Search results for "PowerShell"
-

 330Evasion & Obfuscation
330Evasion & ObfuscationPowerShdll – Run PowerShell with rundll32 (Bypass software restrictions)
Run PowerShell with dlls only. Does not require access to powershell.exe as it uses powershell automation dlls. dll mode: Usage: rundll32 PowerShdll,main...
-

 305Malware
305MalwareFileless malware that uses PowerShell scripts from Window’s registry leading to Click Fraud Malware Campaign
Nowadays Hackers Distributing Advanced Fileless Malware with Evasion capabilities which are very Difficult to Detect. These types of malware sit in the...
-
 97Hackers Repository
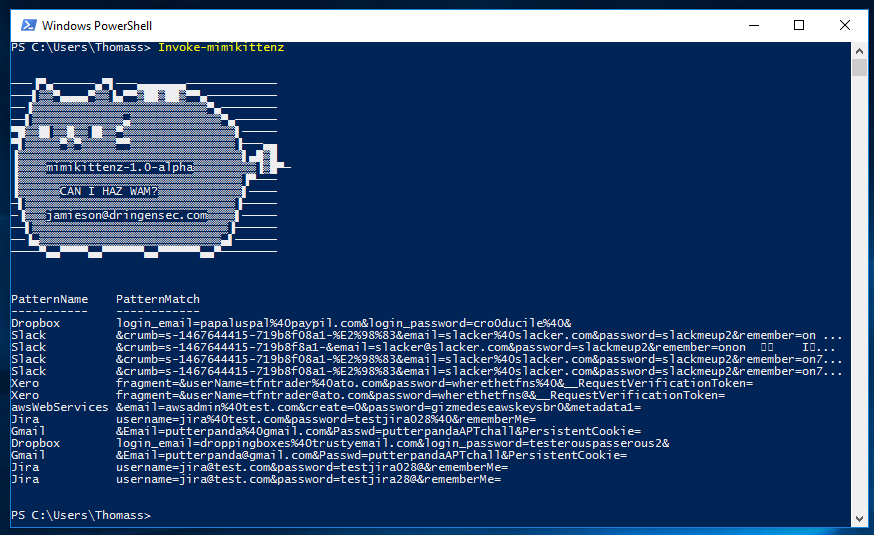
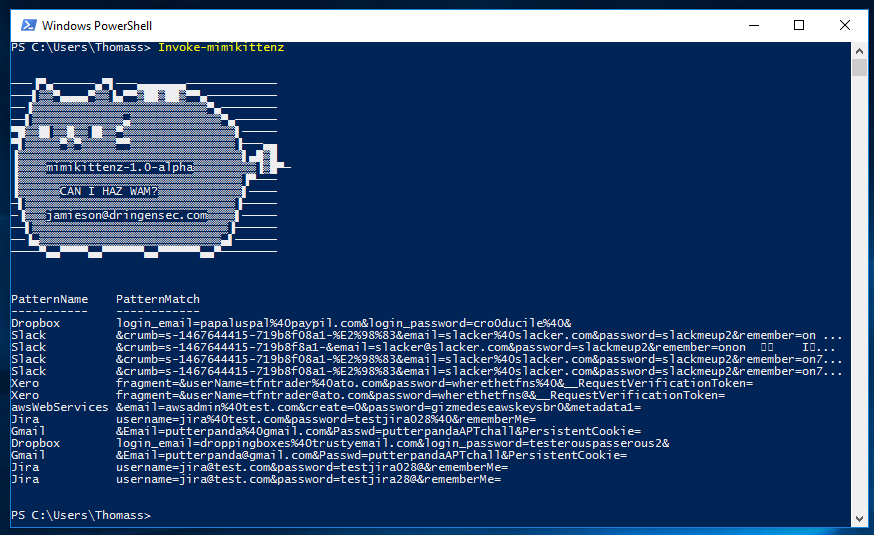
97Hackers Repositorymimikittenz – Powershell Tool for Extracting Juicy info from Memory RAM
A post-exploitation powershell tool for extracting juicy info from memory. mimikittenz mimikittenz is a post-exploitation powershell tool that utilizes the Windows function...
-

