Search results for "Phone"
-

 1.7KMobile Security
1.7KMobile SecurityWhat to do you if your phone is lost or stolen
Losing your smartphone can be expensive, but the cost of the device may not be the final price you’ll be paying
-

 666Mobile Security
666Mobile SecurityHave you backed up your smartphone lately?
With World Backup Day upon us, we walk you through the ways to back up your iPhone or Android phone so that...
-

 1.2KPrivacy
1.2KPrivacyTop 5 Cool Apps to hack an iPhone in 2022
Can an iPhone be hacked? As you possibly understand, the iOS running system is constructed to be hacker-evidence. It also employs some...
-

 1.5KPrivacy
1.5KPrivacyIs your phone listening to you?
Do social media listen in on our conversations in order to target us with ads? Or are we just a bit paranoid?...
-

 3.5KHow To
3.5KHow ToTop 10 iPhone Hacking Apps and Tools | 2020 Edition
Are you looking for iPhone hacking apps that you can use for penetration testing, forensic analysis, or reverse engineering? You are in...
-
 4.5KNews
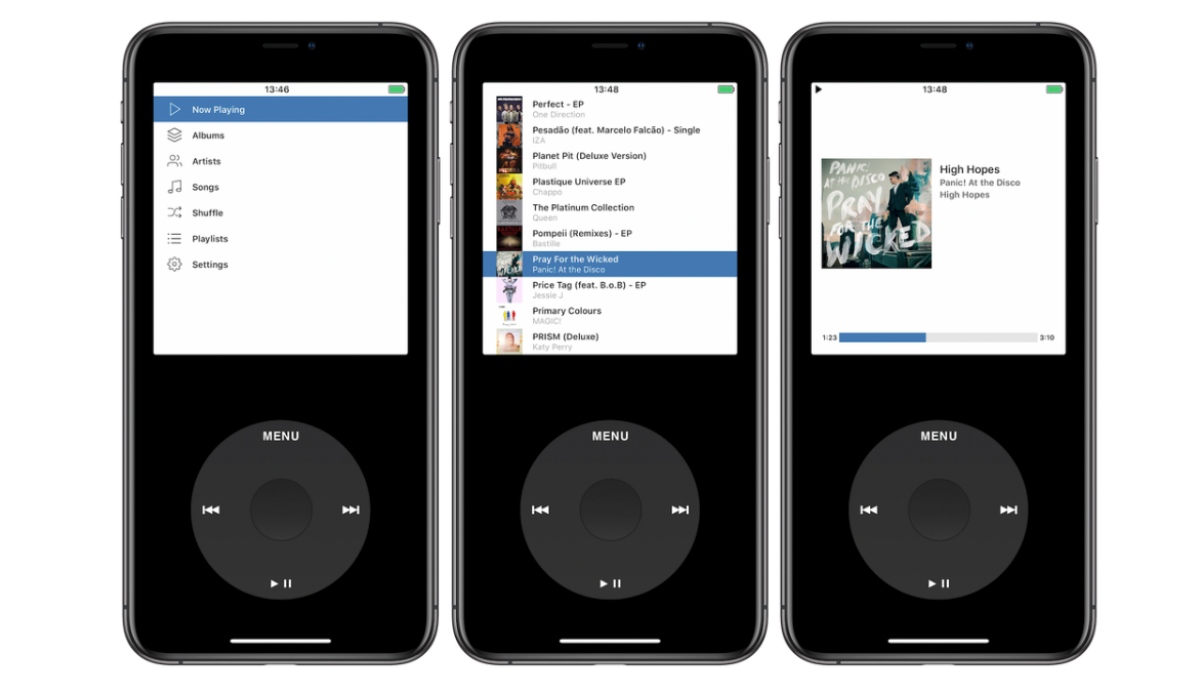
