Search results for "Research"
-

 324News
324NewsResearcher reports how to hack Facebook account with Oculus Integration
How to hack a Facebook account is something that almost everyone wants to know – And now, a security researcher has reported...
-

 246Vulnerabilities
246VulnerabilitiesSecurity researchers flag invite bug in WhatsApp group chats
Security researchers have revealed details of a vulnerability in WhatsApp’s security that could be used to compromise the secrecy of encrypted group...
-

 230Malware
230MalwareESET research: Appearances are deceiving with Turla’s backdoor-laced Flash Player installer
ESET researchers have found that Turla, the notorious state-sponsored cyberespionage group, has added a fresh weapon to its arsenal that is being...
-
 225Articles
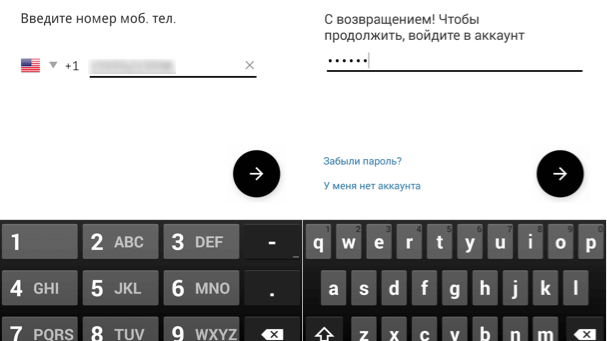
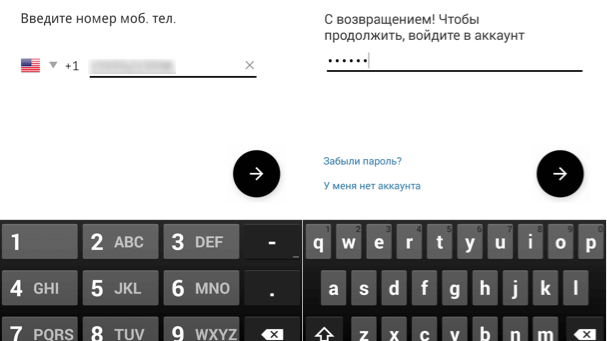
225ArticlesSymantec Researchers Have Discovered A Fake Android App That Steals Uber Credentials
Millions of people have become victims of a FakeApp that is using new tricks to cheat Uber users around the world. Security...
-

 81Incidents
81IncidentsSecurity researcher says DirecTV hardware can be easily hacked
The flaw was privately disclosed to the device maker in June, but six months later, there’s still no patch. Homes signed up...
-

 221Articles
221ArticlesMaker of sneaky Mac adware sends security researcher cease-and-desist letters
The maker of a sneaky adware that hijacks a user’s browser to serve ads is back with a new, more advanced version...
-

 182Hacked
182HackedKorean Researchers Create An “Unhackable and Indestructible” Chip — Here’s How It Works
I don’t need to stress the increasing cybersecurity threats like ransomware and botnets again. Over the course of this year, we’ve witnessed...
-
 187Geek
187GeekMost Software Code Will Be Written By Machines By 2040, Researchers Predict
Imagine a scenario where a programmer needs to follow a couple of tried and tested procedures to write code that becomes a...
-
 317Geek
317GeekResearcher finds pre-installed keylogger in hundreds of HP laptops
When it comes to pre-installed malicious software, HP (Hewlett-Packard) has a thing for them. In May this year, the tech giant was...
-
 193Articles
193ArticlesSecurity Researcher Claims that Apple’s iOS 11 Devices are Prone to Single Point of Failure
After rapidly reinforcing a flaw that acknowledged anyone with access to a High Sierra Mac to take administrative control, Apple still has...
-

 425Malware
425MalwareESET malware researchers awarded prize in open‑source memory forensics competition
The Volatility Foundation, the non-profit organization behind the Volatility Framework, sponsors the yearly Volatility Plugin Contest to acknowledge the best forensic tools...
-

