Search results for "Hacking"
-
 2.4KData Breach
2.4KData BreachLapsus$ Hacking Group Claims to Have Stolen Sensitive Data From Software Gaint Okta Solutions
Recently on March 22, 2022, several screenshots from the computer of one of Okta’s third-party support technicians were published online by the...
-
 3.7KTutorials
3.7KTutorialsBest web application firewall testing tools: Find out what security solutions a target website is using. WAF hacking
A web application firewall (WAF) is a program designed to analyze incoming requests to a web server and, according to the rules...
-

 814Malware
814MalwareRussian Ransomware Gang Retool Custom Hacking Tools of Other APT Groups
A Russian-speaking ransomware outfit likely targeted an unnamed entity in the gambling and gaming sector in Europe and Central America by repurposing...
-

 4.9KIncidents
4.9KIncidentsA member of one of the most dangerous hacking groups has been arrested
A court in Ontario, Canada has sentenced Sebastien Vachon-Desjardins to seven years in prison after pleading guilty to participating as an affiliate...
-

 1.5KIncidents
1.5KIncidentsHacking group offers Russian soldiers 5 million rubles for each surrendered tank
Having successfully compromised more than 300 Russian websites, Anonymous hackers are offering the Kremlin-sent military 5 million rubles (about $45,000 USD) for...
-

 1.7KIncidents
1.7KIncidentsFive individuals arrested for the hacking and millionaire theft from a cryptocurrency exchange platform
Spanish authorities announced the arrest of five people accused of hacking a cryptocurrency exchange company, an incident that resulted in the theft...
-
 3.2KMalware
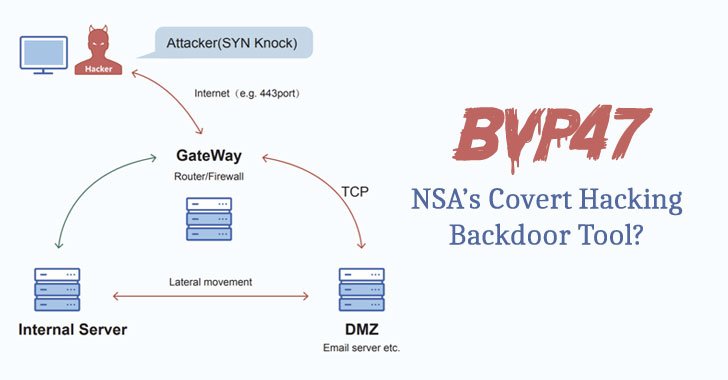
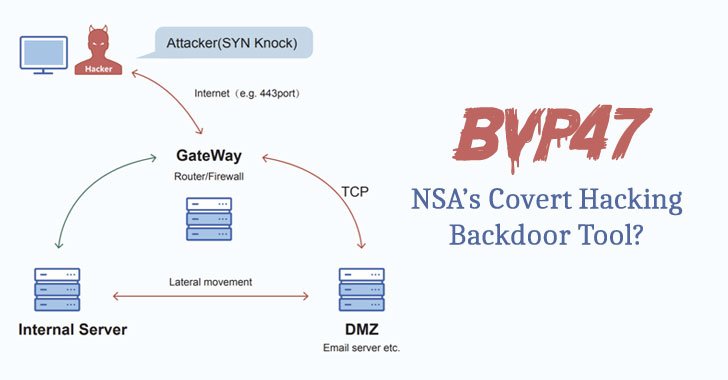
3.2KMalwareChinese Experts Uncover Details of Equation Group’s Bvp47 Covert Hacking Tool
Researchers from China’s Pangu Lab have disclosed details of a “top-tier” backdoor put to use by the Equation Group, an advanced persistent...
-

 3.0KVulnerabilities
3.0KVulnerabilities9-Year-Old Unpatched Email Hacking Bug Uncovered in Horde Webmail Software
Users of Horde Webmail are being urged to disable a feature to contain a nine-year-old unpatched security vulnerability in the software that...
-

 1.4KMalware
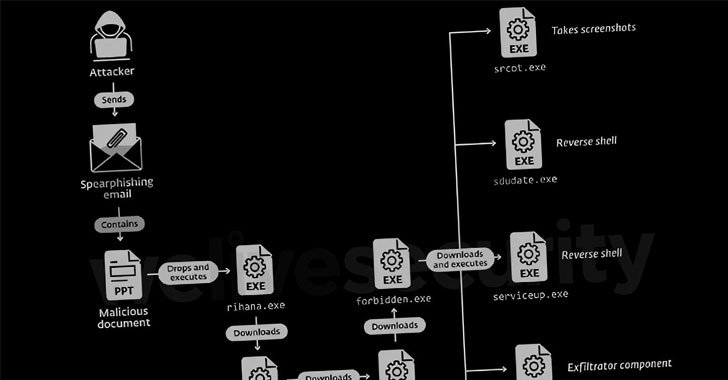
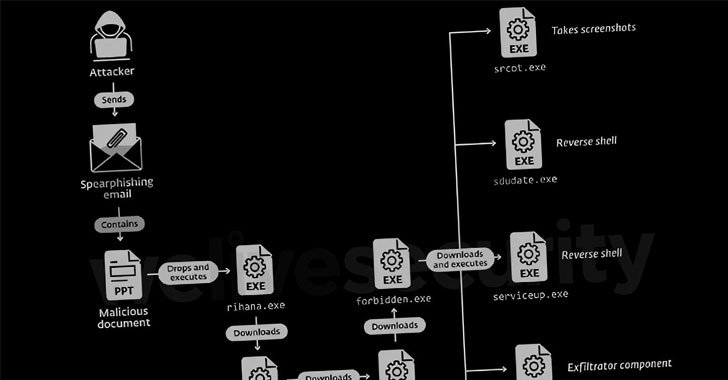
1.4KMalwareExperts Warn of Hacking Group Targeting Aviation and Defense Sectors
Entities in the aviation, aerospace, transportation, manufacturing, and defense industries have been targeted by a persistent threat group since at least 2017...
-
 3.1KCyber Attack
3.1KCyber AttackDoNot Hacking Team Targeting Government and Military Entities in South Asia
A threat actor with potential links to an Indian cybersecurity company has been nothing if remarkably persistent in its attacks against military...
-

