Search results for "Hacking"
-

 3.3KMalware
3.3KMalwareFIN8 Revamped Hacking Toolkit with New Stealthy Attack Features
Syssphinx (aka FIN8) is a financially motivated cyber-crime group deploying revamped sardonic backdoor to deliver Noberus ransomware. This group has been active since...
-
 2.0KMalware
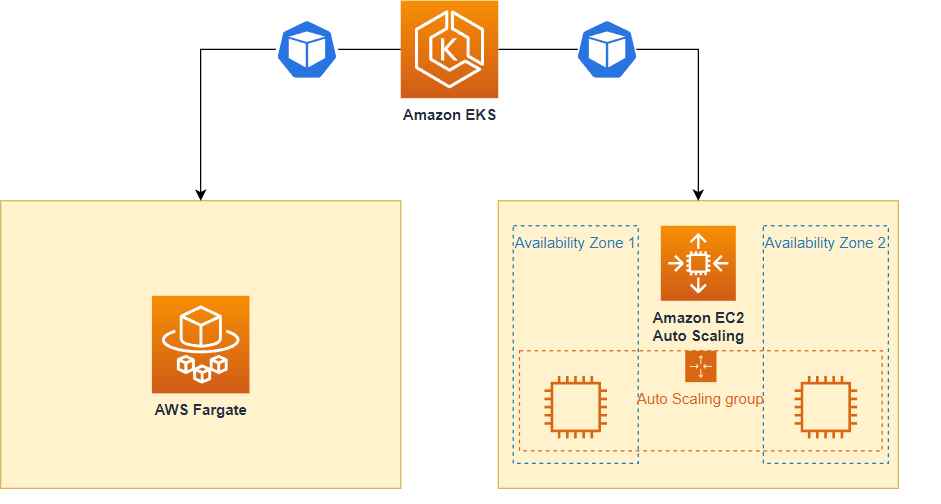
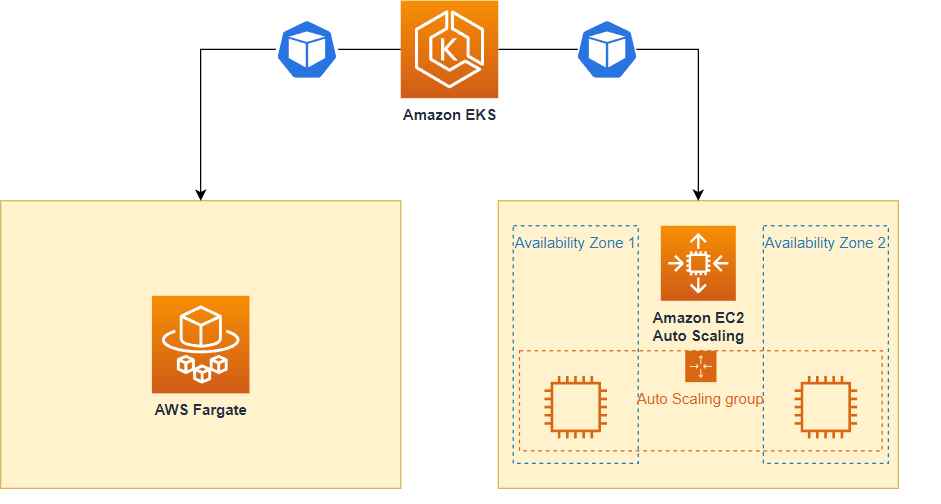
2.0KMalwareHow cyber criminals are hacking into AWS Fargate, EKS & evading cloudtrail logs detection
Sysdig, a company that specializes in cybersecurity intelligence, uncovered a sophisticated hacking operation known as Scarleteel in February. Since then, Scarleteel has...
-

 2.8KData Security
2.8KData SecurityHead of network security of a big cyber security company arrested for hacking into a company
An specialist in Russian cybersecurity who was sought by the United States has been arrested by officials in Kazakhstan, according to his...
-