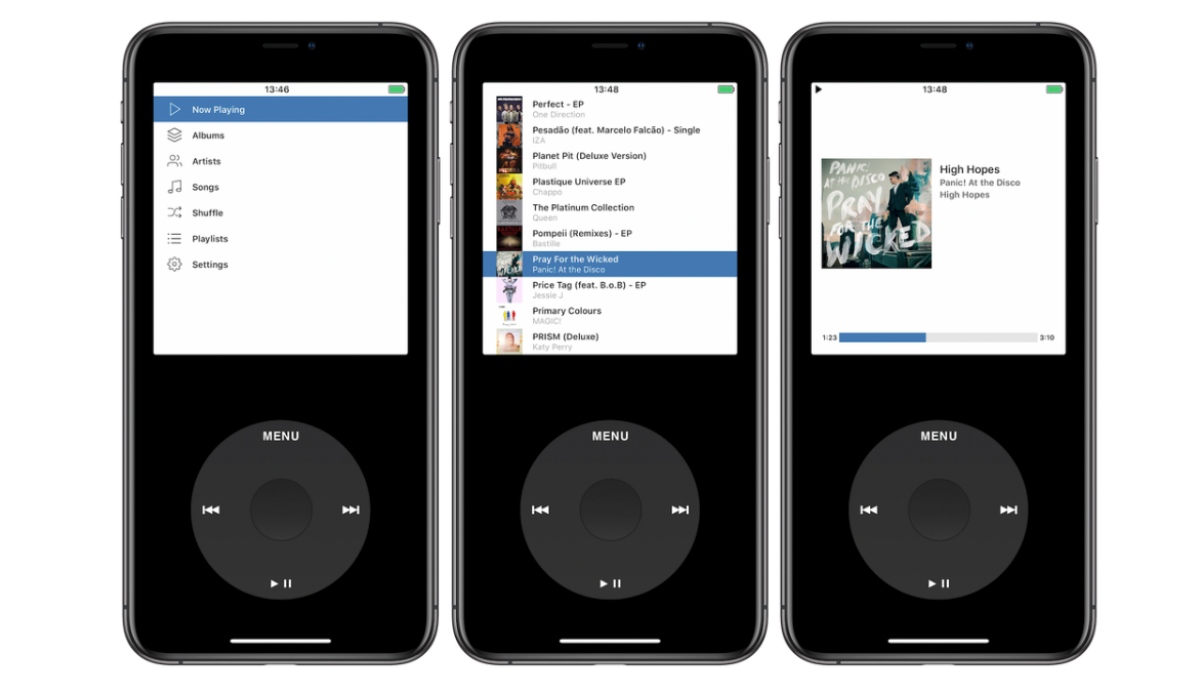
4.5KNewsThis App Turns Your iPhone Into iPod Classic With Iconic Click Wheel
Apple usually doesn’t allow emulator apps in the App Store citing its strong review policies. However, Louis Anslow, an app creator, has...
-
 1.4KNews
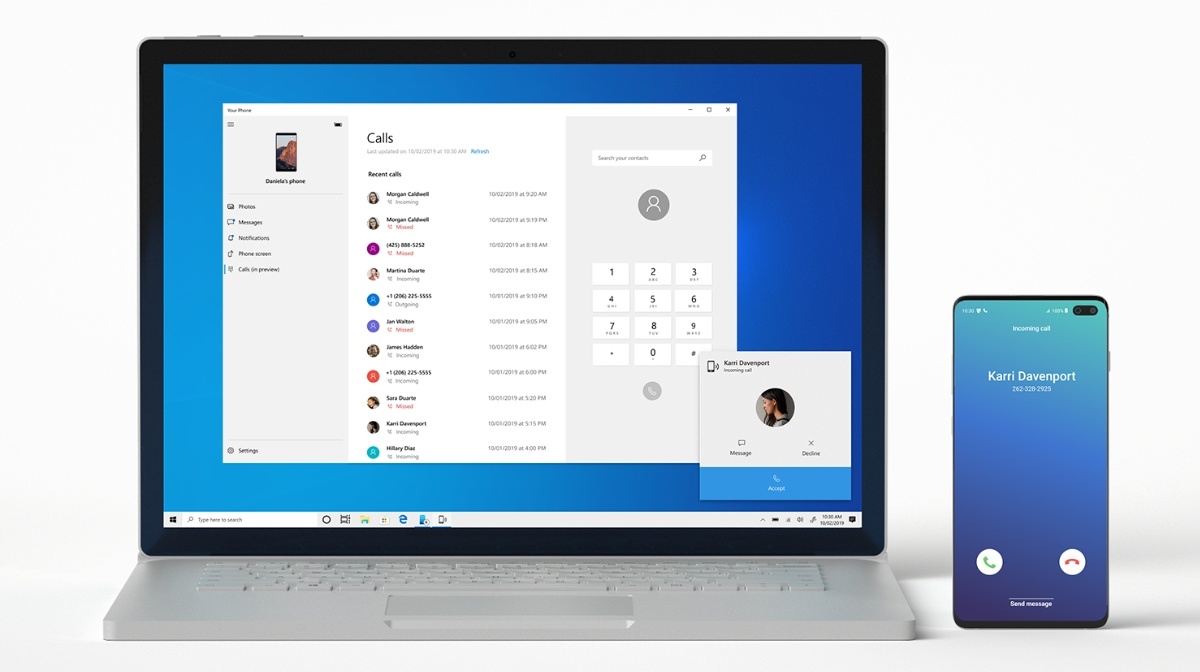
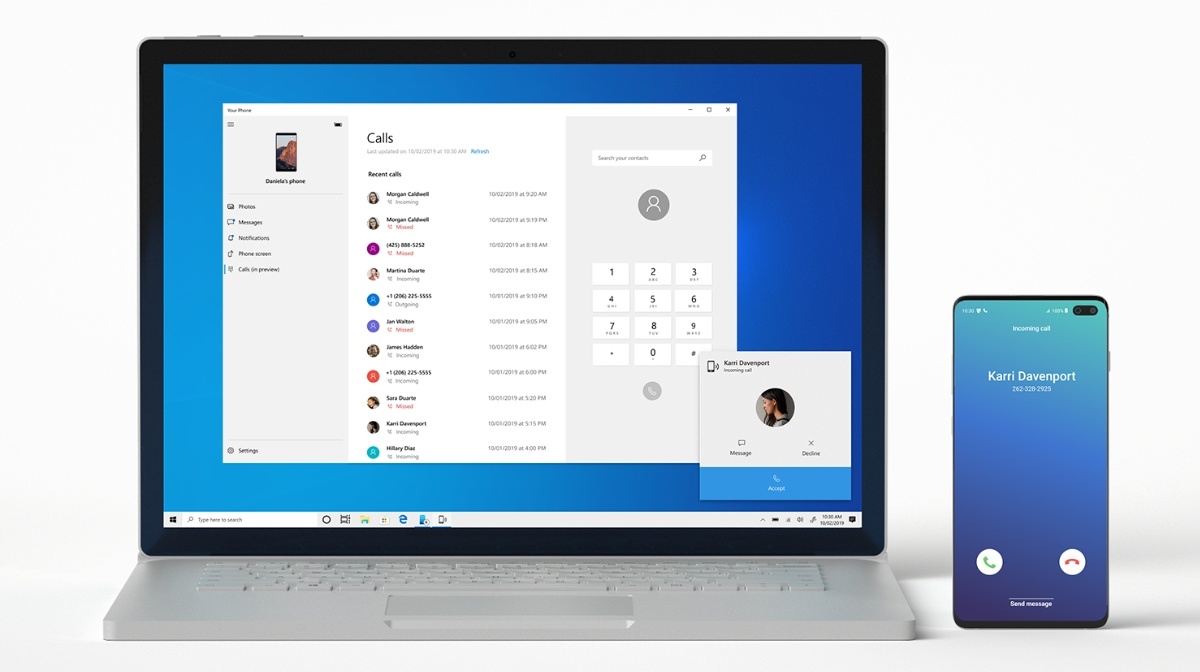
1.4KNewsNow Anyone Can Make ‘Phone Calls’ Via Windows 10 Your Phone App
When talking about the Apple ecosystem, one of the things that I like is that you can receive phone calls on your...
-

