Search results for "Exploitation"
-

 236Vulnerabilities
236VulnerabilitiesVMWARE EXPLOITATION THROUGH UNINITIALIZED BUFFERS
As we approach Pwn2Own 2018, I’m reminded of some of the exploits we saw at last year’s contest. Of course, the most...
-
 256Post Exploitation
256Post ExploitationPOET – A Simple Post-Exploitation Tool
POET is a simple post-exploitation tool to gain a remote shell on target machine. The client program runs on the target machine...
-
 92Hackers Repository
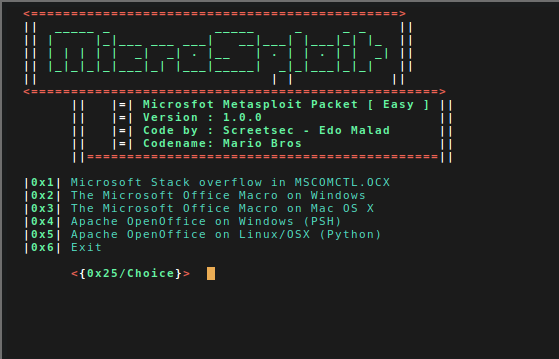
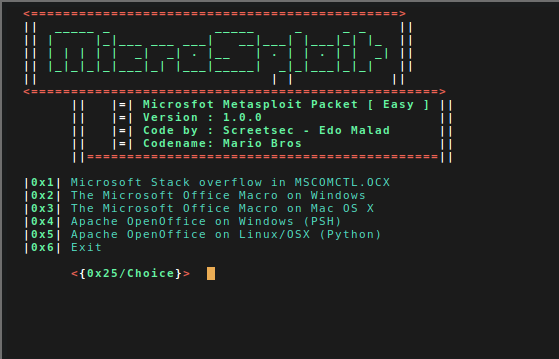
92Hackers RepositoryMicrosploit (Office Exploitation Tool)
a Simple tool and not very special but this tool fast and easy create backdoor office exploitation using module metasploit packet. Like...
-
 299Exploitation Tools
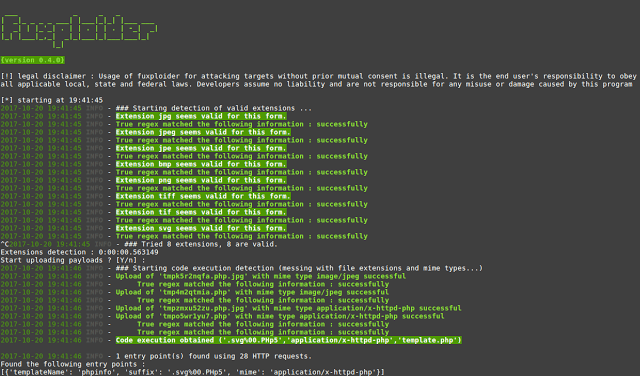
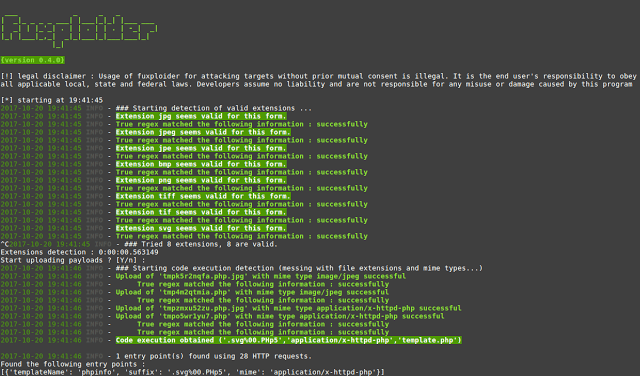
299Exploitation Toolsfuxploider – File Upload Vulnerability Scanner And Exploitation Tool
fuxploider is an open source penetration testing tool that automates the process of detecting and exploiting file upload forms flaws. This tool...
-

 282Hack Tools
282Hack ToolsCommix – Automated Command Injection and Exploitation Tool
Commix (short for [comm]and [i]njection e[x]ploiter) is an automated tool that you can use to test web-based applications with the view to...
-
 313Remote Administration Tools
313Remote Administration ToolsPupy – A Cross-platform Remote Administration and Post-Exploitation Tool
Pupy is an opensource, cross-platform (Windows, Linux, OSX, Android), multi-function RAT (Remote Administration Tool) and post-exploitation tool mainly written in python. It...