 2.4KVulnerabilities
2.4KVulnerabilitiesHacking Grafana servers using Azure AD is quite possible
One of the most popular open-source systems for analytics and visualization, Grafana, was found to have a security flaw.This open-source platform serves...
-

 4.1KData Security
4.1KData SecurityHacking WooCommerce websites to get order details and customer personal information
The ever-changing topography of cyberspace always results in the introduction of new security flaws and vulnerabilities. A major vulnerability, which is now...
-
 4.5KData Security
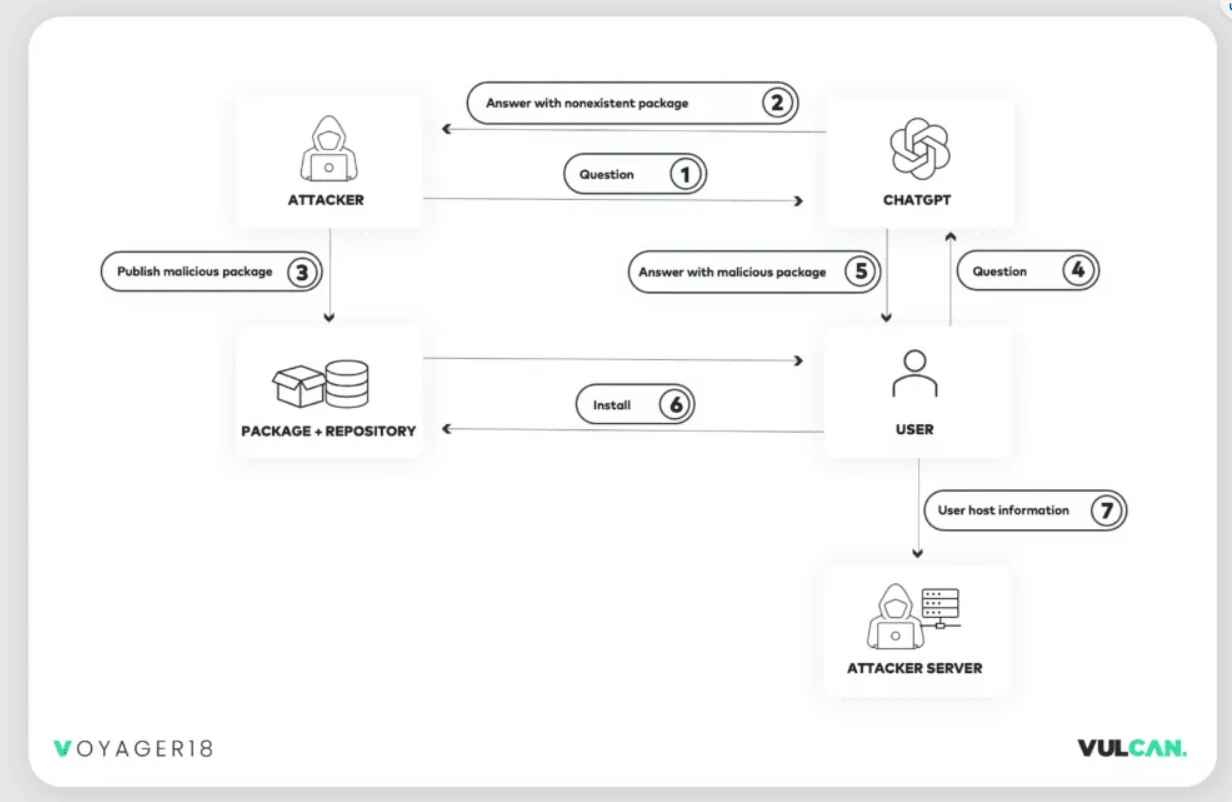
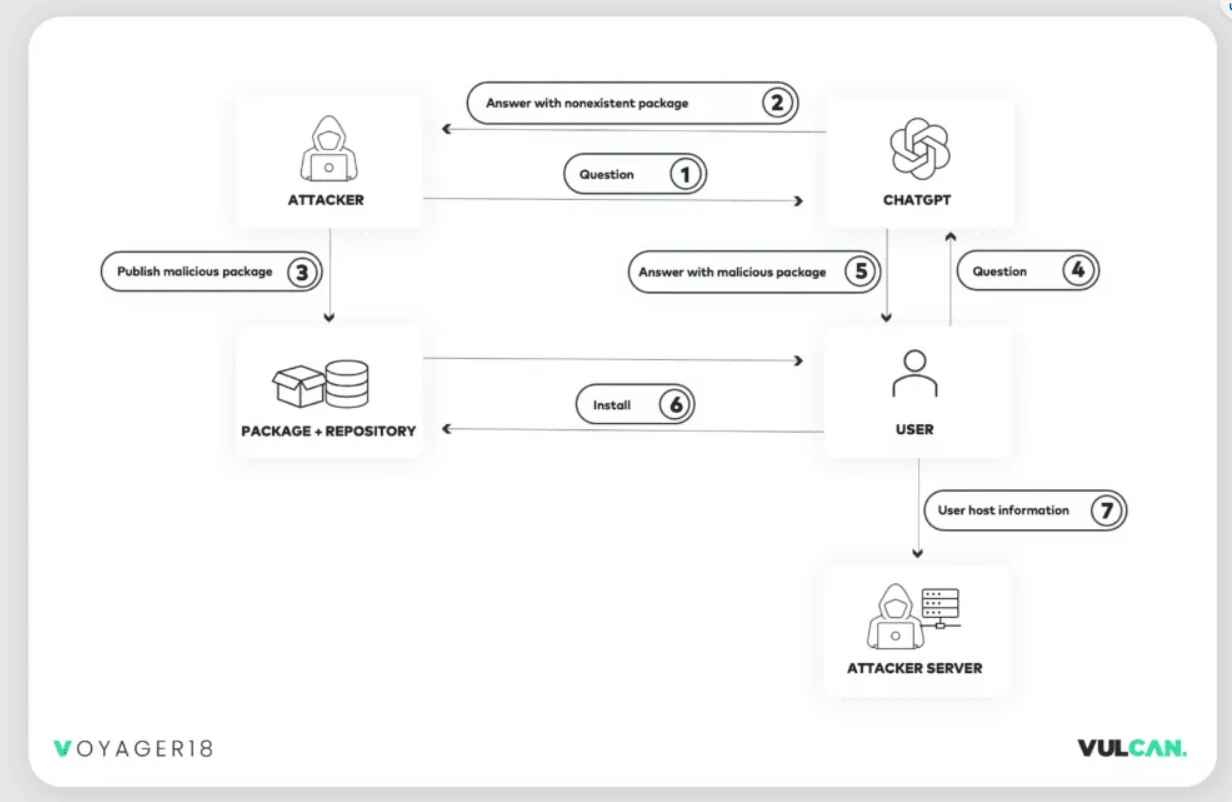
4.5KData SecurityNew undetectable technique allows hacking big companies using ChatGPT
According to the findings of recent study conducted, harmful packages may be readily propagated into development environments with the assistance of ChatGPT,...
-
 4.7KData Security
4.7KData SecurityNew phishing technique to allows hacking someone using .zip & .mov domains
When a victim visits a website ending in .ZIP, a recently developed phishing method known as “file archiver in the browser” may...
-