 2.1KNews
2.1KNewsThis Xiaomi Electric Bike Has Twice As Big Battery As Your Smartphone’s
A Xiaomi Electric Bike is available for consumers to buy at $430 or Rs. 30,700. The brand new electric bike or e-Bike...
-

 2.1KHack Tools
2.1KHack ToolsSeeker v1.2.1 – Accurately Locate Smartphones Using Social Engineering
Concept behind Seeker is simple, just like we host phishing pages to get credentials why not host a fake page that requests...
-

 1.7KVulnerabilities
1.7KVulnerabilitiesFBI advises to put duct tape over Smart TV camera and microphone
Ransomware on Your TV, Get Ready, It’s Coming Currently, smart TVs come with an Internet connection, which allows users to browse the...
-

 2.4KVulnerabilities
2.4KVulnerabilitiesOne again Zoom video conferencing gives hackers easy access to camera and microphone
Cisco recently issued a security alert for all companies using the Zoom Connector, mentioning that this driver could be used maliciously. According...
-

 4.2KNews
4.2KNewsTurn Your Android Phone Into Google Pixel With Lawnchair Launcher 2.0
Many Android launchers strive to give a Google Pixel experience on your current Android devices; however, all of them fall short when...
-

 2.9KNews
2.9KNewsThis Xiaomi Device Charges Your Smartphone & Keeps Your Hands Warm
Xiaomi is not only known for making decent smartphones at decent prices but also produces other quirky products with interesting capabilities. Among...
-

 4.8KNews
4.8KNewsThis iPhone Battery Charging Case Has A ‘Secret Button’ Trick
Since Apple released this year’s iPhone iteration — the iPhone 11 series — we saw the entry of several accessories for the...
-
 3.3KHack Tools
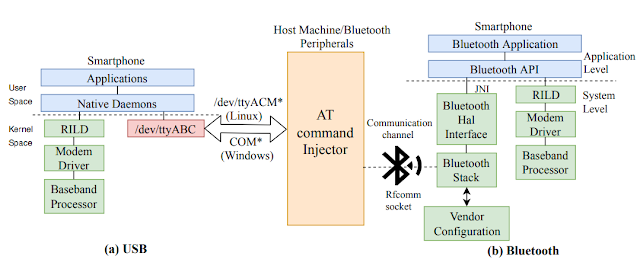
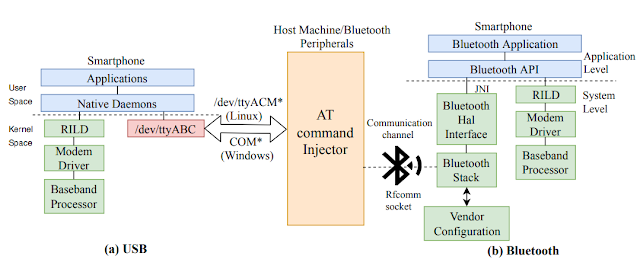
3.3KHack ToolsATFuzzer – Dynamic Analysis Of AT Interface For Android Smartphones
“Opening Pandora’s Box through ATFuzzer: Dynamic Analysis of AT Interface for Android Smartphones” is accepted to the 35th Annual Computer Security Applications...
-

 4.7KNews
4.7KNewsThis Dual-Screen Android Phone Is Also A Linux Computer
We rarely witness innovative products put up on crowdfunding campaign websites like Indiegogo emerge as commercial products. However, here is a company...
-

 3.0KNews
3.0KNewsTesla Model 3 Battery Drain After 22 Days Is Lower Than Your Smartphone
The Tesla Model 3 ‘Vampire’ battery drain is no longer a problem because after a span of 22 days the car’s battery...
-

