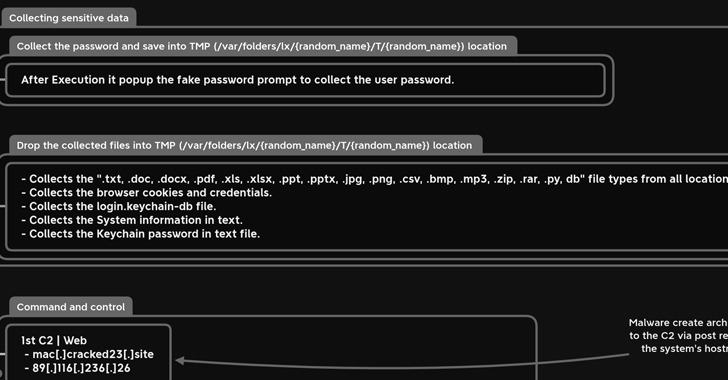
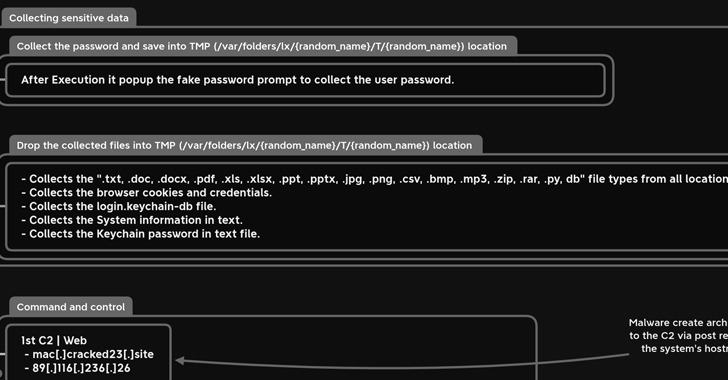
861MalwareNew MacStealer macOS Malware Steals iCloud Keychain Data and Passwords
A new information-stealing malware has set its sights on Apple’s macOS operating system to siphon sensitive information from compromised devices. Dubbed MacStealer,...
-

 1.7KData Security
1.7KData SecurityBlackbaud, a cloud software provider, fined $3 million for failing to notify customers of a ransomware attack
The U.S. Securities and Exchange Commission (SEC) made the announcement today that Blackbaud Inc., a public company located in South Carolina that...
-

 4.3KVulnerabilities
4.3KVulnerabilitiesCritical AWS CloudTrail vulnerability allowed attackers to circumvent CloudTrail & GuardDuty logging
CloudTrail is the tool that AWS administrators rely on to keep track of all API activity inside their accounts. CloudTrail helps teams...
-
 3.6KData Security
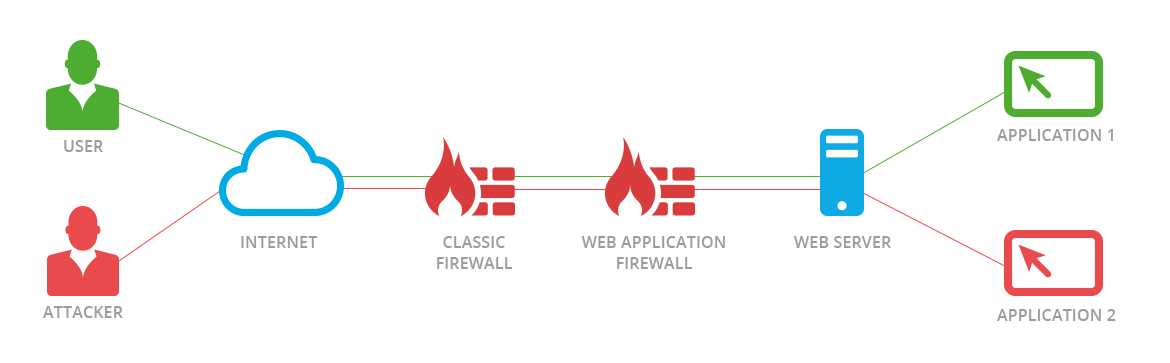
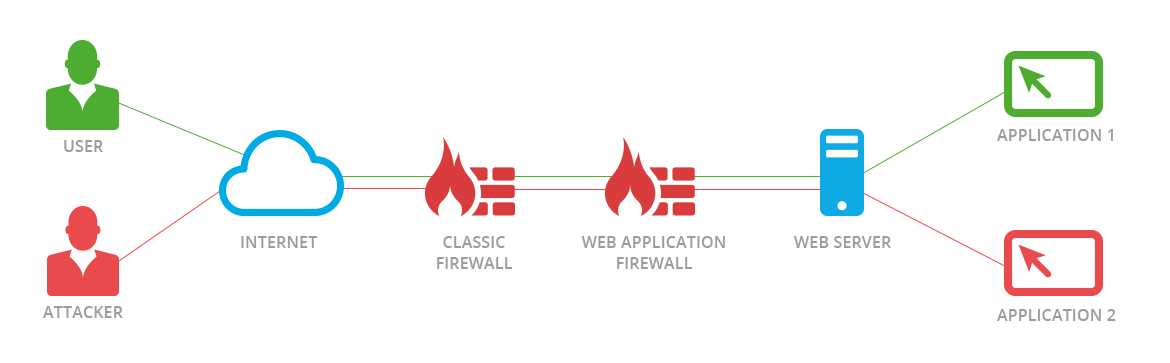
3.6KData SecurityNew JSON-Based SQL Injection attacks allow bypassing Palo Alto, F5, AWS, Cloudflare, and Imperva WAF
Web application firewalls, also known as WAFs, are intended to protect web-based applications and application programming interfaces (APIs) from malicious HTTPS traffic...
-
 4.6KVulnerabilities
4.6KVulnerabilitiesResearchers Disclose Supply-Chain Flaw Affecting IBM Cloud Databases for PostgreSQL
IBM has fixed a high-severity security vulnerability affecting its Cloud Databases (ICD) for PostgreSQL product that could be potentially exploited to tamper...
-

 2.7KVulnerabilities
2.7KVulnerabilities2 important vulnerabilities (XXE & RCE) in VMware Cloud Foundation. Patch immediately
The serious XML External Entity (XXE) and remote code execution (RCE) vulnerabilities in Cloud Foundation have been patched, according to VMware. CVE-2021-39144...
-

 1.9KVulnerabilities
1.9KVulnerabilitiesVMware Releases Patch for Critical RCE Flaw in Cloud Foundation Platform
VMware on Tuesday shipped security updates to address a critical security flaw in its VMware Cloud Foundation product. Tracked as CVE-2021-39144, the...






