Search results for "Malware"
-
 438How To
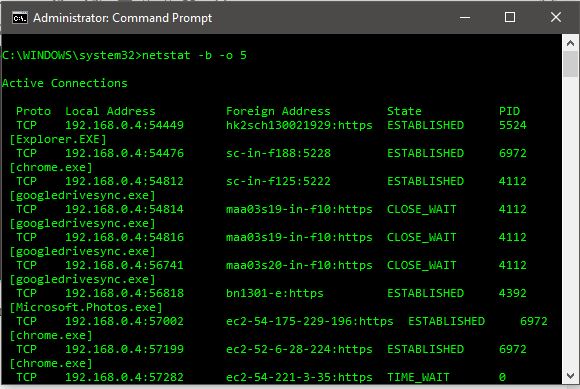
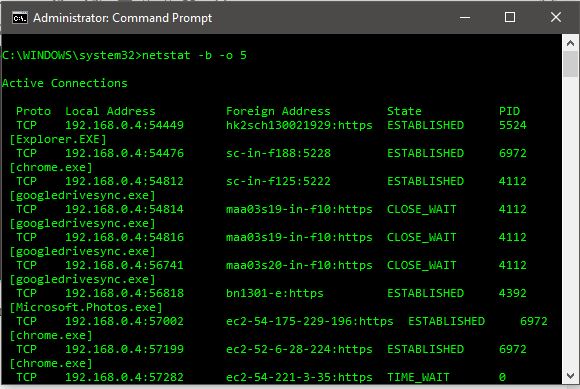
438How ToHow To Find And Kill A Remote Connecting Malware On Windows 10
Short Bytes: Here are the simple and easy steps on how to find, kill and delete a remote connecting malware using command prompt...
-

 136Data Security
136Data SecurityCrooks Deliver Android Malware via Fake Google Chrome Updates
Our research team has recently seen a large amount of activity in our cloud related to an Android infostealer disguised as a...
-

 111Data Security
111Data SecurityGerman Nuclear Power Facility Plagued with Malware since 2008
Good thing is that the servers weren’t connected to the Internet so no damage was done The Gundremmingen nuclear power facility’s computer systems...
-
 177Malware
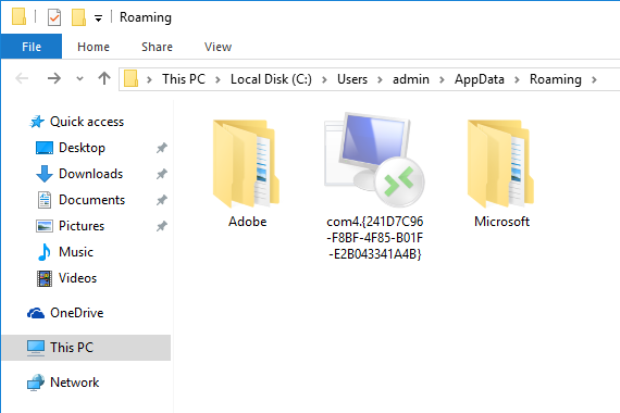
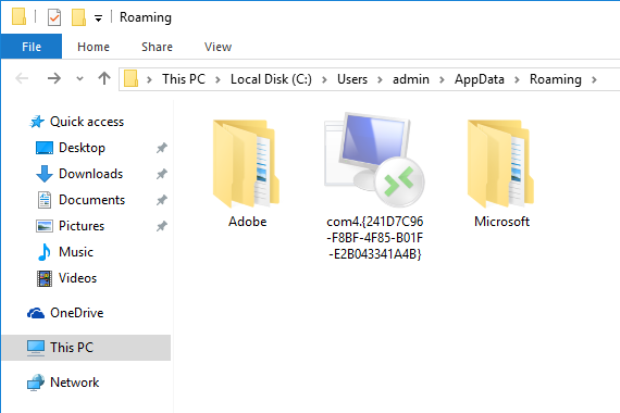
177MalwareMalware Takes Advantage of Windows ‘God Mode’
Microsoft Windows has hidden an Easter Egg since Windows Vista. It allows users to create a specially named folder that acts as...
-

 289Data Security
289Data SecurityEx Tor developer now working for government, responsible for Tor malware
The US government hired an insider to help it with the anonymous browser Tor. Tor is used by millions of people around...
-

 133Data Security
133Data SecurityFormer Tor developer created malware for the FBI to hack Tor users
How does the U.S. government beat Tor, the anonymity software used by millions of people around the world? By hiring someone with...
-

 136Data Security
136Data SecurityRUMMS: THE LATEST FAMILY OF ANDROID MALWARE ATTACKING USERS IN RUSSIA VIA SMS PHISHING
Recently we observed an Android malware family being used to attack users in Russia. The malware samples were mainly distributed through a...
-

 278Geek
278GeekSecurity Experts Discover Malware in Facebook’s Staff Server
This bug bounty hunter hacked Facebook but soon realize there’s something fishy going on A hacker taking advantage of Facebook’s bug bounty...
-