-
 219Exploitation Tools
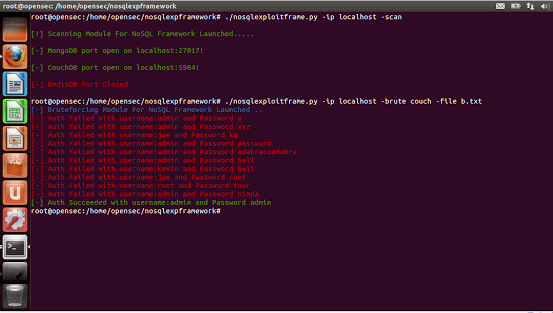
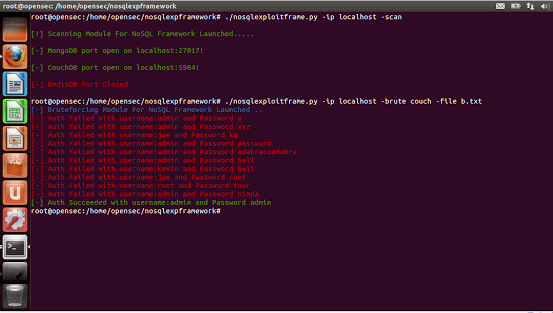
219Exploitation ToolsNoSQL Exploitation Framework 2.0 – A Framework For NoSQL Scanning and Exploitation
A FrameWork For NoSQL Scanning and Exploitation Framework Authored By Francis Alexander. Added Features: First Ever Tool With Added Support For Mongo,Couch,Redis,H-Base,Cassandra...
-
 266Exploitation Tools
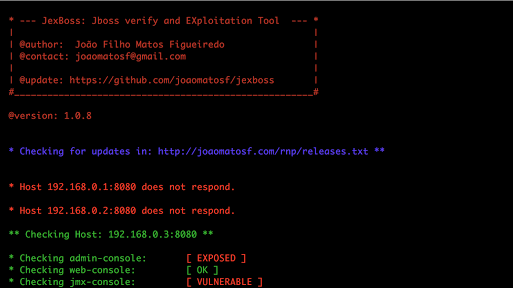
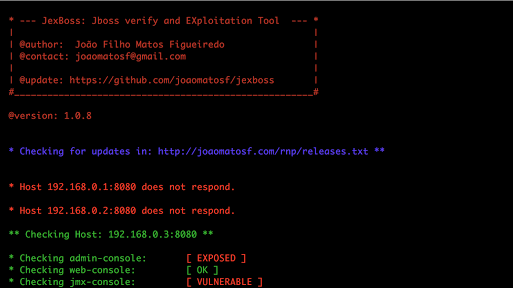
266Exploitation ToolsJexBoss – JBoss (and others Java Deserialization Vulnerabilities) verify and Exploitation Tool
JexBoss is a tool for testing and exploiting vulnerabilities in JBoss Application Server and others Java Platforms, Frameworks, Applications, etc. Requirements Python...
-
 280Exploitation
280ExploitationRouterSploit – Router Exploitation Framework
The RouterSploit Framework is an open-source exploitation framework dedicated to embedded devices. Requirements gnureadline requests paramiko beautifulsoup4 Installation sudo apt-get install python-requests...
