Search results for "Hacking"
-
 185Incidents
185IncidentsLiverpool FC will pay a $ 1M fine for hacking and stealing data of Manchester City players
According to the English newspaper The Mirror, this weekend the Premier League has just revealed a very big secret that Liverpool FC...
-

 391Cyber Events
391Cyber EventsHow Vapes Can Be Used For Hacking Computers
The popularity of vaping has been increasing over the past years. Many people that used to smoke traditional cigarettes are now switching...
-
 400Geek
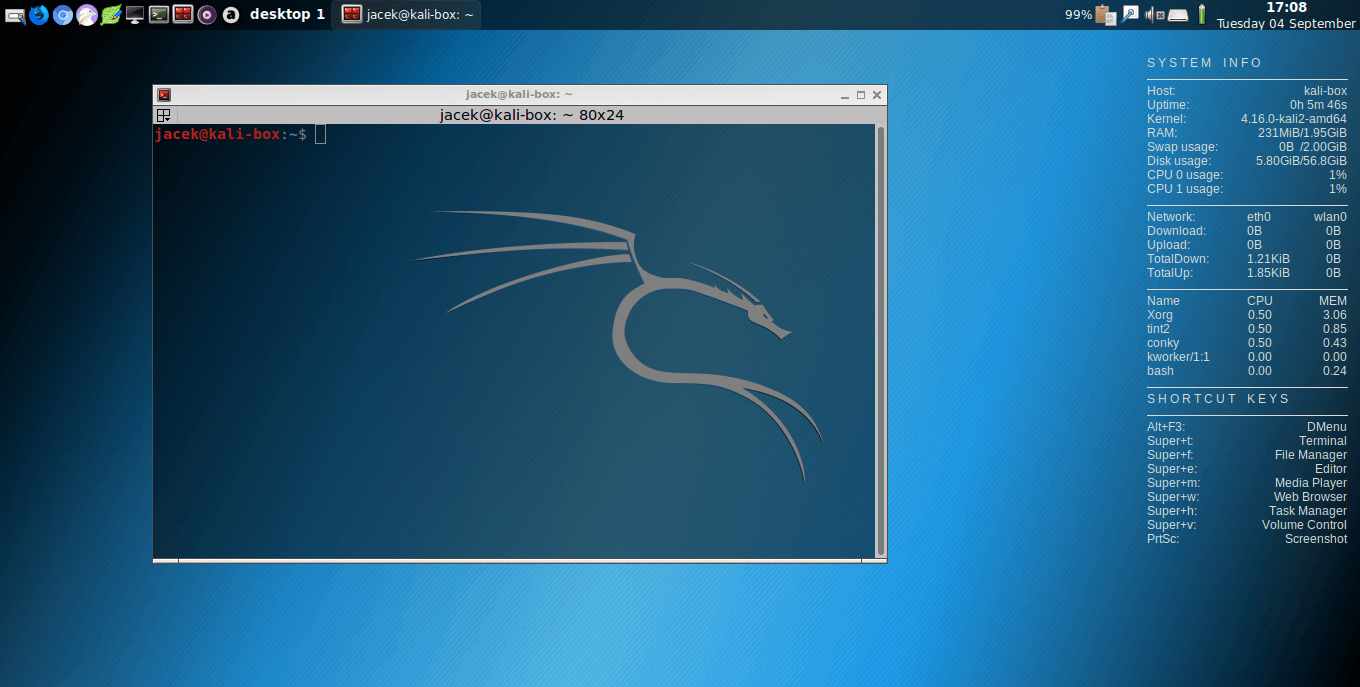
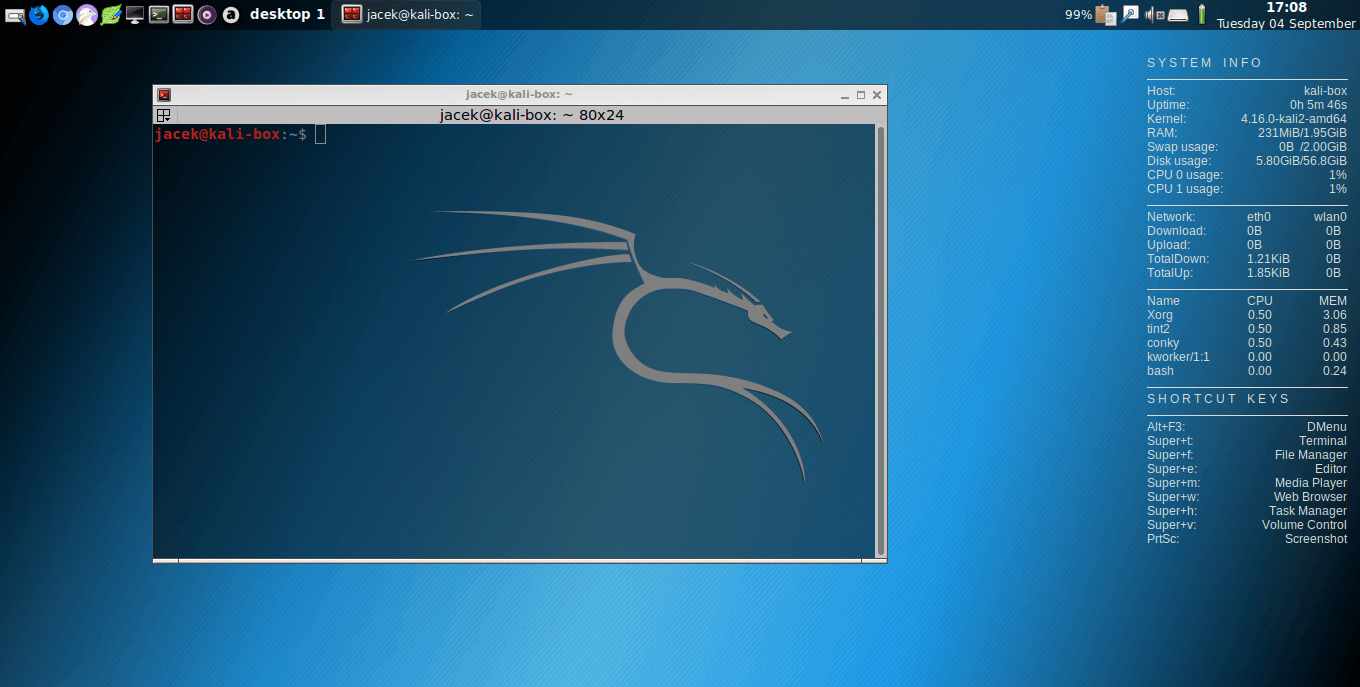
400GeekKali Linux 2019.3 Released For Ethical Hacking Enthusiasts
Earlier this year in May, the folks at Offensive Security shipped Kali Linux 2019.2 — the second Kali release of 2019. The...
-

