Search results for "Research"
-

 371Cyber Crime
371Cyber CrimeGoogle’s Nest security warning after researchers show off 60‑second hack
Google’s Nest thermostat can be hacked in under a minute, according to a blog post and video posted by GTV Hacker. The...
-
 229Surveillance
229SurveillanceHow ANGRY BIRDS Game App is Sharing Your Personal Data with NSA: Proved by Researchers
Mobile applications collecting personal data of users in one form or the other is no more a stunning news. The Snowden documents...
-
 134Privacy
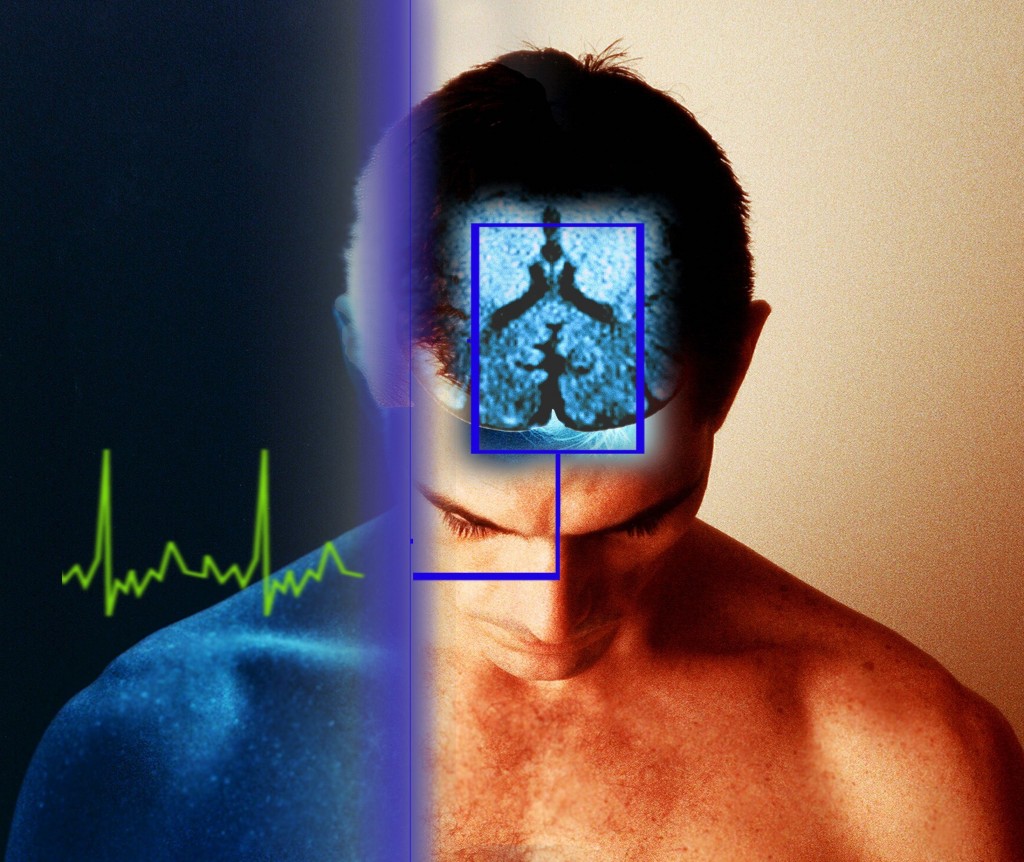
134PrivacyBrainwave privacy standard “is needed” to prevent spying on EEG scan data, researchers warn
Smartphone apps and home equipment for scanning brainwaves could lead to a future in which governments or companies misuse such data as...
-

 168Privacy
168Privacy‘Secure’ web browsing can leak private data to employers and ISPs, researchers warn
University of Berkeley researchers have revealed a technique for identifying individual web pages visited ‘securely’ by users, with up to 89% accuracy,...
-

 104Malware
104MalwareQR codes pose hidden danger to smartphone users, researchers claim
The increasing use of QR codes as a way to add interactive elements, apps and websites to display advertising, competitions or print...
-

