Search results for "Hacking"
-

 4.2KVulnerabilities
4.2KVulnerabilitiesHacking Nintendo Switch, 3DS, and Wii console. Vulnerability allows hacking remote console by simply engaging in an online gaming session with the victim
Nintendo has secretly released a fix for a security flaw that might have allowed hackers to access compromised Switch, 3DS, and Wii...
-
 4.1KMalware
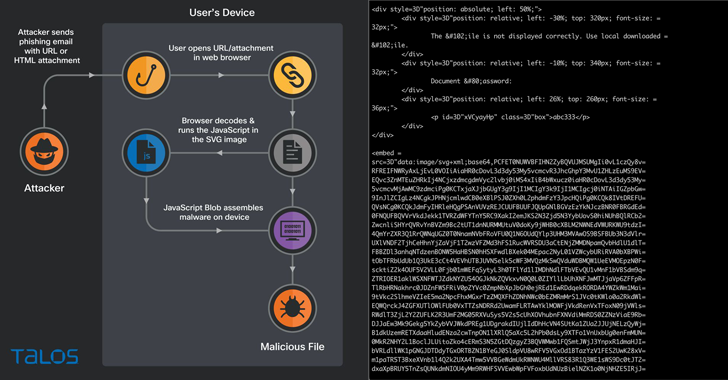
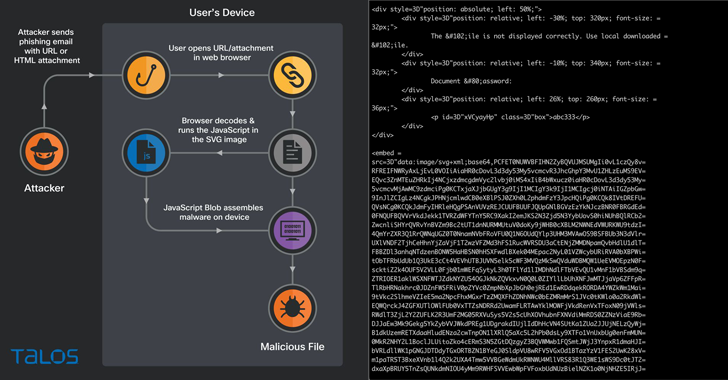
4.1KMalwareHacking Using SVG Files to Smuggle QBot Malware onto Windows Systems
Phishing campaigns involving the Qakbot malware are using Scalable Vector Graphics (SVG) images embedded in HTML email attachments. The new distribution method...
-

 2.7KPrivacy
2.7KPrivacyHacking baby monitors can be child’s play: Here’s how to stay safe
Make sure that the device that’s supposed to help you keep tabs on your little one isn’t itself a privacy and security...
-

 946Malware
946MalwareAPT-36 Hackers Using New Hacking Tools & TTPs To Attack Indian Government Orgs
The cybersecurity analysts at Zscaler ThreatLabz have recently detected a new malicious version of a multi-factor-authentication (MFA) solution, known as Kavach, which...
-
 4.3KVulnerabilities
4.3KVulnerabilitiesCritical RCE Vulnerability Discovered in Popular Cobalt Strike Hacking Software
HelpSystems, the company behind the Cobalt Strike software platform, has released an out-of-band security update to address a remote code execution vulnerability...
-

 1.1KData Security
1.1KData SecurityGang of 31 cyber criminals arrested for stealing cars via hacking software
In a coordinated operation on October 10 throughout the three nations, 31 people were detained. A total of 22 addresses were raided,...
-

 568Vulnerabilities
568VulnerabilitiesTwo critical WhatsApp vulnerabilities allow hacking WhatsApp (Android & iOS) via call or video file. Update immediately
Two security flaws in WhatsApp’s chat app for iOS and Android that might have been used to remotely execute malware on the device...
-

 3.0KCyber Attack
3.0KCyber AttackChina Accuses NSA’s TAO Unit of Hacking its Military Research University
China has accused the U.S. National Security Agency (NSA) of conducting a string of cyberattacks aimed at aeronautical and military research-oriented Northwestern...
-

 2.9KIncidents
2.9KIncidentsLockBit falls victim to a large-scale DDoS attack after hacking into Entrust. LockBit accuses Entrust of being behind the cyberattack
Entrust is accused by LockBit of being behind the cyberattack. If such were the case, a genuine security firm would never retaliate...
-

 4.5KData Security
4.5KData SecurityHow criminals are hacking key fobs to quickly and quietly steal cars
High-tech criminals are increasingly targeting push-start automobiles by hacking into key fobs, leaving many New Orleans car owners stranded according to WSDU...
-