 424Data Security
424Data SecurityGoogle hackers found malicious websites hacking iPhones
According to Google hackers, iPhone hacking spree has been going on for years. In July 2014, Google announced Project Zero where a...
-

 394Hacked
394HackediPhone Is Vulnerable! How Websites Have Been Hacking iPhones For Years?
Today, security researchers at Google shattered the common belief that iPhones are non-susceptible to hacking. The researchers have revealed that a number...
-

 294Vulnerabilities
294VulnerabilitiesGoogle Uncovers How Just Visiting Some Sites Were Secretly Hacking iPhones For Years
Beware Apple users! Your iPhone can be hacked just by visiting an innocent-looking website, confirms a terrifying report Google researchers released earlier...
-
 475Data Breach
475Data BreachCapital One Hacker Also Accused of Hacking 30 More Companies and CryptoJacking
Former Amazon employee Paige Thompson, who was arrested last month in relation to the Capital One data breach, has been accused of...
-

 425Hackers Repository
425Hackers Repository50 Free Hacking Ebooks Collection PDF 2019 – HackingVision
50 Free Hacking Ebooks Collection PDF 2019 Ethical Hacking, Hacking ebooks pdf, Hacking ebooks free download, hacking ebooks collection, Best Hacking eBooks....
-

 443Malware
443MalwareLYCEUM APT Hackers Attack Critical Infrastructures Over a Year using Several Hacking Tools
A new threat group dubbed LYCEUM spotted attacking critical infrastructure organizations including oil, gas and possibly telecommunications using several hacking tools. The...
-

