Search results for "Research"
-

 202Data Security
202Data SecurityResearch finds critical out-of-the-box vulnerabilities on big name laptops
Original Equipment Manufacturers (OEM) refer to the first boot of a new PC as the out-of-box experience (OOBE). As you battle your...
-

 91Vulnerabilities
91VulnerabilitiesIsraeli researchers poke holes in Samsung KNOX security system
The serious vulnerabilities impact Samsung’s Knox security sandbox. A number of severe problems have been discovered within the Samsung Knox security system in...
-
 249Geek
249GeekResearchers Validate Link Between Cancer and Cellphone Radiations
The National Toxicology Program (NTP) carried out a US $25million study, which spanned over 2.5 years. Now, we have gotten to know...
-
 222Geek
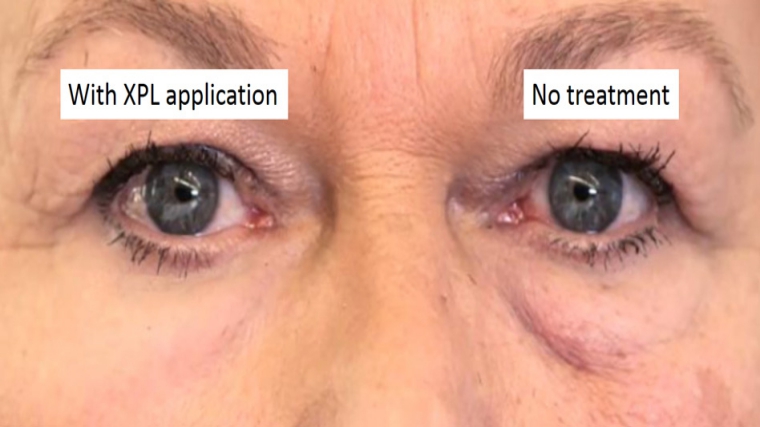
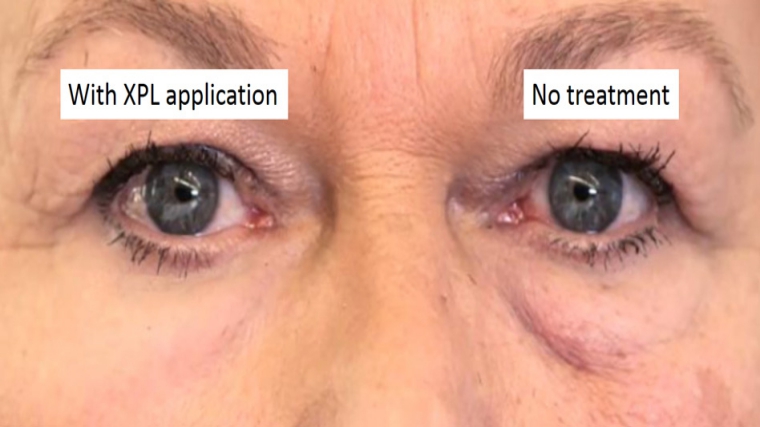
222GeekRevolutionary Tech from MIT Researchers: Skin Cream Remove Wrinkles Instantly
This Miraculous Skin Cream can Remove Wrinkles Instantly Reducing wrinkles and preventing the signs of aging from affecting our youthful appearance and...
-

 332News
332NewsResearcher finds Mexico’s entire voter database (93.4 million) online
Someone leaked entire Mexican voter data on the Internet and it was not even password protected A database containing voter data of...
-

 83Vulnerabilities
83VulnerabilitiesApple just fixed an iMessage bug that researchers called easily exploitable
Your chat history on iMessage just went through a period when it was not altogether safe, but now, all wrongs have been...
-

 63Data Security
63Data SecurityHacking Tesla Model S, too much noise around a great research
Last week at the CeBIT the Lookout’s Co-Founder and CTO Kevin Mahaffey talked about hacking Tesla Model S providing indications on possible...
-
 98Malware
98MalwareResearchers Trick Radamant Ransomware C&C Server into Revealing Decryption Keys
Security researchers 2, Radamant coder 0.Researchers from InfoArmor, an Arizona-based cyber-security firm, have discovered an SQL injection flaw in the control panel...
-

 83Incidents
83IncidentsInternet-Connected Trucks Can Be Tracked and Hacked, Researcher Finds
Insecure configurations expose car telematics to hacking. Industrial vehicles like trailer trucks, delivery vans, or buses that have an Internet connection, can be...
-

 94Data Security
94Data SecurityThe DoD funded the Carnegie Mellon University’s research on Tor Hacking
A judge has confirmed that US Departement of Defense funded the Carnegie Mellon University to conduct research on the Tor hacking. In...
-
 176Data Security
176Data SecurityKaspersky Researcher Shows How He Hacked His Hospital While Sitting In His Car
Short Bytes: When we visit a hospital, we put our complete trust in our doctor and the medical equipment that he/she uses....
-