 2.7KData Security
2.7KData SecurityReconShark: New undetectable reconnaissance tool used by cybercriminals for hacking
Kimsuky is an advanced persistent threat (APT) organization that originates in North Korea and has a lengthy history of launching targeted attacks...
-

 3.2KVulnerabilities
3.2KVulnerabilitiesHacking and modifying patients DNA – RNA sequence becomes easy with these vulnerabilities
A major vulnerability with a ranking of 10.0 was discovered in specific universal copy service software that is used in some Illumina...
-
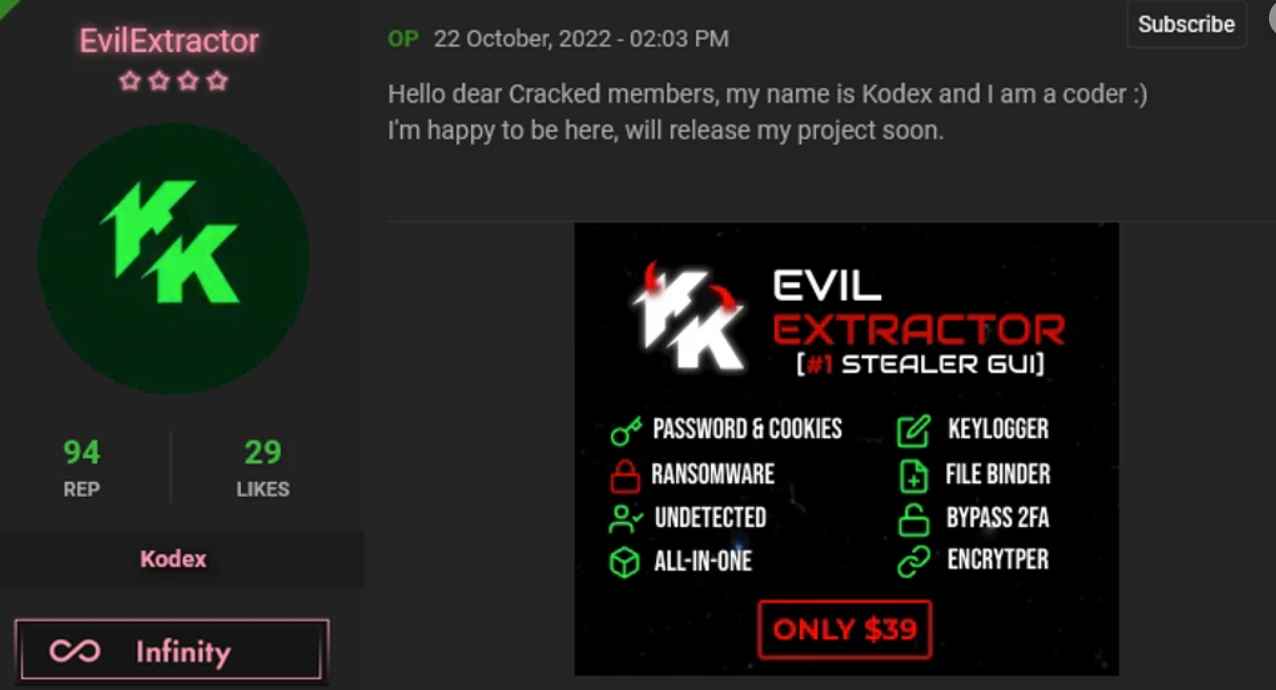
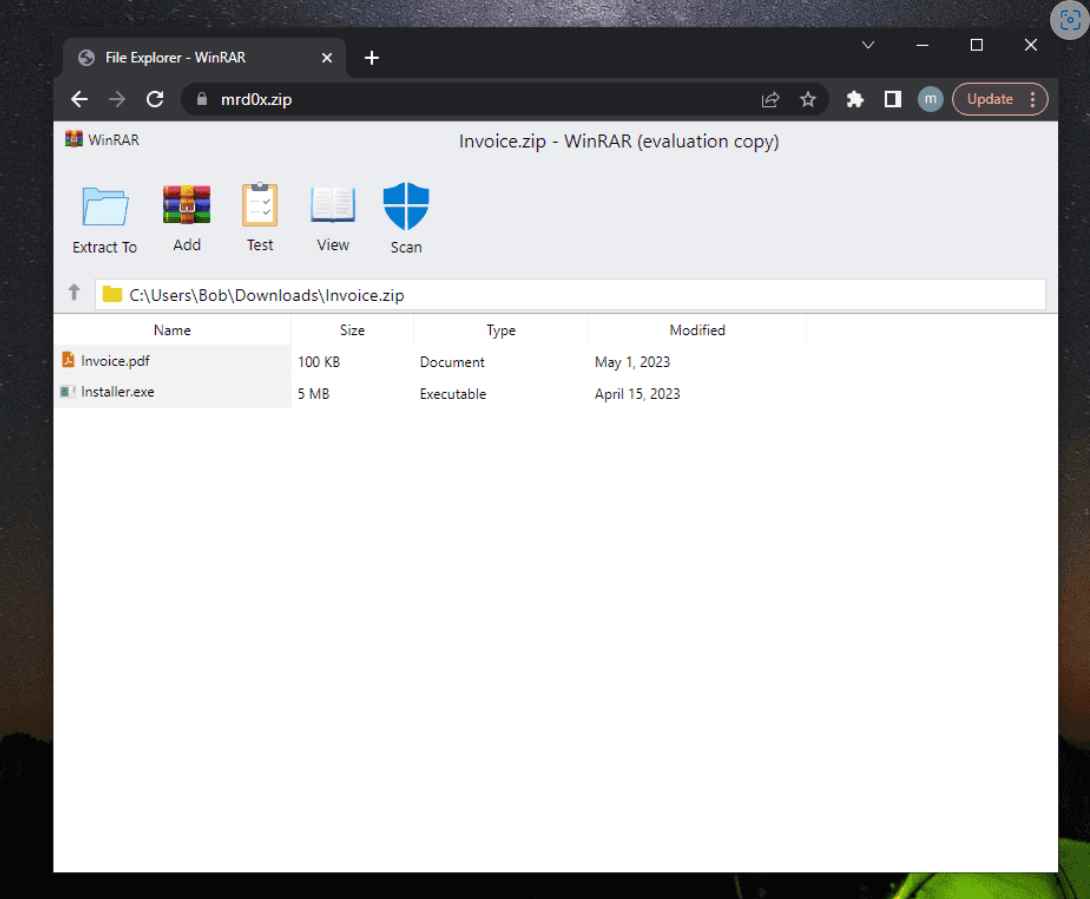
 2.4KMalware
2.4KMalwareNew famous all in one malware and hacking tool among cyber criminals: EvilExtractor
EvilExtractor is an attack tool that is meant to target Windows operating systems to extract data and files from endpoint devices. EvilExtractor...
-

