Search results for "Hijacking"
-

 2.0KMalware
2.0KMalwareResearcher finds DLL hijacking vulnerability in Conti, REvil, LockBit, Black Basta, BitLocker, and AvosLocker ransomware variants that could prevent file encryption
A researcher has detected a critical vulnerability in some of the most common malware and ransomware variants today and whose exploitation would...
-
 5.0KMalware
5.0KMalwareSocial Media Hijacking Malware Spreading Through Gaming Apps on Microsoft Store
A new malware capable of controlling social media accounts is being distributed through Microsoft’s official app store in the form of trojanized...
-

 3.4KMalware
3.4KMalwareOver a Dozen Malicious NPM Packages Caught Hijacking Discord Servers
At least 17 malware-laced packages have been discovered on the NPM package Registry, adding to a recent barrage of malicious software hosted...
-
 347Exploitation Tools
347Exploitation ToolsThreadBoat – Uses Thread Execution Hijacking To Inject Shellcode
Program uses Thread Hijacking to Inject Native Shellcode into a Standard Win32 Application. With Thread Hijacking, it allows the hijacker.exe program...
-
 367Malware
367MalwareMicrosoft Warns of a New Rare Fileless Malware Hijacking Windows Computers
Watch out Windows users! There’s a new strain of malware making rounds on the Internet that has already infected thousands of computers...
-