 386Password
386PasswordTwo‑thirds of couples ‘share passwords to online accounts’, Pew research finds
Couples who have been in a long-term relationship indulge in risky online behaviour, such as sharing passwords for online accounts, with two-thirds...
-

 182Password
182PasswordSniffing body odor has ‘enormous potential’ for biometrics, researchers claim
Body odor could be used as a biometric identifier, with high rates of accuracy, due to chemical patterns in the smell that...
-

 392Cyber Crime
392Cyber CrimeCellphone‑sized $20 gadget can remote‑control car electronics, researchers claim
A tiny, cheap gadget which can ‘hack’ into the network of modern cars to receive radio commands ranging from controlling steering and...
-

 417Malware
417MalwareZombie detector: Half‑century‑old tool may help sniff out botnets, researchers claim
A statistical tool first used in 1966 and currently used in speech and gesture recognition may hold a key to sniffing out...
-

 85Cyber Crime
85Cyber CrimeBorrowing tricks from cybercriminals can ‘scare’ web users into safe browsing, Cambridge researchers claim
Computer users often feel bombarded by warnings about malware - particularly in internet browsers, which often repeatedly warn about risky sites -...
-

 68Cyber Crime
68Cyber CrimeMajor cyber attacks ‘can be predicted’ using computer model, researchers claim
Major international cyber attacks follow a pattern - and attacks such as Stuxnet, which targeted Iran's nuclear plant can be predicted by...
-
 411Cyber Crime
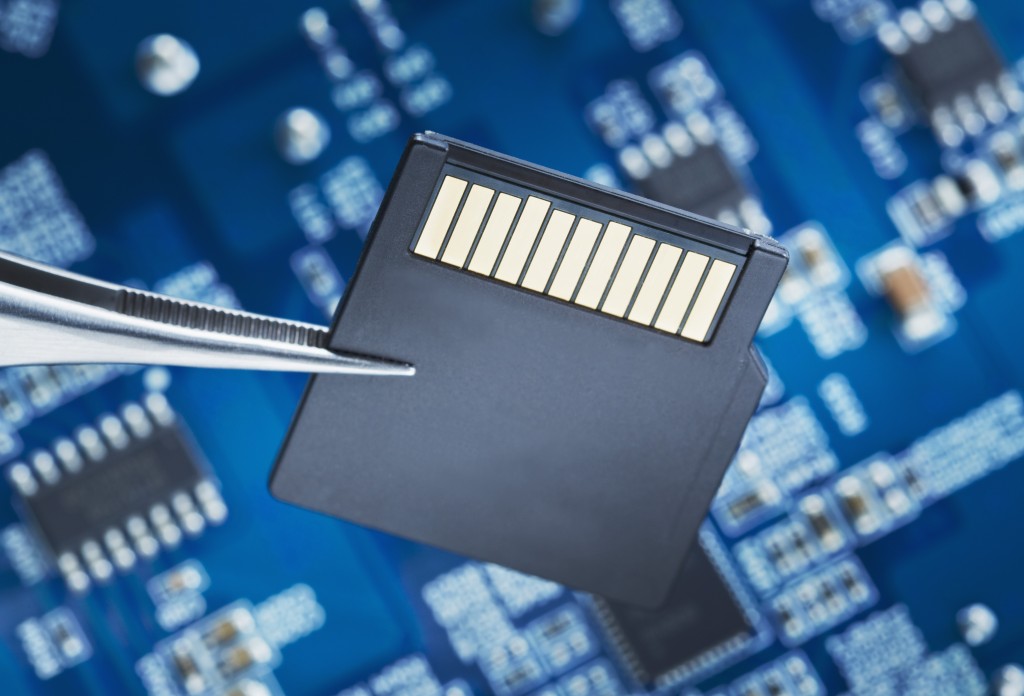
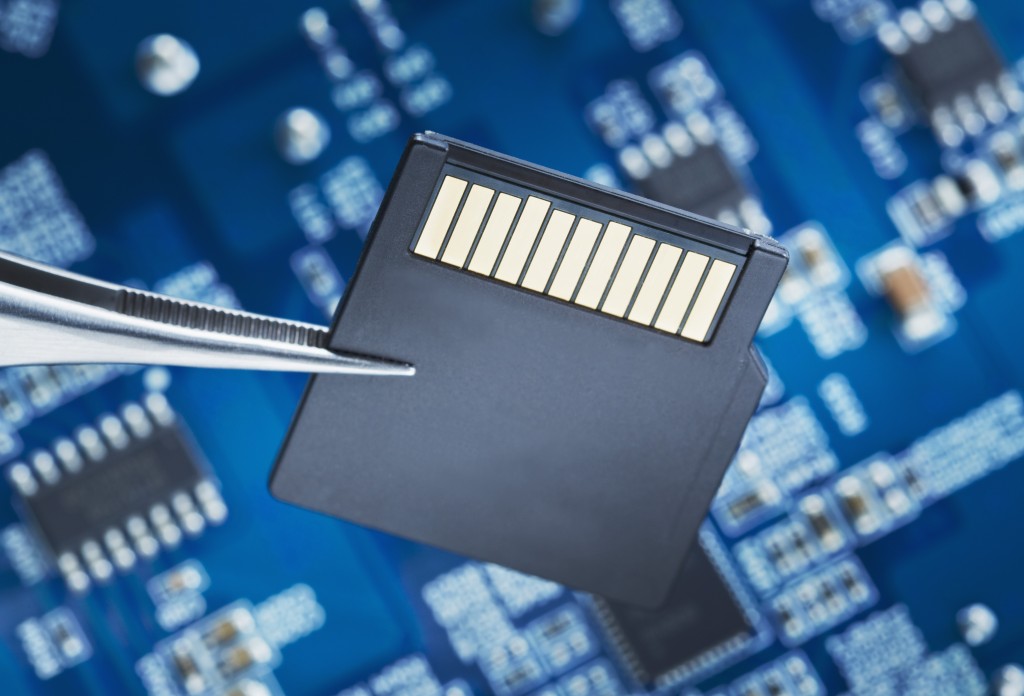
411Cyber CrimeCould new malware steal data from INSIDE your SD card? Researchers claim even solid‑state PC drives could be at risk
Two researchers have demonstrated an attack that could alter and steal data direct from MicroSD cards, using tiny microcontrollers on the cards...
-

