Search results for "Hijacking"
-

 334Malware
334MalwareNew “Roaming Mantis” Malware uses DNS Hijacking Attack to Hack Android Smartphones
Newly discovered Malware called “Roaming Mantis” infiltrate the Android smartphones using a technique known as DNS hijacking and steal the sensitive information...
-

 357Data Security
357Data SecurityTeen Exposes T-Mobile Flaw Allowing Mass Hijacking of User Accounts
Users of popular cell phone carrier T-Mobile could have been in great trouble because a British hacker researcher Kane Gamble identified a...
-

 354Data Security
354Data SecurityTrickBot Variant Steals Bitcoin by Hijacking Cryptocurrency Transactions
Another day, another malware – This time TrickBot’s variant is stealing Bitcoin by hacking cryptocurrency transactions. TrickBot malware, which emerged in late...
-

 303Malware
303MalwareEMOTET Malware Hijacking the Windows API & Evade the Sandbox Analysis
A wide Spread EMOTET malware emerging again with new stealthy capabilities to hijack the Windows API and evade the sandbox detection which also gives...
-

 231Incidents
231IncidentsAdware Installs InfoStealer Trojan that it loads via Chrome DLL Hijacking
A password stealing Trojan called AdService is being quietly distributed by adware bundles that typically install other programs such as Russian adware,...
-
 287Vulnerabilities
287VulnerabilitiesDiscovering a Session Hijacking Vulnerability in GitLab
GitLab is a widely used SaaS provider that focuses on developer related issues, including Git repository management, issue tracking and code review....
-

 387News
387NewsVault 7: CIA’ Dumbo Project Hijacking Webcams and Microphones
The Vault7 saga is far from over, and every passing week we are being introduced to a new set of tricks and...
-

 253Cross Site Scripting
253Cross Site ScriptingCookieCatcher – Tool For Hijacking Sessions Using XSS
CookieCatcher is an open source application that allows you perform session hijacking (cookie stealing) through XSS (cross site scripting). Features Prebuilt payloads...
-

 87Malware
87MalwareHacker “BestBuy” Admits to Hijacking Deutsche Telekom Routers With Mirai Malware
A 29-year-old man pleaded guilty in court on Friday to hijacking over 900,000 routers from the network of Deutsche Telekom, according to...
-
 207Vulnerabilities
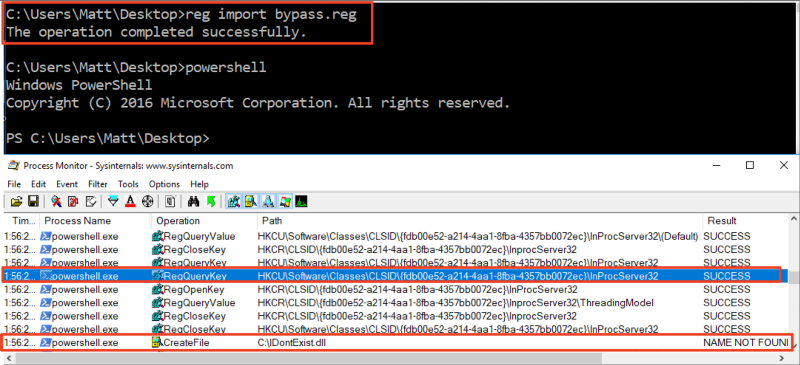
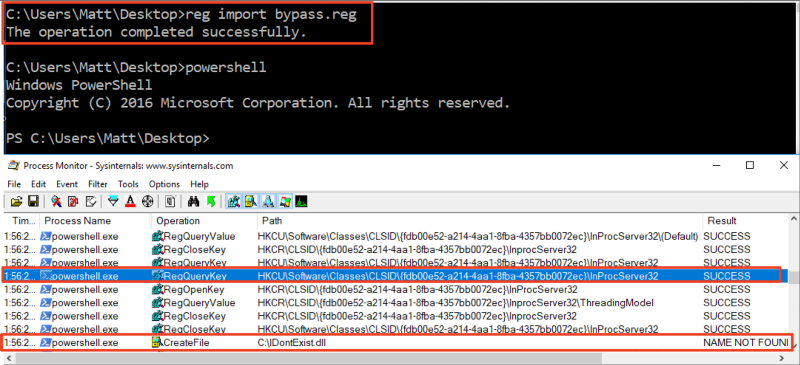
207VulnerabilitiesBypassing AMSI via COM Server Hijacking
Microsoft’s Antimalware Scan Interface (AMSI) was introduced in Windows 10 as a standard interface that provides the ability for AV engines to...
-
 106Vulnerabilities
106VulnerabilitiesVULNERABILITIES EXPOSE ORACLE OAM 10G TO REMOTE SESSION HIJACKING
Oracle’s next quarterly Critical Patch Update is slated for July 18, but two vulnerabilities in an older version of the company’s Oracle...
-

