Search results for "Malware"
-

 192Incidents
192IncidentsHow hackers used this Trojan malware to spy on a territorial dispute
F-Secure researchers say parties involved in the South China Sea arbitration case were infected with the data-stealing NanHaiShu Trojan. Hackers have used...
-

 420Geek
420GeekBeware of Fake Android Prisma Apps Running Phishing, Malware Scam
Beware of fake Prisma photo editing app on Android store targeting users with phishing and malware scam! Prisma app for Android users was launched...
-

 179Malware
179MalwareHacker Compromises Fosshub to Distribute MBR-Hijacking Malware
Audacity and Classic Shell software downloads affected. A hacking crew that goes by the name of PeggleCrew has compromised Fosshub and embedded malware...
-
 79Incidents
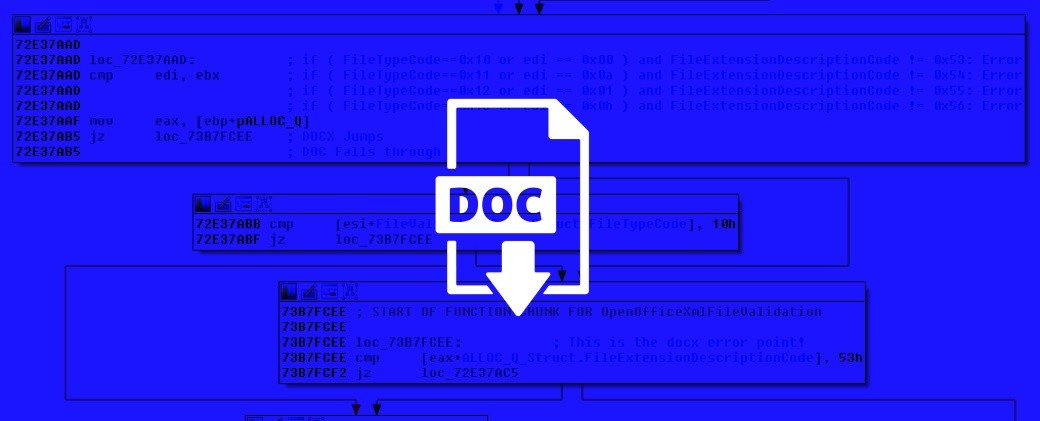
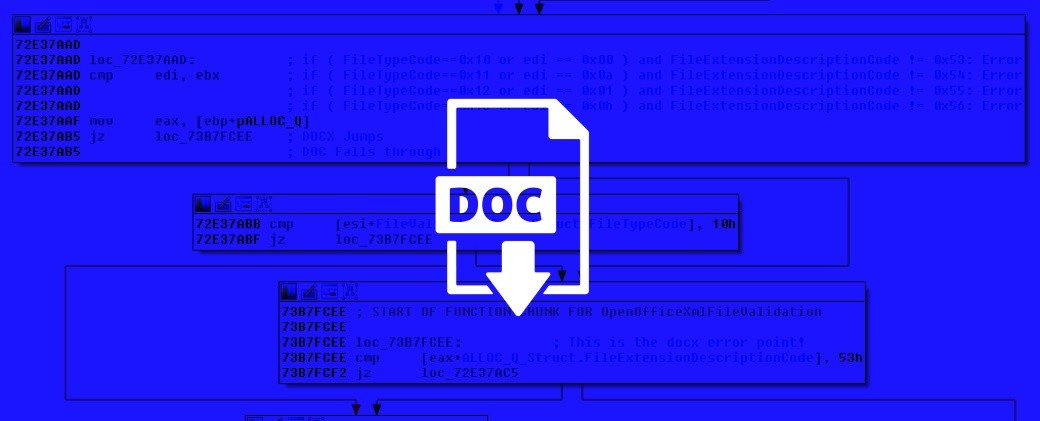
79IncidentsRenaming Office Files Is Enough to Disguise Macro Malware
Macros have been used since the mid 1990s to spread malware and infect systems. Increased user awareness of the need to disable...
-