 361Geek
361GeekVulnerability in Zoom video conference app lets Mac’s camera hijacking
The vulnerability in the Zoom video conference app lets attackers hijack Mac’s camera by merely using malicious websites. The Zoom video conference...
-
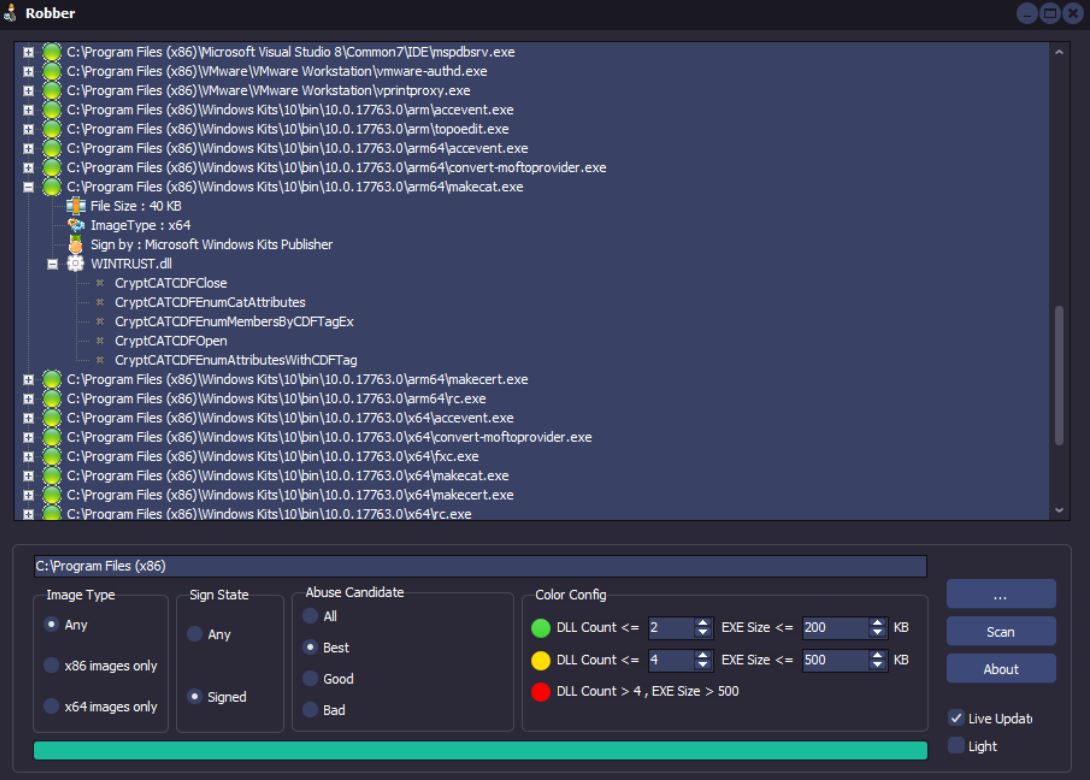
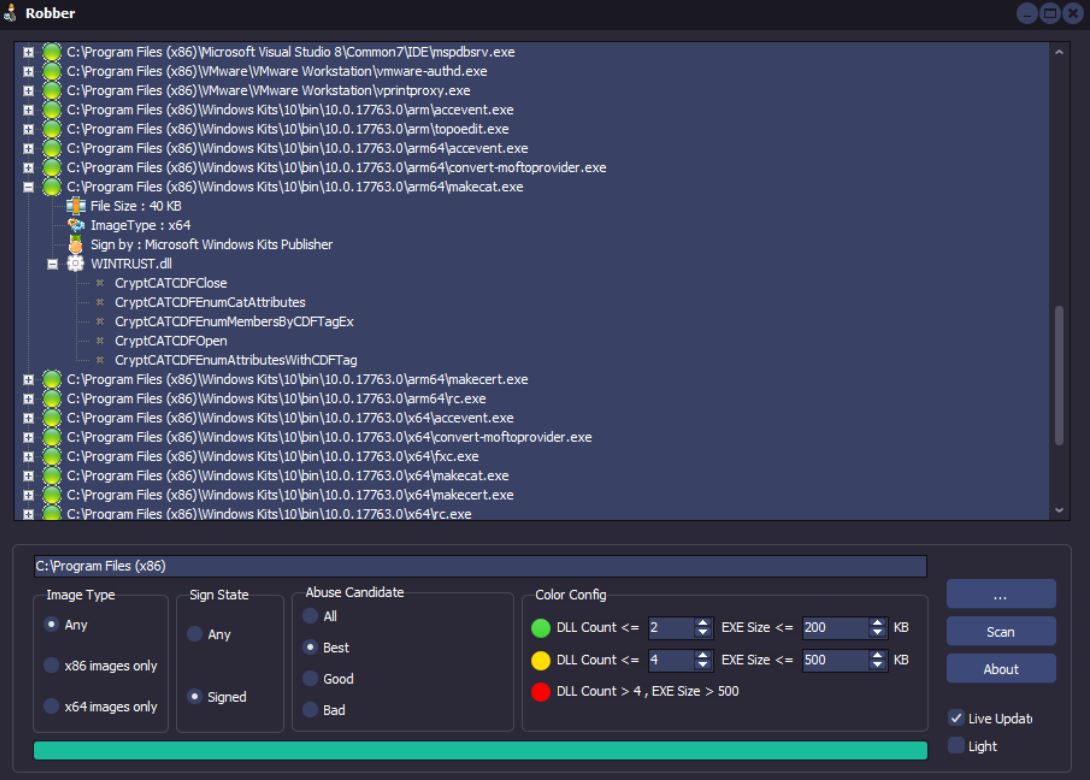 332Hack Tools
332Hack ToolsRobber – Open Source Tool for Finding Executables Prone to DLL Hijacking
Robber is a free open source tool developed using Delphi XE2 without any 3rd party dependencies. What is DLL hijacking ? Windows...
-

 303Cyber Crime
303Cyber CrimeHackers hacked: Account hijacking forum OGUsers pwned
The stolen OGUsers database is available on RaidForums for download. On 12th May, hackers managed to steal the database of a famous...
-

 450Incidents
450IncidentsHackers sent to jail for stealing over $2M USD in cryptocurrency with SIM hijacking attack
Hackers sent to jail for stealing over $2M USD in cryptocurrency with SIM hijacking attack. According to IICS’s web application security course,...
-