 175Vulnerabilities
175VulnerabilitiesSESSION HIJACKING, COOKIE-STEALING WORDPRESS MALWARE SPOTTED
Researchers have identified a strain of cookie stealing malware injected into a legitimate JavaScript file, that masquerades as a WordPress core domain....
-
 139Vulnerabilities
139VulnerabilitiesCisco patches switch hijacking hole – the one exploited by the CIA
Telnet security flaw fix finally lands – or just use SSH, yeah? Cisco has patched a critical security flaw in its switches...
-
 80Vulnerabilities
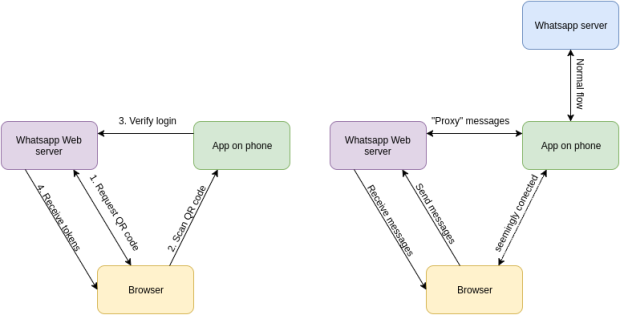
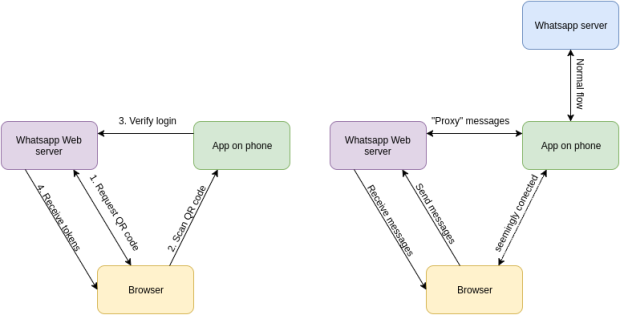
80VulnerabilitiesHIJACKING WHATSAPP ACCOUNTS USING WHATSAPP WEB
Whatsapp accounts are based on phone numbers. This means your phone number is your username and it’s also used for authentication. While...
-
 251Cyber Attack
251Cyber AttackA person Hijacking Unprotected MongoDB Databases for Ransom
Almost years again, we warned users approximately publicly on hand MongoDB instances – almost six hundred Terabytes (TB) – over the internet...
-
 170Data Security
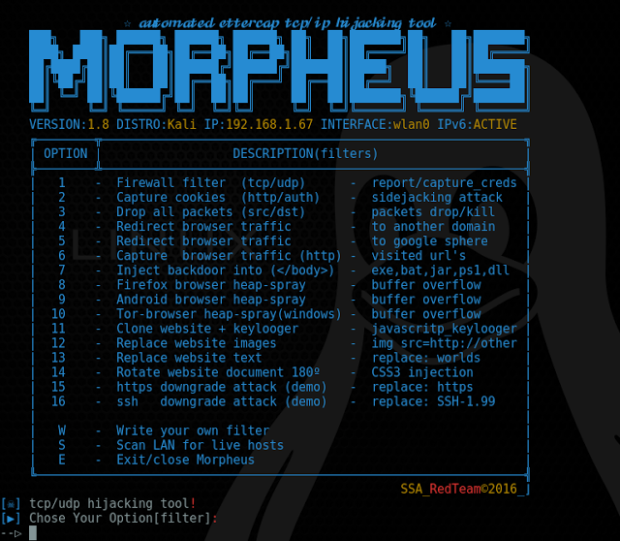
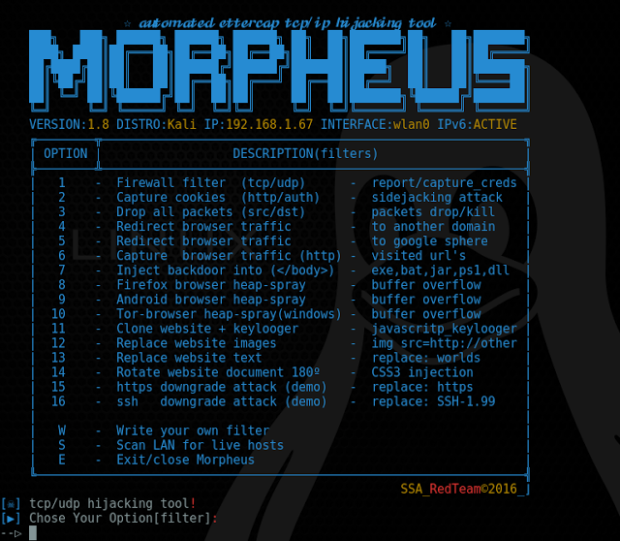
170Data SecurityAutomated Ettercap TCP/IP Hijacking Tool – Morpheus
Morpheus is a framework tool which automates TCP/UDP packet manipulation tasks by using etter filters to manipulate target requests/responses under MitM attacks...
-

