Search results for "Hijacking"
-
 79Data Security
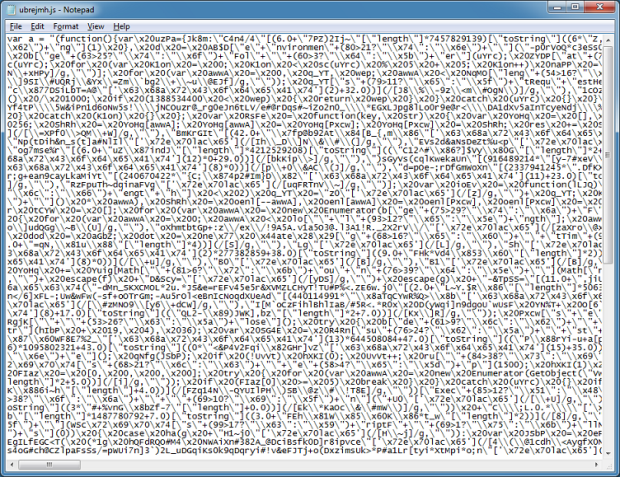
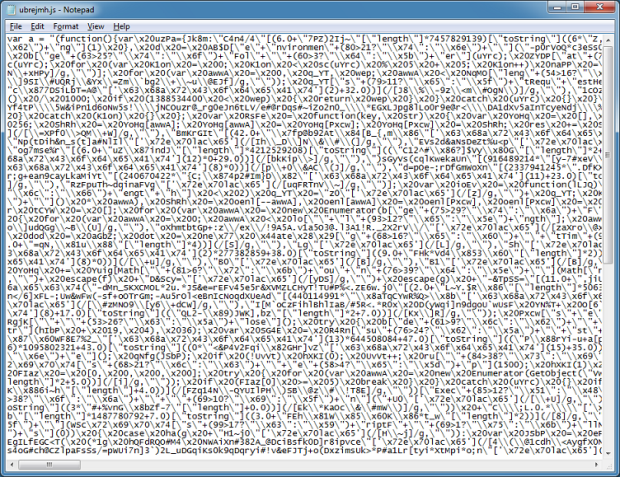
79Data SecurityJavascript Leads to Browser Hijacking
I came across this nasty-looking script that hijacks your browser. It appears to have been around in some shape or form since...
-

 170Vulnerabilities
170VulnerabilitiesLinux bug leaves 1.4 billion Android users vulnerable to hijacking attacks
Off-path attack means malicious hackers can be located anywhere on the Internet. An estimated 80 percent of Android phones contain a recently discovered...
-
 156Data Security
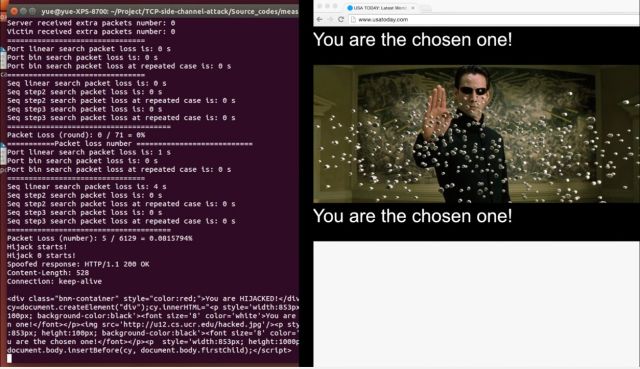
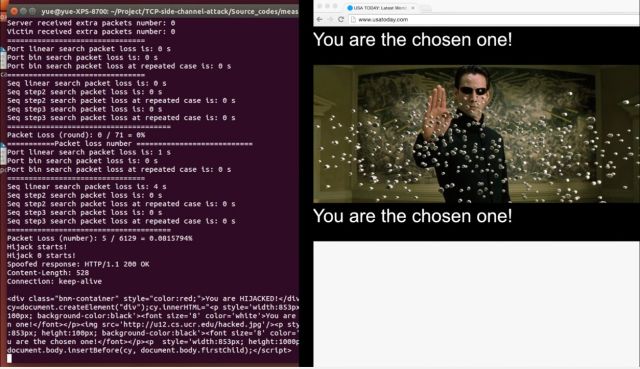
156Data SecurityLinux bug leaves USA Today, other top sites vulnerable to serious hijacking attacks
“Off-path” attack means hackers can be anywhere with no man-in-the-middle needed. Computer scientists have discovered a serious Internet vulnerability that allows attackers...
-