 175Malware
175MalwareMalware Used in DNC Hack Has Roots in Chinese Open-Source Tool
X-Tunnel is roughly based on XTunnel PortMap. One of the malware variants used to infiltrate and hack the Democratic National Committee (DNC)...
-
 325Cyber Crime
325Cyber CrimeScammers Using Genuine PayPal Emails to Spread Banking Malware
Another day another PayPal scam — This time, it’s highly sophisticated and comes from a genuine PayPal email address! PayPal like other financial institutions...
-
 195Malware
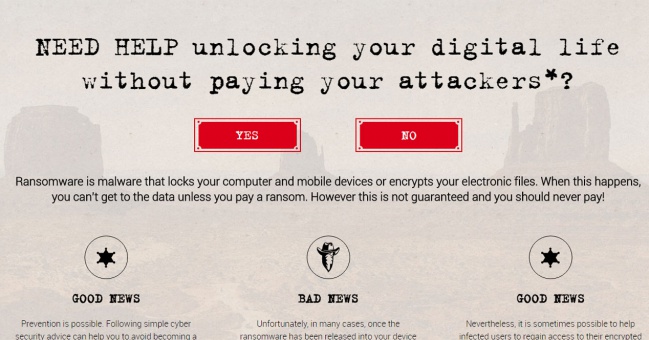
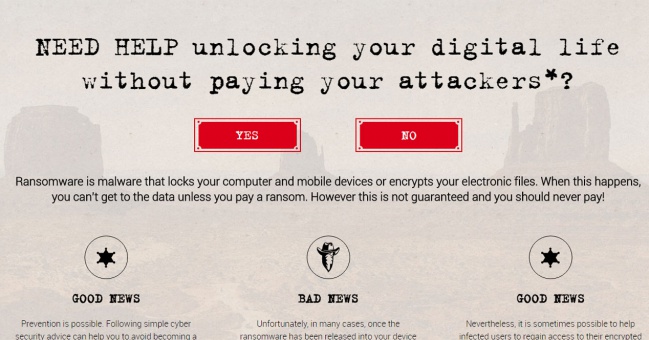
195Malware‘No More Ransom’ helps you recover data after a malware attack
A new website set up by Europol, Intel and Kaspersky to help resist the threat of ransomware could allow you to recover...
-
 149Data Security
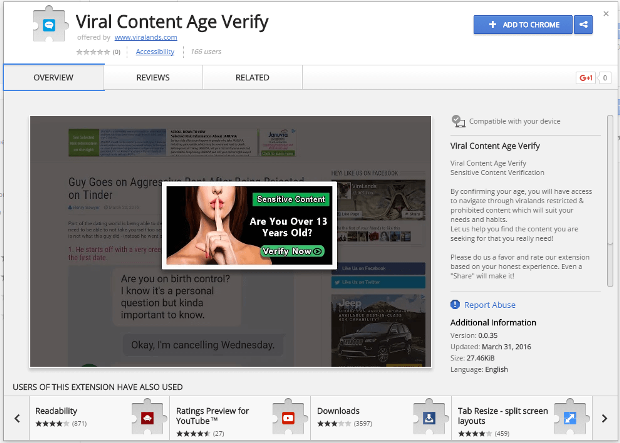
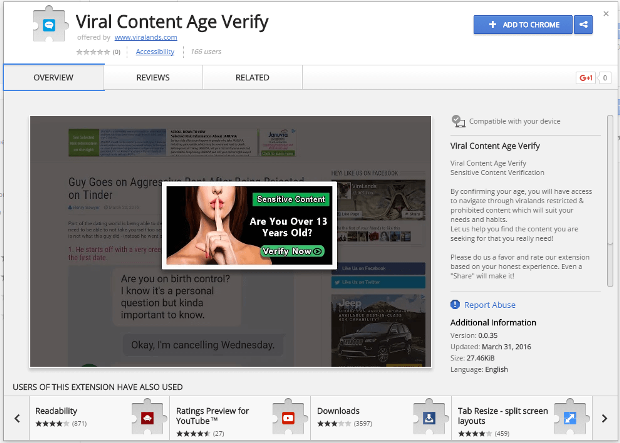
149Data SecurityMalware in the browser: how you might get hacked by a Chrome extension
Increasingly, browsers are taking on a central role in our daily lives. With web apps for everything, we have placed our most...
-
 184Malware
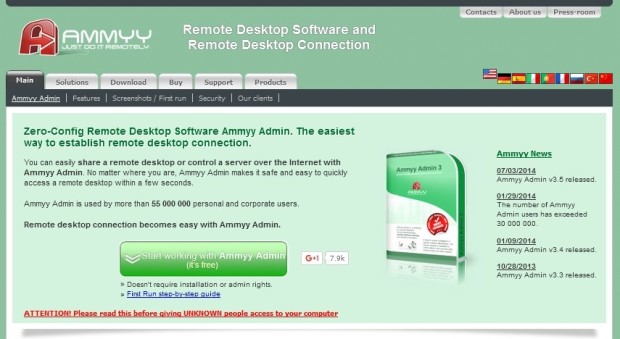
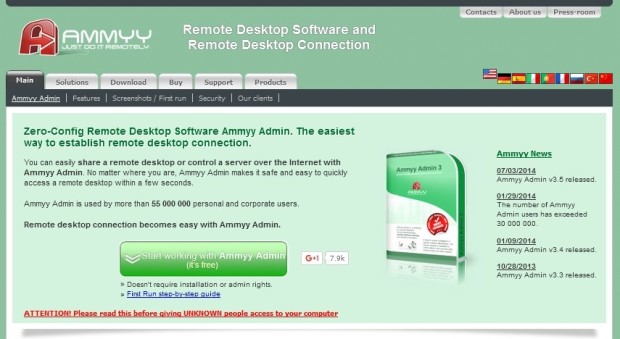
184MalwareWebsite of Remote Admin App Compromised Over and Over Again to Spread Malware
It may be a good idea to stay away from this software. The website of the Ammyy Admin remote desktop management utility has...
-