 3.7KIncidents
3.7KIncidentsDIGITAL OCEAN USERS’ EMAILS LEAKED AFTER MAILCHIMP HACKING INCIDENT
DigitalOcean has revealed that some of its customers’ emails were exposed to attackers thanks to an attack on the Mailchimp email marketing...
-
 3.3KMalware
3.3KMalwareLNK files is one of the most common way of hacking into enterprise environment
HP has highlighted a new wave of cybercriminals who spread families of ‘malware’ in business environments using files with shortcuts or links...
-
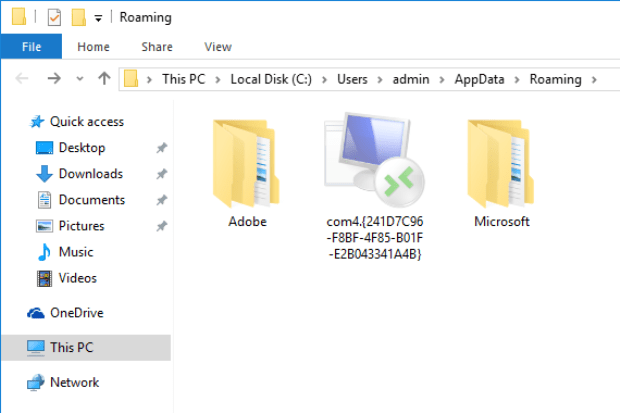
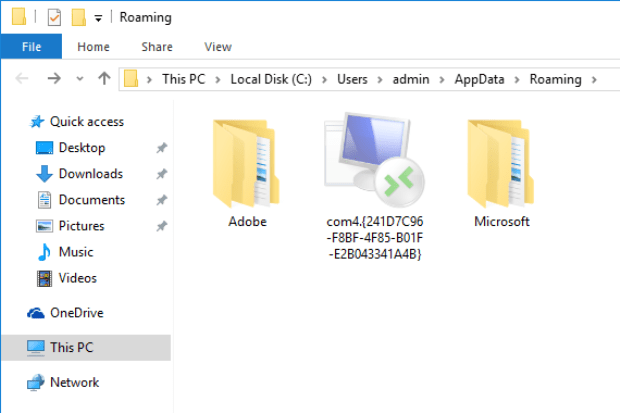
 2.4KData Security
2.4KData SecurityKali Linux 2022.3 released with new hacking tools and improved performance
We can say that Kali Linux is one of the most important distributions in terms of computer security. Now they have released...
-
 4.3KMalware
4.3KMalwareChinese Hackers Using New Manjusaka Hacking Framework Similar to Cobalt Strike
Researchers have disclosed a new offensive framework referred to as Manjusaka that they call is a “Chinese sibling of Sliver and Cobalt...
-

 2.4KVulnerabilities
2.4KVulnerabilitiesCritical vulnerability allows unlocking, starting & stealing Honda Cars without key. Hacking Honda vehicles
Rolling-PWN attack vulnerability CVE-2021-46145 affecting all Honda cars models that exist from the year 2012 up to the year 2022. This vulnerability...
-

 5.0KLeaks
5.0KLeaksOver 1 Billion Individual Data Leaked Due to Alleged Chinese Police Database Hacking
In a leak that, if verified, could be one of the biggest data breaches in history, hackers might have obtained a wealth...
-
 4.5KMalware
4.5KMalwareZuoRAT Malware exclusively designed for hacking ASUS, Cisco, DrayTek, and NETGEAR SOHO routers
A new malware has been discovered that actively attacks home and small business routers in Europe and North America. That malware attacks...
-

 888Malware
888MalwareGALLIUM APT Hackers Using New Hacking Tool “PingPull” To Attack on Telecom & Government Sectors
An APT group named GALLIUM has recently been using a new and hard-to-detect remote access trojan named PingPull. The trojan is being...
-

 2.3KMalware
2.3KMalwareHacking Scenarios: How Hackers Choose Their Victims
Enforcing the “double-extortion” technique aka pay-now-or-get-breached emerged as a head-turner last year. May 6th, 2022 is a recent example. The State Department...
-

 2.9KIncidents
2.9KIncidentsIndian HDFC Bank deposits millions in customers’ accounts by mistake. Hacking incident or just a software flaw?
Last weekend, HDFC Bank clients received a message showing a non-exact balance in their accounts, making them believe they had received a...
-

 1.9KVulnerabilities
1.9KVulnerabilitiesZero-day vulnerability in Microsoft Office Pro Plus, Office 2013, Office 2016, and Office 2021 allows remote network hacking with just a single click
A few days ago, the security researcher known as “nao_sec” reported the detection of a file specially crafted Word document to exploit...






