Search results for "Hacking"
-

 2.4KMalware
2.4KMalwareChinese Hackers Attacking Major Telecoms Using Sophisticated Hacking Tools
The security researchers of Cybereason Nocturnus have recently detected three malicious cyber-espionage campaigns that are targeting the major telecommunication companies all over...
-

 1.4KData Security
1.4KData SecurityExposing Chinese hackers: how they’re hacking telecom companies and listening to your calls
A group of researchers discovered three different groups of threat actors linked to the Chinese government using previously seen Microsoft Exchange exploits...
-

 4.3KHacking
4.3KHackingOn course for a good hacking
A story of how easily hackers could hit a hole-in-one with the computer network of a premier golf club in the UK.
-

 534Leaks
534LeaksSecurity Experts Tie Covert Wiper Tool to Iranian Railway Infrastructure Hacking Attempt
Security experts at SentinelOne have come across a previously unidentified data-scrubbing malware tool that was a portion of an uncontrollable malware attack...
-

 2.5KTutorials
2.5KTutorialsTop 15 hacking tools for doing penetration testing from mobile phones
Pentesting has become one of the main practices of the cybersecurity community and even represents an important source of income for independent...
-

 675Incidents
675IncidentsThe most dangerous hacking group encrypts over a million computers in 17 countries and hacks more than 1000 companies
The operators of the REvil ransomware, one of the most dangerous hacking groups in the world, have deployed a massive new operation....
-

 905Cyber Attack
905Cyber AttackNSA, FBI Reveal Hacking Methods Used by Russian Military Hackers
An ongoing brute-force attack campaign targeting enterprise cloud environments has been spearheaded by the Russian military intelligence since mid-2019, according to a...
-
 4.9KMalware
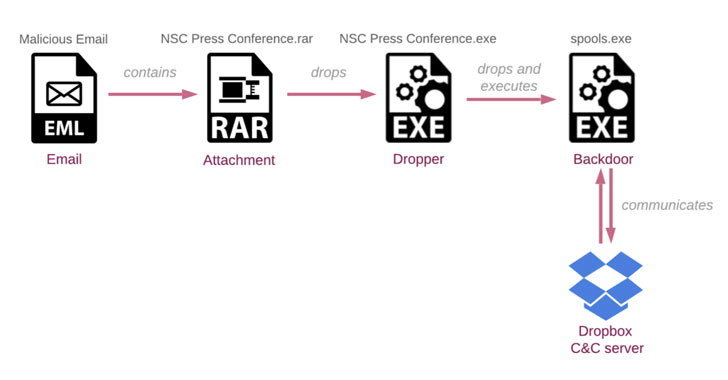
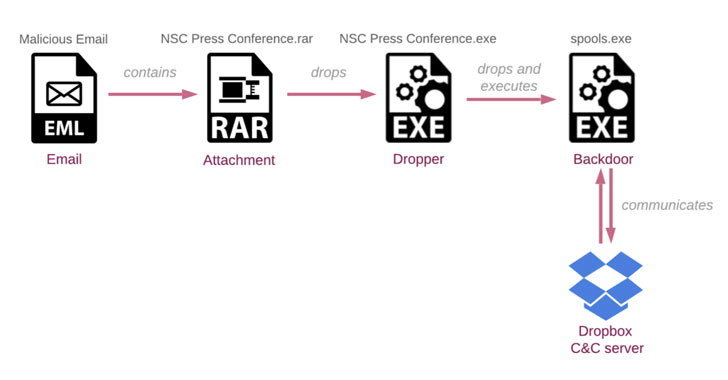
4.9KMalwareIndigoZebra APT Hacking Campaign Targets the Afghan Government
Cybersecurity researchers are warning of ongoing attacks coordinated by a suspected Chinese-speaking threat actor targeting the Afghanistan government as part of an...
-

 1.5KData Security
1.5KData SecurityPickpocketers in Latin America are stealing iPhones and hacking banking apps but nobody knows how
A new cybercriminal campaign is hitting the streets of Sao Paulo, Brazil, with a group dedicated to stealing iPhone devices in order...
-