 2.9KData Security
2.9KData SecurityHow people are hacking & stealing Lime e-bikes and scooters to convert them to personal bikes
A councillor has said that the public e-bikes are being hacked and ridden for free after videos on social media detailing how...
-
 4.5KMalware
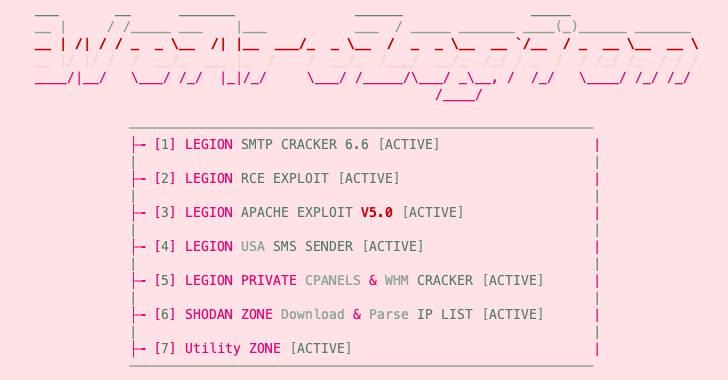
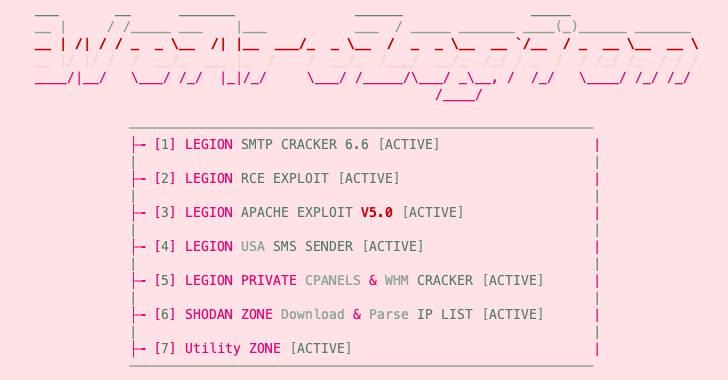
4.5KMalwareNew Python-Based “Legion” Hacking Tool Emerges on Telegram
An emerging Python-based credential harvester and a hacking tool named Legion is being marketed via Telegram as a way for threat actors...
-

