Search results for "Research"
-
 251Geek
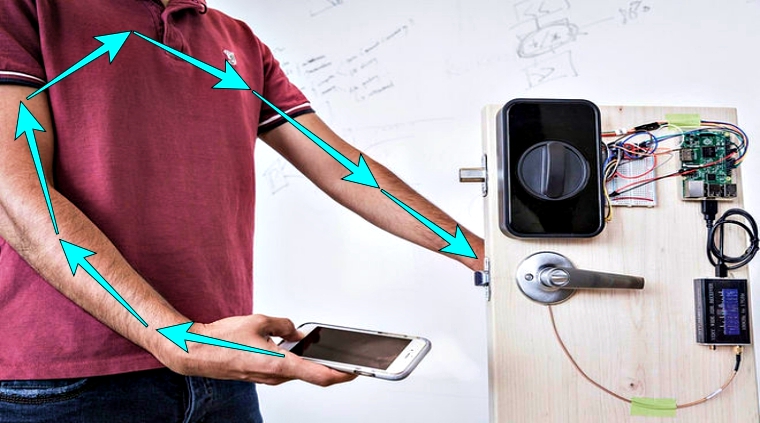
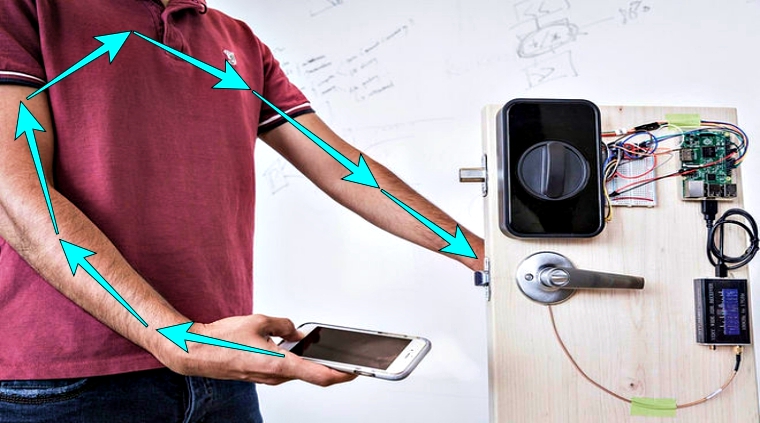
251GeekResearchers Send Secure Passwords Using the Human Body
Sending passwords through an Internet connection or Bluetooth is not safe anymore so these researchers have developed a technology that sends passwords...
-

 165Malware
165MalwareCrypto needs more transparency, researchers warn
Publish primes with seeds, so we know there are no backdoors. Researchers with at the French Institute for Research in Computer Science and...
-
Mobile Security
Malware researcher Lukas Stefanko will be online on Reddit
WeLiveSecurity author and ESET researcher Lukas Stefanko will be answering questions about Android malware on Reddits‘ popular Subreddit r/IamA.
-

 197Geek
197GeekConfirmed! Researchers Are Close To Creating A Hack-Proof Code
Short Bytes: More and more things are getting connected to the internet. Apart from its advantages, it also raises a concern regarding...
-

 173Vulnerabilities
173VulnerabilitiesCar Hacking Research: Remote Attack Tesla Motors
With several months of in-depth research on Tesla Cars, we have discovered multiple security vulnerabilities and successfully implemented remote, aka none physical...
-

 175Data Security
175Data SecurityFACEBOOK FIXES VULNERABILITY THAT LED TO ACCOUNT TAKEOVER, PAYS RESEARCHER $16K
Facebook quickly resolved a vulnerability in its Business Manager tool late last month that could have let an attacker take over any Facebook page....
-
 118Cyber Crime
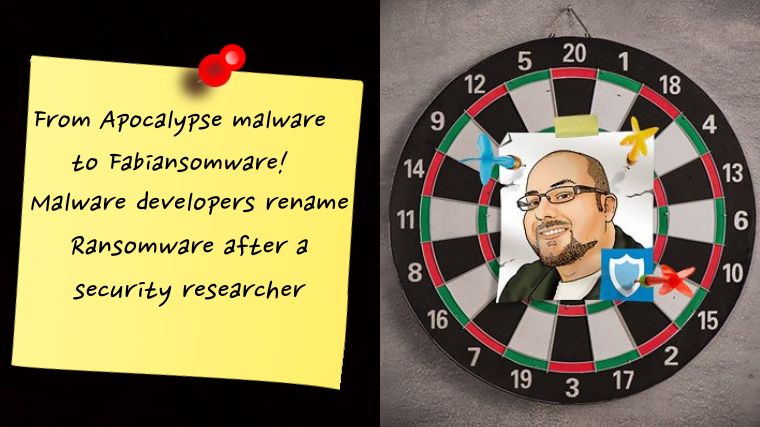
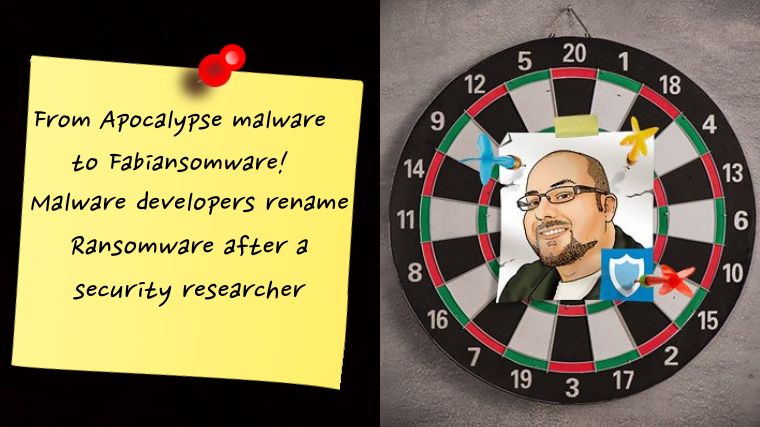
118Cyber CrimeMalware Authors Rename Ransomware After Emsisoft’ Security Researcher
His name is Fabian Wosar and he is a Ransomware Decrypter from Emsisoft, known for being an expert in his job. However, Wosar...
-