-
 288Post Exploitation
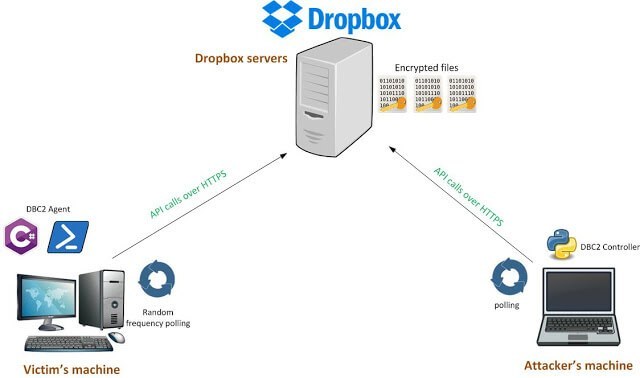
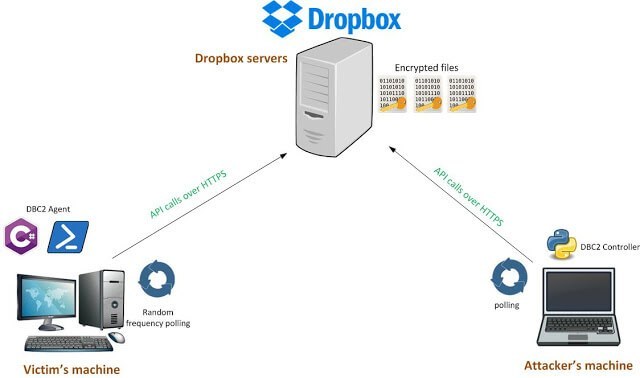
288Post ExploitationDBC2 (DropboxC2) – A Modular Post-Exploitation Tool, Composed Of An Agent Running On The Victim’S Machine
DBC2 (DropboxC2) is a modular post-exploitation tool, composed of an agent running on the victim’s machine, a controler, running on any machine,...
-
 150Hack Tools
150Hack ToolsThe Mole – Automatic SQL Injection Exploitation Tool
The Mole is an automatic SQL Injection exploitation tool. Only by providing a vulnerable URL and a valid string on the site...
-
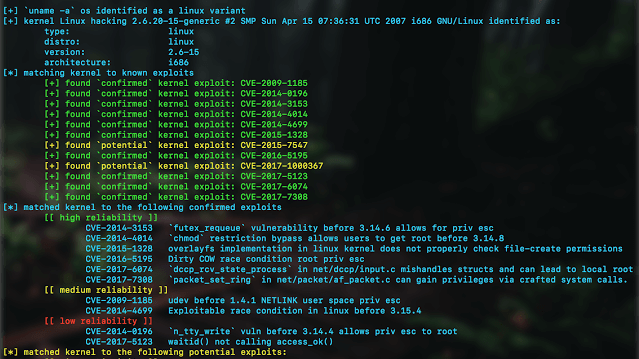
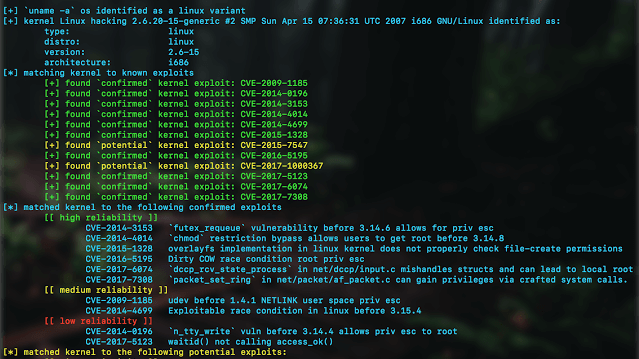 323Post Exploitation
323Post ExploitationKernelpop – Kernel Privilege Escalation Enumeration And Exploitation Framework
kernelpop is a framework for performing automated kernel exploit enumeration on Linux, Mac, and Windows hosts. Requirementspython3 Currently supported CVE’s: *CVE-2017-1000367 *CVE-2017-1000112...
-

 212Hack Tools
212Hack ToolsEmpire – Powershell Exploitation kit with Web Interface
Empire is a post-exploitation framework that includes a pure-PowerShell2.0 Windows agent, and a pure Python 2.6/2.7 Linux/OS X agent. The framework offers...
-
 271Exploitation
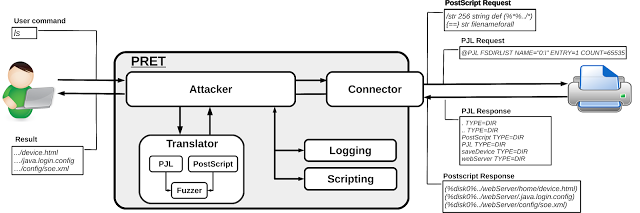
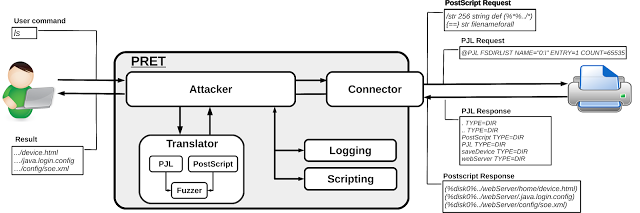
271ExploitationPrinter Exploitation Toolkit – Hacking Printers
PRET is a new tool for printer security testing developed in the scope of a Master’s Thesis at Ruhr University Bochum. It...
