Search results for "Cloud"
-

 4.5KMalware
4.5KMalwareHackers Use Cloud Services to Distribute Nanocore, Netwire, and AsyncRAT Malware
Threat actors are actively incorporating public cloud services from Amazon and Microsoft into their malicious campaigns to deliver commodity remote access trojans...
-

 855Vulnerabilities
855VulnerabilitiesUnpatched severe vulnerability with CVVS score of 7.7 in VMware’s Cloud Foundation, ESXi, Fusion and Workstation platforms
Cybersecurity specialists report the detection of a critical vulnerability in some VMware products, including Cloud Foundation, Fusion and Workstation. According to the...
-

 3.4KVulnerabilities
3.4KVulnerabilitiesMicrosoft Azure cloud exposed customers’ confidential source code since 2017
A few weeks ago Microsoft contacted a small group of Azure customers to inform them that they could be affected by a...
-

 1.7KVulnerabilities
1.7KVulnerabilitiesOxeye Identifies Vulnerabilities Cloud Native Applications with CNAST Platform
According to Gartner’s 2021 Magic Quadrant for Application Security Testing, “Modern application design and the continued adoption of DevSecOps are expanding the...
-

 765Malware
765MalwareHackers Using Compromised Google Cloud Accounts to Mine Cryptocurrency
Threat actors are exploiting improperly-secured Google Cloud Platform (GCP) instances to download cryptocurrency mining software to the compromised systems as well as...
-
 1.2KData Security
1.2KData SecurityCloud security is an ongoing struggle to keep sensitive data safe. Is it getting any easier?
The latest cloud security breaches show that we have miles to go as we keep fighting to keep our sensitive data safe. ...
-

 2.9KData Security
2.9KData SecuritySolarWinds hackers, Nobelium, hit cloud providers and resellers
So far, Microsoft has informed 140 companies about the new attack campaign being carried out by Nobelium 14 of which were compromised...
-

 2.5KVulnerabilities
2.5KVulnerabilitiesZero-day vulnerability in Apple’s new iCloud Private Relay service for iOS 15 allows seeing user real IP addresses
Cybersecurity specialists report the detection of an unpatched vulnerability in iCloud Private Relay, a service implemented by Apple in its latest update...
-

 3.3KCyber Crime
3.3KCyber CrimeiCloud phishing scam – Man stole private photos of 620,000 women
LA County resident booked in iCloud phishing scam pretended to be an Apple representative. A Los Angeles County man identified as Hao...
-

 966Cyber Crime
966Cyber CrimeMan impersonates Apple support, steals 620,000 photos from iCloud accounts
The man was after sexually explicit photos and videos that he would then share online or store in his own collection
-
 1.5KDDOS
1.5KDDOSCloudflare Recorded 17.2 Million Request-Per-Second (rps) – Largest HTTP DDoS Attack Ever Detected
Being a USA-based web infrastructure and website security company, Cloudflare works for other companies managing connections to servers and web pages. Recently,...
-
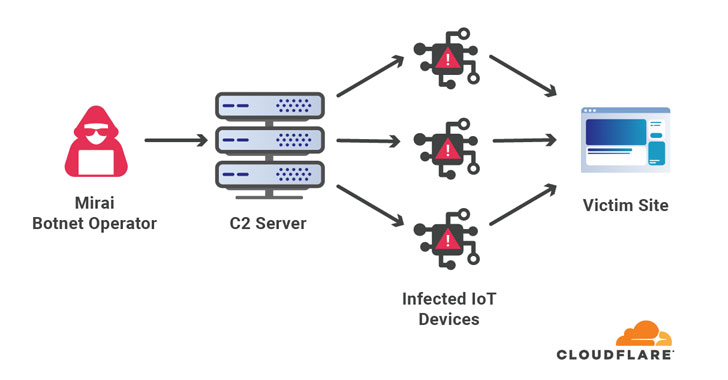
 2.1KCyber Attack
2.1KCyber AttackCloudflare mitigated one of the largest DDoS attack involving 17.2 million rps
Web infrastructure and website security company Cloudflare on Thursday disclosed that it mitigated the largest ever volumetric distributed denial of service (DDoS)...
-

 2.4KVulnerabilities
2.4KVulnerabilitiesVulnerabilities in Palo Alto Prisma Cloud Compute and Cortex XDR agent. Patch now
The security teams of the technology firm Palo Alto Networks announced the correction of a set of vulnerabilities in Prisma Cloud Compute,...
-

 3.0KMalware
3.0KMalwareRussian APT Hackers Launched A Mass Global Brute Force Attack to Hack Enterprise & Cloud Networks
Recently, in a joint warning, the cybersecurity agencies of the US and UK have released a set of large-scale brute-force attacks escorted...
-

 1.7KVulnerabilities
1.7KVulnerabilitiesGoogle cloud VMs servers can be hacked via DHCP using this vulnerability in a specific scenario
A recent security report states that it is possible to hijack sessions on Google Compute Engine virtual machines to gain root access...
-

 3.7KMalware
3.7KMalwareSiloscape: First Known Malware Targeting Windows Containers to Hack Cloud Environments
Using Windows Server in a “Windows container”? Then beware of it, as recently, it has been confirmed that highly sophisticated malware has...
-

 3.8KMalware
3.8KMalwareHow Apple Gave Chinese Government Access to iCloud Data and Censored Apps
In July 2018, when Guizhou-Cloud Big Data (GCBD) agreed to a deal with state-owned telco China Telecom to move iCloud data belonging...
-
 5.1KCyber Events
5.1KCyber EventsWarning as hackers breach MFA to target cloud services
According to CISA, it has verified one of the users had their account breached even though they were using “proper multi-factor authentication...
-

 4.3KGeek
4.3KGeekWhat are the future prospects of a Cloud architect?
The people who are responsible for the management of the Cloud computing architecture in an organization are known as cloud architects. They...
-

 1.1KVulnerabilities
1.1KVulnerabilitiesMicrosoft’s Anzure cloud-container technology allows hackers to directly update your files
Cybersecurity specialists from Intezer report the finding of a privilege escalation vulnerability in Microsoft Azure Functions whose exploitation would allow threat actors...
-

 2.8KVulnerabilities
2.8KVulnerabilitiesBypassing WAF in Azure, Cloudflare Access via H2C smuggling attack
A group of specialists has detailed a method for abusing a well-known “H2C smuggling” technique in order to authenticate and bypass some...