 163Malware
163MalwareSecurity firm clarifies power-station ‘SCADA’ malware claim
It’s not the next Stuxnet, says SentinelOne, it’s just very naughty code. Malware hyped as aimed at the hear of power plants...
-
 202Malware
202MalwareEleanor Mac malware connects your webcam to the dark web
The malware dubbed Backdoor.MAC.Eleanor is embedded surreptitiously in the fake app EasyDoc Coverter.app and allows to control your webcam from the dark...
-

 293News
293NewsChina Hacked Federal Deposit Insurance Corporation Via Backdoor Malware
The US Federal Deposit Insurance Corporation (FDIC) was hacked between 2010 to 2013 and the usual suspect is China! The House Committee on...
-
 160Incidents
160IncidentsRussians and Malware Involved in $2 Million ATM Heist in Taiwan
ATM transactions suspended in Taiwan for two days. Taiwan’s top eight banks have suspended operations on 900 ATMs after crooks stole NT$70 million...
-
 302Hacked
302HackedFBI Created Child Porno Website Playpen, Defends Its “Good” Malware In Court
Short Bytes: In order to catch child pornography watchers, FBI created a website Playpen and hosted it on the dark web. Later...
-
 78Vulnerabilities
78VulnerabilitiesNation-backed malware that infected energy firm is 1 of 2016’s sneakiest
Tool only drops malware after painstakingly dismantling AV and other defenses. A campaign that targeted a European energy company wielded malware that’s so...
-

 184Data Security
184Data SecurityPosing as ransomware, Windows malware just deletes victim’s files
Tagged as “Ranscam”, Powershell and script-based malware is a botched smash-and-grab. There has been a lot of ingenuity poured into creating crypto-ransomware, the...
-
 148Data Security
148Data SecurityMalware’s Constant Evolution Requires Advanced Protections
Malware developers are fast learners. They adapt to new security measures in record time and find new ways to evade detection or...
-

 197Hacked
197HackedPokemon Go Is A “Malware” And “Hackers’ Dream”, Security Experts Say
Short Bytes: Nintendo’s insanely popular augmented reality mobile game Pokemon Go is a massive security risk. Surprisingly, this app has complete access...
-
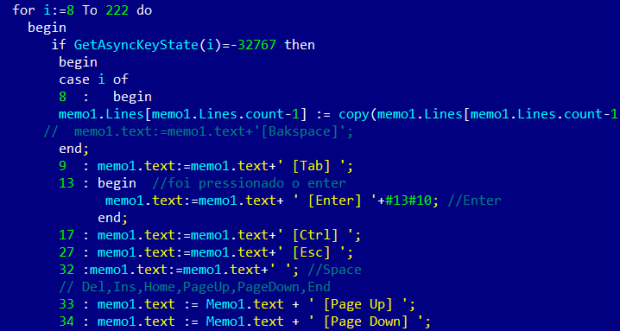
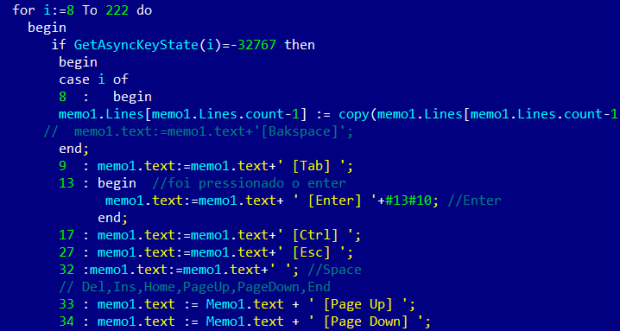
 151Data Security
151Data SecurityCode of destruction – malware analysis
We should always think twice before running an unknown program downloaded from the Internet. Of course not every application is dangerous, but...
-

 394Data Security
394Data SecurityWatch Out for Keydnap Malware Stealing Mac Login Credentials
The latest malware targets Mac users to steal their user credentials — Watch out and don’t fall for it! A new Mac...
-

 196Data Security
196Data SecurityNew OSX/Keydnap malware is hungry for credentials
ESET analyzes multiple samples targeting OS X every day. Those samples are usually potentially unwanted applications that inject advertisements into browser displays while...