 233How To
233How ToMorpheus – Automated Ettercap TCP/IP Hijacking Tool
Morpheus is a framework tool which automates TCP/UDP packet manipulation tasks by using etter filters to manipulate target requests/responses under MitM attacks...
-

 235Data Security
235Data SecurityJSON hijacking for the modern web
Benjamin Dumke-von der Ehe found an interesting way to steal data cross domain. Using JS proxies he was able to create a...
-
 205Vulnerabilities
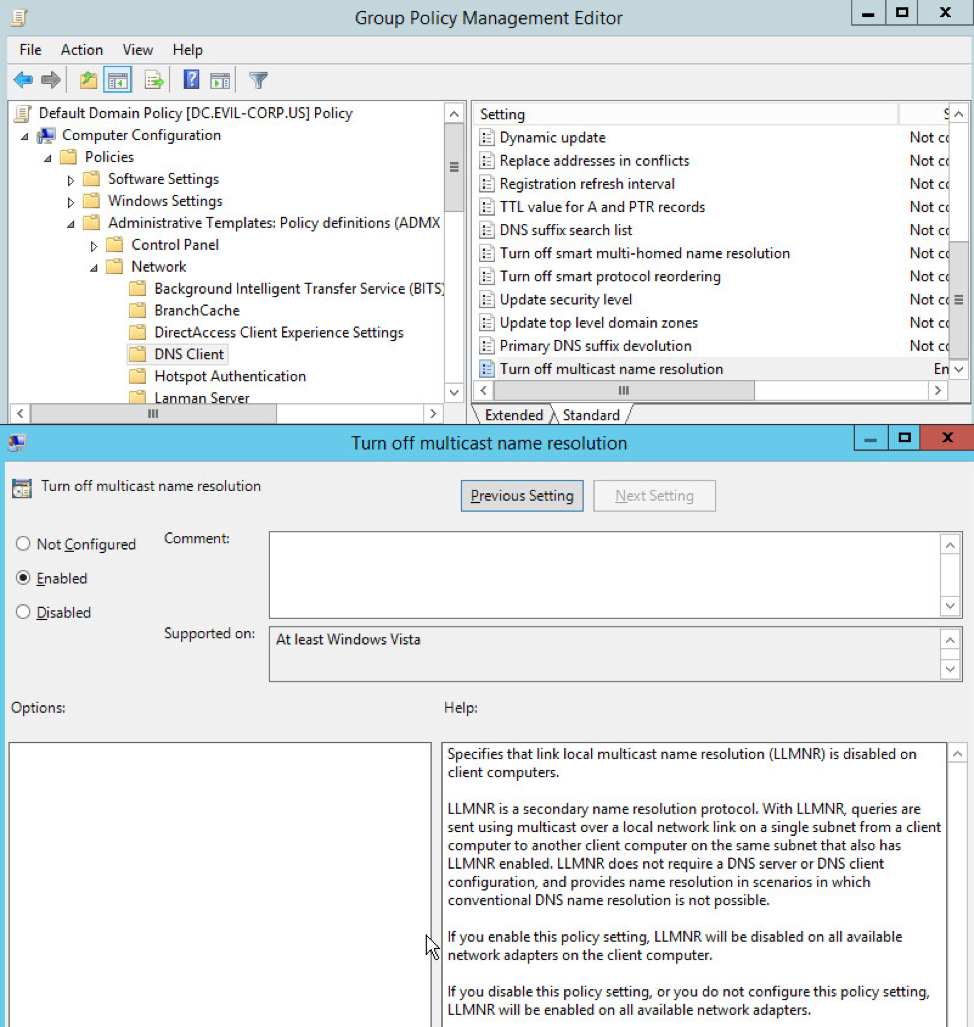
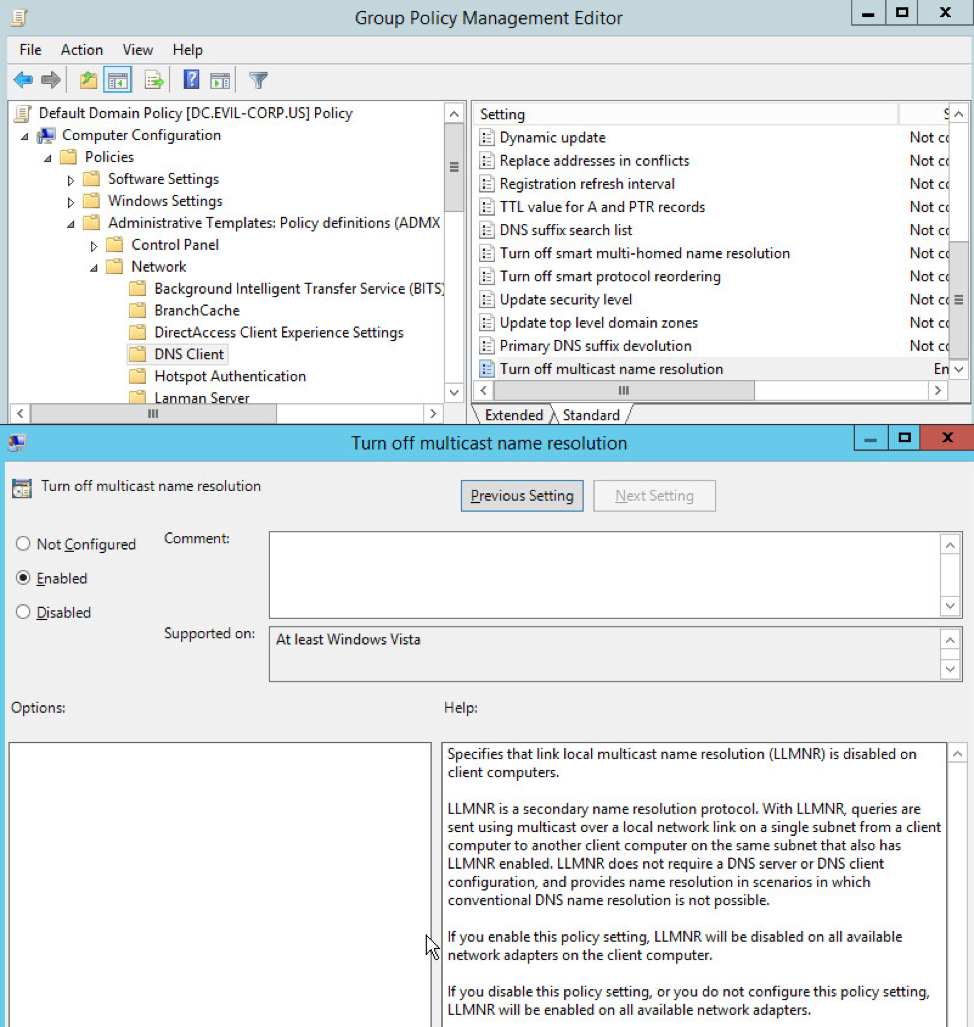
205VulnerabilitiesBLOCKING LOCAL NETWORK HIJACKING ATTACKS
Adversaries who have compromised one system in a network frequently hijack the network traffic of other systems on the same subnet to...
-

