Search results for "Encryption"
-

 204Vulnerabilities
204VulnerabilitiesVulnerabilities in self encrypted SSD allow attackers to bypass disk encryption
Master passwords and flawed standards implementations allow attackers to access encrypted data without having to know the user’s password Researchers in digital...
-

 231Vulnerability Analysis
231Vulnerability Analysistestssl.sh – Testing TLS/SSL Encryption Anywhere On Any Port
testssl.sh is a free command line tool which checks a server’s service on any port for the support of TLS/SSL ciphers, protocols...
-
 334Cryptography
334CryptographyCyberChef – A web App For Encryption, Encoding, Compression & Data Analysis
CyberChef is a simple, intuitive web app for carrying out all manner of “cyber” operations within a web browser. These operations include...
-

 346Malware
346MalwareFive Eyes Group demands access to crime suspects data through encryption backdoors
The group threatens to take legal action Five Eyes alliance member countries have threatened to implement legislation if technology providers do not cooperate...
-

 214News
214NewsThanks, Skype, For Boosting Security With End-To-End Encryption
The new Skype 8.0 has been fully redesigned and will replace its predecessor, version 7.0, which will cease to function after September...
-

 176Vulnerabilities
176VulnerabilitiesPGP Users Warned of New Email Encryption Security Vulnerabilities
A team of information security experts released a warning about a group of vulnerabilities that affect users of PGP and S / MIME. EFF...
-
 179Hacked
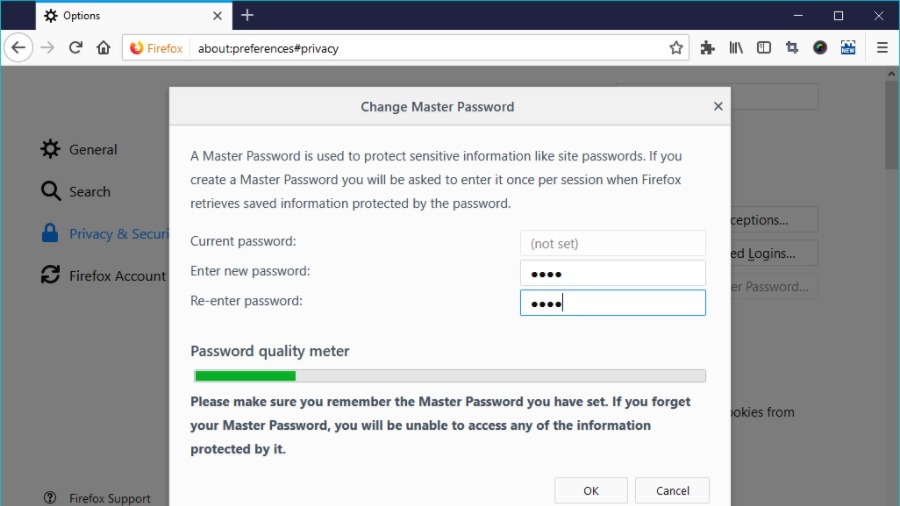
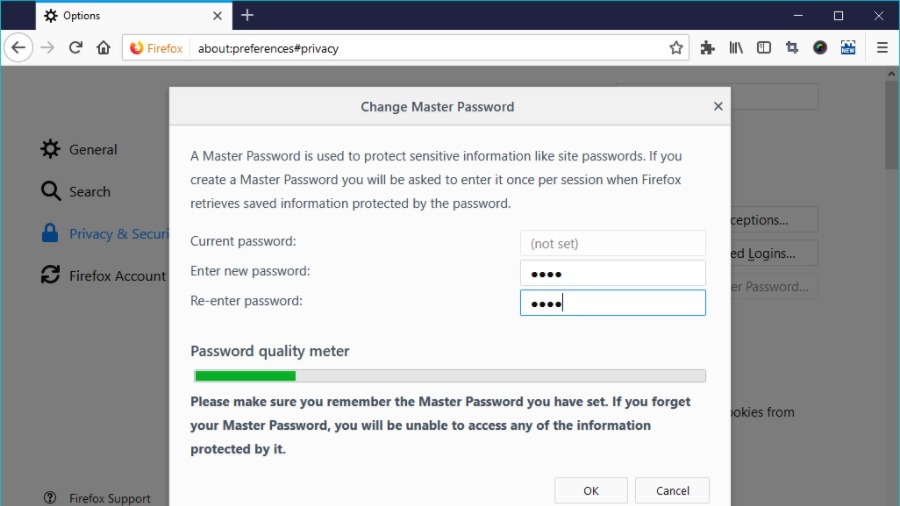
179HackedFirefox’s Weak Master Password Encryption Can Be Cracked In Just 1 Minute
You might rest assured after setting a Master Password in the Firefox web browser, but it’s not as secure as you think....
-

 318Data Security
318Data SecurityFBI supports & blames encryption for 7,800 devices it can’t unlock
FBI (Federal Bureau of Investigation) director blames encryption for thousands of phones the Bureau could not unlock but then he also supports “strong...
-

 390Reviews
390ReviewsExpressVPN Review 2018: A VPN For Fast Streaming And Strong Encryption
In the past, you might have read the in-depth review of NordVPN on Fossbytes. But one needs to consider more than one...
-