 284Data Security
284Data SecurityNewly discovered PWOBot malware is a total keylogger
Security Researchers Discover a Potentially Dangerous Cross-Platform PWOBot Malware Family- PWOBot Now this can be termed as devastating news for computer users...
-

 169Data Security
169Data SecurityPoS Malware Steals Credit Card Numbers via DNS Requests
Malware uses clever trick to avoid detection. A new version of the NewPosThings PoS malware is using a clever technique to extract data...
-
 295Data Security
295Data SecurityGozNym Malware Hits Banking Systems in Canada and The US
The U.S and Canadian banks are threatened by a double jeopardy, double the trouble as the twice powerful malware mega menace called...
-
 234Hacked
234HackedMicrosoft PowerShell — Hackers’ New Favorite Tool For Coding Malware
Short Bytes: You might not know but PowerShell, the ubiquitous force running behind the Windows environment, is slowly becoming a secure way...
-

 129Data Security
129Data SecurityMalware Created with Microsoft PowerShell Is on the Rise
PowerShell scripts seen in around 38% of malware incidents. Microsoft’s PowerShell task automation framework is becoming one of the most popular tools for...
-

 213Geek
213GeekLatest Facebook Video Malware Scam Targets Chrome Users
Whether it has reached you as “My First Video,” “My Video,” or “Private Video,” all these refer to a malicious Facebook scam...
-

 82Malware
82MalwareMalware found in surveillance cameras sold through Amazon
Security researcher finds malicious code embedded within cameras offered for sale on Amazon. Last week, independent security researcher Mike Olsen discovered that CCTV...
-

 82Data Security
82Data SecurityClick-Fraud Ramdo Malware Family Continues to Plague Users
Ramdo is a family of malware that performs fraudulent website ‘clicks.’ Ramdo malware activity first surfaced in late 2013 and has since...
-

 228Data Security
228Data SecurityMobile Devices Used to Execute DNS Malware Against Home Routers
Attacks against home routers have been going around for years—from malware that rigs routers to DNS rebinding attacks and backdoors, among others. ...
-
 103Malware
103MalwareBe careful products sold on Amazon are infected with malware
Beware, even things on Amazon come with embedded malware… this is the disconcerting discovery made by the expert Mark Olsen. The security expert Mike...
-
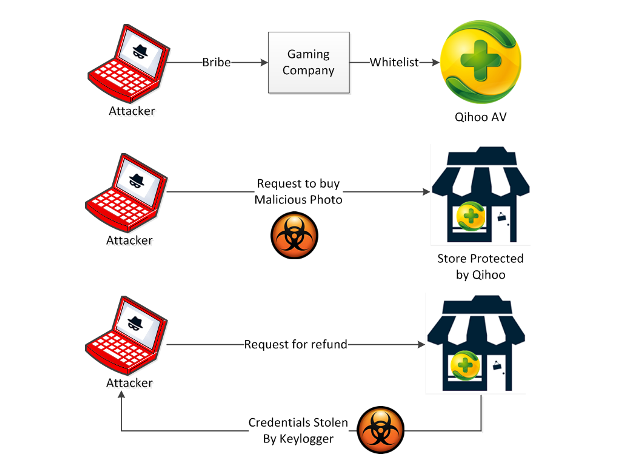
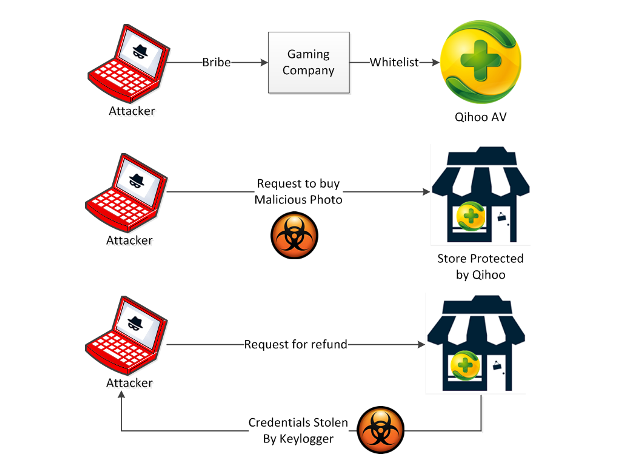 75Data Security
75Data SecurityQihoo 360: Just the Tip of the Whitelisted Malware Iceberg
The Check Point Mobile Threat Prevention team has long stressed how dangerous it can be to get apps from places other than...
-

 260Geek
260Geek“Evil Skype” Malware Kit “Su-A-Cyder” Lets Attacker Spy on Apple Devices
An “evil” version of Skype is uploaded to an Apple iPhone. A whitehat hacker created a tool that automates the process of...
-

 185Malware
185MalwareDDoS Attacks With BillGates Linux Malware Intensify
XOR botnet authors migrate to using BillGates malware. Over the past six months, security researchers from Akamai’s SIRT team have observed a shift...