 1.4KHow To
1.4KHow ToHow To Stop Someone From Spying On Your Cell Phone
People have the right to privacy on their mobile phones. However, with the increase of malicious hackers and the use of third-party...
-
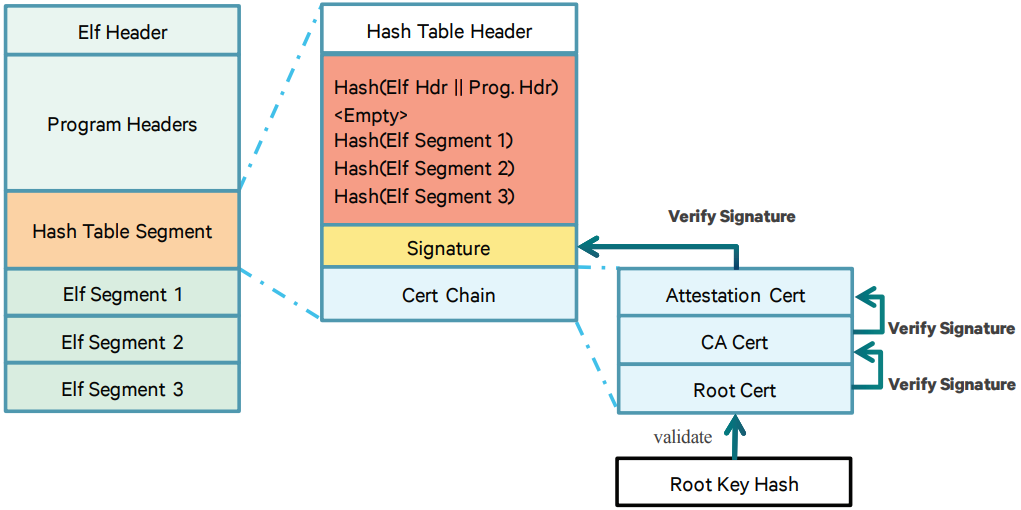
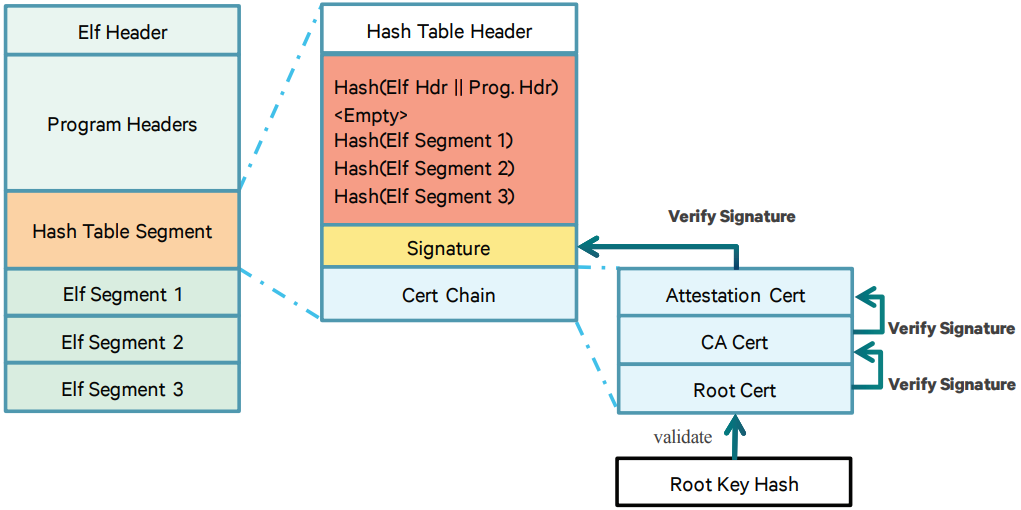 3.9KNews
3.9KNewsQualcomm vulnerability may reveal critical data in your Android phones
Recently, Check Point researchers analyze a vulnerability (CVE-2019-10574) discovered in the Qualcomm Trusted Execution Environment (TEE) for Android devices. An attacker could...
-

 1.4KHow To
1.4KHow To3 ways an attacker may compromise a phone without the victims knowledge
We carry our mobile phones everywhere with us. These devices store our personal information. If this data falls into the wrong hands,...
-

 661News
661NewsAndroid Flaw Lets Camera Spy On You Even When Your Phone Is Locked
A security flaw in Android OS makes it possible for rogue apps to hijack a user’s smartphone camera and take pictures, record...