 223Geek
223GeekDeleting anyone’s Facebook photo, a bug that earned researcher $10,000
The social media giant Facebook has more than 2 billion monthly active users so when there is a bug in it, that’s...
-
 262Malware
262MalwareTop Websites Are Using Keyloggers Recording Even Passwords, Research Shows
Well over 400 high profile websites are collecting all the keys that you’ve pressed, and it turns out that most of them...
-

 220Geek
220GeekResearchers demonstrate Amazon Key system can be hacked
Rhino Security Labs’ researchers have discovered a vulnerability in Amazon’s Key delivery service and Cloud Cam security camera. This vulnerability allows an...
-
 221News
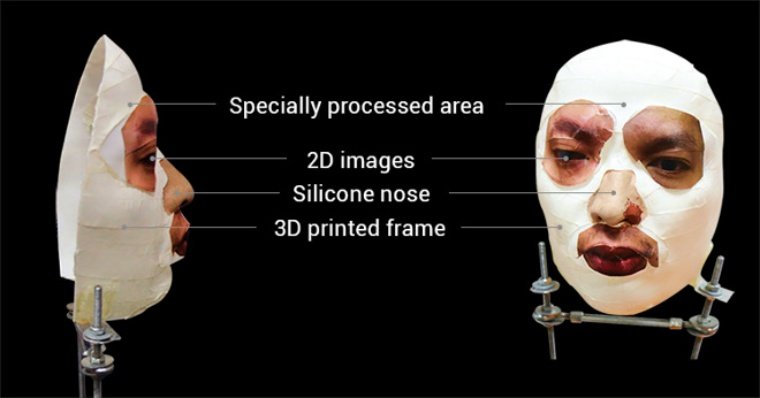
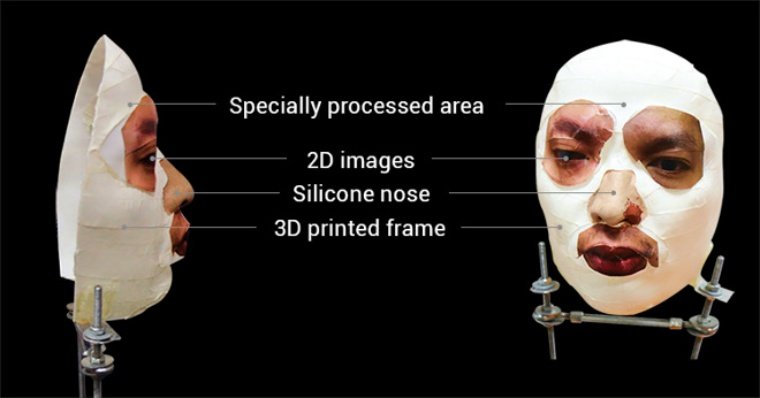
221NewsAll it took for researchers was a mask to bypass iPhone X Face ID
Apple Inc. introduced Face ID facial recognition system on September 12, 2017, with the launch of iPhone X and claimed that even...
-

 133Geek
133GeekResearcher Identifies Bugs in Google’ Bug Tracker Program
A security researcher has identified bugs in Google’s bug tracker platform Issue Tracker. It is indeed ironic that the software intended to...
-

 157Cyber Crime
157Cyber CrimeESET research team assists FBI in Windigo case – Russian citizen sentenced to 46 months
Relating the collaboration between ESET experts and the FBI about the Windigo's operation, which ended with the sentencing of Maxim Senakh.
-

 197Articles
197ArticlesLG Robot Vacuums can act as the best Spying Machines according to Security Researchers
The flaw was discovered by researchers from Check Point in the user authentication method between the SmartThinQ portable app and LG’s back-end...
-

 308News
308NewsResearchers hack vacuum cleaner; turn it into perfect spying device
According to the findings of Check Point researchers, there is a vulnerability in the LG smart home infrastructure through which hackers can...
-

 173Articles
173ArticlesAccording to Research: 25% of the Federal Government Mails are Fraud
Agari supports email fraud on behalf of larger than 400 federal websites, including the real sites of the departments of Health and...
-
Articles
Security Researchers think that Google’s Home Mini Requires a software fix to prevent it from hearing everything
Smart Home Systems like the Google Home Mini is intended to only listen for a specific wake word, in this case, it’s...