 2.8KIncidents
2.8KIncidentsHacking campaign seeks to steal NFT tokens from thousands of digital artists
A recent hacking campaign targeting digital artists and creators of non-funible tokens (NFT) led to the theft of sensitive information and an...
-

 1.5KMalware
1.5KMalwareBackdoorDiplomacy: the new hacking group targeting politicians and diplomats worldwide
A newly discovered hacking group is deploying an ambitious malicious campaign against politicians in Africa and the Middle East. The operation, identified...
-

 2.3KIncidents
2.3KIncidentsHacking into encrypted messaging platform ANOM to arrest of 525 criminals, seizing of tons of drugs and millions of dollars
The Federal Bureau of Investigation (FBI), in collaboration with the Australian Federal Police announced the end of Operation Ironside or Trojan Shield,...
-
 1.8KCyber Attack
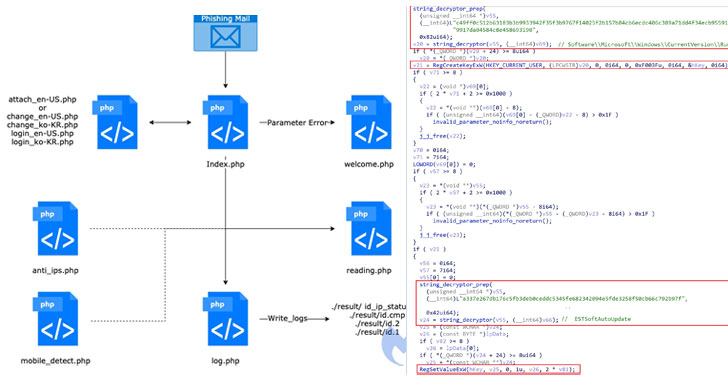
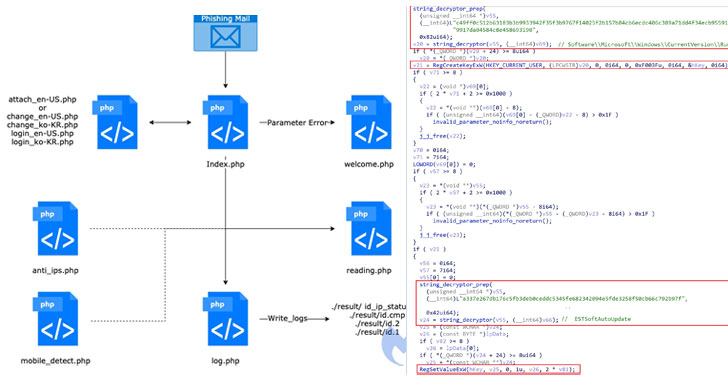
1.8KCyber AttackResearchers Uncover Hacking Operations Targeting Government Entities in South Korea
A North Korean threat actor active since 2012 has been behind a new espionage campaign targeting high-profile government officials associated with its...
-

 1.1KTutorials
1.1KTutorialsTop 15: Tools to do internal vulnerability assessment of the network. Hacking into corporate networks
Pentesting is one of the most important processes in cybersecurity, as it allows a correct analysis of internal vulnerabilities to determine the...
-

 3.9KTutorials
3.9KTutorialsStep by step process of hacking ATMs using black box. ATM jackpotting
Attacks on ATMs on the street have evolved in great steps, leaving behind the methods of physical engagement of these machines to...
-

 3.5KMalware
3.5KMalwareNew wave of ransomware attacks linked to Avaddon hacking group
Cybersecurity specialists report detecting a new wave of attacks potentially linked to the Avaddon ransomware variant. This is a strain detected in...
-

 3.2KMalware
3.2KMalwareNew Financially Motivated UNC2529 Hacking Group Targets U.S. Organizations with 3 Malware
The cybersecurity researchers of FireEye’s cybersecurity team at Mandiant have recently proclaimed that the phishing campaign, which mopped across financial, communications, medical,...
-