 197Vulnerabilities
197VulnerabilitiesPowerShell Injection with Diskless Payload Persistence and Bypass Techniques
PowerShell continues to be the tool of choice for defenders, IT administrators, and hackers. The extensibility, support, and ability to have a...
-

 206Hackers Repository
206Hackers RepositoryGenerate-Macro – Powershell Script To Generate a Malicious Microsoft Office document with a Specified Payload and Persistence Method
Credits Matt Nelson (enigma0x3) – Coded by Matt Nelson (@enigma0x3) DOWNLOAD GENERATE-MACRO https://github.com/enigma0x3/Generate-Macro This Powershell script will generate a malicious Microsoft Office...
-

 98Hackers Repository
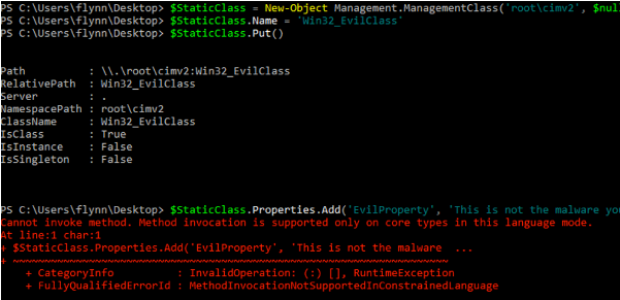
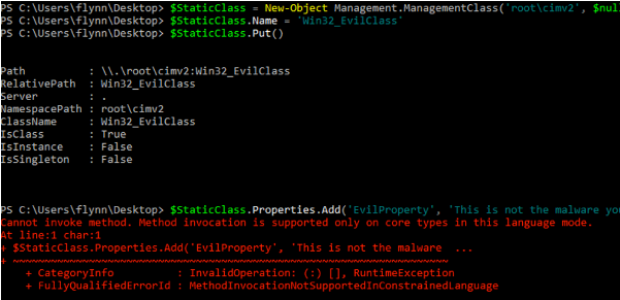
98Hackers RepositoryResearcher Developed A WMI-Based Hacking Tool in PowerShell
Windows Management Instrumentation (WMI) is a set of specifications from Microsoft for combining the management of devices and applications in a network...
-
 277Vulnerabilities
277VulnerabilitiesWMImplant – A WMI Based Agentless Post-Exploitation RAT Developed in PowerShell
Just over one year ago (November 2015), I released WMIOps, a PowerShell script that enables a user to carry out different actions...
-

 306Vulnerabilities
306VulnerabilitiesAttackers Leverage Excel, PowerShell and DNS in Latest Non-Malware Attack
Increasingly, cyberattackers have been leveraging “non-malware” attack methods to target vulnerable organizations. Recently, the Carbon Black Threat Research Team was alerted about...
-
Hackers Repository
Unicorn – PowerShell Downgrade Attack Evade Anti-Virus
Unicorn is a simple tool for using a PowerShell downgrade attack and inject shellcode straight into memory. Based on Matthew Graeber’s powershell...
-

 217Data Security
217Data SecurityResearchers uncover PowerShell Trojan that uses DNS queries to get its orders
Delivered by “secure” Word doc, pure PowerShell malware fetches commands from DNS TXT records. Researchers at Cisco’s Talos threat research group are...
-

