Search results for "Malware"
-

 376Cyber Crime
376Cyber CrimeHacking Team’s Licence Canceled, No More Malware Selling Outside Europe
HACKING TEAM YET AGAIN IN HOT WATER, LOSES LICENSE TO SELL MALWARE OUTSIDE EUROPE Just a year after it was hacked, the...
-
 114Data Security
114Data SecurityCISCO ‘HIGH SEVERITY’ FLAW LETS MALWARE BYPASS FIREPOWER FIREWAL
Technology vendor Cisco is pushing out security updates to customers to address a critical vulnerability found in its recently introduced line of FirePower...
-
 179Malware
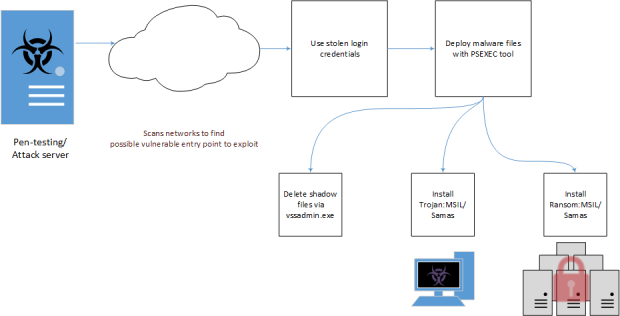
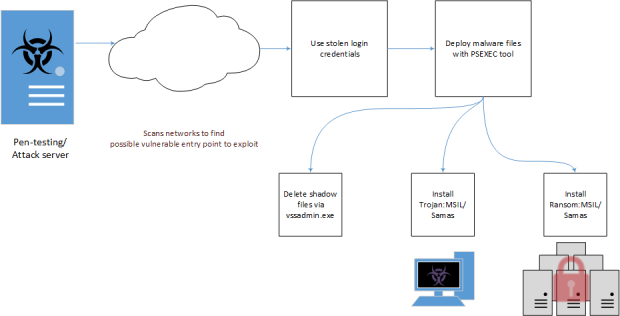
179MalwareWhy malware like the Samsam ransomware are so dangerous for hospitals?
The FBI issued a confidential urgent “Flash” message to the businesses and organizations about the Samsam Ransomware, why it is so dangerous?...
-

 326Data Security
326Data SecurityAlert Gamers: RAT Activity Identified in Steam Stealer Malware Scam
Alert: The previously discussed Steam Stealer malware is way bigger than we thought — The malwarE is also embedded with a remote...
-

 196Data Security
196Data SecurityTop Firefox extensions can hide silent malware using easy pre-fab tool
The fix? No patch, just destroy all extensions. Black Hat Asia The most popular Firefox extensions with millions of active users are open...
-

 94Malware
94MalwareLatest Steam Malware Shows Signs of RAT Activity
We have been alerted to a recent Steam scam, thanks to one gamer who is quick to inform her friends in the...
-

 165Malware
165MalwareThe evolution of Brazilian Malware
Brazilian malware continues to evolve day by day, making it increasingly sophisticated. If you want to know how the various malicious programs...
-

 203Cyber Crime
203Cyber CrimeScammers Distribute Malware to Drivers in Speeding Ticket Scam
Scammers Distribute Malware to Drivers in Pennsylvania using Accurate Speeding Data Scammers and their antics are simply unbelievable. This time, scammers have...
-
 74Malware
74MalwarePOS MALWARE TOOL ‘TREASUREHUNT’ TARGETS SMALL US-BASED BANKS, RETAILERS
As more US companies snuff out point of sale malware by deploying chip-and-PIN bankcard technology, attackers are rushing to exploit existing magnetic...
-
 77Incidents
77IncidentsTop Australian Classifieds Site Serves Malware In Malvertising Attack
Gumtree is a free classified advertising site and subsidiary of eBay particular popular in the UK, Australia, and South Africa. Gumtree is the number one local...
-