 389Data Security
389Data SecurityNew hacking technique to exploit antivirus and extract data from servers
TokyoWesterns’ team of web application security experts just unveiled a new attack method that, if exploited, would allow the extraction of sensitive...
-
 293Incidents
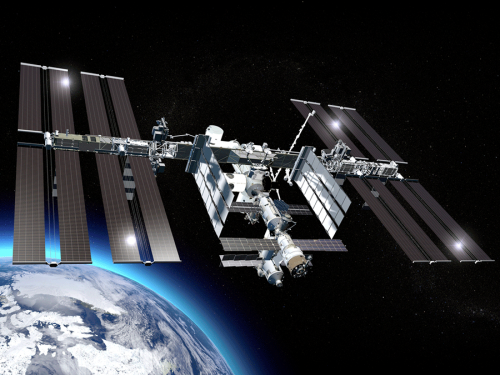
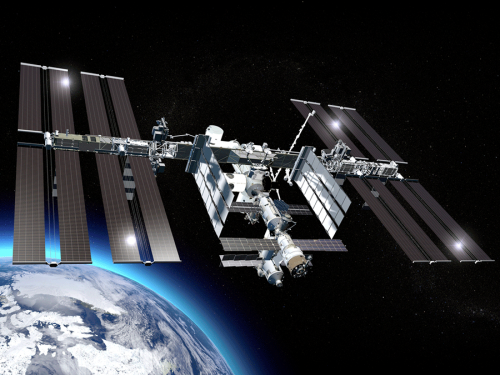
293IncidentsThe first hacking from space; an astronaut hacks her ex’s bank account from Space Station
An unprecedented event related to cybersecurity and space missions was revealed this weekend. According to web application security specialists, a National Space...
-

 547Exploitation
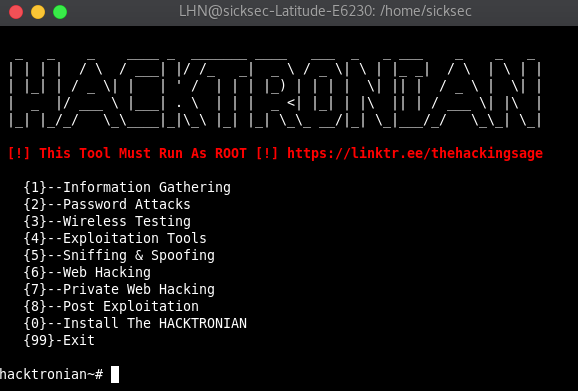
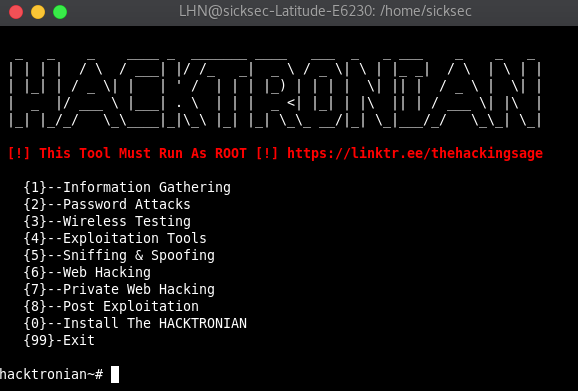
547ExploitationHacktronian – All In One Hacking Tool For Linux & Android
Pentesing Tools That All Hacker Needs, Hacktronian is an all in one hacking toolkit. HACKTRONIAN Menu : Information Gathering Password Attacks Wireless...
-

 379Hacked
379HackedNasty Botnet Neutrino Caught Hacking Other Hackers’ Web Shells
A crypto mining botnet operation, going for almost a year, is hijacking web shells of other hackers, according to report from Positive...
-

 370Malware
370MalwareYou want to make millions in Fortnite? This videogame hacking tool is a ransomware
Fortnite is one of the most used online games nowadays, surpassing 250 million players worldwide. These figures have begun to attract the...
-
 424Tutorials
424TutorialsHack Website Using Google Hacking or google Dorking – Part I
You normally use Google for finding anything online. Google is most widely used search engine all over the world. Google Hacking is...
-
 588Hacking Tools
588Hacking ToolsHacktronian – An all in one hacking tool for Linux and Android
Hacktronian is an open-source penetration testing framework designed for social engineering and multiple server side attacks, it has a number of...
-
 450Malware
450MalwareNewly Discovered Hacking Tools Remotely control the Hacked Computers via a GUI & Command-Line Interface
Researchers discovered two new malicious hacking tools (BalkanRAT, BalkanDoor) from the ongoing campaign Balkans that act as a remote access trojan and...
-