 191Exploitation
191ExploitationTater – A PowerShell implementation of the Hot Potato Windows Privilege Escalation Exploit
Tater is a PowerShell implementation of the Hot Potato Windows Privilege Escalation exploit. Included In p0wnedShell – https://github.com/Cn33liz/p0wnedShell PowerShell Empire – https://github.com/PowerShellEmpire/Empire...
-
 125How To
125How ToHow to Install Powershell on A Linux Computer
We know that PowerShell is open source. It is now available for both Linux and Mac. You can download the official packages from...
-
 195Incidents
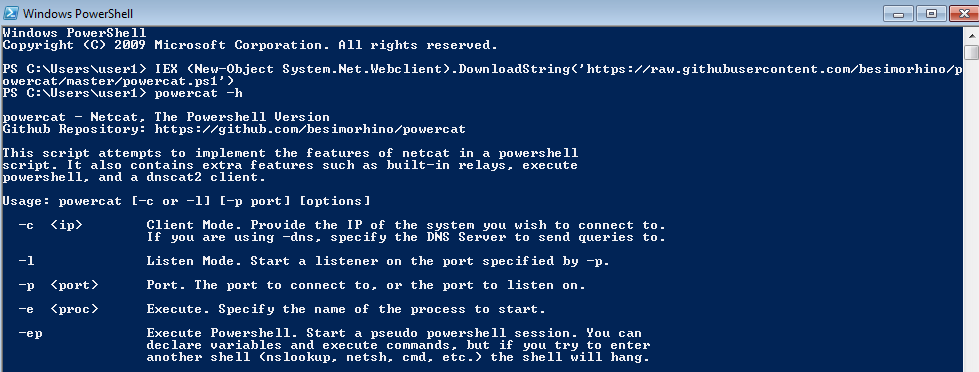
195IncidentsPentesting Windows environments: remote delivery of PowerShell payloads
PowerShell is an amazing post-exploitation tool available to the attacker during engagements in Windows environments. Tools like PowerSploit or PowerShell Empire help...
-

 156Malware
156MalwareMicrosoft PowerShell Becomes a More Popular Malware-Spreading Tool
Symantec warns of growing number of malicious scripts. Microsoft PowerShell is a really powerful tool for IT professionals running Windows, and the...
-
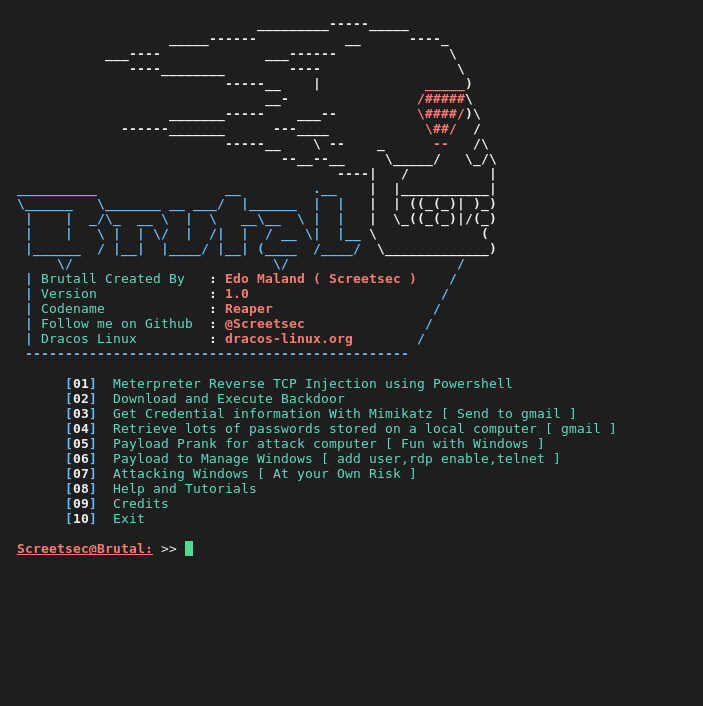
 192Hack Tools
192Hack ToolsBrutal – Toolkit to quickly create various payloads,powershell and virus attacks
Brutal is extremely useful for executing scripts on a target machine without the need for human-to-keyboard interaction ( HID -ATTACK )...
-
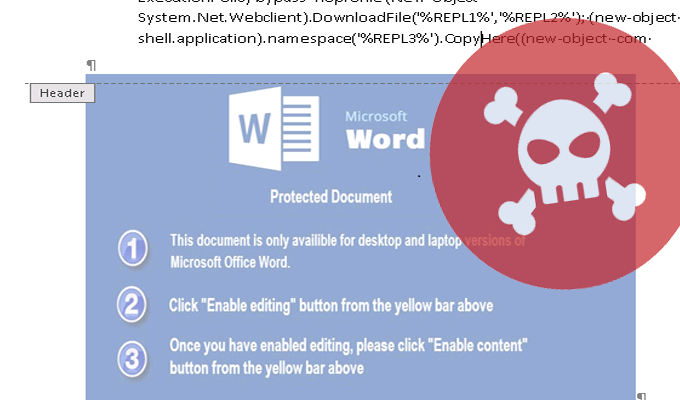
 160Data Security
160Data SecurityHANCITOR DOWNLOADER ABUSING APIS, POWERSHELL COMMANDS
We recently observed Hancitor attacks against some of our FireEye Exploit Guard customers. The malicious document used to deliver the Hancitor executable...
-

