Search results for "Research"
-

 69Cyber Crime
69Cyber CrimeSmartphone “contactless” payment systems may be at risk from snooper devices, researchers warn
Phones such as Samsung’s Galaxy S4 ship with Near Field Communication chips built in - and many companies hope to use these...
-

 393Cyber Crime
393Cyber CrimeSome D‑Link routers contain “backdoor” which allows remote access, researcher warns
Some models of the popular routers made by D-Link contain a “backdoor” which could allow a remote attacker access to settings and...
-

 89Password
89PasswordWindows 8 picture passwords “can be cracked”, researchers warn
The “picture passwords” used in Windows 8 machines are more vulnerable than Microsoft hoped, a research team claims. An analysis of more...
-
 98Malware
98Malware“Dr Jekyll” apps can sneak into App Store by hiding their dark side, researchers claim
Apps with a hidden “dark side” could sneak past Apple’s approval process, according to researchers at Georgia Tech. The researchers proved this...
-

 87Cyber Crime
87Cyber CrimeAndroid “master key” leaves 900 million devices vulnerable, researchers claim
Up to 900 million devices running Android could be affected by a new vulnerability which would allow cybercriminals “full control” over affected...
-

 105Malware
105MalwareMass malware attacks “could be triggered by music”, researchers claim
Future malware attacks could be triggered by music or even lighting - allowing cybercriminals to command and control large numbers of infected...
-
 265Data Security
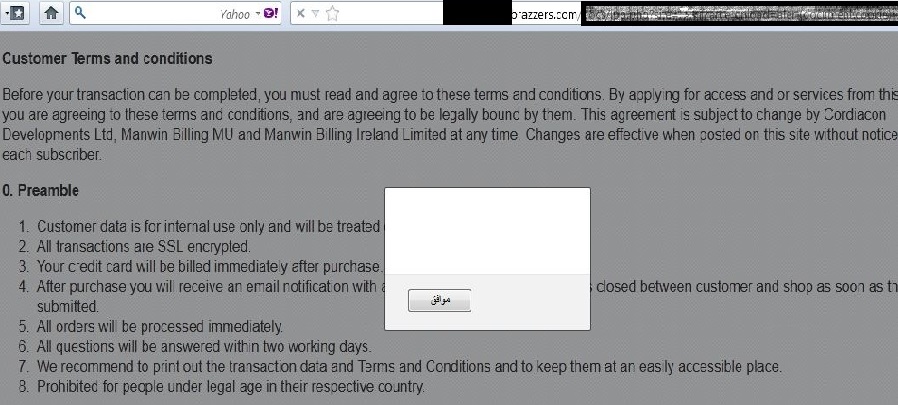
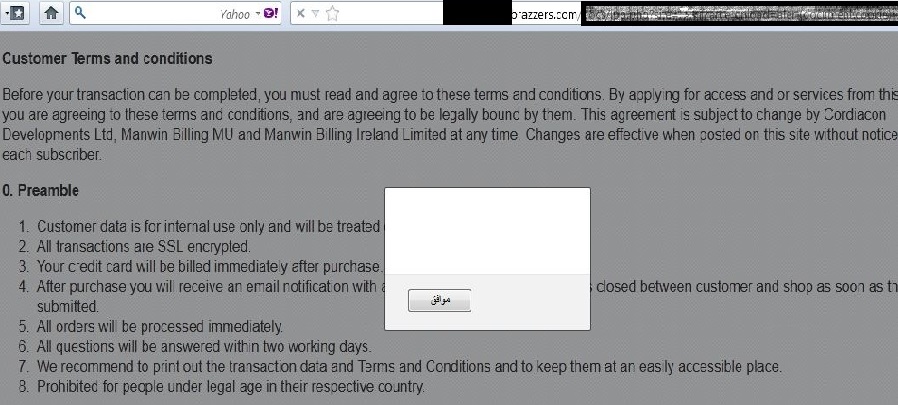
265Data SecurityPakistani Researcher Founds Critical XSS Vulnerability on Brazzers, BMW, Toyota and Ford Website
Earlier I updated readers with latest vulnerabilities that were found on IndiaTimes and ASK.com by a Pakistani security researcher Danish Tariq, this...
-

 350News
350NewsPakistani Security Researcher Founds XSS Vulnerability in IndiaTimes and Ask.com
An independent security researcher from Pakistan, going with the name of Danish Tariq has claimed to found cross site scripting vulnerability (XSS)...
-
 200Data Security
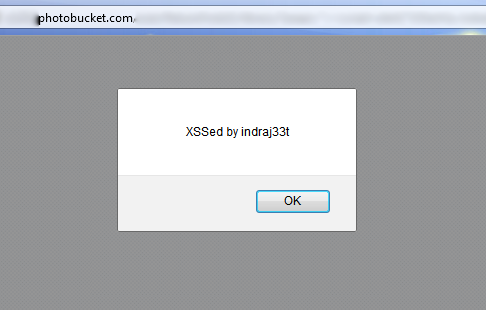
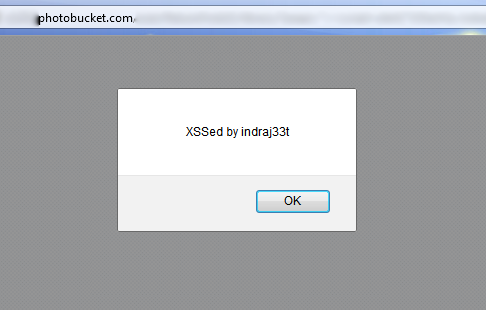
200Data SecurityIndian Security Researcher Founds XSS Vulnerability in Photobucket.com
A 15 years old independent security researcher from India, going with the name of Indrajeet Bhuyan has claimed to found cross site scripting...
-