 179Malware
179MalwareHacker Compromises Fosshub to Distribute MBR-Hijacking Malware
Audacity and Classic Shell software downloads affected. A hacking crew that goes by the name of PeggleCrew has compromised Fosshub and embedded malware...
-
 194Vulnerabilities
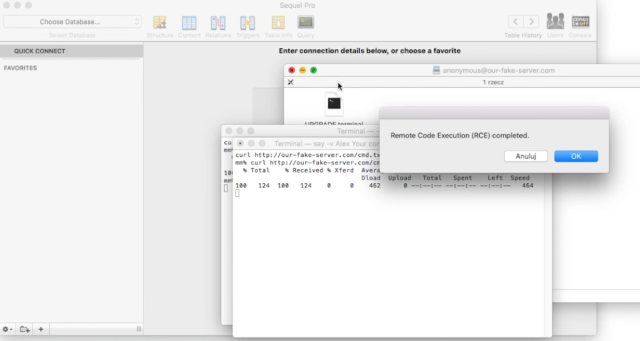
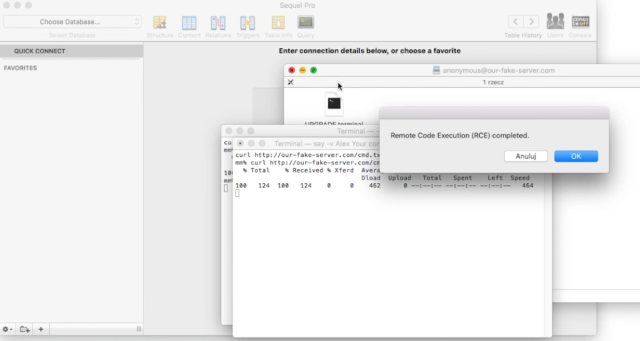
194VulnerabilitiesMagento – Re-Installation & Account Hijacking Vulnerabilities
Before discovering my latest Magento RCE, I’ve found two different vulnerabilities, both resulting in the complete compromise of customer data and/or the...
-
 255Data Security
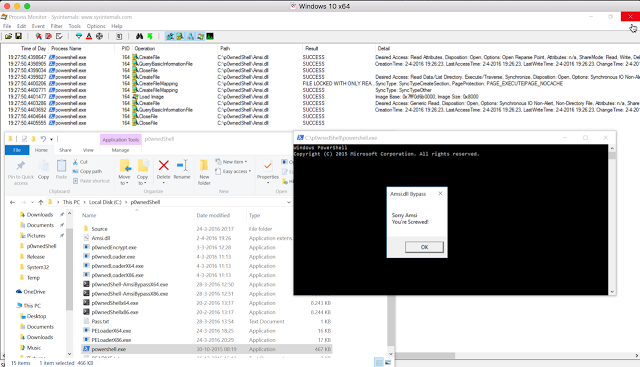
255Data SecurityBypassing Amsi using PowerShell 5 DLL Hijacking
While doing some research on the inner workings of Microsofts new Antimalware Scan Interface technology within Windows 10, i found a DLL...
-
 188Data Security
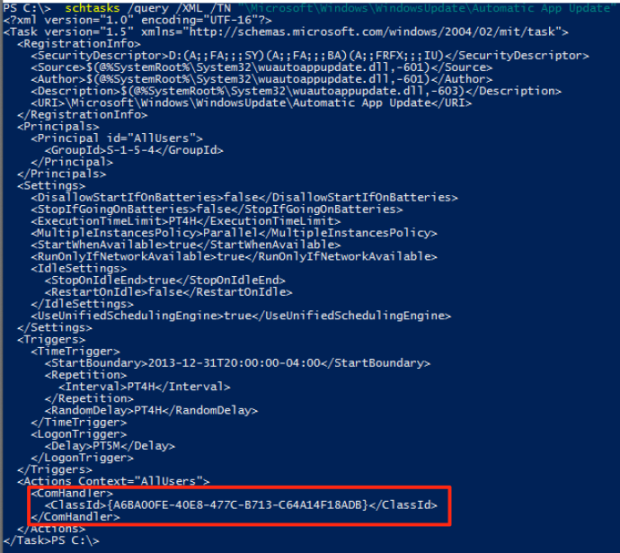
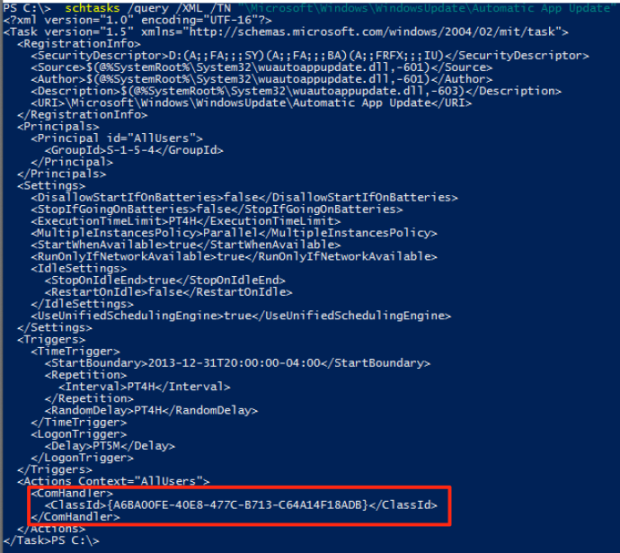
188Data SecurityUSERLAND PERSISTENCE WITH SCHEDULED TASKS AND COM HANDLER HIJACKING
A while back I was exploring userland COM and stumbled across some 2011 research by Jon Larimer explaining the dangers of per-user...
-