 224Malware
224MalwareHackers Launching DNS Hijacking Attack to Gain Access to Telecommunication & ISP Networks
Researchers discovered a new malicious campaign called “Sea Turtle,” attack public and private entities in various countries using DNS hijacking as a...
-
 393Social Media Hacking
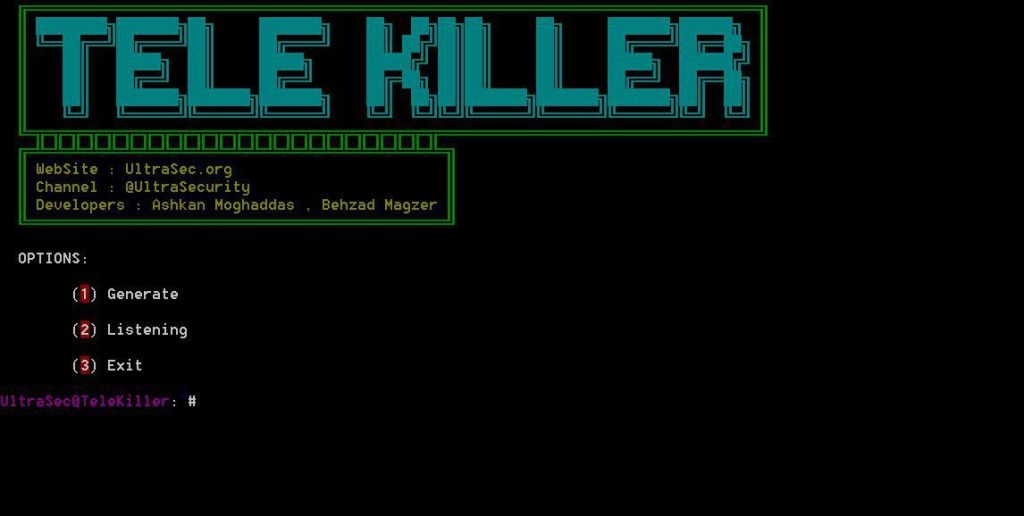
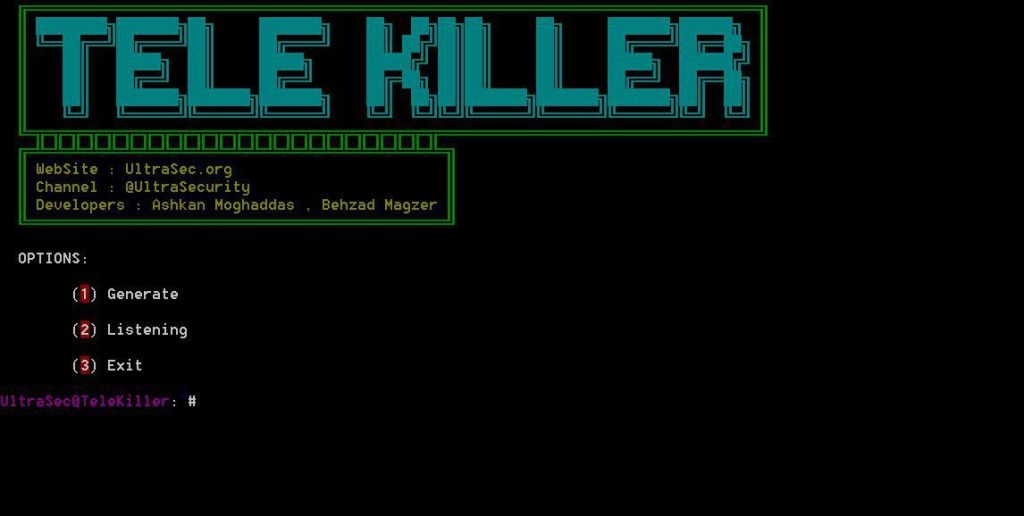
393Social Media HackingTeleKiller – A Tools Session Hijacking And Stealer Local Passcode Telegram Windows
A Tools Session Hijacking And Stealer Local passcode Telegram Windows Features : Session Hijacking Stealer Local Passcode Keylogger Shell Bypass 2 Step...
-