 1.9KData Security
1.9KData SecurityBlueNoroff APT that hacked Bangladesh Bank is now only focusing on hacking cryptocurrency businesses and exchanges
For almost five years, SecureList researchers reported the identification of an Advanced Persistent Threat (APT) group apparently linked to the infamous Lazarus...
-
 1.4KCyber Attack
1.4KCyber AttackUS Cyber Command Links ‘MuddyWater’ Hacking Group to Iranian Intelligence
The U.S. Cyber Command (USCYBERCOM) on Wednesday officially confirmed MuddyWater’s ties to the Iranian intelligence apparatus, while simultaneously detailing the various tools...
-

 1.1KIncidents
1.1KIncidentsHacking GMAT exam 780 out of 800: Police arrests a gang who worked with Russian hackers
In a statement, the Strategic Operations Unit of the Delhi Police, India, unveiled the dismantling of a hacking operation dedicated to resolving...
-

 2.8KMalware
2.8KMalwareBeware of Fake Telegram Messenger App Hacking PCs with Purple Fox Malware
Trojanized installers of the Telegram messaging application are being used to distribute the Windows-based Purple Fox backdoor on compromised systems. That’s according...
-

 2.6KVulnerabilities
2.6KVulnerabilitiesNew Log4j attack allows hacking devices that are not exposed to internet via localhost
In recent days it was revealed the detection of a new attack vector for the successful exploitation of remote code execution (RCE)...
-
 3.3KMalware
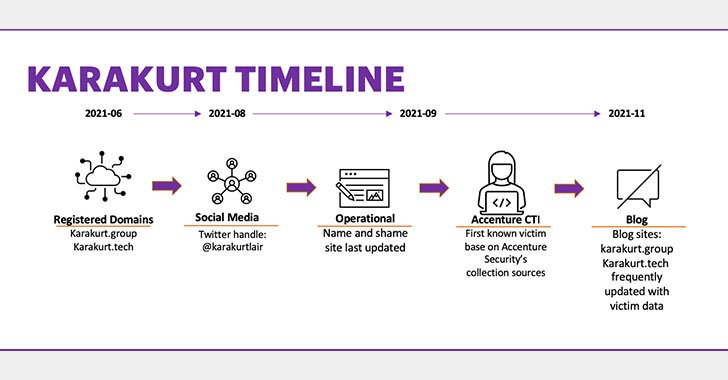
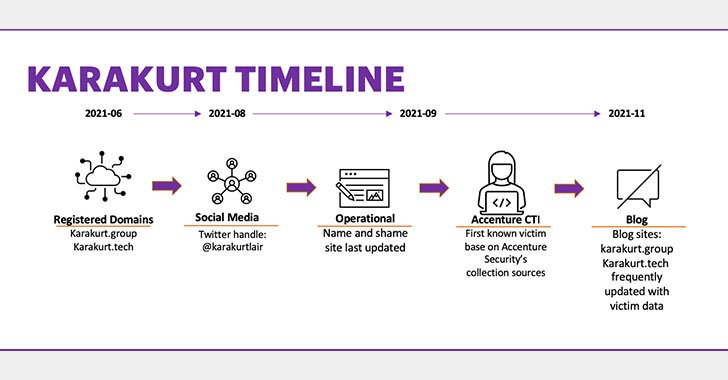
3.3KMalwareKarakurt: A New Emerging Data Theft and Cyber Extortion Hacking Group
A previously undocumented, financially motivated threat group has been connected to a string of data theft and extortion attacks on over 40...
-

 3.4KData Security
3.4KData SecurityUS Military’s Hacking Unit to take on ransomware gangs
The Unit’s boss Gen. Paul Nakasone said that the US military computer operatives are ready to target ransomware gangs and state actors,...
-

 1.7KMalware
1.7KMalwareOver 300,000 MikroTik Devices Found Vulnerable to Remote Hacking Bugs
At least 300,000 IP addresses associated with MikroTik devices have been found vulnerable to multiple remotely exploitable security vulnerabilities that have since...
-

 419Malware
419MalwareIsrael Bans Sales of Hacking and Surveillance Tools to 65 Countries
Israel’s Ministry of Defense has dramatically restricted the number of countries to which cybersecurity firms in the country are allowed to sell...
-
 1.4KCyber Crime
1.4KCyber CrimeRussian language hacking forums warming up to Chinese hackers
Russian cybercrime and hacking forums are opening doors to Chinese and English-speaking threat actors, which so far had been a relatively restricted...
-
 3.1KMalware
3.1KMalwareRedCurl Corporate Espionage Hackers Return With Updated Hacking Tools
A corporate cyber-espionage hacker group has resurfaced after a seven-month hiatus with new intrusions targeting four companies this year, including one of...






