Search results for "Encryption"
-
 2.1KRansomware
2.1KRansomwareNew Version of DeathRansom Ransomware Aggressively Encrypts Network Drive Files After it’s Encryption Bug Fixed by Author
DeathRansom – A new ransomware strain that evolves from no encryption to using a combination of encryption algorithms to encrypt files. The...
-

 4.3KNews
4.3KNewsScientists Crack Largest Encryption Key After 35 Million Hrs Of Computing
French scientists have set a world record by cracking the most complex cryptography algorithm to date. The encryption key, in this case,...
-
 650Hack Tools
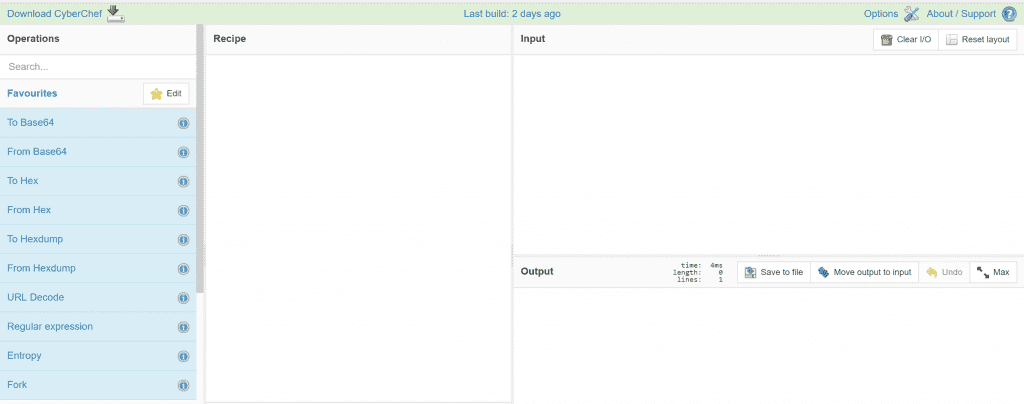
650Hack ToolsCyberChef v9.11.10 releases: web app for encryption, encoding, compression and data analysis
CyberChef The Cyber Swiss Army Knife CyberChef is a simple, intuitive web app for carrying out all manner of “cyber” operations within...
-