 3.9KMalware
3.9KMalwareArid Viper Hacking Group Using Upgraded Malware in Middle East Cyber Attacks
The threat actor known as Arid Viper has been observed using refreshed variants of its malware toolkit in its attacks targeting Palestinian...
-

 3.1KVulnerabilities
3.1KVulnerabilitiesCritical Samba vulnerabilities easily allow hacking of servers
Samba is a free software project that runs on operating systems that are similar to UNIX and supports the Windows file sharing...
-

 753Vulnerabilities
753VulnerabilitiesHacking WPA1, WPA2, and WPA3 using 802.11 Wi-Fi standard vulnerability
An adversary may circumvent encryption for some communications by exploiting a flaw in the widespread 802.11 protocol, which enables them to do...
-
 222Data Security
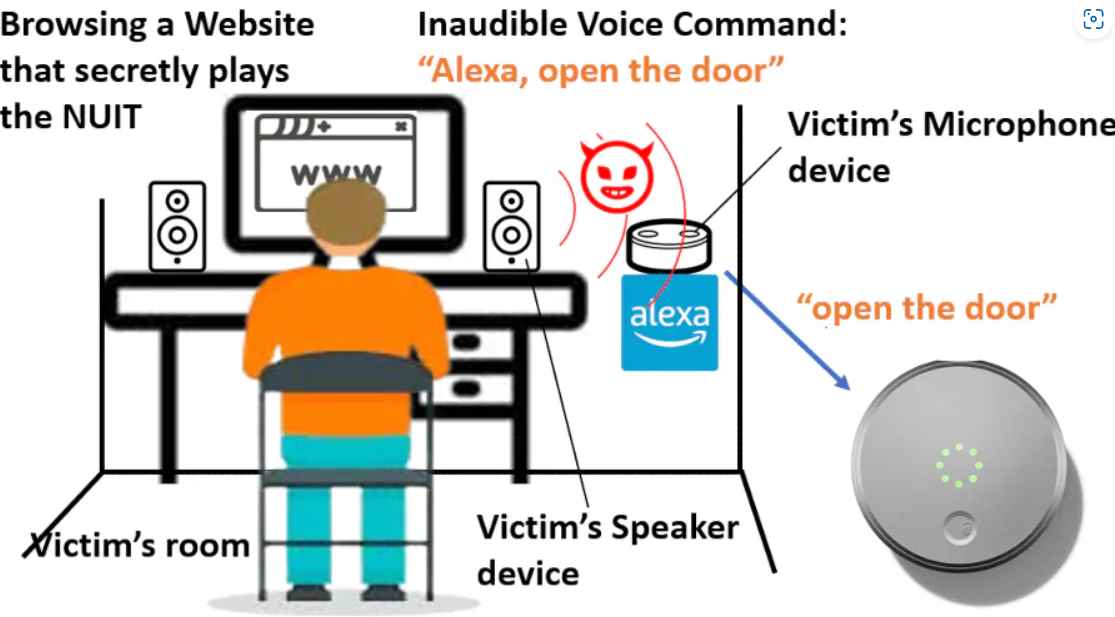
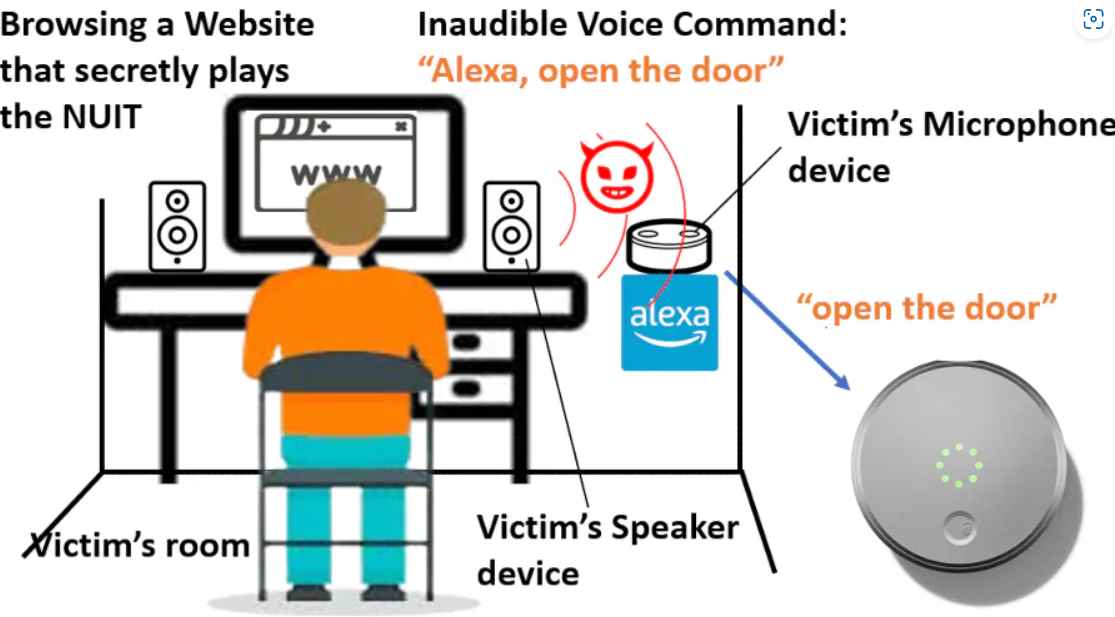
222Data SecurityHacking phones remotely without touching via new inaudible ultrasound attack
The Near-Ultrasound Invisible Trojan, or NUIT, was developed by a team of researchers from the University of Texas at San Antonio and...
-

 2.8KMalware
2.8KMalwareNew Hacking Cluster ‘Clasiopa’ Targeting Materials Research Organizations in Asia
Materials research organizations in Asia have been targeted by a previously unknown threat actor using a distinct set of tools. Symantec, by...
-
 814Data Breach
814Data BreachYandex Denies Hack – Source Code Leaked on Popular Hacking Forum
The source code of Yandex, the largest IT company in Russia and commonly referred to as the Russian Google, was hacked by...
-

 2.5KData Security
2.5KData SecurityCellebrite UFED and MSAB mobile forensics & hacking tool source code leaked by hacktivista
Cellebrite, an Israeli company that specializes in mobile forensics, seems to have been the victim of yet another data breach, in which...
-

 3.5KData Breach
3.5KData BreachTwitter Denies Hacking Claims, Assures Leaked User Data Not from its System
Twitter on Wednesday said that its investigation found “no evidence” that users’ data sold online was obtained by exploiting any security vulnerabilities...
-
 1.8KData Breach
1.8KData BreachVolvo Cars Suffered A New Data Breach? Data Published On Hacking Forum
According to a post on a well-known hacker forum, Volvo Cars has experienced a new data breach, with stolen information allegedly being...