 117How To
117How ToCan you hear us now? ESET researchers podcast every week
Have you checked out the weekly podcast by ESET security researchers? It's called the ESET Malware Report and it covers many security...
-

 389Malware
389MalwareUltrasonic cyber‑attack can “steal information” even from high‑security systems, researchers warn
An audio communication system designed for ultrasonic underwater communications can be used to steal data - even from disconnected PCs in secure...
-

 438Android
438AndroidDeath message: Google Nexus phones can be remote‑crashed by SMS, researcher warns
At least two recent models of Google’s flagship Nexus Android handsets can be crashed remotely - simply by sending them a flurry...
-

 90Password
90PasswordDoes your mouse know it’s you? Researchers claim patterns can “fingerprint” users – and lock out imposters
When any computer user types on a keyboard, the pattern of keystrokes is unique - like a fingerprint. When using a mouse,...
-

 252Surveillance
252SurveillanceNSA: Toilet Cameras are for Research Purposes Only.
We are well familiar with the NSA‘s spying over its own citizens and all over the globe but can the government go to a limit...
-

 394Cyber Crime
394Cyber CrimeMore D‑Link routers are vulnerable to attacks, researcher claims
More vulnerabilities have been discovered in a D-Link router, leaving the device vulnerable to attacks via its web interface - only weeks...
-
 94Password
94PasswordNew ‘inkblot’ passwords could be safe – even AFTER a big breach, researchers claim
The system relies on users describing patterns of blots, then matching descriptions to patterns - and should be foil the automated programs...
-

 92Malware
92MalwareGhost in the machine: Mysterious malware “jumps” between disconnected PCs, researcher claims
A three-year-battle with a mysterious new strain of malware has led researcher Dragos Ruiu to conclude that the BadBIOS malware infesting his...
-

 96Malware
96MalwareScary Code: Top 5 malware that kept researchers up at night
If sinister pieces of malicious code could rise from the dead on Halloween, which would be the most scary for antivirus researchers?...