 175Malware
175MalwareUS says it doesn’t need secret court’s approval to ask for encryption backdoors
Critics have long argued that the government has wide latitude to conduct surveillance under broad approvals from the Foreign Intelligence Surveillance Court....
-
 248Articles
248ArticlesDUHK (Don’t Use Hard-coded Keys) Attack Recovers Encryption Keys & Reveals VPN Connections
DUHK (Don’t Use Hard-coded Keys) is a new crypto implementation attack that could enable attackers to obtain secret keys that secure VPN...
-

 337Cryptocurrency
337CryptocurrencyDUHK Attack allows Hackers to Recover Encryption Keys and Decrypt Communications Passing Over VPN
DUHK attack targets the old vulnerability that resides in the pseudorandom number generator called ANSI X9.31. It is an algorithm widely used...
-
 238Cryptography and Encryption
238Cryptography and EncryptionCryptomator – Cloud Client Side File Encryption
Multi-platform transparent client-side encryption of your files in the cloud. Cryptomator provides transparent, client-side encryption for your cloud. Protect your documents from...
-

 230Hacked
230HackedForget KRACK Attack, 5 Year Old Encryption Bug Returns For Google And Microsoft
While we were still finding it difficult to forget the Krack attack, a five-year-old bug has resurfaced in a new form to...
-
 191Vulnerabilities
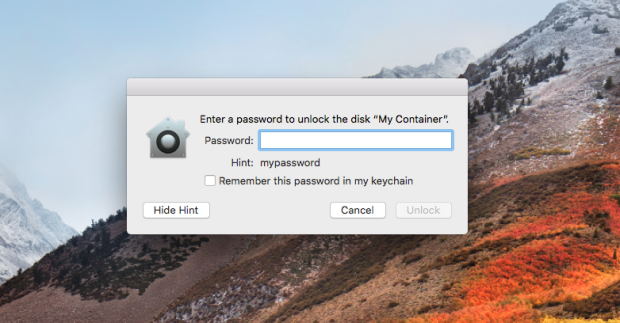
191VulnerabilitiesApple Issues Emergency Patch to Fix Password Leak in Disk Encryption Utility
Apple rushed out an emergency patch Thursday that fixed an incredulous bug in its shiny new High Sierra operating system that revealed APFS volume...
-
 220Incidents
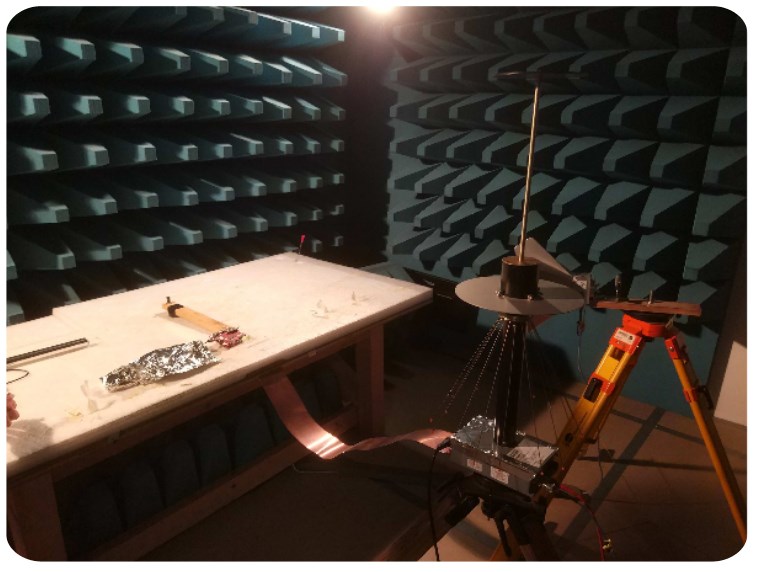
220IncidentsExperts Recover AES256 Encryption Key From a PC’s Electromagnetic Emissions
A team of researchers from Fox-IT and Riscure has put together a device using off-the-shelve electronic parts that deduces encryption keys using...
-
 239Vulnerabilities
239VulnerabilitiesPerl devs fix an important flaw in DBD—MySQL that affects encryption between client and server
Perl development team solved a flaw in DBD—MySQL in some configurations that wasn’t enforcing encryption allowing an attacker to power MiTM attacks....
-

 208Vulnerabilities
208VulnerabilitiesUK Govt Wants Encryption Backdoors but Can’t Even Protect Its Email Servers From a Brute-Force Attack
A “determined” attacker has breached the email system of the UK Parliament over the weekend, according to a statement put out by...
-

 179News
179NewsEuropean Government Proposes Ban On Encryption Backdoors
The European Parliament has set up a revised list does not require that the encryption of a party to a party when...
-
 517News
517NewsHow To Prevent Growing Issue of Encryption Based Malware (Ransomware)
The threat of ransomware attack is growing and here is how to protect yourself from encryption based malware known as ransomware. The...
-
 145Hacked
145HackedResearcher Open Sources WannaKey Tool That Cracks WannaCry Ransomware Encryption
It’s more than a week since WannaCry ransomware started causing panic among the internet community. However, as time passes, more and more...