 112Incidents
112IncidentsChrome Extension Caught Hijacking Users’ Browsers
Google removes Chrome extension that hijacked Web browsers. Google has intervened and banned the Better History Chrome extension from the Chrome Web Store...
-

 95Incidents
95IncidentsiCloud Account Hijacking Scam Is as Bad as Ransomware
Crook hijacks iCloud account, locks victim’s Mac.Crooks have discovered a method of turning Apple’s security features against the company’s users, hijacking Apple...
-
 175Vulnerabilities
175Vulnerabilities“Huge” number of Mac apps vulnerable to hijacking, and a fix is elusive
Apps that use 3rd-party updater over insecure HTTP channels subject to MiTM attacks. Camtasia, uTorrent, and a large number of other Mac...
-

 205Vulnerabilities
205VulnerabilitiesDLL Hijacking Issue Plagues Products like Firefox, Chrome, iTunes, OpenOffice
Oracle patches Java installer against DLL hijacking issue. Oracle has released new Java installers to fix a well-known security issue (CVE-2016-0603) that also...
-

 189Vulnerabilities
189VulnerabilitiesIntel Fixes Security Bug to Prevent Attackers From Hijacking the Driver Update Process
Intel-powered laptops are safe again. So are desktops. Intel has released version 2.4 of the Intel Driver Update Utility, fixing a critical...
-
 213Data Security
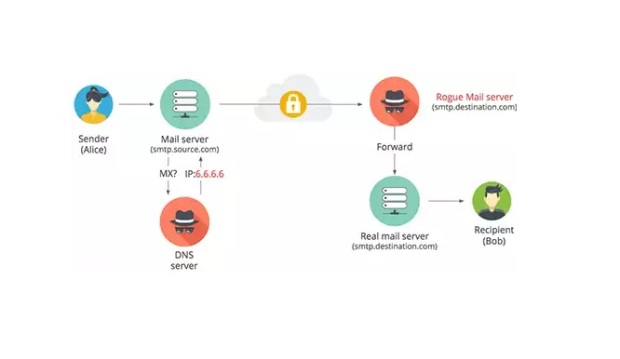
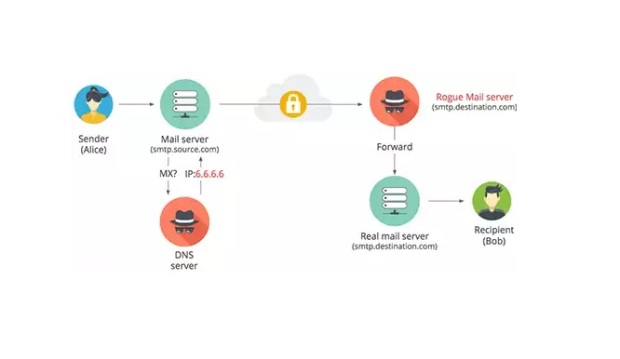
213Data SecurityHow email in transit can be intercepted using DNS hijacking
This article looks at how an attacker can intercept and read emails sent from one email provider to another by performing a...
-

 96Data Security
96Data SecurityRemote Exploitation of Microsoft Office DLL Hijacking (MS15-132) via Browsers
A number of weeks back, security researcher Parvez Anwar posted a number of DLL hijacking vulnerabilities within Microsoft Office on Twitter [1]....
-

 207Data Security
207Data SecurityDLL Hijacking Tutorial
Dll hijacking is a vulnerability that is caused by a misbehavior practiced by all versions of Windows.Many people believe that is a...
-

 98Vulnerabilities
98VulnerabilitiesSteam tightens trading security amid 77,000 monthly account hijackings
Traded items will be “held” for days unless you have two-factor security. Account theft is a common and longstanding problem for all...
-
 108Incidents
108IncidentsHTTPSohopeless: 26,000 Telstra Cisco boxen open to device hijacking
Embedded device mayhem as rivals share keys. More than 26,000 Cisco devices sold by Australia’s dominant telco Telstra are open to hijacking...
-

 100Privacy
100PrivacyHilton HHonors accounts put at risk of hijacking through simple web flaw
Security researchers discovered a vulnerability on the Hilton HHonors website, making it straightforward to hijack any other user's account.
-
 291Data Security
291Data SecurityWordPress Google Analytics Plugin by Yoast Vulnerable to critical site-hijacking
Yet another vulnerability has been found in the Yoast WordPress plugin that can be exploited by attackers allowing them to control the...
-
 322Cyber Crime
322Cyber CrimeRansomware: Cyber-hijacking Malware now has a new deadly face
Everything formidable is often associated with its negative half and the same can be said of the internet. The origins of functional...
-

 102Privacy
102PrivacyUK Broadband ISPs hijacking browsers to push porn blocks
A host of UK broadband providers are hijacking people's browsers mid-session to force them into making decisions on adult content filters.