 101Data Security
101Data SecurityIBM Researchers Hack Into A Smart Building To Highlight The Backdoors Created For Hackers
This smart building was hacked by IBM researchers to show hacking risks associated with Internet of Things. IBM security researchers are warning...
-
 131Vulnerabilities
131VulnerabilitiesTor Project patches critical XSS bug in its blog after researcher publicly discloses it
Tor Project patches critical bug but refuses to acknowledge the bug discovery by a security researcher. Tor Project’s website had a critical cross-site...
-
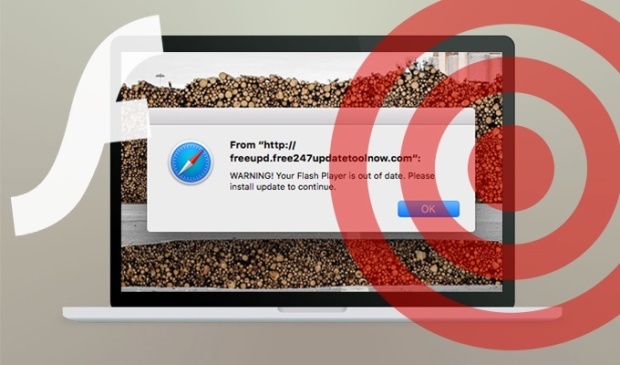
 95Vulnerabilities
95VulnerabilitiesResearchers spotted a new OS X scareware campaign
Experts at the SANS Technology Institute spotted an OS X scareware campaign that leverages fake Adobe Flash Player installers. Johannes Ullrich, security...
-

 356Geek
356GeekResearchers Found 60+ Malware Infected Android Gaming Apps on Play Store
For cybercriminals developing an Android malware is a piece of cake and the problem is Google just not care. According to Dr.Web’s security...
-
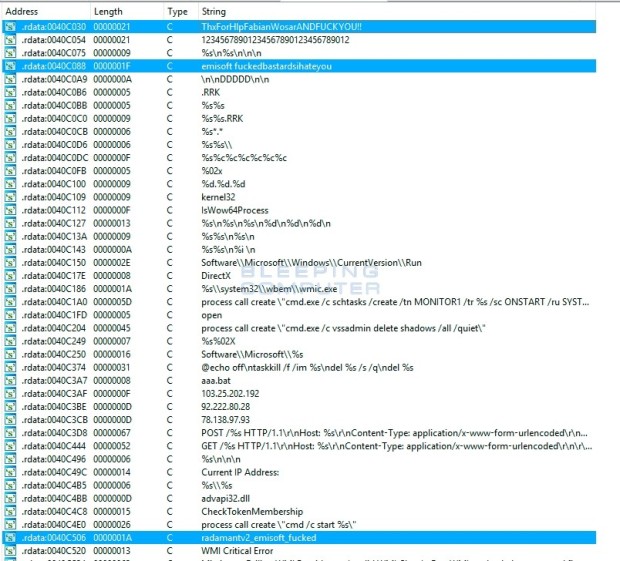
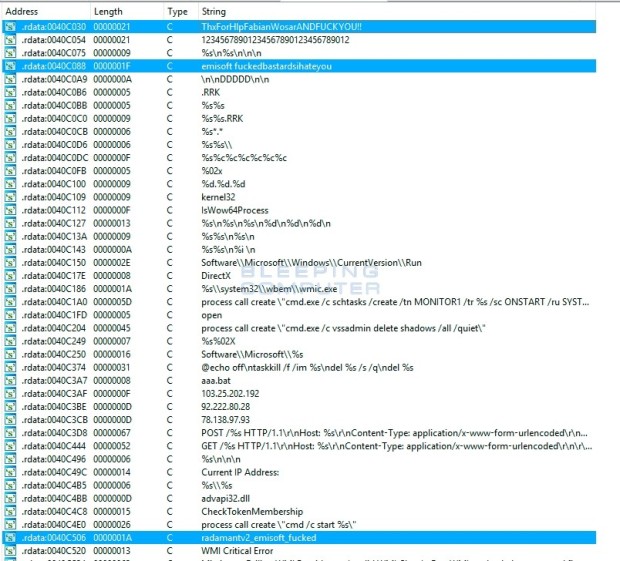 108Malware
108MalwareRadamant Ransomware Author Has a Fit When Researcher Cracks His Encryption
Radamant ransomware v1 and v2 are now decryptable. Fabian Wosar, security researcher at Emsisoft, has managed to crack the encryption algorithm for the...
-

 337News
337NewsResearcher Finds 191 Million US Voter Registration Records Online
Chris Vickery, a security researcher who is known for finding leaked databases online claims he has found US voter registration records of 191...
-

 328News
328NewsInstagram Hacked: Security Researcher Gets Admin Panel Access
Wesley Wineberg, an independent security researcher, participating in Facebook’s bug bounty program, managed to crack his way through Instagram defenses and almost...
-

 183Incidents
183IncidentsResearcher Hacks Instagram, Gets Backend Access
Facebook doesn’t appreciate the effort, threatens to sue. Wesley Wineberg, an independent security researcher, participating in Facebook’s bug bounty program, managed to crack...
-
 284Data Security
284Data SecurityResearcher Threatened with Infection For Exposing Flaw in HIV Dating App
Websites and apps around the world encourage researchers to find bugs in their system, but an Internet dating app for HIV positive...
-

 341News
341NewsMacKeeper Hacked: Researcher Finds 13 Million Credentials Online
ShortRead: MacKeeper, a utility software suite for Mac OS X faced a data breach which has exposed details in relation to its...