 346Data Security
346Data SecurityDNS hijacking campaign is stealing Netflix, Gmail and other services accounts
A DNS hijacking campaign, active for at least three months, has been attacking users of the most popular online services, such as...
-

 300Vulnerabilities
300VulnerabilitiesVulnerability in Windows Deployment Services allows server hijacking
A protocol implementation error appears to be the cause of this flaw Network security and ethical hacking specialists recently published a report...
-

 222Malware
222MalwareMetaMask – First Copy-and-Paste Hijacking Crypto Malware Found in Google Play
The clipper hijacking malware use to intercept the contents of the clipboard and replaces it with the content the attackers want to...
-

 215Articles
215ArticlesFirst Android Clipboard Hijacking Crypto Malware Found On Google Play Store
A security researcher has discovered yet another cryptocurrency-stealing malware on the official Google Play Store that was designed to secretly steal bitcoin...
-

 359Vulnerabilities
359VulnerabilitiesCombination of bugs in WordPress and WooCommerce allows website hijacking
A flaw in how WordPress handles privileges can be exploited to take control of a domain A flaw in the WordPress process to...
-

 226Hacked
226HackedWindows PCs Vulnerable To RID Hijacking; Grants Full System Access To Attackers
A security researcher named Sebastián Castro has uncovered a way of gaining admin rights and boot persistence on Windows PCs that is...
-

 191Vulnerabilities
191VulnerabilitiesVulnerability allows hijacking of software installed in macOS
It has been revealed a dangerous flaw in macOS that allows hackers to hijack applications installed through unusual routes A security report...
-
 248Vulnerability Analysis
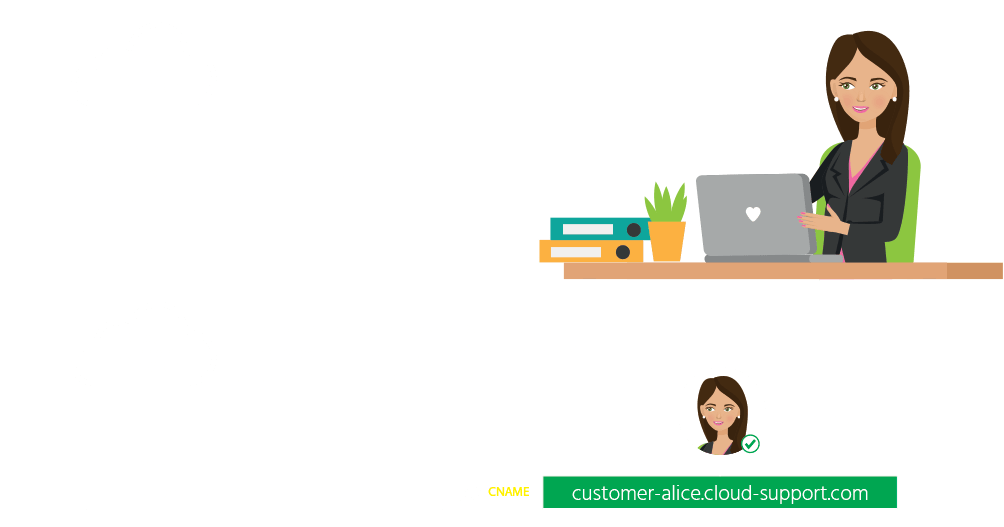
248Vulnerability AnalysisScan your exposure to domain and subdomain hijacking over 10’s of cloud providers
Domain Hijacking is a well-known security issue that can be carried in many different ways. In addition to social engineering or unauthorized...
-

 330Malware
330MalwareDNS Hijacking Method Used by Powerful Malware to Hack Android, Desktop & iOS Devices
Roaming Mantis Malware expands Geographically with many new capabilities. Initially, it targets only the Android users, now the malware authors improved their...
-

 232Incidents
232IncidentsRoaming Mantis uses DNS hijacking to infect Android smartphones
In March 2018, Japanese media reported the hijacking of DNS settings on routers located in Japan, redirecting users to malicious IP addresses....