 423Vulnerabilities
423VulnerabilitiesNew Bluetooth vulnerability allows hacking iOS and Android devices
Wireless protocols are not exempt from cybersecurity risks. IT security audit specialists say that more than one billion Bluetooth-enabled devices (smartphones, IoT...
-

 206Data Security
206Data SecurityIs it possible to kill a person by hacking a speaker?
Science fiction has set this scenario on multiple times: A scientist develops a machine that generates sounds capable of controlling minds, altering...
-

 253Hackers Repository
253Hackers RepositoryAwesome Cellular Hacking Hacking Cellular Networks
Awesome-Cellular-Hacking Please note multiple researchers published and compiled this work. This is a list of their research in the 3G/4G/5G Cellular...
-
 553Exploitation
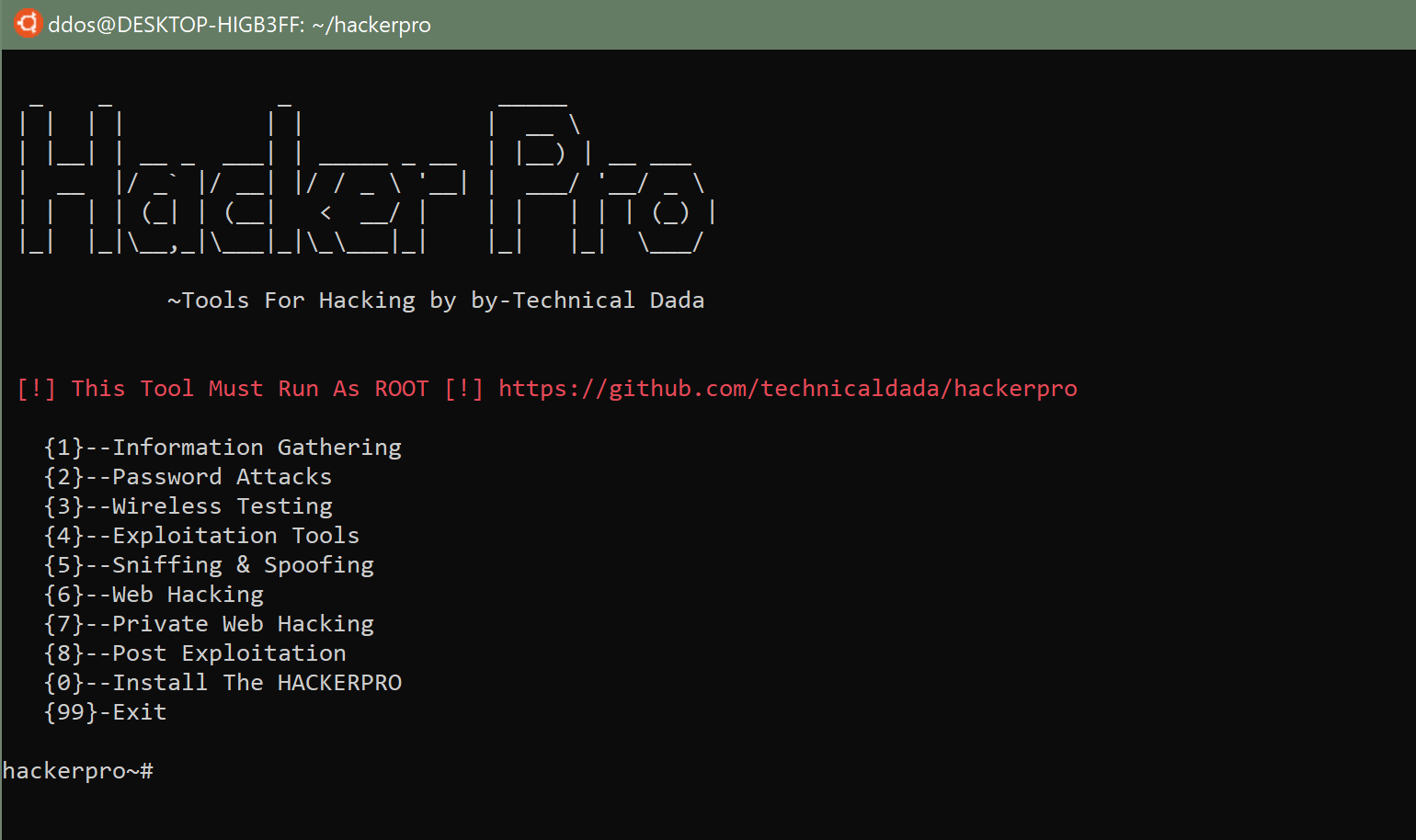
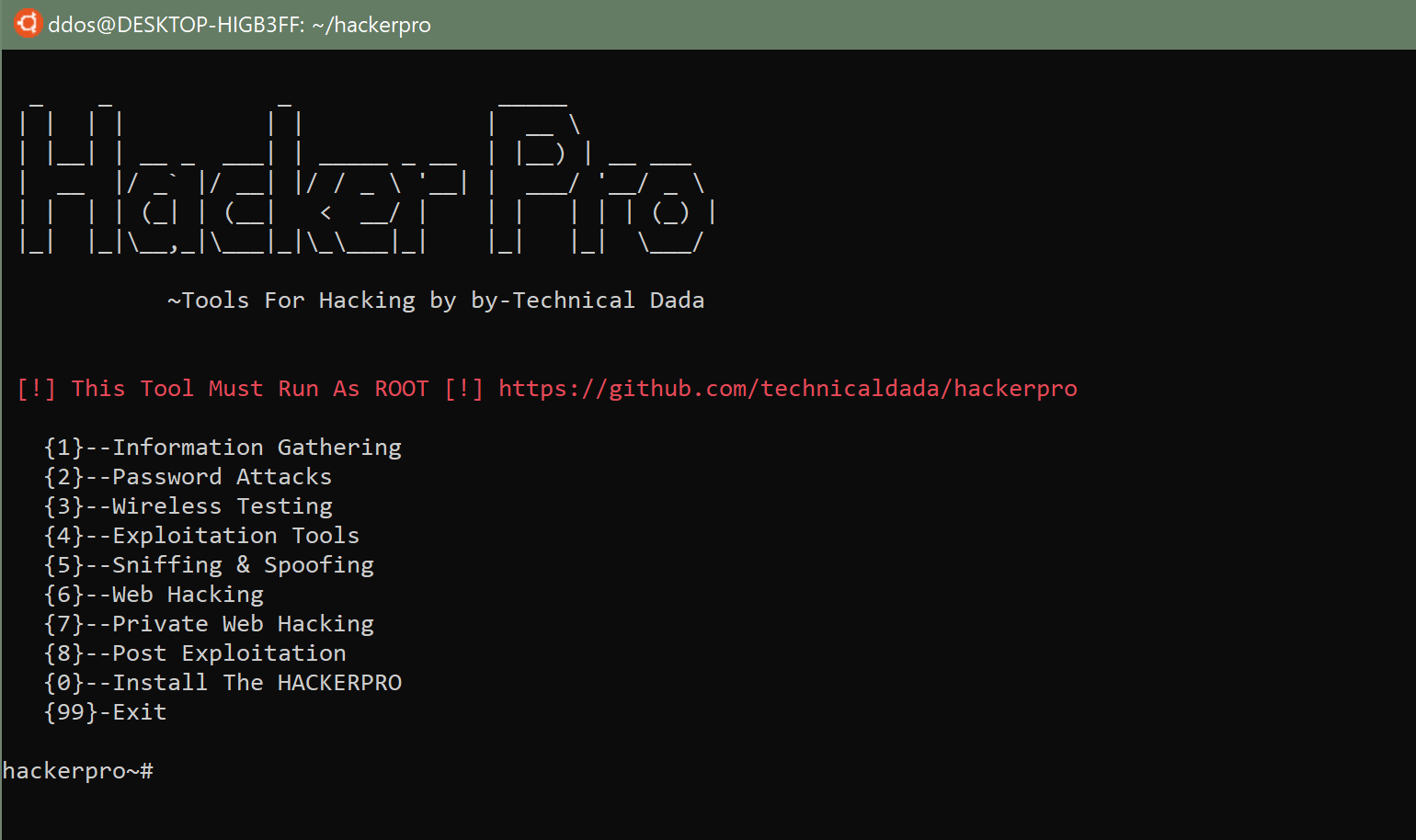
553ExploitationHackerPro: All in One Hacking Tool for Linux & Android
All in One Hacking Tool for Linux & Android (Termux). HACKERPRO Menu : Information Gathering Password Attacks Wireless Testing Exploitation Tools Sniffing...