 178Vulnerabilities
178VulnerabilitiesOAUTH 2.0 HACK EXPOSES 1 BILLION MOBILE APPS TO ACCOUNT HIJACKING
Third-party applications that allow single sign-on via Facebook and Google and support the OAuth 2.0 protocol, are exposed to account hijacking. Three...
-
 263Data Security
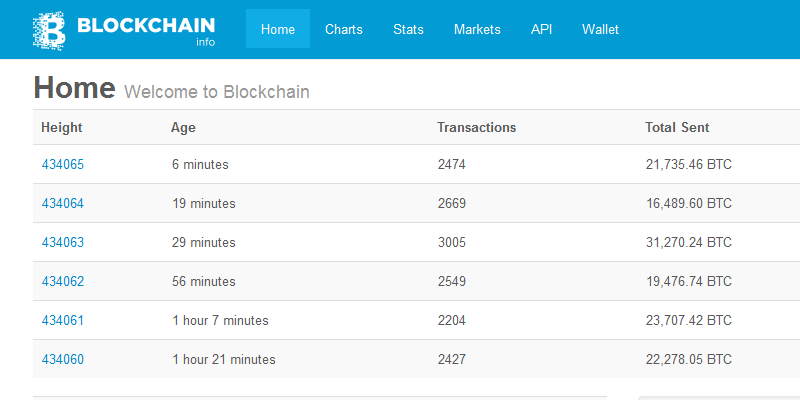
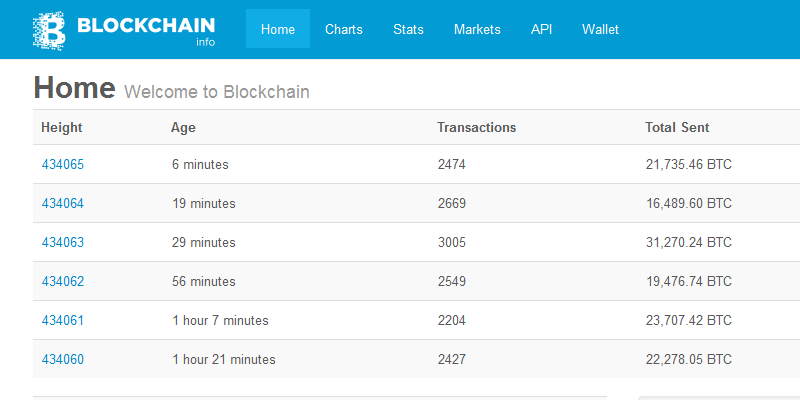
263Data SecurityBitcoin Wallet Blockchain.info Recovers from DNS Hijacking Attack
At the time of writing, everything is back to normal. Blockchain.info, the largest web-based Bitcoin wallet, suffered a DNS hijacking attack today...