 144Incidents
144IncidentsResearchers Use Wi-Fi Signals to Sniff Keystrokes
New WiKey attack can compromise passwords via WiFi signals. It is theoretically possible to accurately detect keystrokes using the Wi-Fi signals from a...
-
 158Data Security
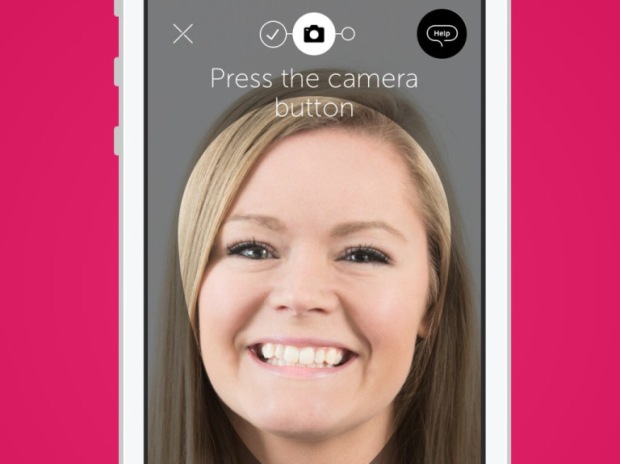
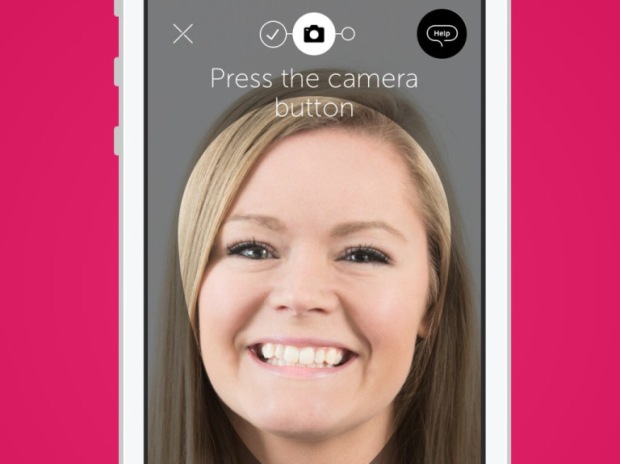
158Data SecurityiPhone’s ‘Live Photos’ can be used to hack bank apps, Claims researcher
Researcher claims that iPhone’s ‘Live Photos’ can be used to hack 2 banks apps. In a shocking discovery, a researcher found that 2...
-

 308News
308NewsWikiLeaks Turkish AKP Email Dumps Contain Malware; Researcher
Last month Wikileaks published emails stolen from Turkish ruling party AKP — Now, a researcher has presented a report showing the AKP...
-
 257Hacked
257HackedYour Linux Distro Can Be Hacked In 60 Seconds Due To Serious TCP Flaw: Research
Short Bytes: Researchers have found a critical flaw that affects all Linux kernel version 3.6 and beyond. If left unnoticed, this flaw...
-
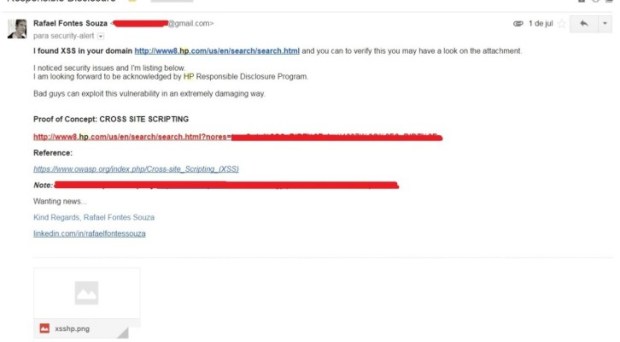
 173Vulnerabilities
173VulnerabilitiesSecurity Researcher found vulnerabilities on the HP Website
The security expert Rafael Fontes Souza has discovered vulnerabilities in the website of HP (Hewlett Packard) and decided to explain concepts of...
-