-
 243Vulnerabilities
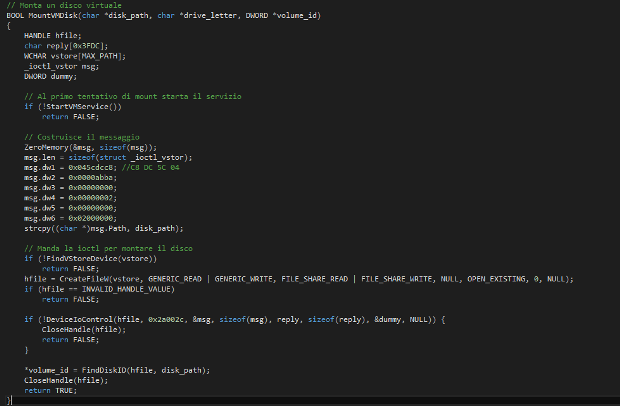
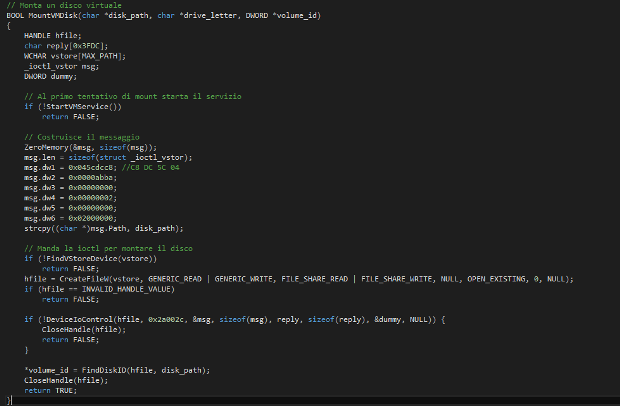
243VulnerabilitiesPost-exploitation: Mounting vmdk files from Meterpreter
Whenever I get a shell on a Windows system with VMware installed I feel a certain frustration at not being able to...
-

 196Vulnerabilities
196VulnerabilitiesOnePlus OTAs: Analysis & Exploitation
In this blog post we present new trivial vulnerabilities found on OnePlus One/X/2/3/3T OxygenOS & HydrogenOS. They affect the latest versions (4.1.3/3.0)...
-
 132Hackers Repository
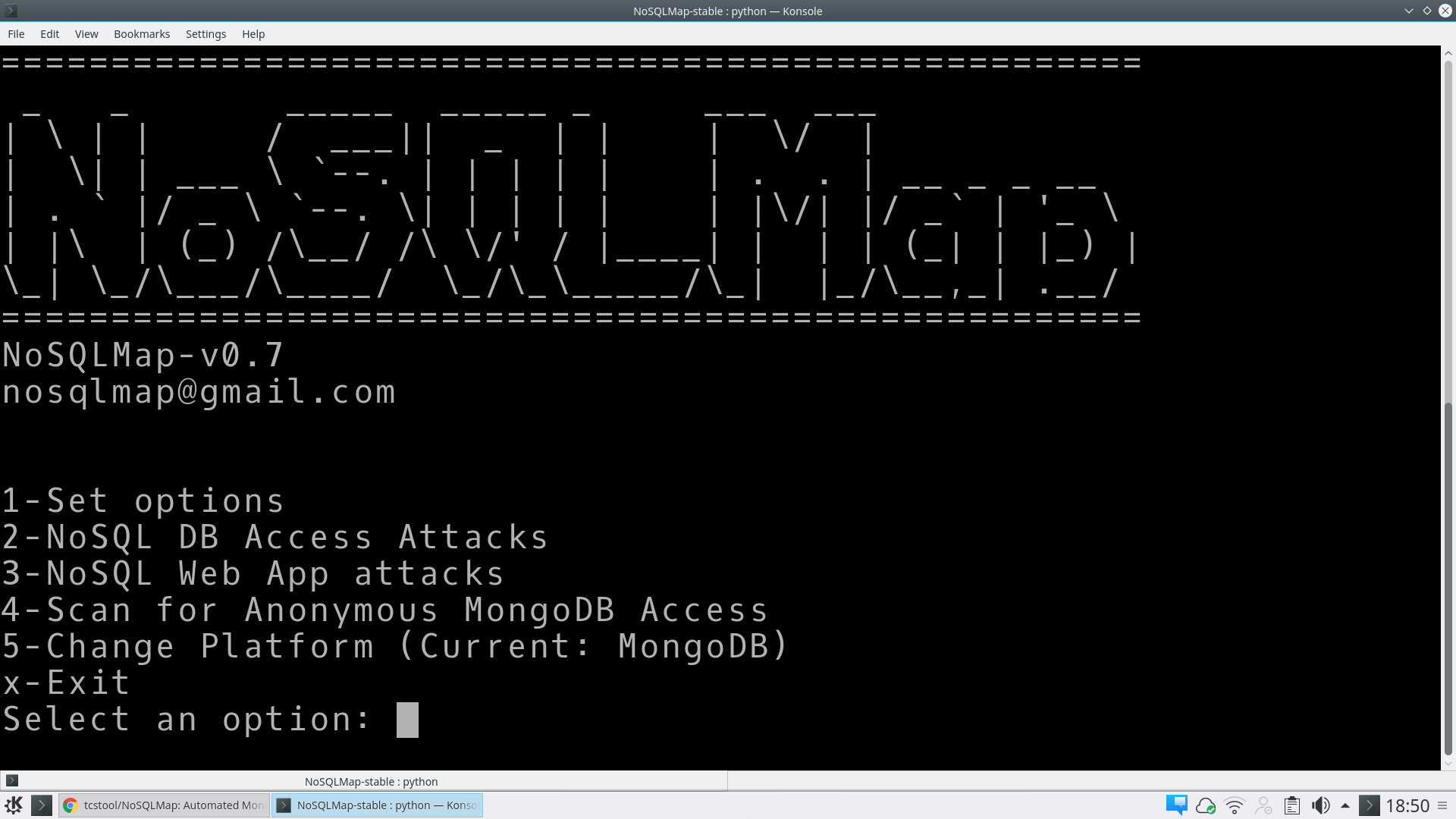
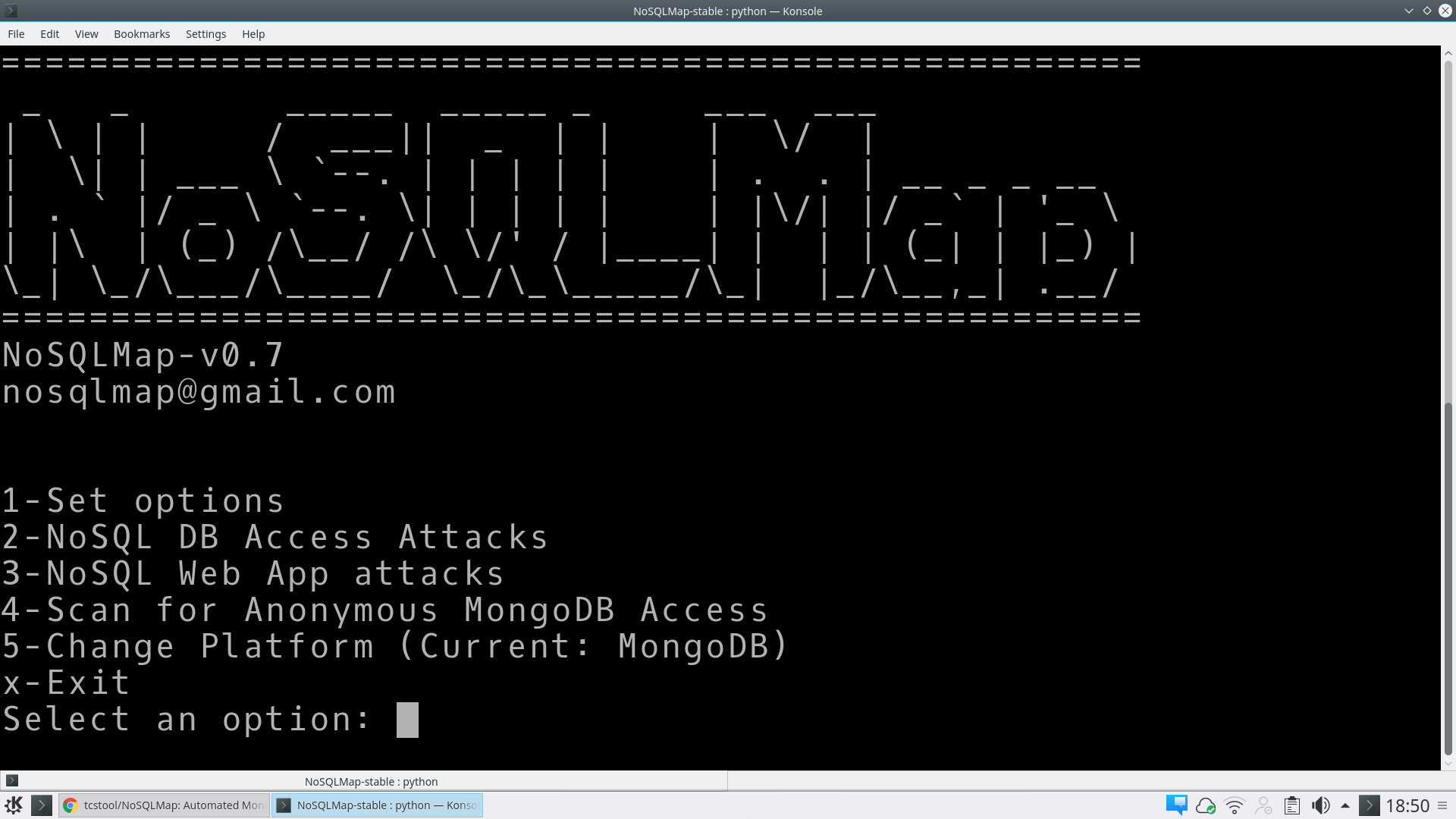