 4.5KTutorials
4.5KTutorialsHow to do pentesting of VoIP servers? Step by step tutorial for hacking VoIP networks
The adoption of Voice over Internet Protocol (VoIP) technology is becoming broader, allowing organizations to communicate over huge distances and very easily....
-
 3.4KData Security
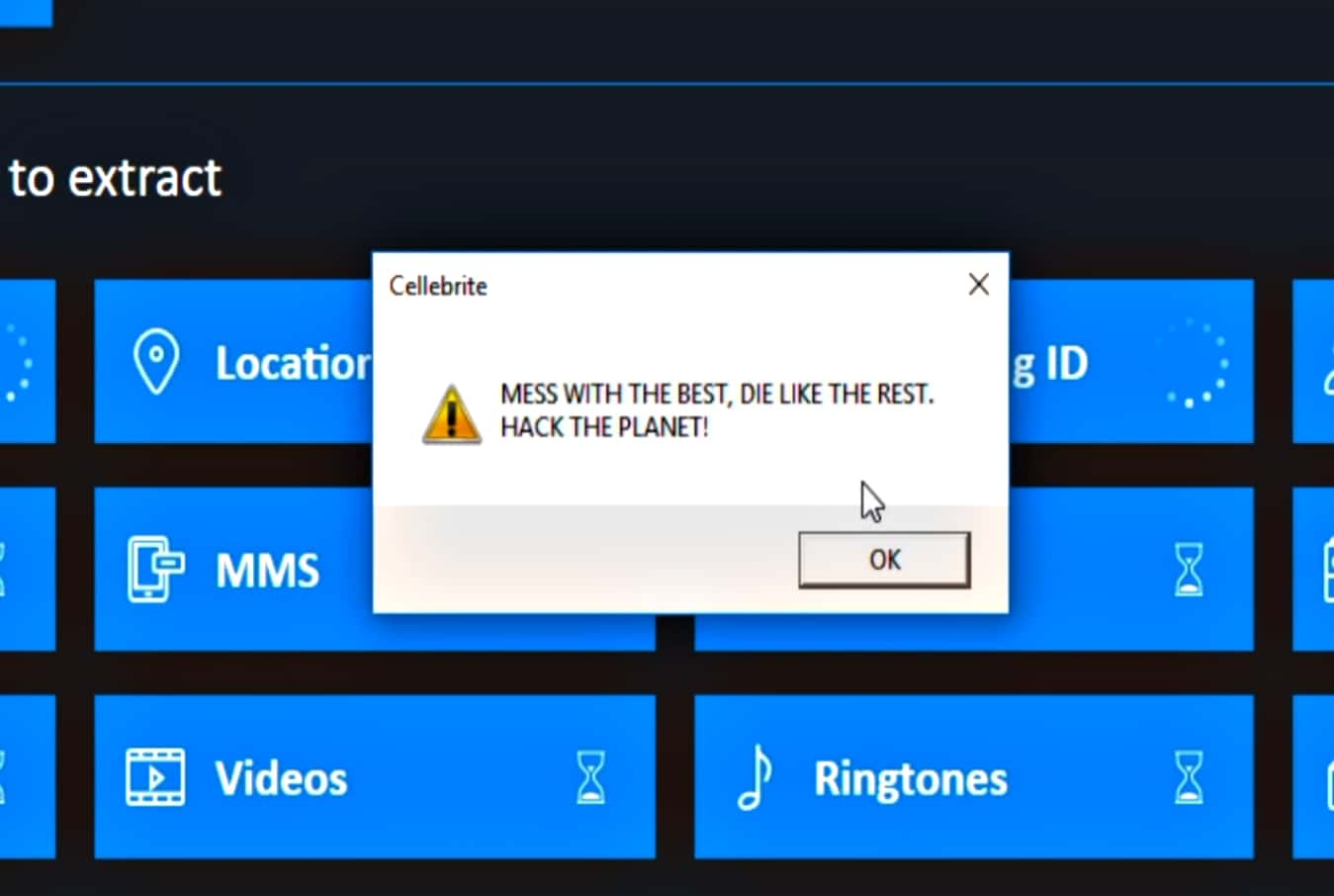
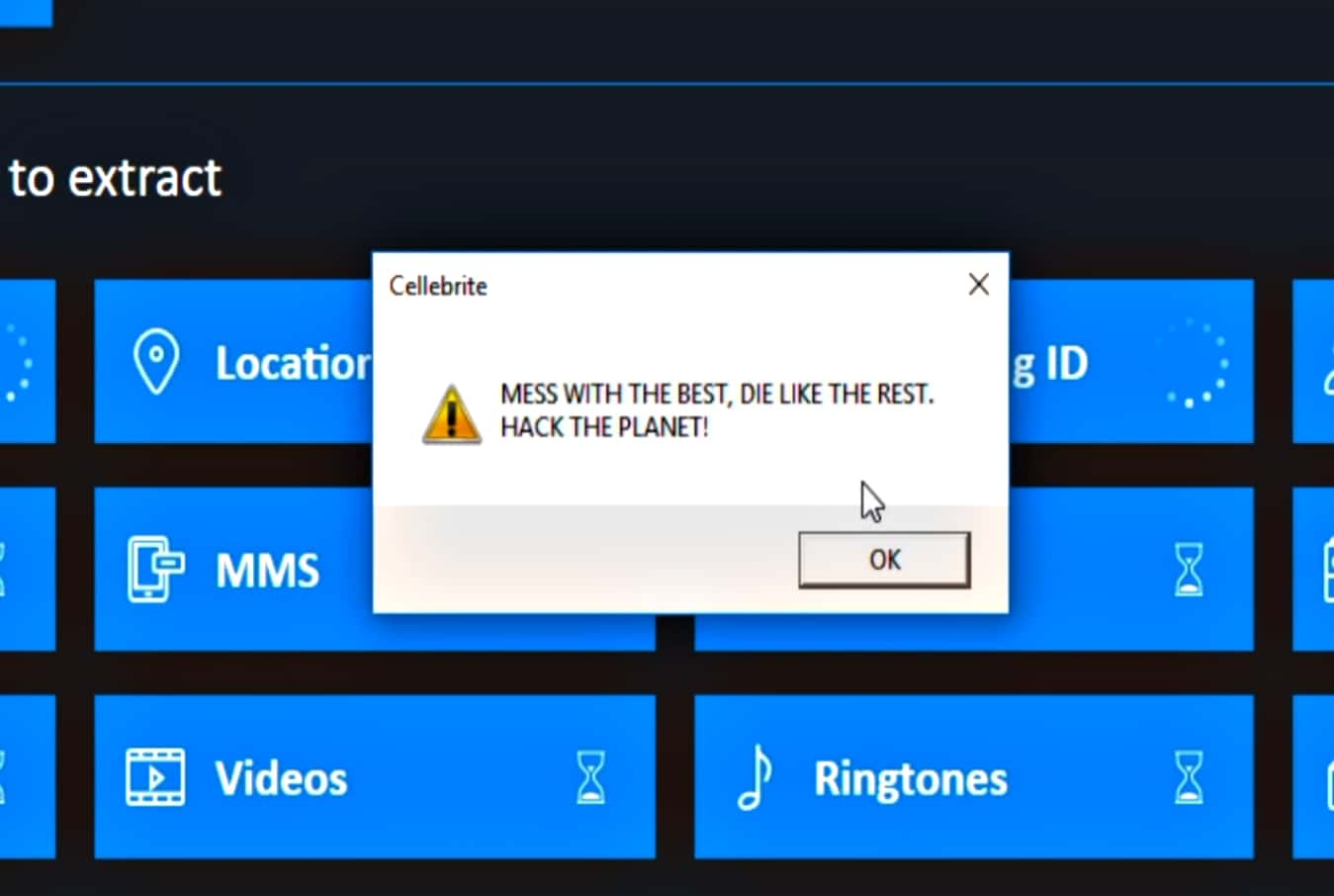
3.4KData SecuritySignal CEO hacks Cellebrite cellphone hacking, cracking tool
Moxie Marlinspike, CEO of Signal states that since Cellebrite itself makes a living from undisclosed vulnerabilities, he decided to disclose the vulnerability...
-

 2.1KData Breach
2.1KData BreachBigBasket Data Leak – Over 20 Million Personal Records Published on Hacking Forum
More than 20 million BigBasket users’ data were recently leaked on a well-known hacking forum known as “ShinyHunter” It’s a popular online...
-

 3.8KData Security
3.8KData SecurityMore than 1 million admin credentials to access Windows RDP servers for sale on dark web hacking forum
A recent security report mentions that a dark web leak containing access keys has been published to more than 1.3 million Windows...