 403Incidents
403IncidentsModern Robin Hood: Ethical Hacker takes control of cybercriminal servers to publish ransomware encryption keys
The most frustrating part of being a cybercrime victim is the low chance of an attacker getting caught; however, malicious hackers don’t...
-
 3.4KPrivacy
3.4KPrivacyPGP Encryption: How Strong Is PGP Security?
Today, privacy is a huge concern for many internet users. With cybercrime on the rise, hackers are victimizing millions on the internet...
-
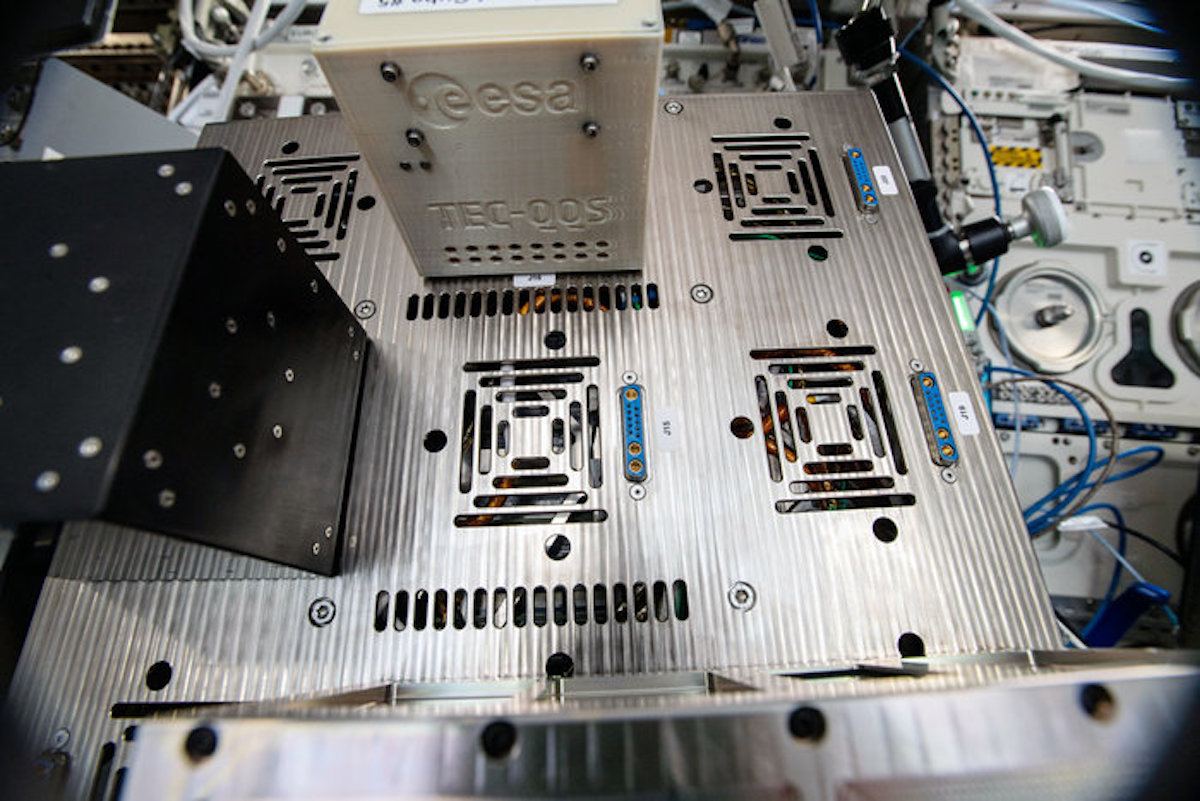
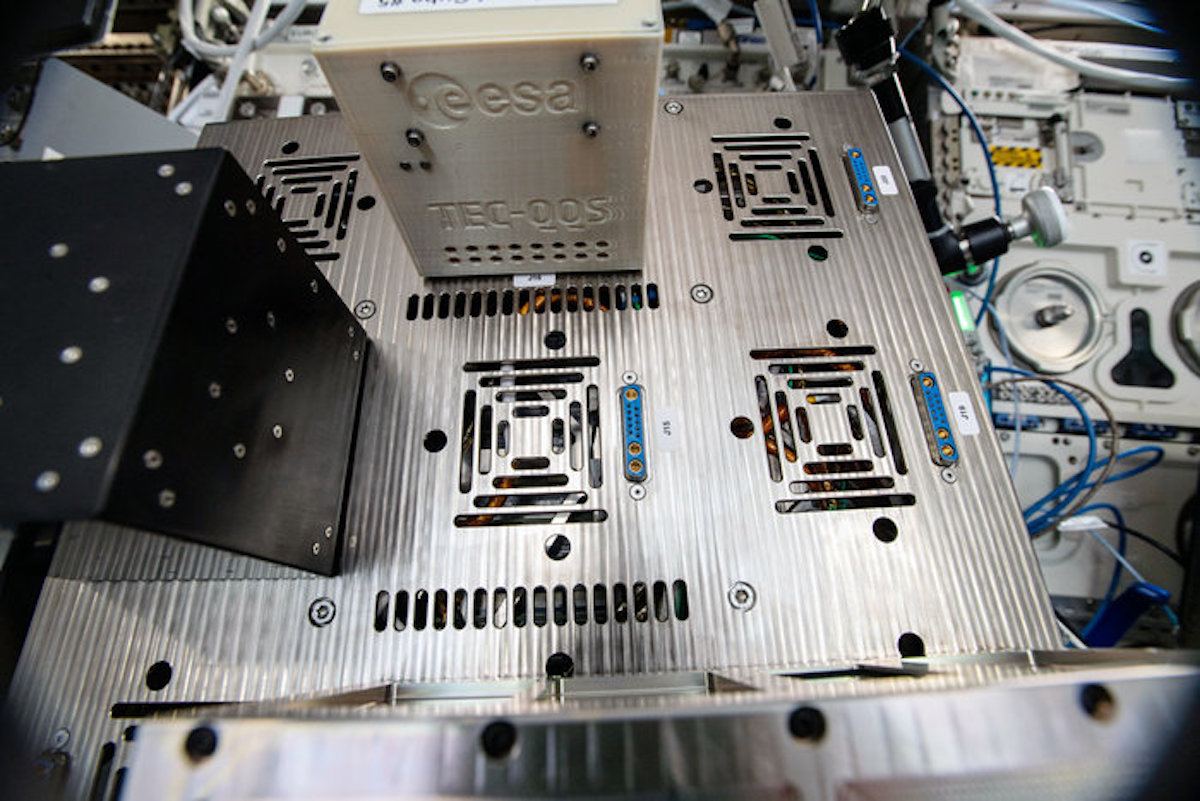 355News
355NewsResearchers Are Using $10 Raspberry Pi Zero For ‘Cheap Encryption’ In Space
There are several techniques of encryption that are deployed to secure communication protocols and devices but these techniques aren’t effective if you...
-
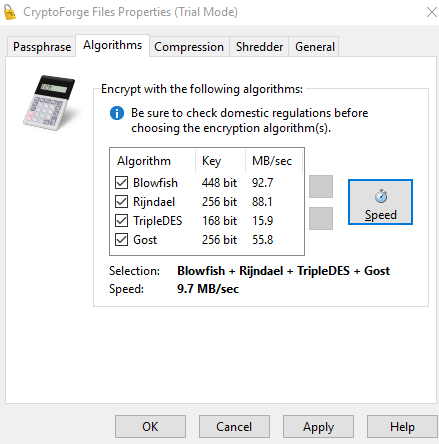
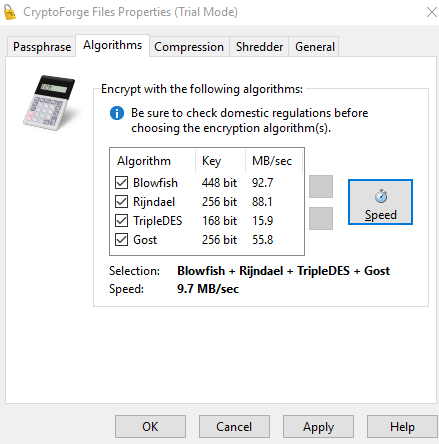 254Cryptography
254CryptographyCryptoforge – Encryption and Privacy Software
CryptoForge is a suite of encryption and privacy tools for personal and professional security. It allows you to protect the privacy of...
-