 82Cyber Crime
82Cyber CrimeGlobal Cyber Security research hub to be set up at Oxford University
A new Global Center for Cyber Security at the University of Oxford will coordinate international work on cyber threats and cyber security....
-

 125News
125NewsSecurity Researchers Show How WiFi-Enabled Cameras can be Easily Hacked to Spy on People
Have you ever thought of your digital SLR acting as a spy on you? Well, this wasn’t true before until two German found a weakness in...
-
 460Privacy
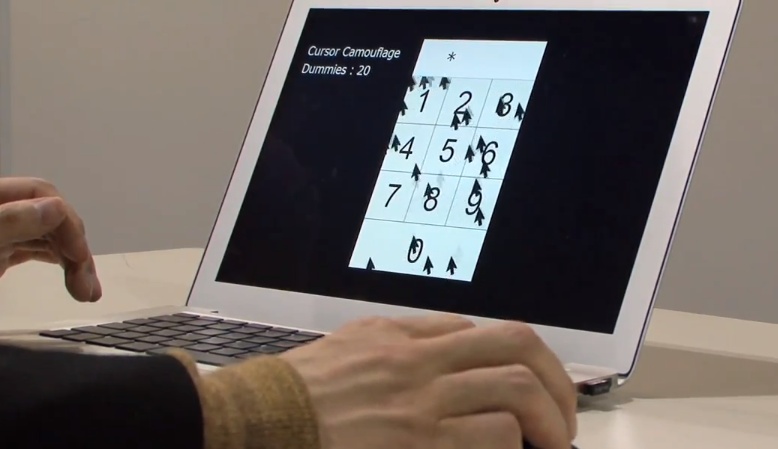
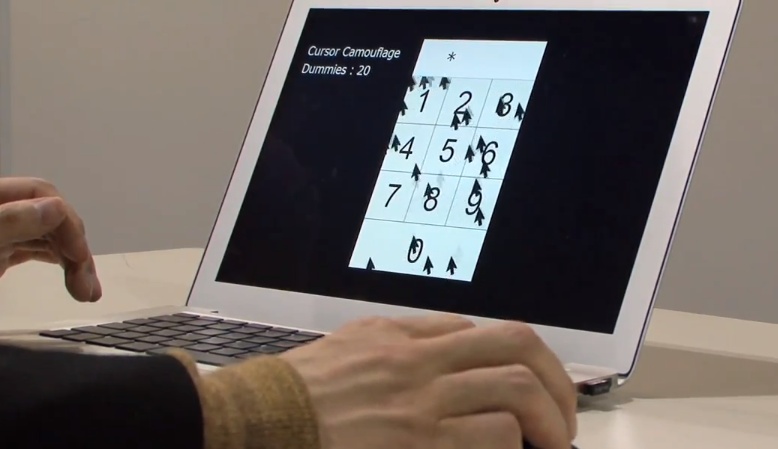
460PrivacyMulti‑cursor password system unveiled by Japanese researchers
A prototype multi-cursor system designed to improve the security of on screen password entry has been posted onto DigInfo, the Tokyo based...
-

 217News
217NewsFake Wikipedia Researcher Hacked Bumi Chairman’s Computer
A coal firm in Indonesia named as Bumi has faced heavy crisis in the recent past, but, firm’s physical performance wasn’t the reason behind...
-

 270News
270NewsSyrian Higher Commission for Scientific Research Breached, 350+ Accounts Leaked by @Gevolus
The official website of Syrian Higher Commission for Scientific Research was breached and in result more then 350+ login information was leaked by...
-

 215Geek
215GeekFamous Android apps ‘leak’ personal details, research says
In a study conducted by the researchers at Germany’s Leibniz University, nearly 13,500 which is 8 percent of famous Android apps can be...
-

 246News
246NewsNasa.gov Ames Research Center hacked & Database leaked By Zyklon B
Nasa, that is known for its poor security is again under attack. This time Nasa’s Ames Research Center database was hacked and leaked...
-
Malware
ESET Research podcast round up
Here are some recently released podcasts by ESET Rearchers, addressing current topics such as the recent VeriSign hacks, the takedown of MegaUpload,...
-
Social Engineering
How to Fool a Security Researcher
...Andrew Lee conducted a fun but disquieting thought experiment in the course of an amusing and informative presentation on user education at...
-
Cyber Crime
Natl Research Council Says: Show Us The MONEY
Surprised to find annual cybercrime damage spread somewhere between 300 million and 54 BILLION? So is the Director of National Intelligence. Today...
-
Cyber Crime
IEEE eCrime Researchers Summit 2010 Call for Papers
The fifth IEEE eCrime Researchers Summit 2010 once again will be held in conjunction with the 2010 APWG General Meeting between October...
-
Malware
Research and the Art of the Obvious
We know that spam works: well, it works well enough for spammers to keep devoting time and money into pumping sewage into...