 274How To
274How ToHow To Install Microsoft PowerShell On Linux And OS X
Short Bytes: Microsoft has open sourced the code of its command line shell and scripting language PowerShell, bringing this automation framework to Linux and...
-

 164Malware
164MalwareBrazilian banking Trojans meet PowerShell
Crooks are always creating new ways to improve the malware they use to target bank accounts, and now Brazilian bad guys have...
-
 291Geek
291GeekMicrosoft PowerShell Is Open Source, Now Available On Linux And OS X
Short Bytes: Microsoft has made the official announcement that it’s open sourcing PowerShell. As a result, the company has released the required...
-
 420How To
420How ToHow To Find Windows Product Key Using CMD, PowerShell, And Windows Registry
Short Bytes: If you are willing to reinstall your Windows operating system, it’s possible that you’ll be stuck at some point due...
-
 252Data Security
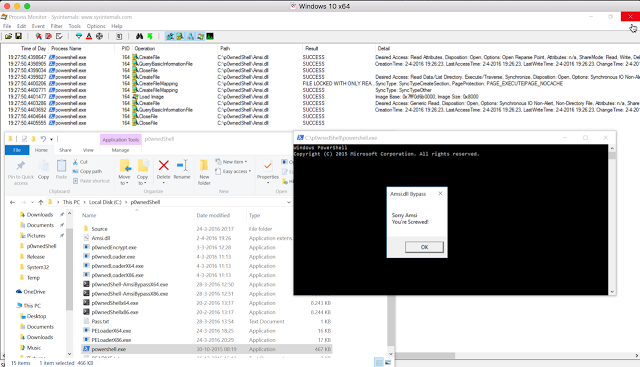
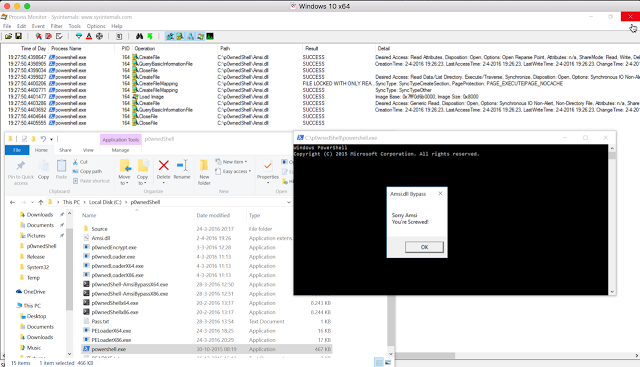
252Data SecurityBypassing Amsi using PowerShell 5 DLL Hijacking
While doing some research on the inner workings of Microsofts new Antimalware Scan Interface technology within Windows 10, i found a DLL...