 381Malware
381MalwareESET discovers new USB‑based data stealing malware
ESET has discovered a new USB-based data stealer capable of stealthy attacks against air-gapped systems – it is also well-protected against detection...
-
 107Data Security
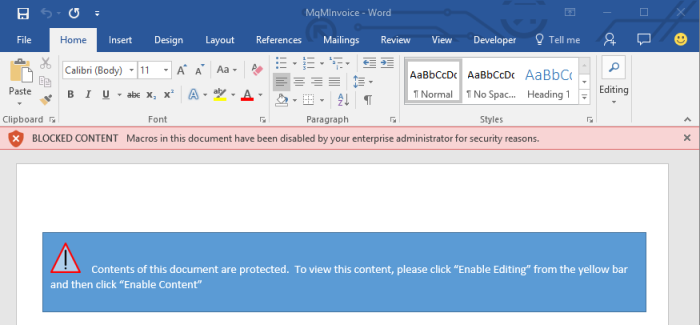
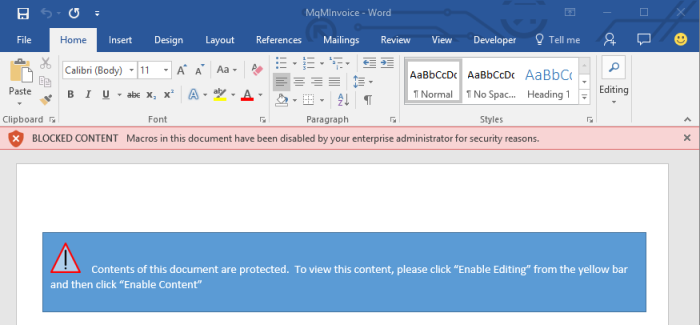
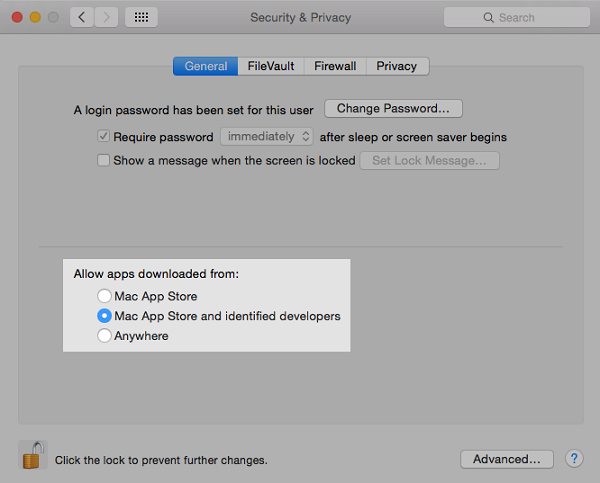
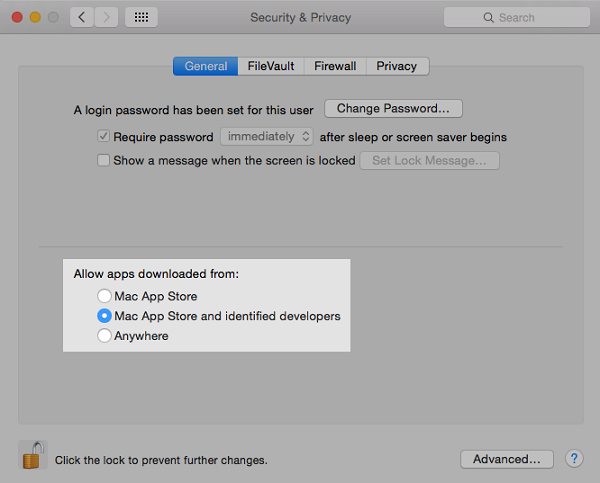
107Data SecurityMicrosoft Adds New Feature in Office 2016 That Can Block Macro Malware
How-to guide also included, showing sysadmins how to protect their enterprises from malicious macro malware. Microsoft is finally addressing the elephant in the...
-

 308Cyber Crime
308Cyber CrimeCyber warfare shows scary signs of where malware is headed
While you might think that what a Russian APT group does to attack Ukrainian infrastructure has little to do with the life...
-

 258Data Security
258Data SecurityWatch Out Gamers: Steam Stealer malware is up and running
Steam Stealer Malware is becoming a sensation for cyber criminals and it puts 125 million Steam users at risk According to the...
-

 114Incidents
114IncidentsMalware Botnet Can Be Abused to Launch DDoS Attacks
DDoS attacks can have an amplification factor of 26.5. An independent security researcher that goes by the name of MalwareTech has discovered a...
-

 171Geek
171GeekiOS Malware AceDeceiver: Hide and Seek between Apple’s DRM Versus MITM
Do you consider non-jailbroken iPhones to be safe? Think again! AceDeceiver is playing havoc with Apple’s most celebrated devices. This malware has...
-
 167Incidents
167IncidentsTo bypass code-signing checks, malware gang steals lots of certificates
Legitimate code-signing certificates provide secret cover for attack groups. There are lots of ways to ensure the success of an advanced hacking operation....
-
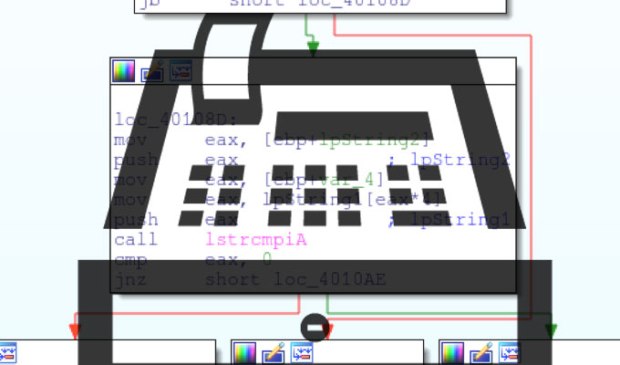
 68Malware
68MalwarePowerSniff Malware Used in Macro-based Attacks
Introduction The concept of file-less malware is not a new one. Families like Poweliks, which abuse Microsoft’s PowerShell, have emerged in recent...
-

 81Incidents
81IncidentsThese Are the Best System Rescue Tools After a Malware Attack
Researchers analyze five AV-made system repair tools.System rescue tools provided by antivirus makers are often used to clean infected systems after the...
-

 114Cyber Crime
114Cyber CrimeNewly Found Malware can steal bank details on Android phones
ESET security researchers have discovered an Android malware targeting banking customers in Australia — The malware also bypasses the two-factor authentication system Four...
-

 177Malware
177MalwareTriada Trojan the most sophisticated mobile malware seen to date
Kaspersky Lab recently spotted a new Android malware dubbed Triads Trojan, which they say is the most advanced mobile malware seen to...