 277News
277NewsTech Companies “Must” Put Backdoors In Encryption, Demands US Attorney General
Encryption has always irked law enforcement agencies and now William Barr, the US General Attorney, has launched a fresh attack against consumer...
-
 253News
253NewsTrump Government Could Ban End-To-End Encryption
Trump is after many things and wants to put an end to a lot of things. This time, the Trump-led administration might...
-
 335Data Breach
335Data BreachMongoDB 4.2 Introduces End-to-End Field Level Encryption for Databases
At its developer conference held earlier this week in New York, the MongoDB team announced the latest version of its database management...
-

 361Malware
361MalwareNew tool to remove GandCrab ransomware encryption
A group of web application security testing experts has released a new version of the tool to remove the encryption imposed by...
-

 383Cryptocurrency
383CryptocurrencyWhat is Encryption?
Encryption is the process of converting clear information into the code to prevent unauthorized access to it. Governments, companies, and individuals use...
-

 337VPN
337VPNTesting your VPN’s Encryption and Privacy – Complete Guide
One little secret of the VPN industry is that most VPNs leak .In one in-depth study of Android free VPN apps, researchers found that...
-

 255News
255NewsProgrammers Are Too Lazy To Implement Password Encryption: Study
A group of researchers from The University of Bonn has found that computer science students need to be explicitly told to employ...
-
 298Malware
298MalwareA new tool to remove GandCrab ransomware encryption
The latest version of the tool is functional for those who suffered ransomware infections between November 2018 and February 2019 Network security...
-

 312Data Security
312Data SecurityNew attack removes TLS protocol encryption
This new attack is also functional against the recently released TLS 1.3 protocol A new cryptographic attack capable of disrupting the encrypted...
-

 215News
215NewsAdiantum- Faster Storage Encryption for All Low-End Devices
Google launched a new cryptographic algorithm(Adiantum), which was specifically designed to work on smartphones and IoT devices that do not have special...
-
 193Articles
193ArticlesGoogle Created Faster Storage Encryption for All Low-End Devices
Google has launched a new encryption algorithm that has been built specifically to run on mobile phones and smart IoT devices that...
-

 290Tricks & How To's
290Tricks & How To'sHow to Test VPN Encryption ?
VPN is a new innovative tool, which protects and secures users online activity and traffic data from the eavesdropping eyes like hackers,...
-

 338Data Security
338Data Security“Anti encryption Bill” is approved in Australia
The Australian government is looking for a way to access encrypted communications of certain services, as well as access to non encrypted...
-

 661Privacy
661PrivacySecurity researchers bypass encryption on self‑encrypting drives
Industry standard specification does not guarantee the safety of the self-encrypting drives despite verification