 175Malware
175MalwareResearchers Hide Malware Inside Digitally-Signed Files Without Breaking Hashes
New technique makes malware detection almost impossible. A team of security researchers from Deep Instinct have discovered a method of injecting malware inside...
-
 197Data Security
197Data SecurityResearchers crack open unusually advanced malware that hid for 5 years
Espionage platform with more than 50 modules was almost certainly state sponsored. Security experts have discovered a malware platform that’s so advanced in...
-
 258Data Security
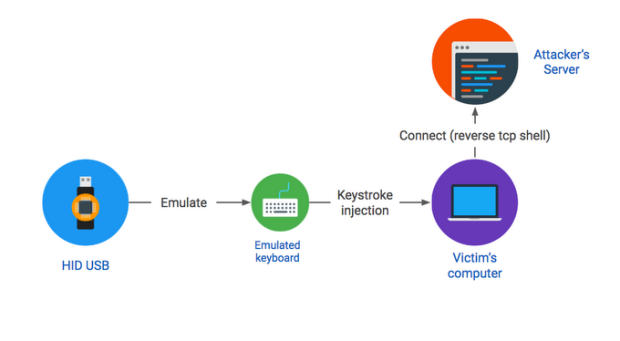
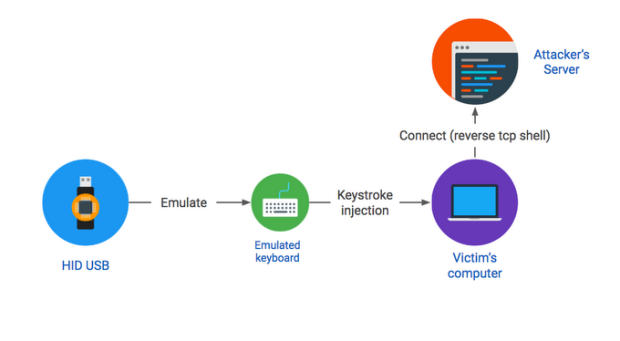
258Data Security#BHUSA2016 – Researcher explained how to hack any PC with a found USB drive
Dropping a malicious USB key in a parking lot is an effective attack vector, as demonstrated by our recent large-scale study. This...
-

 177Data Security
177Data SecurityResearchers Put Together PHP Zero-Day in Order to Hack PornHub
PHP project fixes issues affecting all PHP versions 5.3+ A team of three researchers went so far as to search and discover a...
-
 215Incidents
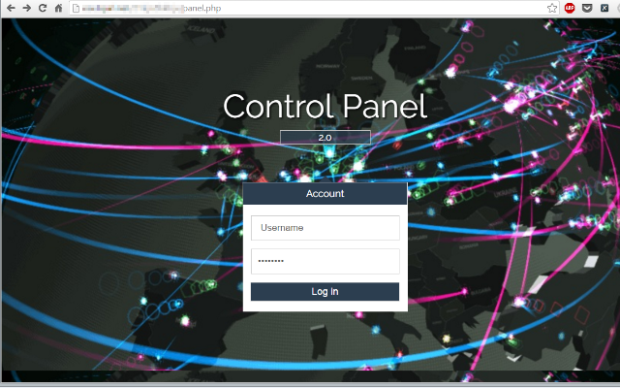
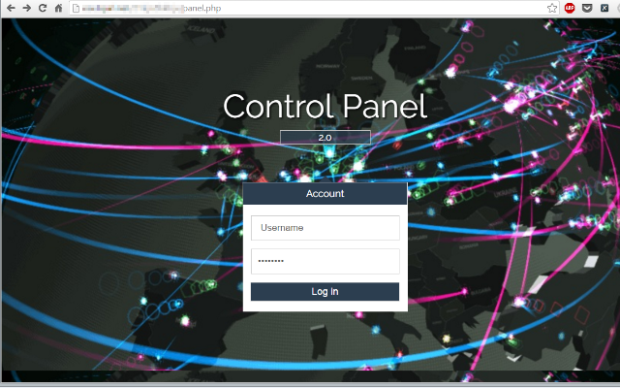
215IncidentsResearchers Hack Their Way into Punkey PoS Malware Backend
Criminals infected over 200 US businesses with PunkeyPOS. Security researchers from PandaLabs have hacked their way into the administration panel of the PunkeyPOS...
-

 156Incidents
156IncidentsRussian government hackers penetrated DNC, stole opposition research on Trump
Russian government hackers penetrated the computer network of the Democratic National Committee and gained access to the entire database of opposition research...
-

 95Data Security
95Data SecurityMore corporate shared folders in cloud filled with malware, research finds
In related studies: Ice is cold; fire still hot. Internet file sharing has long been a prime route for malware to spread. The...
-

 230Data Security
230Data SecurityMITSUBISHI HYBRID SUV HACK PUTS DRIVERS AT RISK, SAYS RESEARCHER
Security experts are warning owners of Mitsubishi Outlander Plug-In Hybrid Electric Vehicle that their cars can be hacked via the automobile’s on-board...
-

 123Data Security
123Data SecurityResearchers show how to steal data through PC components without hacking
No hacking required, as these Israeli researchers demonstrate how to steal data through PC components. A series of side-channel-attacks that can steal...