132Hackers RepositoryNoSQLMap – Automated Mongo database and NoSQL web application exploitation tool
Automated Mongo database and NoSQL web application exploitation tool http://www.nosqlmap.net DOWNLOAD NOSQL https://github.com/tcstool/NoSQLMap NoSQLMap NoSQLMap v0.7 Introduction NoSQLMap is an open source...
-
 280Vulnerabilities
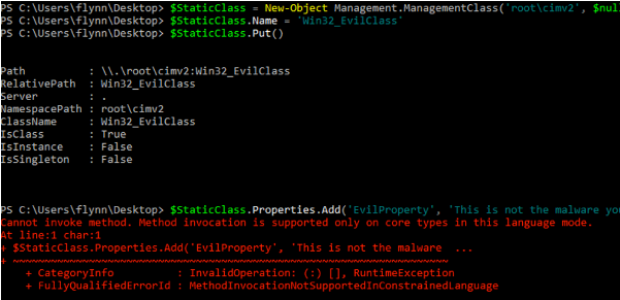
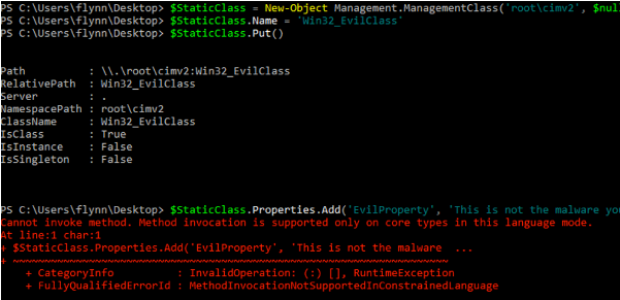
280VulnerabilitiesWMImplant – A WMI Based Agentless Post-Exploitation RAT Developed in PowerShell
Just over one year ago (November 2015), I released WMIOps, a PowerShell script that enables a user to carry out different actions...
-
 310Windows
310WindowsWindows exploitation in 2016
We are pleased to present our annual report Windows exploitation in 2016. In this latest version of our report, we offer a...
-

 304How To
304How ToCommix – Automated All-In-One OS Command Injection And Exploitation Tool
Commix, other wise known as [ comm ]and [ i ]njection e[ x ]ploiter is an automated tool written by that can...
-

 77Incidents
77IncidentsCNACOM – Open Source Exploitation via Strategic Web Compromise
Since a full proof of concept for CVE-2016-0189 vulnerability was published on GitHub, Zscaler ThreatLabZ has been closely tracking its proliferation. The...






